Microsoft’s Security Analyzer was once a decent tool that administrators could use to scan their systems and check for basic best practice settings. Since being discontinued, there’s been a hole that some admins are still looking to fill with a reliable security tool. If you’re looking for a replacement, check out our list of the top Microsoft Baseline Security Analyzer alternatives.
Here is our list of the best Microsoft Baseline Security Analyzer alternatives:
- ManageEngine Vulnerability Manager Plus EDITOR’S CHOICE This package provides vulnerability scanning and then helps fix discord problems with tools that include a patch manager. Available for Windows Server. Start a 30-day free trial.
- Site24x7 (FREE TRIAL) A cloud-based network monitoring tool that continuously gathers metrics from different devices and analyzes them against established metrics. In the event of deviations, it sends alerts to help you quickly resolve the issue. Sign up for a 30-dayfree trial.
- Paessler PRTG Network Monitor (FREE TRIAL) Provides flexibility with sensors designed to scan any port or protocol. Start a 30-day free trial.
- SolarWinds Network Security Tools with Engineer’s Toolset An excellent set of tools designed specifically for network administrators and MSPs. The security tools in this bundle cover patching, network security, and real-time monitoring.
- Intruder A cloud-based network scanner whose goal is to make security simple and hands-off.
- OpenVAS. A powerful open-source scanner that’s backed by a large, active community.
- Nexpose. Offers quality network scanning, with full integration for the Metasploit framework.
The Best Microsoft Baseline Security Analyzer Alternatives
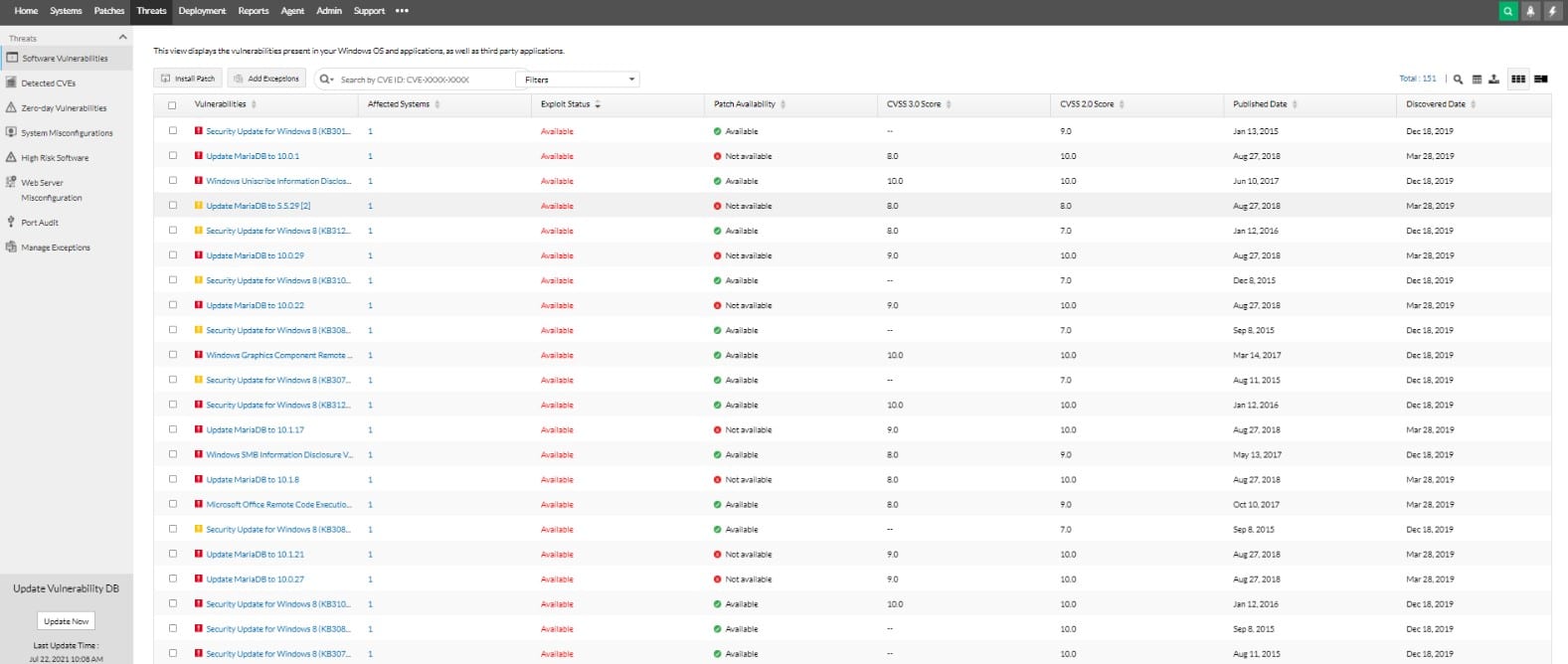
1. ManageEngine Vulnerability Manager Plus (FREE TRIAL)
ManageEngine Vulnerability Manager Plus is an on-premises package that will watch over devices running Windows, Linux, and macOS. The tool starts off by tracking all of the endpoints connected to your network and logging them in an inventory. That inventory discovery cycle continues repeatedly so all new devices get included in the list automatically. The service then scans each device for vulnerabilities.
Key Features:
- Vulnerability scanning
- Asset discovery
- Patch management
- Compliance reporting
- Spots misconfigurations
Why do we recommend it?
ManageEngine Vulnerability Manager Plus stands out as a robust on-premises solution designed for overseeing the security posture of devices running Windows, Linux, and macOS. Its comprehensive set of features includes vulnerability scanning, asset discovery, patch management, compliance reporting, and identification of misconfigurations. Notably, the tool goes beyond mere detection by actively assisting in system updates, addressing security weaknesses stemming from outdated software and device settings. The automation capabilities, from discovering hardware and software to applying patches, make it a powerful ally for organizations aiming to maintain a secure and compliant environment.
