As a network administrator, do you really know what’s happening on your network? Using a port scanning tool can help identify potential vulnerabilities as well as paint a detailed picture as to what devices are open to certain types of communication. In this article, we’ll review the six best port scanner tools you can use to help discover vulnerabilities, and better defend your network.
Here is our list of the best port scanner tools:
- ManageEngine OpUtils EDITOR’S CHOICE An advanced port scanner tool that provides detailed information about every port and the services it runs, enabling you to improve the security of your infrastructure. Download a 30-day free trial.
- ManageEngine Vulnerability Manager Plus (FREE TRIAL) Offers a comprehensive vulnerability and patch management solution that includes continuous scanning across diverse network environments. It combines network visibility with built-in remediation tools, making it ideal for proactive security. Start a 30-day free trial.
- Site24x7 (FREE TRIAL) Continuously monitors the availability and performance of services running on TCP/IP ports, and sends notifications through multiple channels, when the metrics deviate from the established thresholds. Start a 30-day free trial.
- Nmap The most trusted open-source port scanner for penetration testers and network pros, with unmatched customization, scripting, and OS fingerprinting capabilities.
- SolarWinds Port Scanner Combines Nmap’s backend with an intuitive interface, offering efficient scanning, OS detection, and exportable results in a user-friendly package for Windows users.
- Angry IP Scanner Lightweight and fast, this cross-platform tool is perfect for quick network discovery and port scans, making it a help desk favorite.
- Netcat: A barebones command-line utility that excels in precise port scanning and network debugging tasks, favored by advanced users and security professionals.
- Unicornscan A powerful, security-focused tool offering advanced packet crafting and asynchronous scanning for deep network reconnaissance.
- Pentest-Tools A web-based scanning solution that makes port scanning accessible for non-technical users, providing a fast and simple interface for external IP scans.
- IP Fingerprints A free and flexible online port scanner that supports customized scanning types like SYN, ACK, and FIN stealth scans without needing local installation.
What are port scanner tools used for?
From network administrators, security experts, and even hackers, all port scanners help detect what ports are open, closed, or filtered on a device that is on a network.
These details combined with manufacturer information can help give context as to what a device’s purpose is on the network. With that information, attackers will attempt to use known exploits over those ports to gain unauthorized access.
Checking for unnecessary open ports is usually one of the first steps an attacker will do when trying to find ways into your network. As an administrator, we can run these tools first to defend from potential attacks. Port scanner tools give admins a chance to shut down unused ports that are open and terminate suspicious connections.
Ports can be left open unintentionally, or forced open by rootkits and other advanced types of malware. These ports are essentially exploited as backdoors to exfiltrate stolen data and push out commands to existing malware on the network. Performing a network security audit with a trusted port scanner tool can help detect some of the stealthiest types of malware and attacks.
Using a port scanner tool on a network you own is perfectly fine. If for whatever reason you need to run a port scan tool on someone else’s network, ensure you have written permission to do so. Running these tools on networks you do not have permission to is deemed illegal in most countries.
The Best Port Scanner Tools
Let’s dive into some of the best port scanning tools on the market today, and review exactly why they made the list. Some tools below have multiple uses, but today we’ll be focusing on their port scanning features.
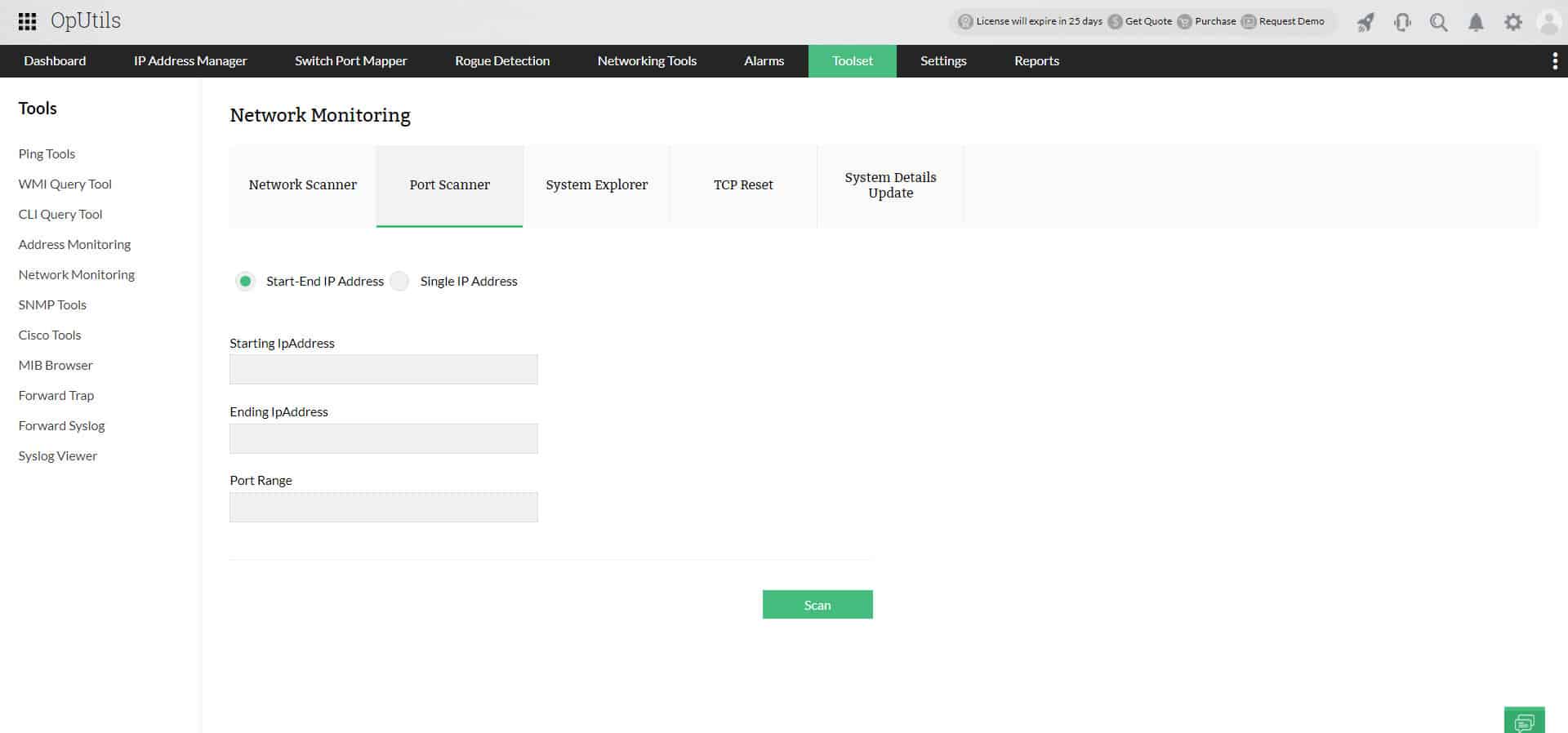
1. ManageEngine OpUtils (FREE TRIAL)
ManageEngine OpUtils is an advanced port scanner that provides complete information about every port in your network. With this tool, you can get insights into how your network ports are connected and the devices accessing each of them.
