Secure Web Gateway (SWG) solutions keep infected PCs off the internet while also enforcing organizational standards. A secure Web gateway removes unwanted software/malware from user-initiated Web/Internet traffic while also enforcing business and regulatory policy compliance. URL filtering, malicious-code identification and filtering, and application controls for popular Web-based services like instant messaging (IM) and Skype must all be included as a minimum in these gateways. Data leak prevention is increasingly being implemented as a native or integrated feature.
In this article, we will look at Forcepoint Secure Web Gateway which is a very popular tool. Alongside, we will also look at some of the famous alternatives that are available.
Forcepoint SWG
Forcepoint Web Security is a cloud-driven web security gateway with URL filtering, data loss prevention, and Advanced Malware Detection (AMD). The Advanced Classification Engine (ACE), which has over 10,000 analytics, machine learning, and behavioral baselines, is used by Forcepoint Web Security to detect threats. It is very good with Malware Blocking, Data Loss Prevention, and Cloud Sandboxing.
The AMD feature is Forcepoint Web Security’s main line of defense against malware. AMD uses cloud sandboxing to contain malware outbreaks and minimize disruption to your network. Sandboxing makes it easier to remediate risk factors and return to normal operations.
The solution is also capable of detecting attacks with 100 percent accuracy using fingerprinting, indicating that it is prepared to deal with less visible dangers. Forcepoint Web Security features data loss prevention to protect your data if an attack succeeds or a disaster occurs. Through a single centralized console, you can easily manage data loss protection policies. Its key features are:
- On Device SWG Because Forcepoint SWG is mobile, it follows your employees wherever and whenever they go to work. It does not require on-premises hardware, VPNs, network hops, or cloud proxies because it decrypts and inspects traffic locally on each device. Remotely delete company data from managed devices with SWG’s on-device agent. On-device security safeguards your staff while they are on the job or working remotely.
- Keeping Threats at a Distance Even decent individuals make blunders from time to time. Data loss, network shutdowns, and time spent researching and recovering can all result from a fast visit to a suspect site. Forcepoint protects you from malware by detecting and quarantining threats before they reach your network. It analyses and stops malware in file uploads and downloads automatically.
- Control over Shadow IT Data is put out of your control via shadow IT. Using your web proxy and firewall logs, it quickly identifies managed and unmanaged cloud apps in real-time. When users try to share data on unmanaged cloud apps, alerts them and directs them to a managed app.
- Interface A thing that greatly influences user-friendliness is the type of interface a tool has. Forcepoint SWG has a very simple interface that is very easy to learn. It makes it very famous among the users.
- More Visibility and Control It enables policy deployment across web, cloud, and private apps. It can encrypt or conceal data in motion or at rest, block data in transit, redact it, or watermark it to track sensitive information. With on-device security, you can scan and prevent file uploads and downloads in real-time. To track sensitive data, block it in transit, encrypt or mask it, redact it, or watermark it. Traffic can be separated with Forcepoint RBI for the ultimate Zero Trust protection. Granular controls allow you to restrict access to all or parts of a website. Allow one group to access a certain subdomain while excluding other groups from accessing the entire site.
- Scalable License The license system is highly expandable, allowing you to expand your requirements at any time.
- Most Valuable Feature The feature that the editor finds most valuable is the flexibility of the single endpoint. A single endpoint for DLP can be used for Cloud Web Security and vice versa. They are also providing CASB functionality on that same endpoint. No other solution provides a single endpoint for CASB, DLP, and that proxy solution.
According to Peerspot, Forcepoint Secure Web Gateway is ranked #1 in the top Web Content Filtering tools, #4 in the top Internet Security tools, and #5 in the top Web Security Gateways.
Although this tool is very effective and is used by a lot of people and organizations all over the globe, there are also some cons associated with this tool. Some of them are:
- Pricing No price is shared on their website. You have to contact the sales team to enquire about the price. Also, the price is comparatively high as compared to its market rivals.
- Documentation There is a lack of documentation. People who have been using it have reported that they would like to see more documentation and self-help articles.
- Deployment The deployment might be made simpler. It could take anything from one to three days. Typically, this entails a vendor engineer and a team of employees from the company.
