SNMP or Simple Network Management Protocol is one of the most famous networking protocols in existence. Network administrators are intimately familiar with components such as SNMP Managers, SNMP Agents, and SNMP traps. The range of SNMP-enabled devices has led to a substantial number of networks incorporating SNMP monitoring to keep tabs on their network. But what is SNMP?
The SNMP protocol can be used to monitor everything from traffic to infrastructure health and network performance. SNMP is an interesting topic because while the concept behind the protocol is relatively simple in practice, things can get a little bit more complicated. In this article, we look at this popular protocol and see how it works.
Contents
- 1 What is SNMP?
- 2 How Does SNMP Work?
- 3 SNMP Manager, SNMP Agent, and MIB Breakdown
- 4 What Ports Does SNMP Use?
- 5 What are SNMP Traps?
- 6 SNMP Commands
- 7 SNMP Versions
- 8 SNMP Monitoring Software
- 9 What are the Advantages of Using SNMP?
- 10 What Are the Disadvantages of Using SNMP?
- 11 Minimizing the Security Risks of SNMP
- 12 What is SNMP? A Networking Essential
What is SNMP?
SNMP was originally created in 1989 in order to allow devices to exchange information with each other throughout a network. There are several versions of SNMP available from the outdated V1 to the most widely-used V3. The SNMP protocol is most commonly used within network monitoring to identify connected devices and monitor the performance of the network as a whole.
However, the usage of SNMP is restricted to whether or not a device is compatible with the protocol. You can only monitor devices that have SNMP-enabled. Though this excludes lots of hardware there are so many vendors producing SNMP-enabled products that SNMP is still one of the most widely-used protocols today.
How Does SNMP Work?
In order to work correctly and transfer information on device status to the end user to monitor, SNMP relies on a number of components. There are four main components that make up SNMP:
- SNMP Manager
- SNMP Agent
- Management Information Base (MIB)
- SNMP Devices
It is important to note that the setup of SNMP is based on a client-server model. With SNMP the SNMP Manager is a platform that has the job of polling SNMP-enabled devices and retrieving data from them. There are a variety of SNMP Managers available on the market, and many of these are free.
SNMP Agents are programs that reside within the piece of hardware you’re interacting with. The SNMP Agent collects data on things like bandwidth and disk space, aggregates it and sends it to the Management Information Base (MIB). An Agent can be any SNMP device connected to the network from a PC right down to a switch or server. The Manager and the Agent are in a constant state of communication with each other.
SNMP Manager, SNMP Agent, and MIB Breakdown
One of the most important aspects to understand about SNMP is the relationship between the key components of SNMP. The SNMP Manager and SNMP Agent are two elements that have a relationship based on data collection. The Agent takes information from a device and passes it on to the SNMP Manager where it can be viewed by the end user with a monitoring tool. We’re going to discuss this below:
SNMP Agent
The SNMP Agent is located within a device. The Agent has the responsibility of collecting information from a device and passing it to the SNMP Manager. Each time a query is made, the SNMP Agent sends data to the SNMP Manager. The SNMP also manages and stores information within the Management Information Base (MIB). When a significant event happens the SNMP Agent will also send notifications to the Manager without being polled.
SNMP Manager
An SNMP Manager (also known as a management station) is a separate system that is used to communicate with an SNMP Agent. Generally speaking, an SNMP Manager is a computer that runs network monitoring platforms. An SNMP Manager queries Agents, receives responses from Agents and acknowledges asynchronous events from Agents.
Management Information Base (MIB)
The MIB is a component contained within SNMP Agents. The SNMP Manager uses the MIB as a database and asks the SNMP Agent for access to particular information. This information is generally needed for the Network Management System (NMS). Essentially the SNMP Manager asks the Agent questions and the Agent uses the MIB to supply the data to the Manager.
MIB files are a set of questions that an SNMP Manager can ask the Agent. The Network Management System polls the Agent to take information from these files and then proceeds to translate it into graphs and displays that can be viewed by the end user. MIBs contain statistical and control values that are determined by the network device. Most hardware providers have private MIB with additional values.
What Ports Does SNMP Use?