Key Features:
- Port Status Monitoring: Checks the status of every port to provide complete visibility.
- Port Services: Makes a list of the services running in each port and the devices connecting to them.
- Extensive Reports: Generates extensive reports that provide information about each port.
- Usage Metrics: Provides information about usage metrics to help make informed decisions.
- Unauthorized Devices: Prevents any unauthorized devices from accessing your ports.
Why do we recommend it?
We recommend ManageEngine OpUtils because of its comprehensive approach to port scanning. This tool detects all open ports in your network and identifies the services running on them to provide detailed views on how every device is using them. A standout feature for us is the detailed scan reports that make it easy for any stakeholder to understand port usage and security. It is also easy to use.
Who is it recommended for?
It is recommended for network administrators, security engineers, and compliance teams of all organizations to better understand the status of each port. It is helpful for MSPs who want to improve the security of their client networks.
Pros:
- Comprehensive Visibility: Provides end-to-end visibility into ports.
- Automated Scanning: Enables you to schedule scanning at specified intervals.
- User Interface: Comes with an intuitive user interface.
- Security: Detects and blocks unauthorized devices from accessing your ports.
Cons:
- Complex Setup: The initial setup is complex and requires technical expertise.
ManageEngine OpUtils starts at $138 per year. Download a 30-day free trial.
EDITOR'S CHOICE
ManageEngine OpUtils wins the Editor’s Choice award for the best port scanner because it scans every port in detail to identify the services running on each and the devices accessing each port. More importantly, it presents all these insights on centralized dashboards and intuitive reports that make it easy for everyone to better understand port statuses. Other advanced features, like setting automated scan schedules, detection of unauthorized devices, and more, make it the top choice on our list.
Download: Get a 30-day FREE trial
Official Site: https://www.manageengine.com/products/oputils/
OS: Windows, Linux
2. ManageEngine Vulnerability Manager Plus (FREE TRIAL)
ManageEngine Vulnerability Manager Plus is a comprehensive vulnerability discovery, assessment, and remediation platform suitable for SMB to enterprise networks.
Key Features:
- Multi-OS Compatibility: Supports Windows, Linux, and Mac for complete infrastructure coverage.
- Integrated Patch Management: Automatically deploys patches for operating systems and third-party applications.
- Continuous Vulnerability Scanning: Runs automated scans across LAN, WAN, and remote sites to ensure ongoing protection.
- Prioritized Risk Assessment: Uses a built-in severity ranking system to streamline remediation efforts.
- Extensive Threat Intelligence: Constantly updates its vulnerability database with emerging security risks.
Why do we recommend it?
ManageEngine Vulnerability Manager Plus earns its recommendation by offering a comprehensive and scalable solution for vulnerability management. Its capacity to conduct thorough scans across diverse networks, including remote sites and WANs, ensures that vulnerabilities are identified throughout the entire infrastructure. The platform’s intuitive severity ranking system streamlines the prioritization of remediation efforts, enhancing the efficiency of the vulnerability management process. With support for various operating systems, including Windows, Linux, and Mac, ManageEngine Vulnerability Manager Plus caters to the needs of diverse networks, making it a versatile and effective choice for businesses of varying sizes.
Vulnerability Manager Plus starts by scanning your entire network to locate vulnerabilities across your hardware and network infrastructure. The scan easily extends beyond your LAN to include remote site subnets and other interconnected WANs. Once complete, the scan provides a severity ranking for each issue found, making it easy to tackle what issues need to be addressed first. The platform supports Windows, Linux, and Mac operating systems, making it an ideal choice for more diverse networks.
Finally, the management platform helps ensure that loopholes stay closed and helps prevent future vulnerabilities moving forward.
Who is it recommended for?
ManageEngine Vulnerability Manager Plus is ideal for SMB to enterprise networks seeking an all-encompassing vulnerability management solution. Network administrators and security professionals tasked with overseeing diverse operating systems, including Windows, Linux, and Mac, will find this platform particularly beneficial. Its automated scanning capabilities and built-in patch management for both OSs and third-party applications make it well-suited for organizations aiming for continuous vulnerability remediation. The flexibility and robust threat intelligence support further position ManageEngine Vulnerability Manager Plus as a valuable asset for businesses looking to fortify their security posture.
Pros:
- Lifecycle-Based Protection: Continuously scans and patches devices from deployment to retirement.
- In-Depth Reporting: Offers detailed reports to help visualize progress and compliance after remediation.
- Highly Flexible Deployment: Operates seamlessly across multiple OS platforms and diverse environments.
- Updated Threat Intelligence: Leverages an evolving vulnerability feed to stay ahead of threats.
- Free Version Available: Offers a no-cost option suitable for smaller organizations with limited budgets.
Cons:
- Initial Setup Time: Requires a significant upfront effort to fully integrate into existing security workflows.
Download a fully-featured 30-day free trial of the ManageEngine Vulnerability Manager Plus.