Forcepoint SWG Alternative Solutions
There are a lot of alternatives for Forcepoint SWG available. Some of them are discussed here:
1. Check Point’s SASE SWG (ACCESS FREE DEMO)
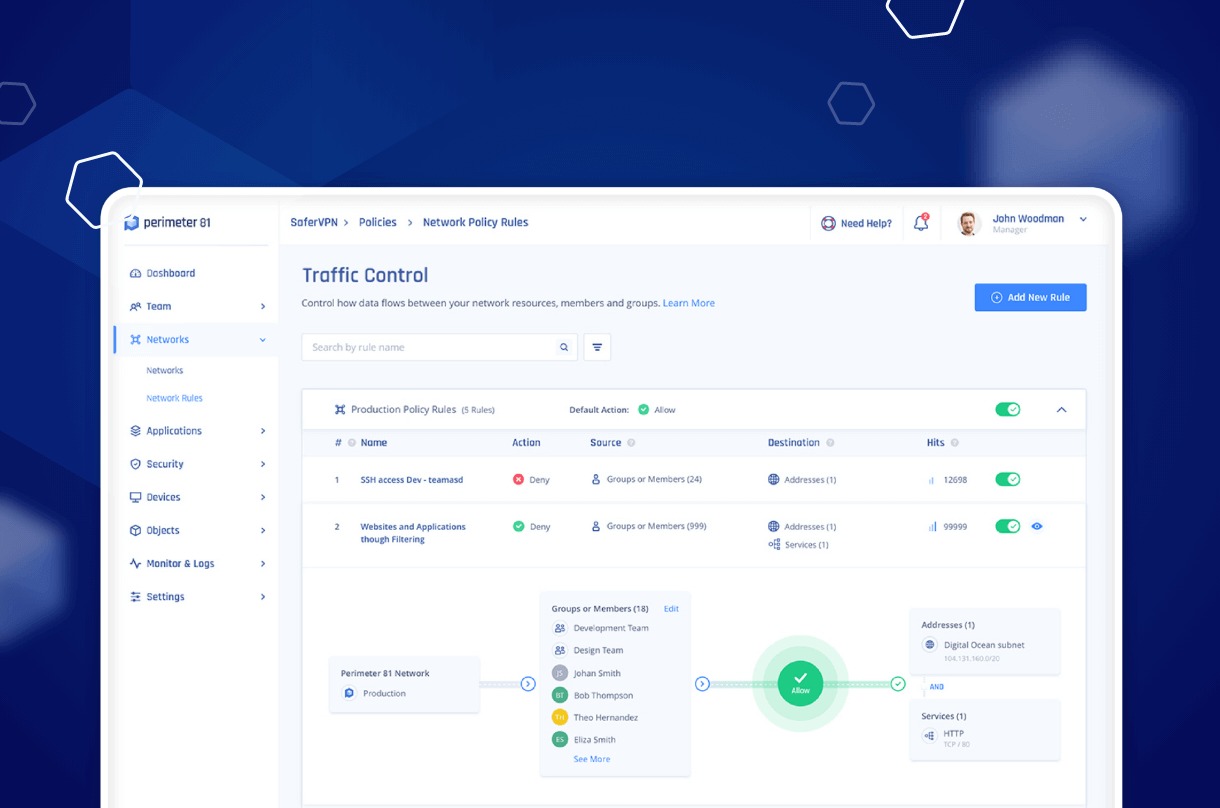
The Check Point’s SASE Secure Web Gateway, formerly Perimeter 81, is a Web filtering solution that protects a company’s network and endpoints against hazardous infections spread through the internet.
The detection of bogus websites that imitate real sites with login screens is also included in the automatic site access limits. These sites are used to steal victims’ login credentials. By rendering these counterfeit sites unreachable, the Secure Web Gateway protects business accounts from hacking.
Pros:
- Always-on protection.
- Cloud-based service with device agents.
- Blocks inappropriate sites.
- Detects fake and infected Web pages.
Cons:
- It doesn’t cover email.
System administrators can also use the tool to create custom filtering rules. These can be used to enforce the company’s Web usage policy at work. It makes it possible to keep company resources from being utilized to view inappropriate websites. Attempts to access prohibited websites are recorded.
The administrator dashboard can be viewed with any ordinary Web browser because this system is a cloud platform. The software isn’t limited to protecting personnel in a single place; it can also safeguard home-based workers’ gadgets. You can access a free demo.