As well as detecting security issues, ManageEngine Vulnerability Manager Plus helps you update your system to shut down the weaknesses that it discovers. The main causes of security loopholes lie with device settings that provide opportunities for hackers to get into your system and move around undetected and also out-of-date software.
The vulnerability scans identify high-risk software and also encourage you to create a manifest of authorized software. With that series of profiles in place, you can better manage onboarding and the vulnerability scanner will keep a lookout for unauthorized software packages installed by users or infiltrated by malware.
System hardening strategies include recommendations for configuration changes and tips on how to block types of activities that could present a threat. The package also includes a patch manager that will automatically seek out the current updates for all of the software that your endpoints are running.
The patch manager should be set up with a calendar that provides maintenance windows. With that in place, the tool will start applying patches automatically at the next available window. This service is able to identify patch dependencies, which enables it to launch patches in the right order. The system is also able to reboot each device after updates where necessary.
All of the discoveries of the Vulnerability Manager Plus system are documented and so are the actions that the system implements to remediate threats. This body of logs is important for compliance reporting and the reporting engine in the package will order, summarize, and format that data in a suitable layout for whichever standard you are complying with.
Who is it recommended for?
This tool is recommended for organizations seeking a comprehensive, on-premises vulnerability management solution for their networked devices. Its versatility in managing Windows, Linux, and macOS endpoints makes it suitable for environments with diverse operating systems. Ideal for IT professionals and security teams, ManageEngine Vulnerability Manager Plus excels in automating tasks related to vulnerability scanning, patch management, and compliance reporting. While its feature-rich nature makes it appealing for large organizations, the availability of a free edition, albeit with limitations on the number of endpoints, ensures that even smaller entities can benefit from its robust security capabilities.
