Data Loss Prevention (DLP) tools are used by businesses to track and audit company files and prevent users from stealing or intentionally deleting data.
DLP tools are designed to protect your proprietary data, see who accessed certain files, and avoid downtime when trying to replace what went missing.
Here’s our list of the best data loss prevention tools:
- ThreatLocker EDITOR’S CHOICE An enterprise-level data loss prevention tool that uses granular policies to block USB and other removable devices from accessing your sensitive data. Start a 30-day free trial.
- Endpoint Protector (GET DEMO) A cloud-based service that supervises data movements on Windows, macOS, and Linux devices and also printers. Also available as a virtual appliance. Access a free demo.
- Guardz (FREE TRIAL) This security package is delivered from the cloud and it blocks intruders and malware from stealing or damaging data. Get a 14-day free trial.
- ManageEngine Endpoint DLP Plus (FREE TRIAL) A package of data protection features that includes sensitive data discovery and data movement controls. Installs on Windows Server. Get a 30-day free trial.
- ManageEngine DataSecurity Plus (FREE TRIAL) A comprehensive data leak prevention and security monitoring tool that safeguards your sensitive data from leaks or losses through endpoints. Start a 30-day free trial.
- SolarWinds Access Rights Manager An intuitive and easy way for sysadmins to protect their data and build custom rules based on policies and past behavior or incidents.
- Code42 Cloud-based data protection with long term data retention.
- Teramind DLP solutions with granular user-based analytics and productivity reports.
- Broadcom Symantec Data Loss Prevention In-depth data discovery and customizable data policies.
- Forcepoint Uses real-time user behavior to assign risk scores and prevent data loss based on changing rulesets.
The best data loss prevention tools
1. ThreatLocker (FREE TRIAL)
ThreatLocker is a powerful cybersecurity solution that streamlines storage control and access to your resources and data. It provides administrators with comprehensive control and enables them to create policies that streamline access.
Why Do We Recommend It?
We highly recommend ThreatLocker for its granular and policy-driven access controls. Using this tool, administrators can set policies for USBs to access only certain locations and file types. Also, they can set the time limit, limit USB access by devices, allow multiple accesses, and more. Such granularity provides complete visibility and control over data access.
Another important aspect is logging. ThreatLocker logs every activity and access, so you can know which user has accessed which file and when. A highlight is that you can use filters to search through the data and find exactly what you need.
Typically, when users need to access a file through USB, they have to request permission from the administrator. Based on the details, the administrator can grant or deny access. All this can be done in real-time, less than 60 seconds at the most, to avoid business disruptions.
Its intuitive user interface and support for multiple environments are other reasons why we recommend this tool.
Who is it recommended for?
It is recommended for organizations of all sizes, especially those that have stringent compliance requirements or need to stay on top of their security. It is also useful for organizations in which employees routinely access system resources through USBs and other external devices.
Get registered for the 30-day free trial.
EDITOR'S CHOICE
ThreatLocker is our editor’s choice for the best data loss prevention tool because of its comprehensive features and granular access policies. Administrators can customize the policies for specific use cases, devices, or even users to restrict access. They can even implement group policies for environments that need fine granularity instead of a simple on/off USB management. Administrators can even test these policies in a learning mode before implementing them in live system to reduce false positives. With such advanced features, ThreatLocker is undoubtedly the top choice for data loss prevention.
Download: 30-day FREE Trial
Official Site: https://www.threatlocker.com/try-threatlocker
OS: Cloud-based SaaS
2. Endpoint Protector (GET DEMO)
Endpoint Protector by CoSoSys is a cloud-based service that offers a range of system protection and monitoring services that revolve around the needs of data loss prevention. Categories of DLP that this system can disrupt include insider threats and intruder attempts on personally identifiable information (PII).
Why do we recommend it?