One of the most common questions asked about SNMP is the port numbers that it uses. The answer to this varies based upon whether you’re talking about the SNMP Manager or SNMP trap. When polling, SNMP Managers uses port UDP 161. In contrast, when an Agent sends information to the Manager via an SNMP trap, SNMP uses port UDP 162.
What are SNMP Traps?
SNMP Traps are a process where a device sends an alert to your network monitoring platform without being polled. A trap ensures that the SNMP Manager stays updated on current developments on the device even if the device isn’t in the process of being polled. This is advantageous to the user because it means the SNMP Manager isn’t responsible for catching every development that occurs.
All SNMP traps can be classified as one of two things:
- Polled
- Autonomous
Polled SNMP traps request updates from connected devices periodically. This depends on the interval that is set by the user. On the other hand, Autonomous SNMP traps are automatically sent to an SNMP Manager once an event occurs. Autonomous traps are the type of traps that are most commonly referred to as alerts. These alerts are triggered when a significant amount of loss or latency or a failure occurred. You can also configure your own autonomous trap parameters so that you receive a notification when something significant happens.
SNMP Commands
There are a number of different commands that you can use for the SNMP protocol. We’ve listed some of the most common ones below:
- GET – A request sent by the Manager to the device to retrieve a value or values from the device
- GET NEXT – Retrieves the value of the next OID from the MIB tree
- GET BULK – Retrieves voluminous data from a large MIB table
- SET – A command from the Manager used to change a value with a managed device
- TRAPS – TRAP is a signal that the Agent sends to the SNMP Manager to notify about an event within a device
- INFORM – This command does what TRAP does but also adds confirmation from the SNMP Manager upon receipt
SNMP Versions
There have been a number of different versions of SNMP since it was released. Today SNMP V1 and V2c are undoubtedly the most commonly-used versions of the protocol. More providers are starting to support SNMP V3 but it still has a ways to go before catching up with the others.
| Version | Defined In | Description | Security |
|---|---|---|---|
| SNMP V1 | RFCs 1155 and 1157 | Open, standard protocol supported by smaller RTUs | Community security |
| SNMP V2c | RFC 1901, RFC 1905, RFC 1906, RFC 2578 | Added the inform command (manage acknowledges with a response message, with improved error handling and better SET commands | Community security |
| SNMP V3 | RFC 1905, RFC 1906, RFC 3411, RFC 3412, RFC 3414, RFC 3415 | More secure, EngineID Identifier used to identify each SNMP entity. Authentication keeps traps secure and SNMP messages are encrypted | User-based security |
SNMP Monitoring Software
In order to make use of SNMP, you need a software interface to view data from the device MIB. Thankfully there is a range of SNMP monitoring solutions available right now. In this section, we’re going to look at some of the best SNMP monitors to help you get the most out of your network monitoring.
SNMP Monitoring with Site24x7 Network Monitoring Tool (FREE TRIAL)
Site24x7 is a cloud-based, agentless SNMP monitoring solution for IT teams managing diverse infrastructure (from routers and firewalls to hybrid cloud services). By using SNMP, Site24x7 collects performance and health metrics from devices supporting SNMP v1, v2c, or v3. This makes it compatible with lots of networked devices set across different environments.
Site24x7 also offers unified observability. It combines network, application, and server monitoring into a single dashboard. The platform also includes real-time alerts, automated device discovery, anomaly detection, and Layer 2 topology mapping. These features are perfect for having end-to-end visibility in complex IT scenarios. Try it free: Start 30-day trial.
Key Features:
Site24x7 blends SNMP and infrastructure monitoring in a way that simplifies network management. Here’s a quick look at what it offers:
- Automatic Discovery: It scans your IP range and spots SNMP-enabled devices on its own.
- Works with Many Vendors: Over 450, including big names like Cisco, Juniper, HP, and Dell.
- Ready-to-Go Device Templates: You get access to 11,000+ pre-built templates, so setup is fast.
- Custom SNMP Counters: You can create your monitors for key hardware or proprietary metrics.
- Real-Time Trap Processing: Get instant alerts when something’s off. This is great for catching issues before they blow up.