Pros:
- A high degree of automation in discovering hardware and software
- Recommendations for procedural standardization
- Manages devices running Linux, macOS, and Windows
- Can patch more than 500 third-party applications
Cons:
- Not a SaaS package
ManageEngine Vulnerability Manager Plus installs on Windows Server. It is a very comprehensive package that you might think is only suitable for large organizations. However, ManageEngine produces a free edition that includes all of the utilities of the paid system but is limited to working with 25 endpoints. That free system is very appealing for small businesses. The paid plans are the Professional Edition for a single network and the Enterprise Edition for multi-site systems. You can get the Professional Edition on a 30-day free trial.
2. Site24x7 (FREE TRIAL)
The Site24x7 SaaS-based tool monitors your networks and all their components to provide comprehensive visibility into their security, availability, and performance. Using this information, you can resolve issues quickly and make informed decisions.
Why do we recommend it?
We highly recommend Site24x7 for its comprehensive coverage and visibility. It can monitor almost any device, service, traffic stream, or any other component in your network. Essentially, it gathers the relevant metrics from each device and compares them against the established thresholds to identify deviations. If found, it sends alerts and provides the required contextual information for quick troubleshooting.
Additionally, all the data is displayed on intuitive dashboards for easy understanding. It also supports data-driven decisions through well-developed graphs and reports.
Another aspect that stands out to us is the level of automation. As soon as you get started, the tool automatically scans your network using SNMP. It maps the devices and their dependencies and creates visualizations through layer 2, layer 3, and topology maps that different teams can use to get the data they need. These visualizations also help teams to identify misconfigurations and performance bottlenecks before they impact the wider organization.
Who is it for?
A good choice for IT teams of medium to large enterprises and MSPs who need a comprehensive network monitoring tool that can send alerts in real time.
To learn more about this tool and see its fit for your organization, sign up for a 30-day free trial.
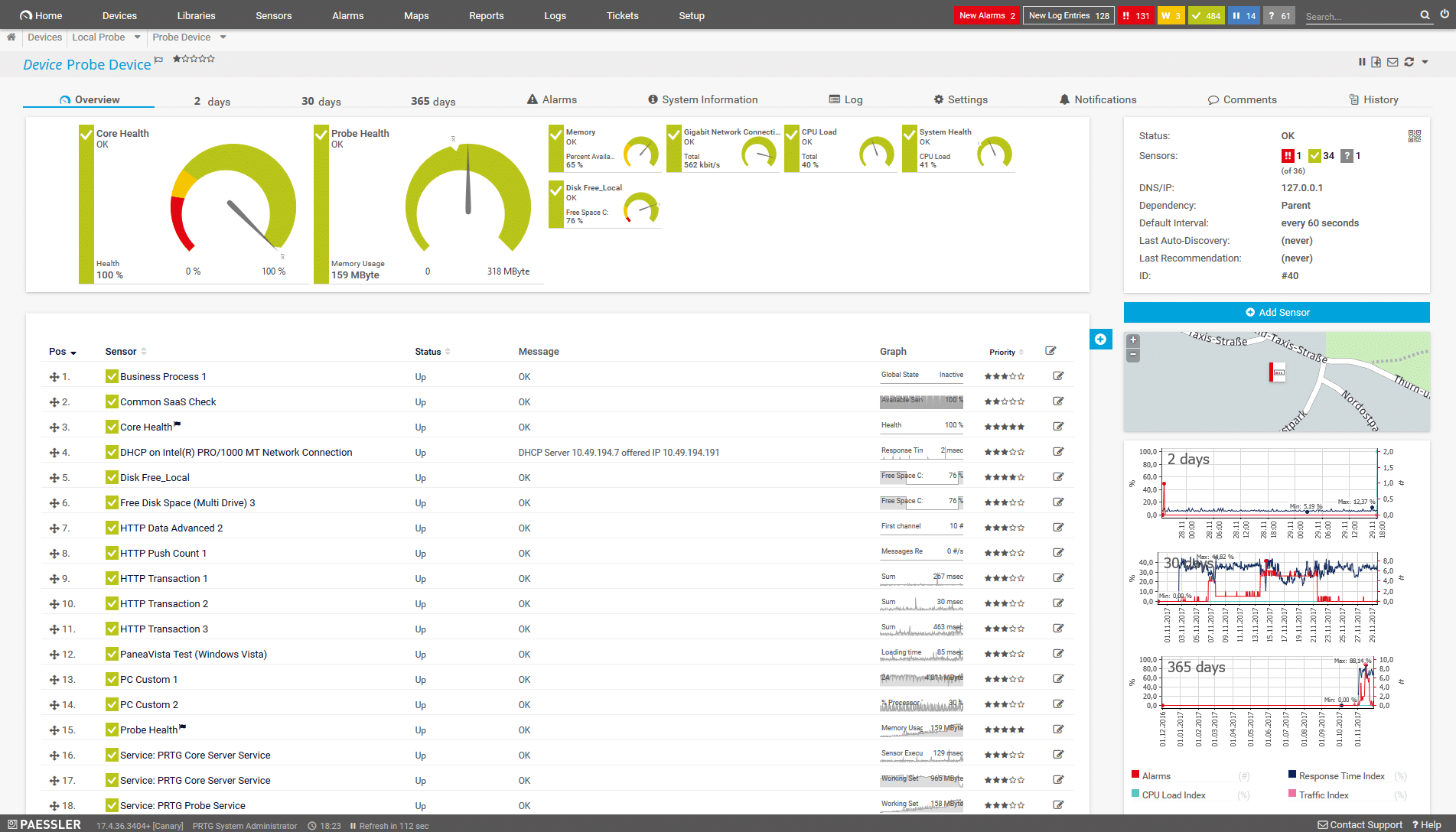
3. Paessler PRTG Network Monitor (FREE TRIAL)