Endpoint Protector earns our recommendation as a top-tier data loss prevention (DLP) solution, backed by our thorough testing and exploration. The cloud-based service excels in mitigating insider threats and thwarting intruder attempts on personally identifiable information (PII). During our hands-on evaluation, we were impressed by its seamless support for Windows, macOS, and Linux devices, providing a comprehensive shield against data breaches. Notably, Endpoint Protector’s robust compliance with data privacy standards like PCI DSS, GDPR, and HIPAA underscores its suitability for businesses navigating stringent regulatory landscapes.
The capabilities of this service will protect data stored on Windows, macOS, and Linux devices. It is also able to monitor access to data passing to and through printers. Endpoint Protector is suitable for businesses that are following the PCI DSS, GDPR, and HIPAA data privacy standards. The service was designed with routines that comply with these standards.
The procedures and standards of Endpoint Protector can easily be adapted through a guided settings management section of the system dashboard. You set policies for file monitoring that can be applied to specific departments or user groups. This means that you can have different data usage allowances operating simultaneously. It is also possible to vary procedures according to the sensitivity rating of data stores.
The Endpoint Protector package includes USB and peripheral management. You can choose to block all device attachments, limit the files that can be transferred, or just record all file movements onto memory sticks.
The ability to fine-tune the data loss prevention system is ideal for the current need to allow remote access by home-based staff. As it is based in the cloud, Endpoint Protector is not enclosed by one single LAN but can easily cope with virtual offices. The service includes an endpoint agent module. This continues monitoring and control tasks when the device is offline.
Who is it recommended for?
Our recommendation for Endpoint Protector is tailored to businesses seeking a versatile and secure DLP solution that transcends traditional boundaries. In our testing, we delved into its user-friendly dashboard, where we effortlessly fine-tuned DLP procedures and set policies based on user groups or departments. The service’s adaptability, allowing organizations to manage USB and peripheral devices, proved to be a valuable asset. Our testing process ensures that this recommendation is grounded in practical insights derived from extensive use of the tool.
You can take out a subscription to Endpoint Protector as a service on the AWS, Azure, and GCP systems. Endpoint Protector also offers a SaaS version and you can get the software for installation on your site as a virtual appliance. There isn’t a free version of Endpoint Protector or a free trial. However, you can request access to a demo system.
3. Guardz (FREE TRIAL)
Guardz is a cloud platform of security monitoring services. It implements the protection of data by scanning endpoints and cloud data accounts and it also works on preventing outsiders and malware from getting system access by monitoring incoming emails.
Intruders get access by stealing account credentials and the most common technique used for credentials theft is the phishing email. The Guardz package is very strong on phishing prevention and it also blocks spam, impersonation attempts, and malware disguised in email attachments.
The email scanner operates as a plug-in for Microsoft Exchange Server/Outlook and Google’s Gmail. These two email services are part of Microsoft 365 and Google Workspace. Guardz also scans the cloud file stored included in those packages: OneDrive and Google Drive.
Buyers of the Guardz platform might be acting a little too late and it is possible that they have already experienced a data breach, including email credentials theft. The package includes a Dark Web scanner that looks on hacker forums for the identities of subscribing companies, particularly email addresses or credentials. The Guardz scanner will raise an alert in the management console if stolen data is encountered.
Another anti-phishing feature in the Guardz package is its phishing simulator. This can be useful for testing the Guardz phishing detector and, if you turn that feature off temporarily, you can use it to train and test user phishing identification abilities.
The phishing detection skills of employees can be sharpened by giving them an awareness training course. The Guardz platform offers a library of course for no extra charge. These courses are supplied as a series of videos and progress through the course will be recorded and shown in the management console.
Endpoints are constantly scanned for signs of malicious activity. This could be in the form of manual actions or the automated moves of malware. The system identifies anomalous behavior, which could indicate an account takeover. It also looks for spyware, keyloggers, adware, viruses, Trojans, ransomware, and fileless malware.
This Guardz platform is a subscription service offered in two plan levels. These are priced per user per month and there is no minimum team size, so even the smallest business can access this system.