- Layer 2 Network Mapping: See how your switches, routers, and access points are connected—visually.
- Health Dashboards: Clean and visual dashboards show you system health, service uptime, and SLAs.
- Real User Monitoring (RUM): This one’s a unique addition. It lets you track performance from the actual user’s point of view, across devices and locations.
Who do we recommend Site24x7 for
While no tool fits every setup, Site24x7 offers a solid mix of visibility and simplicity. It’s ideal for small to mid-sized IT teams, MSPs, and pros in DevOps or NOC roles who need centralized monitoring across complex systems. Industries with strict uptime and compliance needs—like healthcare, finance, and manufacturing—can also rely on its real-time alerts, SLA dashboards, and fault detection. And if you’re running hybrid or multi-cloud environments (AWS, Azure, or global systems), Site24x7 delivers the unified observability to keep everything running smoothly.
Why We Recommend Site24x7
After an active hands-on trial, we found that Site24x7 does an excellent job blending traditional SNMP monitoring with modern, full-stack observability. It lets IT teams monitor physical devices and local infrastructure. It also supports cloud services, all from one platform. This helps catch issues early on, before they reach end users.
A key feature worth mentioning is Real User Monitoring (RUM). It adds to the SNMP data by tracking live performance from actual users across different locations and devices. This level of insight is usually part of more advanced Application Performance Monitoring (APM) tools. In Site24x7 it brings valuable context to how your infrastructure is really performing.
The interface can feel a bit complex at first. However, it quickly becomes essential for getting to the root of problems, improving performance, and preventing future incidents. If you’re looking for enterprise-level visibility without the weight of a full-blown monitoring suite, Site24x7 offers a clean, scalable alternative.
SNMP Monitoring With ManageEngine OpManager (FREE TRIAL)
Another popular SNMP monitoring tool is ManageEngine OpManager. This is a network monitoring and management tool that uses SNMP traps to obtain data on more than 3000 metrics from different network devices. It analyzes this data and compares it with pre-existing thresholds to identify any deviations in availability and performance. OpManager also helps in identifying network faults, and sends alerts on the same to the concerned employees for quick remediation.
OpManager’s network device discovery capabilities automatically identify what devices are connected to your network at any given time. It automatically organizes the devices into different categories. This entire inventory management process is automated.
Key Features:
OpManager integrates SNMP monitoring data into your wider network monitoring, to provide comprehensive visibility into your organization’s operations. Below are a few key features of this tool.
- Automatic Device Discovery: Discovers devices in your network automatically and creates maps for easy understanding.
- SNMP Metrics: Monitors a wide range of metrics, like availability, packet loss, response time, temperature, CPU, fan speed, and more.
- Fault Management: Detects faults and identifies their root cause for speedy troubleshooting.
- Reports: Generates reports that can be easily shared with the concerned stakeholders.
- Low Resource Usage: Uses asynchronous SNMP traps to gather information from network devices.
Who do we recommend ManageEngine OpManager For
ManageEngine OpManager works well for organizations of all sizes, especially those that have different network devices on their infrastructure. MSPs who handle client networks and ensure their smooth working can also benefit from using OpManager, as it can track more than 3000 metrics across different vendors.
Why do we recommend ManageEngine OpManager
OpManager is a comprehensive tool that provides all the insights you need in a single console. It gathers data from network devices without being intrusive, and compares them against established thresholds to identify deviations. Often, these deviations in metrics are due to issues in the underlying device, which, if unresolved, can impact a device’s availability and performance. OpManager sends data about these devices to your team for quick troubleshooting.
This tool also generates extensive reports that can be used to support decisions and communicate with the concerned stakeholders. Due to these features, OpManager can leverage SNMP to keep your network robust and in good health. Download a 30-day free trial.
SNMP Monitoring with Paessler PRTG Network Monitor

Another formidable SNMP monitoring alternative is Paessler PRTG Network Monitor, a scalable network monitoring solution that includes a sensor that supports SNMP V1, V2c, and V3. This tool offers its own auto-discovery feature which allows you to identify SNMP-enabled devices throughout your network automatically. If you want to monitor other types of flows then this is a good choice as PRTG Network Monitor offers NetFlow, IPFIX, and jFlow monitoring.