If you’re looking for more flexibility with pricing and deployment, PRTG Network Monitor offers to monitor on a per sensor basis. For example, setting a monitor to listen for port traffic would count as one sensor. With PRTG you only pay for the sensors you use, giving you more granular control over what features you use, versus what you pay for.
Why do we recommend it?
PRTG Network Monitor earns its recommendation for its flexible pricing model based on a per-sensor basis, allowing users to pay for the specific features and capabilities they utilize. This granularity provides cost control and makes PRTG an attractive option for organizations with varying monitoring needs. Its holistic approach enables monitoring across diverse protocols and traffic types, ensuring comprehensive visibility into network security. PRTG’s adaptability to specific security areas makes it an ideal solution for users seeking tailored monitoring solutions.
Paessler takes a holistic approach by giving you the freedom to monitor many different types of protocols and traffic. If it exists, you can monitor it with PRTG. If you have very specific areas of security you’re looking to monitor, this makes PRTG an ideal solution.
In addition to monitoring, there are plenty of built-in mechanisms for notifications such as HTTP requests, push notifications, and email to keep you or your team in the loop on network and security events. Dependency settings help you dial down alerts to avoid flooding your ticketing system, while the scheduling section allows you to only let through critical alerts after hours.
Who is it recommended for?
PRTG Network Monitor is recommended for organizations of all sizes looking for a customizable and cost-effective network monitoring solution. The per-sensor pricing model is particularly advantageous for those who want precise control over the features they pay for. Ideal for IT professionals and network administrators, PRTG’s extensive capabilities make it suitable for monitoring specific security areas, providing valuable insights and alerts. Whether replacing Microsoft Baseline Security Analyzer or expanding network monitoring capabilities, PRTG offers a versatile solution that can be tailored to the unique requirements of any network.
If you’re looking to replace Microsoft Baseline Security Analyzer and also have some areas of your network that still need to be monitored, PRTGs broad scope of capabilities make it a great choice for any sized network. You can test out all of PRTG’s features with a free 30-day trial.