Guardz specifies that its platform should be administrated by a managed service provider (MSP). However, there is a third plan available on the platform that is itself a managed security service and that is a good solution for companies that don’t have an agreement with an MSP in place. You can assess the Guardz package with a 14-day free trial.
4. ManageEngine Endpoint DLP Plus (FREE TRIAL)
ManageEngine Endpoint DLP Plus is an on-premises package but it doesn’t need to be installed on every endpoint. The software runs on one host and monitors all other endpoints over the network. It is also possible to extend the system over a WAN to monitor data on multiple sites.
Why do we recommend it?
Noteworthy is ManageEngine Endpoint DLP Plus‘s unique architecture, residing on a single host yet efficiently monitoring endpoints across the network, eliminating the need for individual installations. During our evaluation, the system’s adaptability stood out, allowing the extension of monitoring capabilities over wide-area networks (WAN) to oversee data on multiple sites seamlessly. The complexity of configuring DLP routines is simplified through the platform’s extensive library of templates, aligning security policies with specific data protection standards. A standout feature is the tool’s capacity to identify and categorize sensitive data using OCR scanning and fingerprinting, offering a granular approach to data management.
The routines of the DLP are adjusted by the security policies that you set up in the system. This would be a complicated process, were it not for the library of templates offered by the Endpoint DLP Plus dashboard. These adjust all settings to accord with specific data security standards. One of the most important specifications is the definition of “sensitive” data.
Once the DLP service has been set up, the ManageEngine service scours all of the endpoints on your network, looking for sensitive data. The tool includes OCR scanning of document images and it also performs “fingerprinting” which can detect groups of fields that represent personally identifiable information when viewed together.
The system categorizes all of the sensitive data that it discovers. This enables different types of data to be managed according to type and specifically, which users should be permitted access to them. The service tracks and logs user access to each instance of data.
The movement of data is examined through USB device control, email scanning, and monitoring of transfers to and from cloud platforms.
It is possible to identify the applications that generate and process sensitive data and the system will protect these, preventing data exchanges to unauthorized software. Data sent to user-owned devices is guarded with containerization, which prevents it from being accessed through the device’s operating system and blocks storage on those systems.
Who is it recommended for?
Our recommendation for ManageEngine Endpoint DLP Plus is directed at organizations and IT administrators seeking a robust on-premises DLP solution with a focus on simplified yet effective endpoint monitoring. Through our hands-on exploration, we found the dashboard’s template library particularly beneficial, streamlining the setup of security policies and ensuring compliance with data security standards. The platform’s ability to categorize sensitive data and manage user access based on types of data adds a layer of sophistication suitable for environments handling diverse information types. Notably, the tool’s scrutiny of data movements, including USB device control, email scanning, and cloud platform transfers, positions it as an ideal choice for those prioritizing comprehensive data loss prevention. The availability of both Free and Professional editions, with the former supporting up to 25 endpoints, caters to varying organizational sizes and requirements.
The software for ManageEngine Endpoint DLP Plus installs on Windows Server. It is available in two editions: Free and Professional. The Free plan is limited to monitoring 25 endpoints. The paid system is available for assessment with a 30-day free trial.