2. ManageEngine Browser Security Plus (FREE TRIAL)
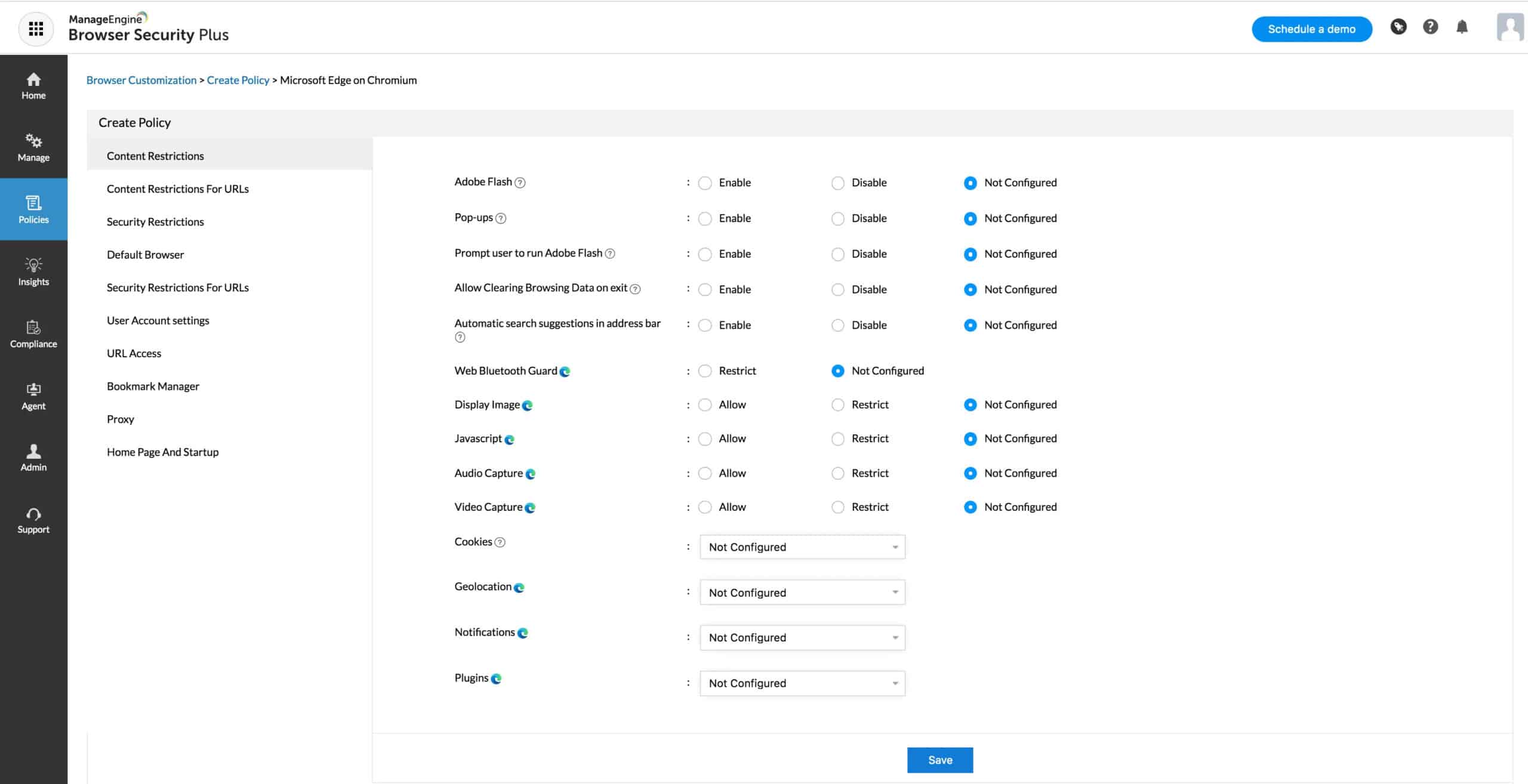
ManageEngine Browser Security Plus provides complete control over your network’s browsers at scale, supporting popular Chromium-based browsers.
Key Features
- Simple agent deployment
- Bulk management options
- Support for a variety of popular browsers
Browser Security Plus gives administrators full control over their organization’s browsers through a lightweight agent that works across many popular browsers. Administrators can easily apply updates, make configuration changes, and manage add-ins at scale through their remote dashboards.
Rather than fussing through group policies, Browser Security Plus automatically catalogs browser use on each device and aggregates that data in one place for simplified management. Whether you’re looking to maintain compliance or simply prevent phishing attacks, Browser Security Plus makes it easy to start protecting your user’s browsing experience.