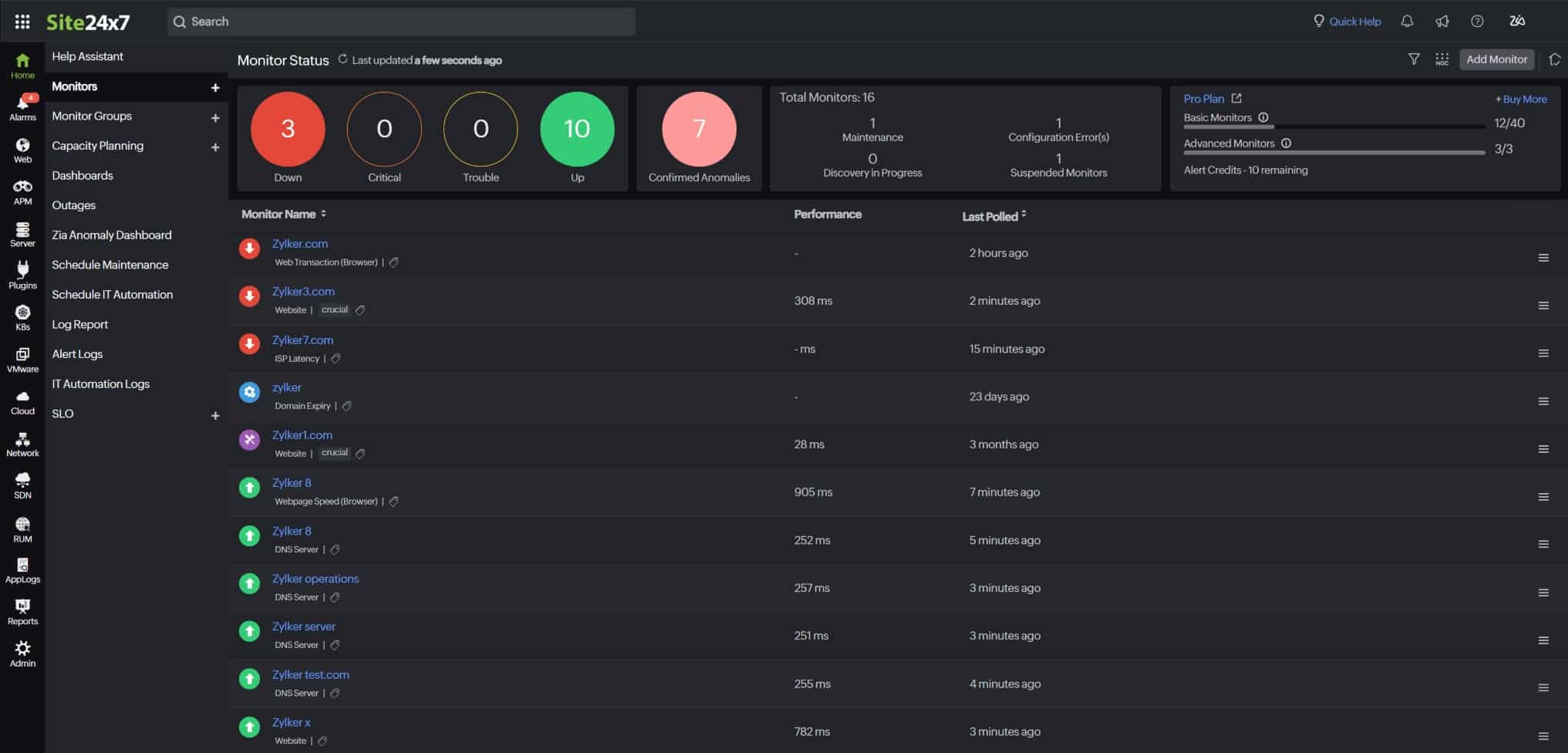
3. Site24x7 (FREE TRIAL)
Site24x7 is a cloud-based port monitoring tool that continuously checks the services running on the ports to evaluate the availability, security, and performance of your ports. You can run these checks from more than 130 locations around the world and at your preferred frequencies.
Key Features
- Service Monitoring: Tracks 20+ metrics of services running on your ports.
- Open Port Notifications: Sends alerts when your ports are opened, provided you have opted to receive them.
- Multi-channel Alerts: Generates notifications through email, SMS, calls, Slack, JIRA, PagerDuty, and more.
- Detailed Analysis: Offers detailed analysis on KPIs for further actions.
- Reports and Dashboards: Displays data on intuitive reports and dashboards.
Why do we recommend it?
We recommend Site24x7 because it is comprehensive and can track 20+ metrics related to services running on your ports. Based on this information, it is easy to spot issues on your ports and their root causes, so you can take action accordingly. Also, we love the way this tool displays information on reports and dashboards. Its multichannel notifications are another plus.
Who is it recommended for?
It is highly recommended for security officers, MSPs, and network administrators who are responsible for maintaining the security and availability of ports.
Pros:
- Intuitive User Interface: The reports, dashboards, and the overall UI are intuitive, making it ideal for employees of all backgrounds.
- Notifications: Sends notifications via multiple channels.
- Extensive Tracking: Tracks more than 20 metrics of all services running on your ports.
- Scalable: Extends to more ports as needed.
Cons:
- Only Cloud: This service is available only as a cloud-based service.
Site24x7 offers three plans – Lite, Professional, and Enterprise. They are priced at $9, $42, and $625, respectively. Start a 30-day free trial.
4. Nmap

Nmap is one of the most widely used and trusted port scanner tools in the world of cybersecurity. It’s the cornerstone of any pentester’s toolkit and helps aid in network discovery, device vulnerability, and network reconnaissance. Nmap which is aptly short for network mapper lives up to its name doing just that.
Key Features:
- Comprehensive Port Scanning: Powerful tool for scanning TCP and UDP ports, identifying open, closed, or filtered ports across networks to assess security and detect vulnerabilities.
- Advanced Host Discovery: Performs network sweeps to discover hosts and devices, even in heavily filtered environments, ensuring thorough network visibility.
- Customizable Scan Types: Offers various scan methods, such as SYN scan, ACK scan, and NULL scan, allowing users to tailor scans for specific use cases and environments.
- Scripting Engine (NSE): Includes a robust scripting engine that automates tasks like vulnerability detection, malware discovery, and service enumeration, extending its functionality.