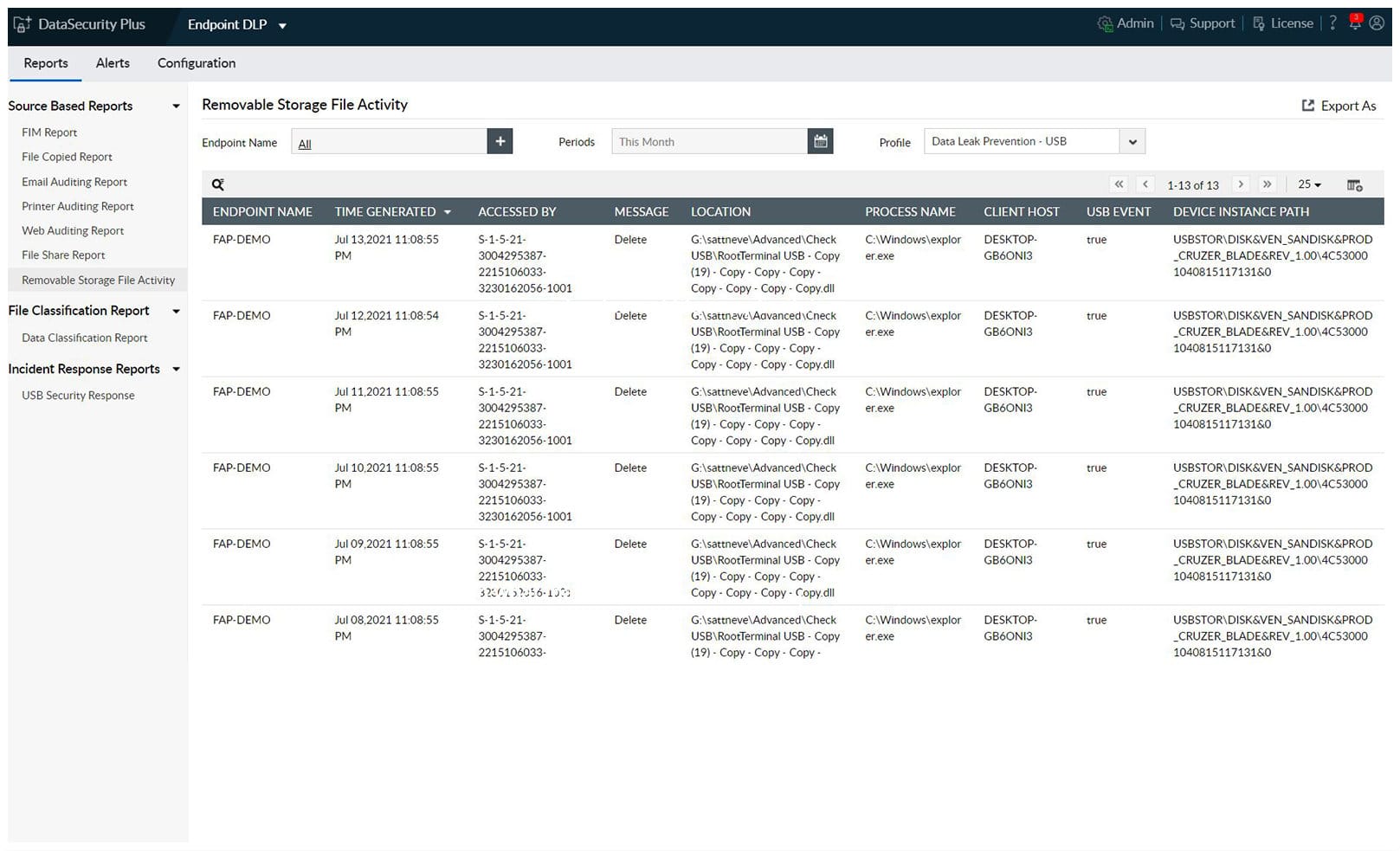
5. ManageEngine Data Security Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is an advanced DLP tool that can safeguard your sensitive data from potential leaks through endpoints. It also generates a list of external devices that connect to your network and audits them for vulnerabilities.
Why do we recommend it?
We recommend this tool because of its comprehensive approach to DLP. It starts with auditing the list of external tools that connect to your network and ensuring that they do not belong to blocked lists. After checking the security of the device, this tool also offers only read-only access to suspicious devices.
When it comes to file sharing, this tool prevents high-risk files from getting copied to external devices. It also spots abnormal user behavior and flags them for further evaluation.
Another aspect we love about this tool is its automated incident response. It comes with predefined remediation options to quickly resolve critical security incidents. It can also identify ransomware attacks by quickly isolating the ransomware-infected endpoints, thereby preventing the lateral spread.
Its advanced reports and intuitive dashboards are other reasons why we recommend this tool.
Who is it recommended for?