What makes PRTG Network Monitor ideal for SNMP monitoring is its range of SNMP sensors. There are five core sensors for monitoring SNMP: the SNMP CPU Load Sensor, SNMP Disk Free Sensor, SNMP Memory Sensor, SNMP Traffic Sensor, and SNMP Hardware Status Sensor. These all bring to the table specific SNMP information that is displayed with dials for ease of access. For example, the SNMP traffic sensor provides you with an overview of how much traffic is flowing through the ports of a device. Paessler has made a 30-day free trial available for PRTG so you can try out the SNMP sensor.
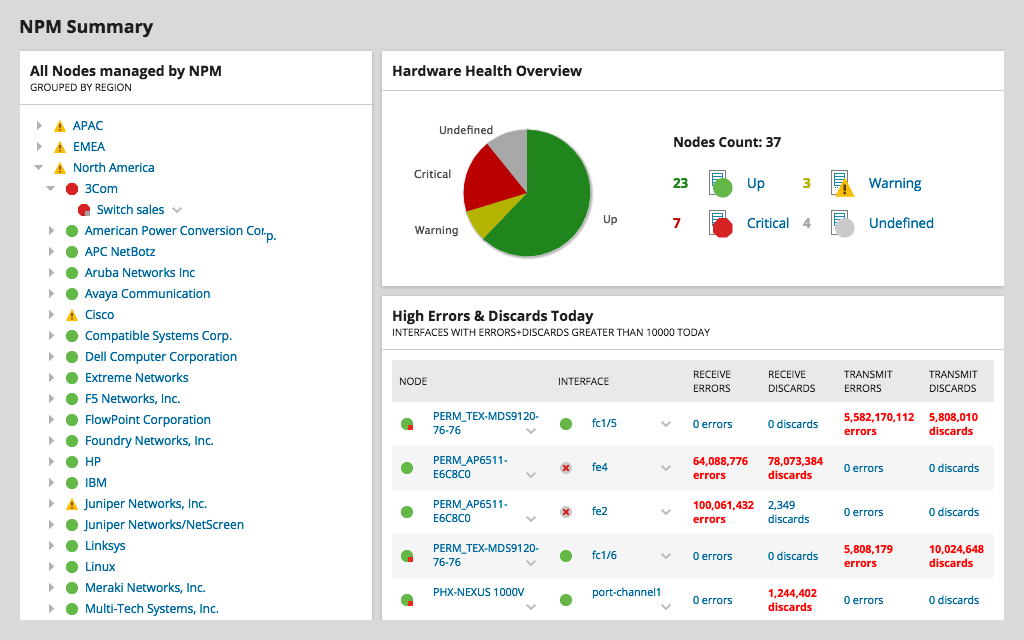
SNMP Monitoring with SolarWinds Network Performance Monitor
SolarWinds Network Performance Monitor (NPM) is a network monitoring tool for Windows that offers support for the SNMP protocol. With SolarWinds NPM you can use SNMP for automatic network discovery to find SNMP-enabled devices throughout your network. This is advantageous for enterprises of all sizes because it means that you don’t have to configure individual devices manually.
SNMP monitoring wise, when you poll devices you will receive information on their current performance and availability. If a device goes down, you’ll know about it. There is also a network topology map that shows the geographical location of SNMP-enabled devices throughout the network. These maps are color-coded so that you can tell the performance of individual devices from a distance. SolarWinds NPM can be downloaded and evaluated on a 30-day free trial.
What are the Advantages of Using SNMP?
There are many different reasons why you should consider using SNMP in your network. The most basic reason why is that it provides you with a large degree of visibility. You can check up on SNMP-enabled devices with an SNMP monitoring tool and verify whether a service is experiencing performance issues. In this section, we’re going to look at some of the main advantages of using SNMP.