- OS and Service Detection: Identifies operating systems, software versions, and running services on remote hosts, providing critical insights for security assessments.
Why do we recommend it?
Nmap stands out as a leading and widely trusted port scanner tool in the realm of cybersecurity. Its robust capabilities make it a cornerstone in the toolkit of penetration testers, aiding in network discovery, device vulnerability assessment, and network reconnaissance. The tool’s success is attributed to its open-source architecture and user-friendly design, fostering active communities for troubleshooting, bug fixing, and feature enhancements. Nmap excels in providing detailed outputs, offering insights into network information, device responses, port statuses, and running services. Its command-line interface, while potentially intimidating for newcomers, is complemented by Zenmap, a graphical alternative that simplifies the scanning process.
What’s made the tool so successful is its open-source architecture and relative ease of use. This has allowed dedicated communities to troubleshoot bugs and add additional features that might be helpful for port scanning.
Nmap scans networks and provides very detailed outputs containing information about the network, how devices responded to the scan, the status of the ports, and what services the device might be running.
This is all done through a command-line interface, which can be a bit intimidating to newer users. While I personally am a fan of the command line, those who want a more graphical-based approach can use Zenmap. Zenmap is essentially Nmap without having to type all of the commands out.
Since Nmap is so lightweight it is preferred among many security professionals, as it can be used to scan massive corporate networks with very little resource footprint. Behind Nmap is an entire Lua programming language and Nmap scripting language. This allows you to automate and script out very specific types of conditions you’re looking to find in your scan.
Who is it recommended for?
Nmap is highly recommended for cybersecurity professionals, penetration testers, and network administrators seeking a powerful and versatile port scanner tool. Its open-source nature allows for continuous community-driven improvements, ensuring reliability and effectiveness. While the command-line interface may require some familiarity, Zenmap provides a graphical option for those who prefer a more user-friendly experience. Nmap’s lightweight footprint makes it ideal for scanning large corporate networks with minimal resource usage. The tool’s compatibility with various operating systems, including Windows, macOS, Linux, Free BSD, and Solaris, enhances its accessibility and makes it an invaluable asset for cybersecurity enthusiasts. Nmap’s free and open-source model further contributes to its popularity and widespread use in the cybersecurity community.
Pros:
- Highly Versatile: Supports a wide range of scan types and use cases, making it suitable for everything from simple network inventory to advanced penetration testing.
- Free and Open Source: Cost-effective and benefits from an active developer and user community that continuously updates and enhances its capabilities.
- Extensive Documentation: Comprehensive guides, tutorials, and community resources make it easier for both beginners and advanced users to leverage Nmap’s full potential.
- Cross-Platform Compatibility: Available on multiple operating systems, including Windows, macOS, Linux, and BSD, ensuring flexibility across diverse IT environments.
- Highly Customizable: Users can configure scan parameters, timing, and output formats to suit their specific requirements, enhancing usability for different scenarios.
Cons:
- No Native GUI: While third-party GUIs like Zenmap exist, they may not provide the full functionality of the command-line tool, requiring users to rely on CLI for advanced tasks.
- Detection by Security Tools: Nmap scans can be flagged by intrusion detection systems (IDS) or firewalls, potentially alerting administrators during penetration testing.
- Limited Reporting Features: While the tool excels at scanning, its native reporting capabilities are minimal, often requiring integration with external tools for comprehensive reporting and visualization.
Nmap is completely free and open source. Nmap runs on nearly all operating systems including Windows, macOS, Linux, Free BSD, and Solaris.
5. SolarWinds Port Scanner
SolarWinds Port Scanner combines the raw power of Nmap and displays its outputs elegantly through a simple and intuitive interface. By selecting an individual device or range of IPs SolarWinds Port Scanner will get to work and display the results in the same window on the right-hand column.
Key Features:
- Comprehensive Port Scanning: Allows users to scan a range of IP addresses to identify open, closed, and filtered TCP and UDP ports, providing detailed insights into network configurations and potential vulnerabilities.
- Hostname and MAC Address Resolution: Resolves hostnames and MAC addresses, offering additional context about the devices associated with each scanned port, which aids in network management and security assessments.
- Operating System Detection: Detects the operating systems of scanned devices, helping administrators understand the network landscape and identify systems that may require updates or patches.
- Configurable Scan Profiles: Users can save scan configurations into profiles, allowing for quick re-execution of scans with predefined settings, enhancing efficiency in regular network monitoring tasks.
- Exportable Results: Scan results can be exported in multiple formats, including XML, XLSX, and CSV, facilitating easy sharing and further analysis of the data collected during scans.
Why do we recommend it?
SolarWinds Port Scanner stands out as an excellent choice due to its effective combination of the powerful Nmap engine with a user-friendly interface. The tool efficiently translates the robust scanning capabilities of Nmap into an intuitive display, allowing users to select specific devices or IP ranges effortlessly. With features like multi-thread scanning and adaptive timing behavior, SolarWinds Port Scanner excels in scanning larger networks swiftly. Its ability to save and reuse scan configurations, coupled with support for various export formats and IANA port names, enhances its usability for both regular scans and comprehensive network assessments.
The tool also utilizes multi-thread scanning and adaptive timing behavior to shorten the total time needed to scan, making it a great tool for larger networks with more devices. For administrators that run scans regularly scan configs can be saved and reused at later on other networks or at a later time.
Results can be exported into several formats such as XML, CSV, and XLSX and fully supports IANA port names that can be edited in a separate file after scanning has been completed.
The tool gives a great quick breakdown if the ports are open, closed, or filtered, and even performs OS detection. The OS detection feature is used by attackers to gain contextual information about what services could be running, as well as narrow down what types of attacks are possible.
Each tool has its own methods of identifying operating systems. This is called a “Fingerprint” and is usually based on a number of different factors such as TCP/IP stack or other information that the device is broadcasting.
Who is it recommended for?
SolarWinds Port Scanner is highly recommended for network administrators and security professionals who prioritize a balance between advanced scanning capabilities and user-friendly interfaces. Its suitability extends to those managing larger networks with multiple devices, thanks to its efficient multi-thread scanning and adaptive timing. This tool is ideal for users who require quick and reliable insights into open, closed, or filtered ports, along with robust OS detection features. The ability to export results in various formats adds to its versatility, making it a valuable asset for network administrators seeking a comprehensive yet accessible port scanning solution.