It is recommended for network engineers and MSPs who are responsible for maintaining the security of their environment and the integrity of sensitive data. It is a good choice for compliance teams and security professionals as well. Start a 30-day free trial.
6. SolarWinds Access Rights Manager

SolarWinds Access Rights Manager was built specifically for system administrators who need to track which users are accessing certain files and comply with regulatory requirements such as GDPR, HIPAA, and PCI-DSS.
Why do we recommend it?
Access Rights Manager from SolarWinds stands out as a robust solution in the realm of access management, and our recommendation is rooted in the comprehensive testing and exploration we conducted. Tailored for system administrators, it seamlessly facilitates user tracking and ensures compliance with regulatory frameworks such as GDPR, HIPAA, and PCI-DSS. During our hands-on evaluation, the platform’s intuitive file structure design emerged as a standout feature, empowering administrators to swiftly visualize, modify, and manage file permissions. The graphical interface, particularly the insightful flow chart representation of inherited permissions, enhances the overall user experience and simplifies the identification of potentially malicious activities. SolarWinds Access Rights Manager’s versatility and ability to automate documentation across various servers make it an ideal choice for organizations prioritizing data protection and user auditing.
Through an intuitive file structure design, you can quickly see a file or folder’s permission and change it on the fly. Under the Permissions tab, you can sort by mapped drive, folder structure, or even individual user to see exactly what permissions each object has.
Under the graph section, you’ll get a comprehensive view of all inherited permissions linking to a specific object in a flow chart form. This makes it simple to visually see permissions and eliminates the need to manually check access rights manually through Active Directory.
The graphical interface makes it easy to see how a user’s credentials are being used and if any permissions had been changed. This feature allows you to quickly spot potentially malicious behavior and shut it down before it becomes a problem.
The Home screen makes it easy to navigate the Access Rights Manager and accomplish what you need. Menus and functions are grouped around what you want to achieve and make getting to where you need to go simple.
You can set up security alerts to be sent to you, or your IT team to investigate suspicious activity such as unauthorized access or privilege escalation. The built-in auditing tools help you establish a baseline of accessible access and help your form and support a data forensic timeline.
You can configure Access Rights Manager to automatically document actions from Sharepoint, Exchange, Microsoft Dynamics, or any of your Windows-based servers. These actions can be compiled into audit-ready reports, or accessed from a logbook view to breakdown files access by time and date.
Templates make assigning or removing the proper permissions easy across multiple servers and file systems. In a few clicks, you can remove or assign permissions to dozens of objects for an individual user or group using Access Rights Manager.
Who is it recommended for?
Our recommendation for SolarWinds Access Rights Manager is targeted at system administrators and organizations with a paramount focus on securing sensitive data and adhering to regulatory standards. Through our testing, we found that the platform’s user-friendly Home screen, coupled with logically grouped menus, facilitates seamless navigation and quick accomplishment of tasks. The ability to configure security alerts and leverage built-in auditing tools enhances the tool’s suitability for those aiming to establish a robust baseline of access activities and respond promptly to potential security threats. This recommendation is grounded in our thorough evaluation, ensuring that it aligns with the practical needs and preferences of administrators dealing with access rights and permissions.
If protecting your data and auditing your users is a priority for your organization, Access Rights Manager is one of the most intuitive and feature-rich tools to accomplish just that. You can test out all of the Access Rights Manager’s features for free on a 30-day free trial.
7. Code42

Code42 is a cloud-native DLP tool that focuses heavily on protecting data while not interfering with user productivity. The system automatically collects all files from multiple endpoints such as servers, PCs, and laptops and securely stores every version of them in the Code42 cloud.
Why do we recommend it?
Code42 stands out for its cloud-native approach to Data Loss Prevention (DLP), prioritizing data protection without compromising user productivity. Our testing revealed its seamless collection and secure storage of file versions from diverse endpoints, ensuring comprehensive and real-time data restoration capabilities. The ability to monitor, audit, and detect modifications, movements, or deletions of data, even on offline endpoints, contributes to its robust DLP functionality. Code42’s risk analysis system, automatic detection of file movements, and configurable risk mitigation for specific files enhance its efficacy in identifying and addressing potential data breaches.
