A packet sniffer captures the data that travels around a network. Packet sniffers come in a range of types, and one category is a piece of hardware.
When you want to look at the flow of traffic around a network or detect for network intrusion, your first requirement is for a packet sniffer. Software packet sniffers range from straightforward data capture and storage systems through to sophisticated traffic analysis packages.
In this guide, you will learn about a variety of packet sniffing software and find out the strengths and limitations of each. Packet sniffers aren’t just meant for wired networks. Many packet sniffers can monitor your wireless traffic and others can cover hybrid networks, even tracing traffic to cloud-based services contracted in by your company.
This guide focuses on a list of the best packet sniffers, both free and paid, available on the market in 2018. After the summaries, you can read more about the different uses of a packet sniffer.
Here is our list of the best packet sniffers:
- SolarWinds Network Performance Monitor (FREE TRIAL)
- ManageEngine NetFlow Analyzer (FREE TRIAL)
- Paessler Packet Sniffer
- ireshark
- EtherApe
- SmartSniff
- Microsoft Message Analyzer
- Free Network Analyzer
- Network Miner
- Capsa
- Netsniff-NG
- Kismet
- Ettercap
- KisMAC
- EtherDetect
Packet Sniffers by operating system
| Software | Windows | Linux | Unix | Mac OS |
| SolarWinds Network Performance Monitor | Yes | No | No | No |
| ManageEngine NetFlow Analyzer | Yes | Yes | No | No |
| Paessler Packet Sniffer | Yes | No | No | No |
| Wireshark | Yes | Yes | Yes | Yes |
| EtherApe | No | Yes | Yes | Yes |
| SmartSniff | Yes | No | No | No |
| Microsoft Message Analyzer | Yes | No | No | No |
| Free Network Analyzer | Yes | No | No | No |
| Network Miner | Yes | Yes | Yes | Yes |
| Capsa | Yes | No | No | No |
| Netsniff-NG | No | Yes | No | No |
| Kismet | No | Yes | Yes | Yes |
| Ettercap | Yes | Yes | Yes | Yes |
| KisMAC | No | Yes | No | No |
| EtherDetect | Yes | No | No | No |
1. SolarWinds Network Performance Monitor (FREE TRIAL)
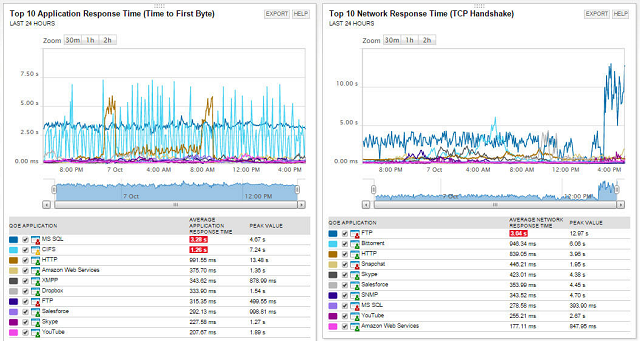
The SolarWinds Network Performance Monitor focuses on gathering status information from network-attached equipment. It also has a packet sniffer module that can help analyze traffic as it moves around the network.
The packet sniffer can look at the origins of traffic on your network. Seeing which terminal data originated at can help you detect unauthorized network intrusion. Examining packets on the network will tell you what applications generate the most traffic.
The dashboard of the packet sniffer shows network throughput and identifies each of the applications that send out packets. You can see the response times per application over the past 24 hours. The records that indicate slow responses show warnings highlighted in red. You can nominate a start and end points for analysis, which allows you to examine traffic on different network segments. Other utilities in the Network Performance Monitor extend the visibility of network events found during packet analysis. These include the PerfStack screen, which enables you to view metrics for underlying services together with application traffic data. This greatly aids in identifying the cause of traffic bottlenecks.
The Network Performance Monitor is not free. The price of the system increases with the number of devices you have connected to your network. SolarWinds offers an alternative method for network traffic monitoring, which is called the NetFlow Traffic Analyzer. This system uses the system messages sent out by routers and switches instead of capturing packets from the network.
The company offers a package called the Network Bandwidth Analyzer Pack, which combines both the Network Performance Monitor and the NetFlow Traffic Analyzer. All of the SolarWinds packages are designed to run on Windows Server 2012 and Windows Server 2016, though it can collect data from devices running any operating system. You can access the Network Performance Monitor, the NetFlow Traffic Analyzer, and the Bandwidth Analyzer Pack on a 30-day free trial.
2. ManageEngine NetFlow Analyzer (FREE TRIAL)
To find the packet sniffer offered by ManageEngine, you need to look at the company’s NetFlow Analyzer tool, which can be installed on Windows and Linux. Although NetFlow is a Cisco network device messaging system, the NetFlow Analyzer also includes packet analysis capabilities.