Pros:
- User-Friendly Interface: The intuitive design of SolarWinds Port Scanner makes it accessible for users with varying levels of technical expertise, simplifying the process of conducting comprehensive port scans.
- Efficient Performance: With support for multi-threaded scanning and adaptive timing behavior, the tool efficiently handles large networks, reducing the time required to complete scans.
- Standalone and Free: As a free, standalone tool, SolarWinds Port Scanner provides essential port scanning capabilities without the need for additional software or financial investment, making it a cost-effective solution for network administrators.
- Customizable Scans: The ability to configure scan parameters and save them as profiles allows users to tailor scans to specific needs and quickly rerun them as necessary, streamlining routine network assessments.
Cons:
- Limited Advanced Features: While effective for basic port scanning tasks, SolarWinds Port Scanner lacks some advanced features found in other tools, such as vulnerability detection or integration with broader network management systems.
- Windows-Only Compatibility: Primarily designed for Windows operating systems, which may limit its utility for organizations utilizing diverse or non-Windows environments.
- No Real-Time Monitoring: Performs point-in-time scans and does not offer continuous monitoring capabilities, requiring users to initiate scans manually to obtain updated information.
Having such reliable OS detection and ease of use puts SolarWinds Port Scanner on our list. This tool is available for free for Windows operating systems only.
6. Angry IP Scanner
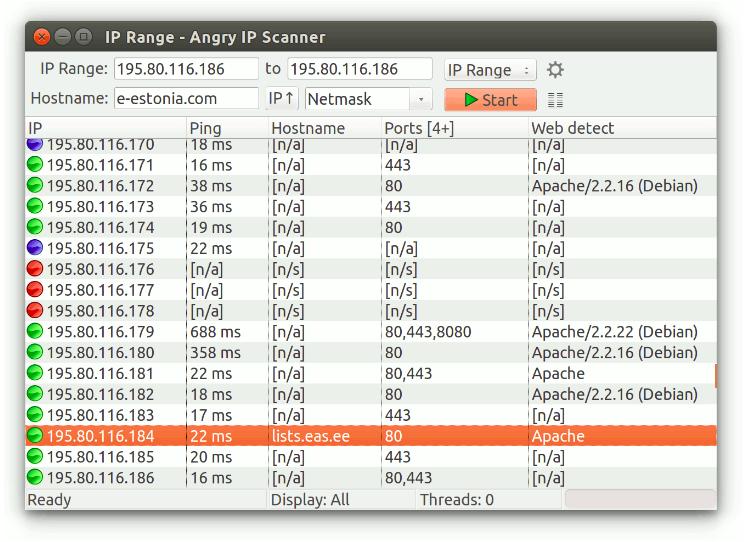
Angry IP Scanner is a great tool for quick and simple port scans, especially if used for network discovery. While other tools are more focused on security, Angry IP Scanner is built more for network discovery and device identification.
Key Features:
- Fast Network Scanning: Performs rapid scanning of IP addresses and ports using a multithreaded approach for enhanced speed and efficiency.
- Cross-Platform Compatibility: Operates seamlessly on Windows, macOS, and Linux, making it accessible to users across various operating systems.
- Extensibility with Plugins: Allows users to expand functionality with plugins to retrieve additional information such as NetBIOS details and web server detection.
- Command-Line Interface: Offers a CLI option for integration with scripts and automation of scanning tasks.
- Exportable Results: Enables saving scan results in formats like CSV, TXT, and XML for easy analysis and reporting.
Why do we recommend it?
Angry IP Scanner earns its recommendation as an excellent tool for swift and straightforward port scans, especially when geared towards network discovery. While some tools prioritize security aspects, Angry IP Scanner excels in network exploration and device identification. It has become a staple for help desks and technicians navigating unfamiliar networks, offering a quick and efficient solution for scanning subnets or entire IP ranges. Within minutes, the tool provides a list of IP addresses, their open ports, hostnames, and ping times, enhancing troubleshooting efforts and network connectivity assessments.
This tool is a staple among help desks and any technicians who find themselves working on a new network that they are unfamiliar with. In a matter of seconds, you can specify a subnet or entire IP range to scan. In just a minute or so a list of IP addresses will quickly populate along with their open ports and hostname.
The tool also displays the ping time from you to the device, which can be helpful if troubleshooting network connectivity. I personally used this tool to help track down devices that lost their static IP address, and it has never let me down.
You can also get a brief description of what the device could be running, for example, Angry IP may detect a device is running Apache or Windows. The scans are done using multithreading making it incredibly fast and efficient to run even on larger networks.
Who is it recommended for?
Angry IP Scanner is highly recommended for help desks, technicians, and network administrators dealing with new or unfamiliar networks. Its user-friendly interface and rapid scanning capabilities make it a valuable asset for swift network discovery. The tool’s ability to detect devices, display open ports, and provide brief descriptions of running services, such as Apache or Windows, adds to its versatility. While not primarily designed for security-focused port scanning, Angry IP Scanner strikes an excellent balance between functionality and ease of use. Moreover, its cost-effective nature, being freely available, positions it as an unbeatable choice for those seeking an efficient yet budget-friendly port scanning solution.
Pros:
- User-Friendly Interface: Intuitive design ensures accessibility for both beginners and advanced users, simplifying the scanning process.
- Lightweight and Portable: Requires no installation and can be run directly from a USB drive, adding flexibility for on-the-go use.
- Open-Source and Free: Cost-effective and benefits from community-driven updates and enhancements.
- Customizable Scanning: Users can define IP ranges, select specific ports, and apply filters to tailor the scanning process to their needs.
Cons:
- Requires Java Runtime Environment: Users must have Java installed, which may be an additional setup step for some.
- Limited Advanced Features: Lacks more sophisticated functionalities like detailed vulnerability assessments or in-depth service detection found in other tools.
- Potential Security Concerns: Improper use of the tool can trigger security alerts or be misinterpreted as malicious activity, requiring ethical and cautious use.