Any modifications to data are indexed and updated as they are changed in realtime. Every file version is saved for long term data restoration. This ability to roll back and recover missing or modified files is a key function of Code42.
The second aspect of Code42 is data monitoring and auditing. Administrators can easily see what data was changed, moved, or deleted. You can view reports or get alerts for specific actions such as media being copied to a flash drive, or file permission changes. Audits and investigations can take place even when the endpoint in question is offline.
Code42 gives you the option to be alerted to risky activity and can help you identify potential data breaches or risks. You can sort activity by file movement to gain visibility to see where your data is moving.
You can automatically detect when your files are being copied off the network, on to removable media, or added to a file upload service. Code42’s risk analysis system automatically prioritizes users who need further investigation based on their actions.
When configuring Code42 you can prioritize specific files or folders to mitigate risk against data loss. Within the data protection dashboard, Code42 will automatically highlight your risk exposure to certain assets based on file type and its access history. This makes adjusting access and finding internal threats a simple and quick process.
Who is it recommended for?
Our recommendation for Code42 is tailored to organizations seeking a user-friendly yet powerful cloud-native DLP solution. This tool is ideal for businesses prioritizing comprehensive data protection without hindering user workflows. Code42’s risk analysis capabilities make it suitable for enterprises aiming to proactively identify and investigate potential data breaches or risks. Additionally, the platform’s configurable risk mitigation and insightful data protection dashboard simplify the process of adjusting access controls and swiftly addressing internal threats.
You can test Code42 free for 60 days when you sign up for a trial.
8. Teramind DLP

Teramind is a user monitoring and data loss prevention tool that can be configured both via the cloud or housed on-premises. Like Access Rights Manager you can view and customize permissions to specific resources on your network based on user, folder, or group.
Why do we recommend it?
Teramind DLP stands out as a robust user monitoring and data loss prevention tool, offering both cloud and on-premises configurations. During our testing, the tool’s Enterprise Dashboard provided a comprehensive top-down view of user activities, with detailed security metrics highlighting risks and data movements. Teramind’s granular insights, including specific commands executed by users, proved invaluable in identifying insider threats and potential malware activities. The ability to configure rules for blocking, reporting, or warning users against policy violations, such as data transfer to external drives, adds a layer of proactive security. The platform’s flexibility to create custom rules and compliance-based rules, such as PCI-DSS detection, enhances its adaptability to diverse security needs.
There are two distinct dashboards that break down Teramind’s findings, the Enterprise Dashboard and the Focus Dashboard. In the Enterprise Dashboard, you get a top-down overview of users that are online, their daily activity, and what files they accessed.
You’ll also see company level security metrics graphed out showing any risks that were detected as well as any data that had left the network. Next to security metrics are productivity metrics which chart work times verse idle time and break down productivity based on groups, machine, or individual.
Teramind can get very granular and even see what specific commands users have executed on their machines. These types of insights are vital at identifying insider threats and malware that could be looking for ways to navigate throughout your network. You can configure rules to either completely block specific actions, report actions, or send a message to the user that what they are attempting to do is against company policy.
For example, if certain data is to not leave the network and Teramind detects a user is attempting to move it to a flash drive, you can configure a rule to block that action from happening and send a message to the user warning them against that action.
You’ll have plenty of details based on user behavior to build out your own rules and alerts around what you’re looking for. For example, creating alert templates around specific clipboard monitoring actions, commands run on a machine, or search history can help you highlight a disgruntled employee and stop an insider threat before any real damage is done.
While you can configure your own rules there are compliance-based rules built in such as PCI-DSS detection, PHI data detection, and other common rules you can enable out of the box to immediately start checking for user compliance.
If you want to get granular in your user’s online behavior and are interested in productivity metrics as well as data protection then Teramind might be the DLP solution you’re looking for.
Who is it recommended for?