4. SolarWinds Network Security Tools with Engineer’s Toolset
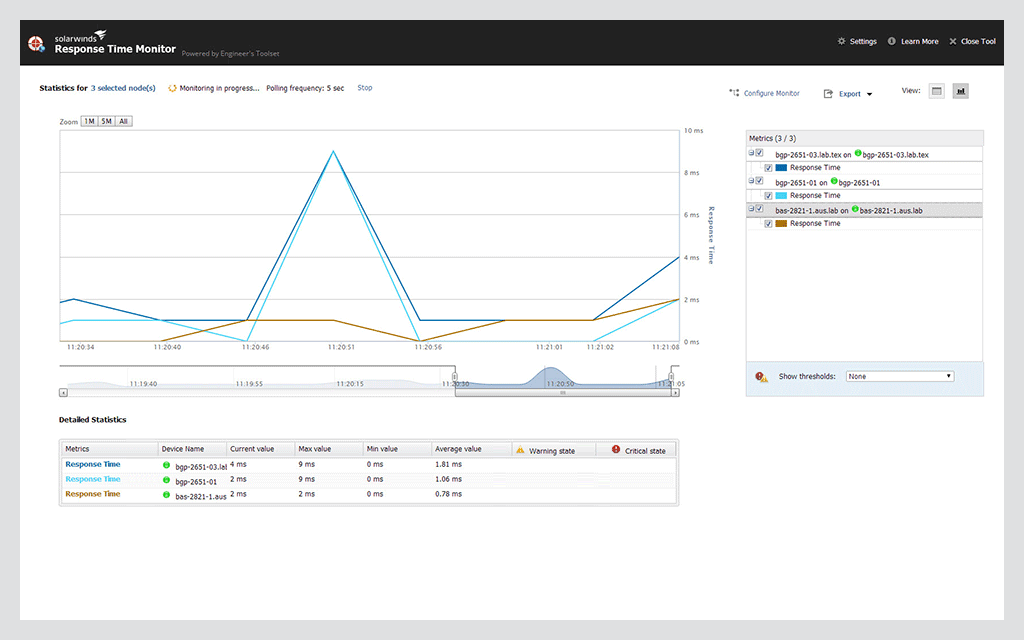
The Engineer’s Toolset is an administrator’s best friend and contains an entire suite of tools that can help you monitor your network, manage devices, and implement security measures. With that being said we’ll focus on just how useful the network security tools are for replacing Microsoft Baseline Security Analyzer.
Why do we recommend it?
The Engineer’s Toolset by SolarWinds stands out as an exceptional choice, particularly for replacing Microsoft Baseline Security Analyzer (MBSA). This comprehensive suite of tools is a network administrator’s indispensable companion, offering a range of functionalities for network monitoring, device management, and robust security implementation. Notably, the Patch Manager component addresses the limitations and shortcomings often encountered with WSUS, providing an intuitive patching dashboard, compliance reporting, and pretested patching packages. The real-time monitoring capabilities of Security Event Manager further elevate the toolset by offering an easily interpretable dashboard for quick insights into security-related events, coupled with automated threat detection and response features that add an extra layer of protection.
Patch Manager is your one-stop-shop for managing Microsoft Windows updates, as well as keeping your third-party programs up to date. If you’ve used WSUS for patch management, you’ve likely experienced its shortcomings and run into plenty of limitations. Patch Manager was designed to fill that void by providing an intuitive patching dashboard, compliance reporting, and an array of pretested patching packages.
For real-time monitoring, Security Event Manager keeps sysadmins up to speed with all security-related events across the network. Security Event Manager features an easy to read dashboard that gives you a top-down view of outstanding issues at a glance. One of my favorite parts of this tool is its automated threat detection and response.
During configuration, you can set specific events or thresholds to trigger actions such as disabling a user account, removing permissions, or executing a custom script. This, of course, requires a bit of time to set up and test but eliminates the last minute panic when a security breach occurs.
Security Event Manager goes above and beyond what MBSA could ever do by providing a forensic breakdown of file monitoring and added elements of intrusion detection. Also, the tool kit comes with a tool you might not expect, an SNMP dictionary attack tool. Use this tool to simulate attacks on network devices to find flaws in your own security or weak passwords set by end-users. SolarWinds has compiled some of the most commonly used dictionaries for you to use out of the box but also allows for you to import your own, or even customize an existing dictionary.