The tool isn’t the best port scanner for security purposes but strikes a great balance between port scanning features and ease of use. For the low price of free, you simply can’t beat it.
7. Netcat
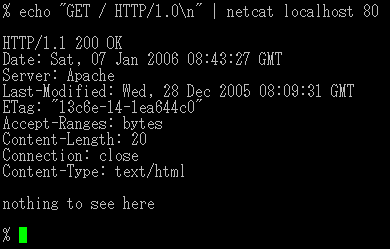
Netcat is similar to Nmap and dates back to the early 1990s. Despite being so old, it’s still in use today and has been a trusted tool in the utility bags of technicians all over the world. Netcat is the definition of barebones, meaning it doesn’t have any fancy features or utilities, it simply just does its job.
Key Features:
- Port Scanning: Performs basic port scanning to identify open ports and services running on a target host.
- Data Transfer and Debugging: Allows for the transfer of files and data between systems and serves as a debugging tool for testing network connectivity and communication.
- Listening Mode: Acts as a network listener for incoming connections on specified ports, useful for troubleshooting or creating lightweight servers.
- Flexible Protocol Support: Supports both TCP and UDP protocols, making it adaptable for various network tasks.
- Scripting and Automation: Easily integrates with scripts, enabling automation of repetitive networking tasks such as connection tests or payload delivery.
Why do we recommend it?
Netcat, despite its age dating back to the early 1990s, remains a trusted and reliable tool in the utility bags of technicians globally. This command-line-based tool is the epitome of barebones functionality, devoid of fancy features, focusing on efficiently executing its core tasks. Netcat’s strength lies in its versatility and the ability to perform specific scanning methods. For example, using the -z syntax allows quiet scanning for open ports without sending data, enabling discreet assessments without triggering intrusion detection systems. Its detailed and security-oriented results make it a specialized yet powerful tool for network security purposes.
Netcat is command-line based meaning it has a steep learning curve than other GUI port scanner tools. You can get very specific with your scanning methods. For instance, you can use the -z syntax to only scan for open ports without sending data to them. This is a way to quietly scan for ports without alerting intrusion detection systems.
Let’s take a look at some of the commands and how their output would look.
To scan port ranges 50-100 for open ports quietly you could use the following command:
nc -z -v 10.10.5.8 50-100
Since the -v command was used, the results will display in a verbose form.
nc: connect to 10.10.5.8 port 20 (tcp) failed: Connection refused nc: connect to 10.10.5.8 port 21 (tcp) failed: Connection refused Connection to 10.10.5.8 22 port [tcp/ssh] succeeded! nc: connect to 10.10.8.8 port 23 (tcp) failed: Connection refused nc: connect to 10.10.5.8 port 79 (tcp) failed: Connection refused Connection to 10.10.5.8 80 port [tcp/http] succeeded!
While these results aren’t as simple as the results you’d get for SolarWinds or ManageEngine, they are more detailed and security-oriented. That being said Netcat is definitely a more specialized tool based on network security.
Alternatively, you can even send files through Netcat and spin up an online chat server between two hosts. The tool has many uses, but one of its best features is its port scanning abilities.
Who is it recommended for?
Netcat is recommended for seasoned technicians and network security professionals who value a command-line approach and require detailed, security-focused port scanning. The tool’s steep learning curve may be challenging for beginners, but its capabilities extend beyond traditional port scanning. Netcat’s versatility allows for tasks such as sending files and establishing online chat servers between hosts. While it lacks a graphical user interface, Netcat’s specialized features make it an indispensable asset for those with a security-centric focus. It is available for both Windows and Linux environments, catering to a broad range of users in the cybersecurity domain.
Pros:
- Lightweight and Efficient: Compact tool with minimal system requirements, ensuring fast and efficient operation.
- Highly Versatile: Broad range of functionalities, from port scanning to acting as a backdoor, makes it a valuable tool for networking professionals and penetration testers.
- Cross-Platform Support: Available on multiple platforms, including Linux, macOS, and Windows, offering flexibility for users in diverse environments.
- Command-Line Interface: Provides precise control over network operations, with customizable options for various tasks.
- Open Source: As a free and open-source tool, Netcat is accessible to all users and benefits from community support for continuous improvements.
Cons:
- Steep Learning Curve: The command-line interface may be intimidating for beginners and requires familiarity with network concepts to use effectively.
- No Graphical Interface: The lack of a GUI may deter users who prefer visual tools for network management tasks.
- Outdated Features in Some Versions: Some implementations of Netcat may lack modern networking features available in newer tools.
Netcat is available for Windows as well as Linux environments.
8. Unicornscan
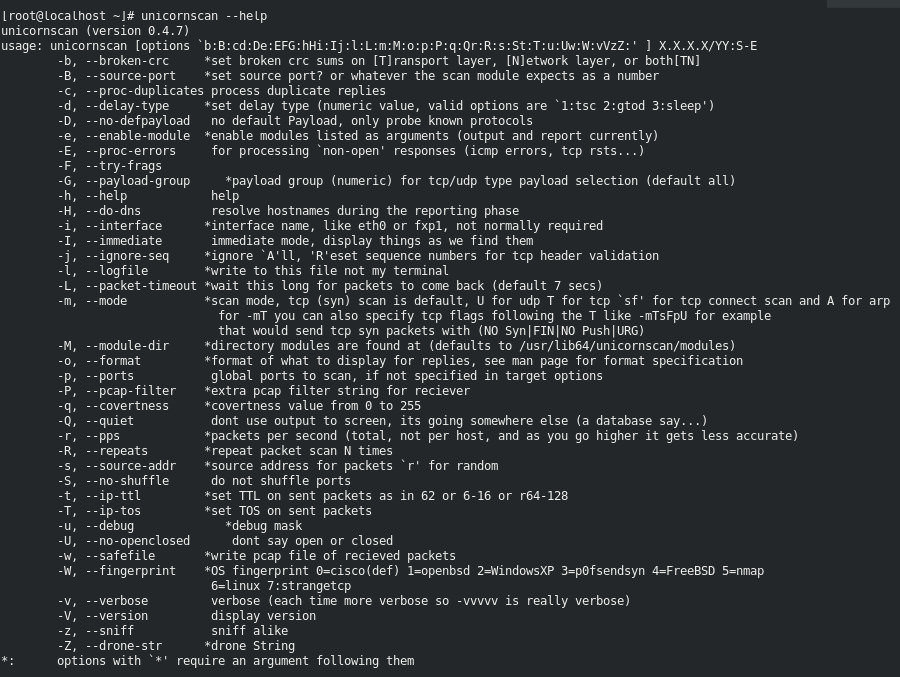
Unicornscan is a popular port scanner tool among the security community but doesn’t get much attention outside of these small groups. This Linux command-line tool supports asynchronous TCP and UDP scanning as well as IP port scanning with service and system detection.