SNMP Open Protocol
One of the biggest advantages of SNMP is that it is an open protocol. An open protocol is a protocol that isn’t confined to one vendor like a proprietary protocol is. As an open protocol, SNMP is supported by a range of vendors. With a proprietary protocol, you’re always at the mercy of the vendor who produced it. As an open protocol, SNMP has a variety of vendors that you can buy from to keep this technology as accessible as possible.
Alerts with SNMP Traps
SNMP traps act as alerts for the status of your connected devices. Whether it’s a fault or failure within a device, SNMP traps keep the SNMP Manager updated as things progress. This means that SNMP traps are integral for keeping you up-to-date with what is going on. The variety of parameters that can be configured within SNMP traps also opens up your options dramatically.
Fault Management
Based on the widespread usage of SNMP and the alerting ability of SNMP traps, SNMP is an excellent fault management solution. You can monitor the health of devices through polling and SNMP traps to make sure that you don’t miss any crucial details. Once your SNMP Manager receives information from the MIB it has the depth to allow the person to solve it.
What Are the Disadvantages of Using SNMP?
Even though SNMP provides you with a vast amount of detail there are a number of areas where SNMP is lacking. The main areas are in terms of scalability and security. SNMP has a tendency to struggle with larger workloads and older versions are particularly vulnerable to outside access. In this section, we’re going to look at some of the disadvantages that come with SNMP.
Scalability
One significant problem with SNMP is its lack of scalability. SNMP struggles to retrieve large volumes of data. While the data you receive provides you with lots of information this doesn’t translate well to monitoring large bundles of data like an entire routing table. In this sense SNMP is resigned to those cases where you want to enjoy an in-depth perspective of a few things rather than complete visibility over a large data set.
Security
One of the biggest issues with SNMP is its lack of security. While SNMP V3 makes use of encryption and other security measures SNMP V1 and V2c are vulnerable to outside attacks. The reason is that these two versions barely have any form of authentication. Even SNMP V3 needs to be configured against unauthorized users. There is no way to get around the fact that SNMP acts as an entry point to your network.
Devices Need to be SNMP-Enabled
With SNMP you are also limited to monitoring SNMP-enabled devices. If a device isn’t SNMP-enabled then you can’t monitor it with SNMP. This is why most network monitoring tools include a mix of protocols so that the user can patch together visibility. If you want to use SNMP monitoring then you want to make sure that a significant number of devices throughout your network are SNMP-enabled so that you can see what is happening.
Minimizing the Security Risks of SNMP
As mentioned above, the main security risks of SNMP are present within V1 and V2c. The lack of authentication means that you need to take other measures to minimize the risk to your systems. While you’re better off using V3 you can reduce the threat to your network by changing the default community and configuring SNMP to read-only. Read-only will help to make sure that unauthorized users can’t tamper with your data.
That being said where possible we recommend that you upgrade to SNMP V3. SNMP-enabled devices can often be upgraded to later versions of SNMP. By doing this you will reduce the security risks that SNMP has for your system. If you’re using outdated equipment then this might not be possible but it is a good idea to check.
However, even on SNMPV3, you’ll want to make sure you have optimized your settings for security. To do this you would enable authPriv which includes a mix of authentication and encryption that will help to keep you protected from malicious entities. You will also want to make sure that you have different passwords for authentication and encryption so that you can’t be breached here either. It is also a good idea to apply Access Control Lists (ACLs) to ensure that unauthorized computers can’t access the device.
What is SNMP? A Networking Essential
SNMP is one of the most widely-used open protocols in the world. While it isn’t without its problems, SNMP offers a level of network monitoring potential that is only rivaled by a few other protocols. Deploying SNMP monitoring within your network will allow you to verify the status of your SNMP-enabled devices and keep your network secure from unforeseen downtime.
When using SNMP you will need to take extra care to make sure that you have the correct security configurations in place for your version number. This way you can minimize the vulnerabilities that are inherent to SNMP and keep your network protected from unauthorized users.
Lastly, you’ll want to make sure that you pick the right SNMP monitoring tool for your network. A good SNMP monitoring tool will help to turn that boring data into visually compelling graphs and charts for you to browse. Site24x7 and ManageEngine OpManager are two network monitoring tools we recommend based on their ease of use and high-quality visualization.