Our recommendation for Teramind DLP is tailored to organizations seeking a versatile solution for user behavior monitoring and data loss prevention. The tool is ideal for those interested in in-depth productivity metrics alongside robust data protection features. Teramind’s granular insights and configurable rules make it a valuable choice for businesses aiming to proactively identify and address insider threats, ensuring security against potential data breaches. The platform’s compliance-based rules, including PCI-DSS and PHI data detection, make it suitable for organizations requiring immediate checks for user compliance.
Teramind DLP starts at $150.00 (£121.55) per month for 10 endpoints and is available for a free trial.
9. Broadcom Symantec Data Loss Prevention

Broadcom Symantec DLP combines data endpoint scanning that actively monitors user behavior and file access to assess risk and automatically take corrective action. Similar to Code42, Symantec DLP works by deploying endpoint agents that scan company machines for specific data to identify those who have the highest risk of data loss, or discover who has access to files they’re not authorized to.
Why do we recommend it?
Broadcom Symantec DLP is a comprehensive data loss prevention solution that employs active endpoint scanning and user behavior monitoring to assess and mitigate data loss risks. During our testing, the DLP solution, comprising Endpoint Discover and Endpoint Prevent, demonstrated efficient identification of data storage, versions, and unauthorized access. The use of three detection technologies—description-based scanning, fingerprinting, and learning metrics—enhances the system’s capability to find, match, and track files across the network. Symantec’s granular control over data copying, restriction of specific data to various media, and Trusted Device Support for whitelisting specific media provide organizations with versatile and robust data protection options.
The DLP solution is broken down into two parts, DLP Endpoint Discover, and DLP Endpoint Prevent. Together these agents work on actively identifying where data is stored, how many versions there are, and if those machines or users are allowed access to that data.
DLP Endpoint Discover utilized three points of detection technology to find, match, and track files across a network. Description based scanning looks for matching keyphrases, patterns, or expressions as well as other signature-based forms of detection.
Fingerprinting looks for partial or exact matches of files coming from structured sources or databases. In the meantime, the Learning metric builds an understanding of unstructured data such as intellectual property, source code, and company secrets. The agent can then build an understanding of how this data is accessed and provide you with recommendations and a report ready overview of how some of your company’s most sensitive files are being accessed.
Like most DPL solutions you can restrict specific data to be copied to other forms of media such as flash drive, cell phone, CD, or DVD. However, with Symantec DLP you have even more granular control and can white list specific forms of media through Trusted Device Support. This enables organizations to define certain media that can be used with confidential or restricted data within the company.
Symantec takes an analytic approach to DLP and does a great job at providing an actionable discovery process and giving sysadmins the tools they need to lock down data and provide company-wide compliance.
Who is it recommended for?
Our recommendation for Broadcom Symantec DLP is targeted at organizations seeking a robust and analytic data loss prevention solution. Ideal for businesses prioritizing active endpoint scanning and user behavior monitoring, this DLP tool proves effective in identifying, tracking, and securing sensitive data across the network. The platform’s granular control options, including white-listing specific media, make it suitable for organizations with diverse data protection needs. Symantec DLP is well-suited for businesses aiming to enforce company-wide compliance, providing system administrators with the tools needed for effective data lockdown and risk mitigation.