Key Features:
- Asynchronous Stateless Scanning: Performs asynchronous stateless TCP and UDP scanning, allowing for high-performance scans by sending probes without waiting for responses, which accelerates the scanning process.
- Custom Packet Crafting: Enables users to craft custom packets at the byte level, providing precise control over the scanning process and facilitating the evasion of certain security measures.
- Protocol-Specific Scanning: Supports protocol-specific scanning, sending tailored signatures to elicit responses from various services, enhancing the accuracy of service detection.
- Active and Passive Detection: Offers both active and passive methods for remote operating system, application, and component identification by analyzing responses, aiding in comprehensive network profiling.
- PCAP Logging and Filtering: Includes PCAP file logging and filtering capabilities, allowing for detailed analysis and record-keeping of network scans.
Why do we recommend it?
Unicornscan, a Linux command-line tool, has gained popularity within the security community for its robust port scanning capabilities. While it might not enjoy widespread recognition outside security-focused circles, its asynchronous TCP and UDP scanning, coupled with IP port scanning and detailed service and system detection, make it a powerful asset for security professionals. Unicornscan’s strength lies in its flexibility, allowing security experts to perform highly detailed scans using unconventional network discovery methods. These methods often unveil details missed by other tools during scans of remote systems and services.
Like Nmap, the tool is incredibly detailed and flexible allowing security professionals to scan devices for ports in a number of different and unique ways. One of the reasons for Unicornscan’s popularity is its use of unconventional network discovery methods that can discover details missed by other tools when scanning remote systems and services.
Although there is no GUI for Unicronscan, we find the syntax to be simple to use, even easier than Nmap in some cases. One of the easiest ways to get access to Unicornscan is to get it from a free Kali Linux distribution. Alternatively, you can install it on other forms of Linux as well.
Who is it recommended for?
Unicornscan is highly recommended for security professionals, penetration testers, and network administrators operating within the Linux environment. The tool’s popularity within the security community is a testament to its effectiveness in uncovering nuanced details during scans. While it lacks a graphical user interface, Unicornscan’s command-line syntax is user-friendly, especially for those already familiar with Linux command-line tools. Users can conveniently access Unicornscan through free distributions like Kali Linux, making it readily available for penetration testing and security assessments.
Pros:
- High-Performance Scanning: Asynchronous architecture enables rapid scanning of large networks, making it suitable for extensive reconnaissance tasks.
- Advanced Customization: Crafts packets and customizes scans provides flexibility for specialized testing scenarios and research purposes.
- Open-Source Availability: Freely accessible and benefits from community-driven development and support.
- Comprehensive Detection Capabilities: Supports both active and passive detection methods, offering a thorough approach to identifying network services and configurations.
Cons:
- Steep Learning Curve: Advanced features and command-line interface may be challenging for beginners, requiring a solid understanding of networking concepts.
- Limited User Interface: Lacks a graphical user interface, which may deter users who prefer visual tools for network scanning tasks.
- Infrequent Updates: The tool has seen limited updates in recent years, potentially affecting compatibility with newer systems and lacking some modern features.
9. Pentest-Tools

Pentest Tools is a website where you can scan ports of external IP addresses. You can think of it as an online “done for you” version of Nmap. Simply put in the external IP address you wish to scan and click scan. The light version is free, which only shares the top 100 ports and shares the hostname as well as the IP address and service version the device is running.
Key Features:
- Comprehensive Vulnerability Assessment: Offers a suite of tools to identify vulnerabilities in websites and network infrastructures, providing detailed reports and remediation recommendations.
- Attack Surface Mapping: Automatically maps the attack surface, helping security teams understand potential entry points for attackers.
- Internal Network and VPN Scanning: Supports scanning of internal networks and VPNs to detect vulnerabilities within the organization’s perimeter.
- Scan Scheduling and Automation: Allows users to schedule scans and automate testing processes, ensuring regular assessments without manual intervention.
- API Access and Integration: Provides API access for integration with other security tools and workflows, enhancing the efficiency of security operations.
Why do we recommend it?
Pentest-Tools serves as a convenient online platform for users looking to perform port scans on external IP addresses without the need for extensive technical knowledge. Comparable to an “online done-for-you” version of Nmap, Pentest-Tools simplifies the scanning process. Users can input the external IP address they want to scan and initiate the process with a click. The light version, available for free, offers insights into the top 100 ports, along with the hostname, IP address, and service version of the target device.
For access to the direct operating system, all 65535 port scan results, and a full traceroute, you’ll need to pay. Plans are broken up into four tiers and start at $65.00 per month. Considering Nmap is a free tool, I don’t think this service is worth it among technical professionals but could be useful for someone who is not as tech-savvy but still needs the results of an in-depth port scan.
Below is the output from a “light” scan with the Pentest Tools site:
Starting Nmap ( https://nmap.org ) at 2021-02-23 21:40 EET
NSE: Loaded 40 scripts for scanning.
Initiating Ping Scan at 21:40
Scanning XX.XXX.XXX.XXX [4 ports]
Completed Ping Scan at 21:40, 0.23s elapsed (1 total hosts)
Initiating SYN Stealth Scan at 21:40
Scanning ec2-XX-XX-XX-XX.compute-1.amazonaws.com (XX.XXX.XXX.XXX) [100 ports]
Discovered open port 443/tcp on XX-XX-XX-XX
Discovered open port 80/tcp on XX-XX-XX-XX
Increasing send delay for XX-XX-XX-XX from 0 to 5 due to 11 out of 15 dropped probes since last increase.