Who is it recommended for?
The SolarWinds Engineer’s Toolset, with its Network Security Tools, is recommended for network administrators and IT professionals tasked with comprehensive network monitoring, device management, and security enforcement. Specifically, for those who have found WSUS lacking in patch management, the Patch Manager within this toolset proves to be a valuable replacement, streamlining the patching process and enhancing compliance reporting. Security Event Manager is ideal for sysadmins seeking real-time monitoring, automated threat detection, and response mechanisms, offering a top-down view of security issues across the network. The toolset’s versatility extends to professionals looking for forensic file monitoring, intrusion detection, and even simulation tools like SNMP dictionary attack capabilities, providing a robust solution for security-conscious environments.
All of these security tools plus more are conveniently bundled in the Engineer’s Toolset. You can test out any of these tools completely free for 14 days.
5. Intruder

Intruder is an entirely cloud-based scanner that is designed to find weaknesses and vulnerabilities in your network before the hackers do. Intruder utilizes similar external scanning that financial institutions use to ensure PCI compliance, and that best practices are being met. While Intruder isn’t reinventing the wheel, it does a good job delivering you actionable reports on areas of weakness prioritized by the level of impact it could have on your network.
When a threat or missing patch is found, you can receive an alert to be notified as soon as it’s found. Alerts are also integrated into Slack and Jira, making this an ideal tool if your team works with one of those apps.
Intruder is definitely marketed towards those who aren’t tech-savvy and lacks the ability for you to customize attack vectors, ports, or any of the fine details most tools allow for. If you’re looking for the most hands-off approach to threat prevention and monitoring, Intruder is a solid option. Of course, all of this convenience comes at a price. The base monthly fee starts at $101 when billed annually.
6. OpenVAS

OpenVAS is an open-source and completely free vulnerability scanner that was first published in 2009. Much of the power behind OpenVAS comes from the community where you’ll find more than 50,000 different types of vulnerability tests you can run through the software.
Why do we recommend it?
OpenVAS, an open-source and free vulnerability scanner, earns its recommendation due to its robust community-driven support and an extensive database of over 50,000 vulnerability tests. The tool provides unparalleled flexibility and power, allowing users to conduct a wide array of vulnerability tests limited only by their skills and imagination. While OpenVAS may lack the plug-and-play convenience of commercial alternatives, it compensates with a highly customizable approach, making it suitable for users seeking in-depth control over their scans.
The flexibility and power of OpenVAS are only limited to your imagination and skillset. With that being said, as with most open-source products your support will be limited to the community forums, and what you can piece together across Google searches.
While not much about OpenVAS is plug and play, you’ll find yourself with a rudimentary dashboard displaying the number of tasks you have running. Also, your CVEs that are created over time, and a pie chart view of the number of current threats found based on severity.
Once a scan is finished, you’ll have the chance to view what was found under the results tab. Here you’ll see a list of the type of vulnerabilities that were found, what their severity rating is, and the corresponding port number and service that encompasses it.
Drilling down into the results you’ll be given a fairly technical summary of how the attack was carried out and how your system reacted to that attack. Below this, the scan provides the next steps to mitigate this type of attack. Sometimes this is as easy as changing a password, other times it can involve numerous steps. I was pleasantly surprised by the level of detail provided in this section.
Although there are a vast amount of documentation and use case examples in the Knowledge Base, I found there is still a fairly steep learning curve for utilizing OpenVAS to its full potential.
The level of customization you apply to OpenVAS is extremely high given the fact the entire tool itself is open source. You might find this ideal if you’re looking to scan very specific ports and protocols on custom applications or other non-conventional programs.
For most corporate environments, OpenVAS will likely be too much to learn and take too long to be worth the effort. But for those who are on a budget and have the time and dedication to really learn OpenVAS, this could be the alternative to Microsoft Baseline Security Analyzer you’ve been looking for.