10. Forcepoint DLP
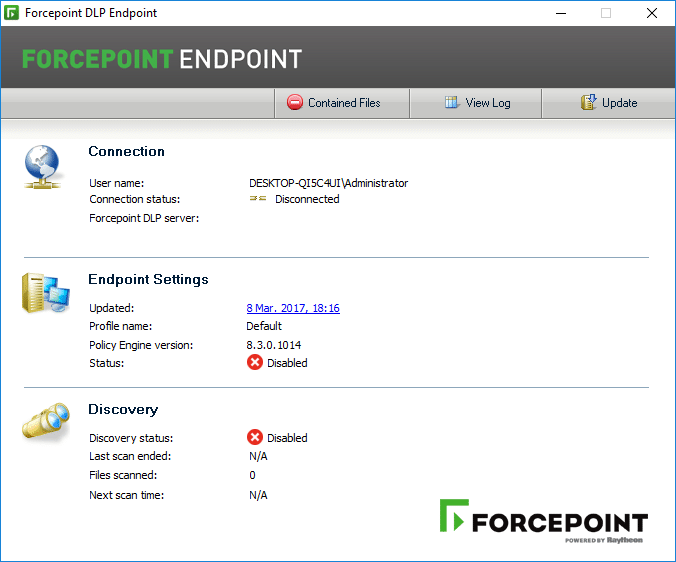
Forcepoint DLP is an agent-based data discovery and loss prevention SaaS solution aimed to keep data secure, and compliance requirements met. Forcepoint utilizes user behavior metrics to map out and identify rogue or malicious actions and stop them before data is compromised.
Why do we recommend it?
Forcepoint DLP stands out as an effective agent-based data discovery and loss prevention SaaS solution, designed to ensure data security and compliance. During our testing, Forcepoint’s emphasis on user behavior metrics demonstrated its ability to map and identify potential threats, preventing data compromise in real-time. Notably, the platform excels in reducing false positives by combining standard rules with adaptive learning technology, distinguishing between accidental actions and actual breaches. The granular control over data sharing, coupled with rule sets based on user, content, location, and method, offers organizations versatile and precise control over their data security.
Forcepoint focuses heavily on sorting data and identifying real threats to reduce the number of false positives that are reported by so many of DLP solutions. Forcepoint combines standard rules with technology that learns over time to understand the difference between a data breach, and an employee who might have mistakenly moved a file somewhere they shouldn’t have.
This looks at the types of data and patterns that users have used in the past and compares them to the realtime actions they are taking now. This same system can also highlight data breaches and identify hijacked accounts or malicious data-stealing software.
You’ll have granular control over not just your data, but exactly how it’s shared and with whom. Much like networking firewalls you can create rule sets based around the Who, What, Where, and How your data is moving across the network, and then assign a specific action to that exact scenario.
For example, if the system detects that Human Resources is sending personal data to another business partner via email, you can create a rule that automatically encrypts that email. If that same data is moved to Dropbox or a file transfer service, you could configure Forcepoint to block that action and warn the end-user.
Each user can be assigned a risk score based on their current and past actions. The higher the score the more likely it is that the account is a risk to data. For each file or area of your network, you can assign threat thresholds to lock out users or restrict access to your network based on the risk factors.
Who is it recommended for?
Our recommendation for Forcepoint DLP is directed at organizations seeking a robust SaaS solution for data discovery and loss prevention. Ideal for businesses prioritizing the reduction of false positives, this DLP tool effectively leverages user behavior metrics to identify and thwart potential threats. Forcepoint’s adaptive learning technology, which analyzes past actions to differentiate between breaches and unintentional activities, makes it suitable for organizations focusing on accurate threat detection. The platform’s granular control options, including rule sets based on various parameters, cater to businesses wanting precise control over data sharing and movement. Forcepoint DLP is well-suited for organizations aiming to maintain data security, ensure compliance, and assign risk scores to users based on their actions.
If you’re interested in Forcepoint DLP you can request a free trial at Forcepoint’s office site.
Choosing a DLP tool
No matter what software you choose it’s critical to have a DLP system in place to keep your companies IP protected and your data secure from theft or deletion.
For most corporate environments SolarWinds Access Rights Manager will provide you the protection and tools your company needs to secure data, change access rights, and monitor real-time data access without impeding productivity or working through a steep learning curve.
For organizations more focused on their users’ behavior and productivity insights, Teramind DLP combines detailed reporting down to the specific user and can highlight internal threats while also alerting and preventing data loss through behavior risk analysis.
Lastly, if you’re looking for a solution that can both control access to your data, and provide quick file recovery, Code42’s long term file retention can restore missing or delete files in a few clicks.
Does your organization have a data loss prevention tool in place? Let us know in the comments below.