Completed SYN Stealth Scan at 21:40, 22.63s elapsed (100 total ports)
Initiating Service scan at 21:40
Who is it recommended for?
Pentest-Tools is recommended for individuals who may not possess advanced technical skills but still require the results of a thorough port scan. This online platform offers a user-friendly interface for users seeking a quick and easy way to perform port scans on external IP addresses. While technical professionals might prefer free alternatives like Nmap, Pentest-Tools could be particularly useful for those who value simplicity and convenience. For users requiring more advanced features, such as access to full port scan results and a comprehensive traceroute, subscription plans starting at $65.00 per month are available.
Pros:
- User-Friendly Interface: Designed to be accessible for users with varying levels of cybersecurity experience, facilitating ease of use.
- Centralized Vulnerability Management: Combines multiple scanning capabilities into a single platform, allowing for streamlined vulnerability management processes.
- Detailed Reporting: Generates comprehensive reports with clear explanations of findings and actionable remediation steps, aiding in effective vulnerability management.
- Responsive Customer Support: Offers prompt and helpful support, assisting users in resolving issues and optimizing the tool’s usage.
Cons:
- Limited Advanced Features: May lack some advanced functionalities found in other penetration testing tools, potentially requiring supplementary tools for comprehensive assessments.
- Pricing Considerations: The cost may be a factor for small businesses or individual practitioners when compared to other tools in the market.
10. IP Fingerprints

IP Fingerprints is another online tool that allows you to scan remote IP addresses through a few simple clicks. What’s nice about this tool is that it is entirely free and allows you to choose which ports or port ranges you want to scan. For more in-depth scanning you can switch to the Advanced tab and toggle between different types of scanning filters.
Key Features:
- Network Port Checker: Provides a Network Port Checker tool that allows users to input an IP address and a range of ports to check, helping identify open ports and assess network security.
- IP Geolocation: Offers IP geolocation services, enabling users to determine the physical location associated with a specific IP address, which can be useful for various analytical purposes.
- Traceroute Tool: Includes a traceroute feature that maps the path data packets take from the user’s device to a target IP address, assisting in diagnosing network connectivity issues.
- Ping Utility: Provides a ping utility to test the reachability of a host on an IP network, measuring round-trip time for messages sent to the destination.
- WHOIS Lookup: Users can perform WHOIS lookups to retrieve registration details of domain names or IP addresses, offering insights into ownership and administrative contacts.
Why do we recommend it?
IP Fingerprints stands out as a valuable online tool for port scanning remote IP addresses with ease and simplicity. This tool offers a user-friendly interface that allows users to initiate scans through a few straightforward clicks. Notably, IP Fingerprints is entirely free, providing an accessible option for users seeking basic port scanning functionality. One of its notable features is the ability to customize scans by selecting specific ports or port ranges. Additionally, the Advanced tab offers more in-depth scanning options, allowing users to choose from various scan types such as SYN stealth, NULL stealth, FIN stealth, XMAS, ACK, and Window scans. The tool also provides flexibility in ping types, including TCP, ICMP, or both, along with options for OS detection and the use of fragmented packets to evade firewall detection.
For instance, you can choose between scan-type methods, and sort through SYN stealth, NULL stealth, FIN stealth, XMAS, ACK, and Window scans. If you want to use ping instead you can choose between TCP, ICMP, or both for your ping type. There are a few general options that can be turned on for more details, such as OS detection and the ability to use fragmented packets to avoid firewall detection.
While this tool can take a long time depending on how large your port range is, it’s an excellent online alternative for port scanning with plenty of customization options that are usually only reserved for tools like Nmap or Unicornscan.
Below are the results from a port scan I ran checking ports 80-5000. It took roughly 10 minutes to complete.
Host is up (0.095s latency). Not shown: 911 closed ports PORT STATE SERVICE 80/tcp open http 111/tcp filtered rpcbind 135/tcp filtered msrpc 136/tcp filtered profile 137/tcp filtered netbios-ns 138/tcp filtered netbios-dgm 139/tcp filtered netbios-ssn 445/tcp filtered microsoft-ds 513/tcp filtered login 520/tcp filtered efs
Who is it recommended for?
IP Fingerprints is recommended for users who prioritize simplicity and customization in an online port scanning tool. This tool is suitable for individuals looking for a free and accessible solution for scanning remote IP addresses. While the scanning process may take time depending on the port range, IP Fingerprints serves as an excellent online alternative, offering customization options typically found in more advanced tools like Nmap or Unicornscan. Whether users are new to port scanning or seek a straightforward online tool with customization capabilities, IP Fingerprints is a valuable choice.
Pros:
- User-Friendly Interface: Designed with an intuitive interface, making it accessible for users with varying levels of technical expertise.
- Comprehensive Toolset: By offering a variety of network diagnostic tools in one place, IP Fingerprints allows users to perform multiple tasks without needing to switch between different services.
- Free Access: Many of the tools provided by IP Fingerprints are available for free, making it a cost-effective solution for individuals and small businesses.
- No Installation Required: As a web-based service, users can access the tools directly through a browser without the need for software installation, providing convenience and ease of use.
Cons:
- Limited Advanced Features: While suitable for basic network diagnostics, IP Fingerprints may lack some advanced functionalities required by professional network administrators or security analysts.
- Performance Variability: As an online service, the performance of the tools can be affected by internet connectivity and server response times, potentially leading to delays in obtaining results.
- No Customer Support: The platform does not offer dedicated customer support, which may be a drawback for users requiring assistance or encountering issues.
Which port scanner tool is right for you?
While we’ve narrowed it down to the best port scanner tools, you may be wondering which one is best for you. SolarWinds Port Scanner is going to provide the best general overall port scanning for most sysadmins and general technicians. Its ease of use and quick installation secure its place at number one.
For those who want to dive deep into port scanning for cybersecurity research and penetration testing, Nmap is a tried-and-true professional port scanning tool that has been in use since the early 1990s. For those who are looking for an alternative to Nmap, I’d highly recommend Unicornscan for similar functionality with more unique scanning features.
Do you have a favorite port scanner? If so, let us know about it in the comments below.