Who is it recommended for?
OpenVAS is recommended for users and organizations with a budget-conscious approach and a willingness to invest time and effort in learning a comprehensive, open-source vulnerability scanner. Ideal for those who prioritize customization and have specific scanning requirements, OpenVAS may pose a steep learning curve for beginners but offers a cost-effective alternative to commercial tools. Community forums and extensive documentation contribute to its appeal for users comfortable with a more hands-on and community-supported approach to vulnerability scanning.
7. Nexpose

Nexpose is an on-premises security scanner developed by Rapid7, the same company that developed the popular offensive security tool Metasploit. One feature that sets Nexpose apart from the other tools is its Real Risk Score system.
Why do we recommend it?
Nexpose, developed by Rapid7, stands out among security scanners with its distinctive Real Risk Score system. This feature assigns a score from 1-10 to threats, considering factors such as the vulnerability’s age, available public exploits, and the likelihood of a successful attack. This quantitative approach provides valuable insights for prioritizing patching and threat mitigation efforts. The tool’s integration with the Metasploit framework, developed by the same team, enhances its capabilities, making it an excellent choice for those seeking a comprehensive security solution.
Nexpose finds and scores threats on a 1-10 scale taking into account the vulnerability’s age, number of public exploits that are available, and the chance that an attack would actually be successful. This level of insight gives you a quantitative look at just how you should prioritize your patching and threat mitigation.
On the active side of your network, Nexpose can be configured to immediately detect new devices on your network and scan them. Rather than relying on infrequent data dumps and definition updates, Nexpose’s ‘Adaptive Security” taps into its Sonar Project to find and compare your results to some of those latest threat discoveries.
In addition to basic network scanning, you can also configure Nexpose on a policy level to help your network stay compliant with standards like PCI, NIST, and CIS. These policy templates come preconfigured and only need to be launched to run. When the scan is complete, a report gives you step by step instructions on what needs to be done starting with the actions that will make the biggest difference in terms of compliance.
Since this tool was created by the same team that worked on Metasploit, you can expect a full-on integration with the Metasploit framework. While this integration may be more than what most companies need, it makes a perfect pair for admins who are looking to simulate a breach and play on the offensive side to test their network.
Lastly, all of this data is compiled in a remediation report that’s pre-designed to be ready to hand off to executives and other individuals that just need a high-level overview of the results. The report does a great job of staying simple, yet informative. A large letter grade is marked in the top left-hand corner to give an immediate indication of your network’s standing.
Who is it recommended for?
Nexpose is recommended for security professionals and administrators looking for an on-premises security scanner with advanced risk assessment capabilities. The Real Risk Score system offers a nuanced understanding of vulnerabilities, aiding in effective prioritization. Organizations aiming for compliance with standards like PCI, NIST, and CIS will benefit from Nexpose’s policy-level configurations. The tool’s integration with Metasploit caters to users interested in a more offensive security approach, allowing them to simulate breaches and test network defenses. The remediation report simplifies complex results for executive-level understanding.
You can test out all of the features Nexpose has to offer free for a full 30-days.
Choosing Microsoft baseline security analyzer alternatives
It’s clear that Microsoft Baseline Security Analyzer is outdated and doesn’t fit most organizations’ needs anymore. While we’ve listed the best alternatives to MBSA, we’ve found a few tools that work especially well depending on your company’s size and requirements.
Managed service providers and most medium-sized businesses will greatly benefit from ManageEngine Vulnerability Manager Plus and Site24x7. Not only will these tools replace the functionality of MBSA, but they’ll also provide even further protection through streamlined automation and solutions you can implement right out of the box.
For businesses that have more time than money, OpenVAS is a free and open-source scanner that can be configured in almost an unlimited number of ways. Just make sure you have the time to invest in mastering it, as there is little to no support beyond the community.
So what’s your favorite alternative to MBSA? Be sure to let us know your favorite tool in the comments below.