Pros:
- Easily to manage browsers across large networks
- Quickly detect malicious add-ins and connections to harmful sites
- Includes support for various popular browsers
- Easily add and remove browser extensions
Cons:
- Can take time to explore all management features
Download a fully-featured 30-day free trial of the ManageEngine Browser Security Plus.
3. N-able Mail Assure

The N-able Mail Assure solution was previously provided by SolarWinds MSP as an edge service. MSPs can offer Mail Assure to their clients as an add-on service. When recommending Mail Assure to consumers, the MSP can incorporate technician oversight in its pricing plan. Although N-able sells the Mail Assure system to MSPs, there’s no reason why in-house IT departments shouldn’t use it as well.
All email traffic from the MSP’s clients must be routed through the Mail Assure system via a VPN because it is hosted on N-able servers. Similarly, all incoming emails are routed through the Mail Assure server before being routed through the VPN to the client’s PC.
Pros:
- Because it’s hosted in the cloud, there are no hidden infrastructure charges.
- MSPs and multi-tenant environments are catered for.
- If self-learning is used to improve threat detection, data obtained internally is used.
- Protects email servers hosted in the cloud.
Cons:
- The platform offers a lot of capabilities that will take some time to properly understand.
When a client’s email arrives at the Mail Assure server, it is scanned for security concerns such as spam, phishing attempts, address spoofing, impersonation, malicious content, and poisoned links. While serving all of its customers throughout the world, N-able compiles a threat intelligence database from all of the attacks it encounters. This centralized attack profile ensures that any threat discovered in one region of the world is immediately available to defend all other Mail Assure subscribers.
Apart from the threat intelligence database, Mail Assure also scans for common attack signatures and uses a sourced mail address blacklist.
The edge service also provides archiving and continuity services. Genuine email archives are automatically archived and can be restored on demand. The continuity service extends to all accounts on the protected system’s online mailboxes, allowing all users to access and send emails even if the primary email server is inaccessible.
4. CleanBrowsing

CleanBrowsing takes an alternative approach to network-wide Web security. Rather than protecting a network and filtering all traffic, the CleanBrowsing service concentrates on the Web pages requested by browsers within a company.
As a DNS resolver, the ClearBrowsing mechanism works. The browser converts the URL of a Web page into an internet address when a user requests it. By referring to a DNS server, the DNS resolver provides this address. The CleanBrowsing system, however, scans that page for infection, malicious content, or impersonation before delivering the retrieved address.
Pros:
- Protects against phishing emails that contain links.
- Access to specific websites might be restricted.
- Blocking access to certain types of websites is an option.
- There is no need to maintain onsite software.
Cons:
- It doesn’t block malicious traffic outside the requested Web page delivery.
The address of the service is simply nominated for the browser’s default DNS server when integrating this service. However, you can set up the redirection by altering the network router’s settings, which will apply the DNS service to all devices on the network.
CleanBrowsing is based in data centers all over the world. These dispersed locations offer faster reaction times as well as continuous availability.
CleanBrowsing is a completely free program. This service is most likely best suited for personal usage and small companies. It will prevent pornographic content and protect you from phishing attacks. There are three editions of the paid version. You can use these to create your own filtering rules, as well as receive adult content and phishing protection.
With the three premium options, you may monitor a large number of devices and incorporate endpoints from all over the world in one monitoring package. The technology can be used on mobile devices as well.
5. Zscaler Web Security

Zscaler Web Security is a web security gateway that includes URL filtering, a firewall, cloud-based application control, antivirus, anti-spam, DNS filtering, and other features. One of the benefits of being a part of the cloud gateway is that any threat detected by any user is automatically banned for all customers – there are over 120,000 security updates daily to safeguard clients from the latest threats. The program can also inspect SSL traffic, which is difficult to analyze on many other platforms.
Pros:
- DLP tools for file recovery and integrity monitoring are included in this adaptable cloud-based SaaS.
- Detects harmful packers in SSL traffic.
Cons:
- Need to contact the sales team for pricing.
- It might be time-consuming to set up.
- More troubleshooting articles for new users would be helpful.
To find new threats, the antivirus uses signatures from over 60 threat sources. However, the program isn’t just for monitoring security events; it may also help you improve the performance of your network. Zscaler Web Security’s bandwidth control capabilities can prioritize vital apps over less important traffic. Several data protection features are available to secure your files from loss or destruction. Protect user data by implementing Data Loss Prevention. A Cloud Application Security Broker controls user access to apps, and File Type Controls control which files can enter and depart the network.