The analyzer includes deep packet inspection. Although it wouldn’t be much use to look at the content of encrypted packets, the inspection capabilities offer a good route to examine the headers of packets. The analyzer captures packets and stores them to a file. This is because examining packets in isolation can only give you so much information. Being able to aggregate data and plot trends gives more powerful analytical capabilities.
The packet header information includes the source and destination addresses and port numbers of a transfer. Thus, you can assess the impact of protocols, applications, and the impact of user activity on network utilization. Important comparisons between network response times and application response times will give you an idea of which applications are overloading or slowing down the network. That information will help you decide whether to expand capacity, selectively limit network access, or investigate alternative and less bandwidth-hungry applications.
The packet capture files can be stored and loaded back into the NetFlow Analyzer dashboard for long-term performance comparison. This gives you the capability to assess the effects of infrastructure investments.
As an alternative to packet capture, you can use the NetFlow Analyzers system message reading capabilities. These rely on information sent out by network infrastructure following the NetFlow, NetStream, Appflow, sFlow , cflow, J-Flow , FNF, and IPFIX standards.
The ManageEngine NetFlow Analyzer is priced by a count of interfaces. An Interface is a Layer 3 physical or logical interface or a port on a switch or router. The software for this package can be installed on Windows or Linux.
The system is available in two versions: an Enterprise edition suitable for small, medium, and large networks; and the Distributed edition suited to large enterprises. You can get a 30-day free trial for either of these versions.
3. Paessler Packet Sniffer
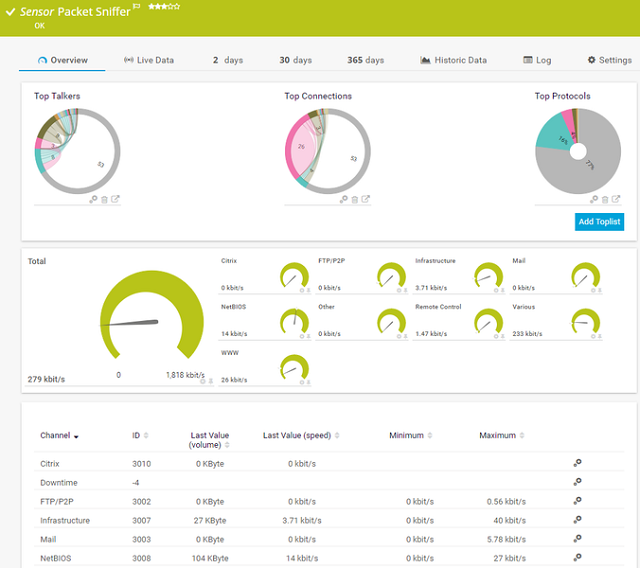
Paessler produces a network monitoring package called PRTG that includes the All-In-One Packet Sniffing Tool. One of the elements of this tool is a packet sniffer. PRTG can only be installed on the Windows operating system. However, a cloud-based version of the package is accessible through a browser and so can be used from any operating system.
PRTG offers a range of network traffic analysis methods including a packet sniffer. An alternative to this is provided by the package’s ability to capture system messages from network hardware (IPFIX, NetFlow, sFlow, and J-Flow). The packet analysis function of the system lets you to identify which terminals, applications, and protocols generate traffic on your network. This information enables control of network access and throttling of bandwidth to specific MAC or IP addresses, protocols, or applications.
The dashboard of the PRTG interprets the information that the packet sniffer collects and displays it through graphical data visualizations. These include color-coded dials, which make it easy to spot critical conditions at a glance. The Paessler PRTG system is priced on the number of “sensors” that you wish to monitor. A sensor is an attribute on a device. For example, the traffic on a network connection is a sensor and so is a monitored switch port. Paessler explains that it takes five to ten sensors to properly monitor a device. You can download a free trial of the system. If you monitor 100 sensors or less, you can use PRTG completely free of charge.
4. Wireshark

Wireshark is a very handy free packet sniffer that can be installed on Windows, Linux, Unix, and macOS. This system will capture packets passing along your network. It can scan wi-fi and Bluetooth as well as wired networks. The collected packets can be shown in the Wireshark dashboard and/or saved to file. The file formats that Wireshark can write to and read from are numerous. They include tcpdump, Pcap NG, Microsoft Network Monitor format, and Sniffer Pro.
Once you get packets into the dashboard’s data viewer, you have a lot of visualization options. Records can be filtered and you can also identify packets by protocol, including the ability to isolate VoIP streams. You can enable coloring rules to quickly recognize different packet sources and statuses.
Wireshark is developed by a not-for-profit organization that has no income stream from advertising. The developers of the system are funded by donations and by sponsorship from a company, called Riverbed Technology. Riverbed produces a network performance monitor, called SteelCentral, which is designed to integrate Wireshark. However, Wireshark has its own front end, so you don’t need to buy in extra software in order to examine the data that it collects. You can use Wireshark at the command line through a facility called TShark.
5. therApe
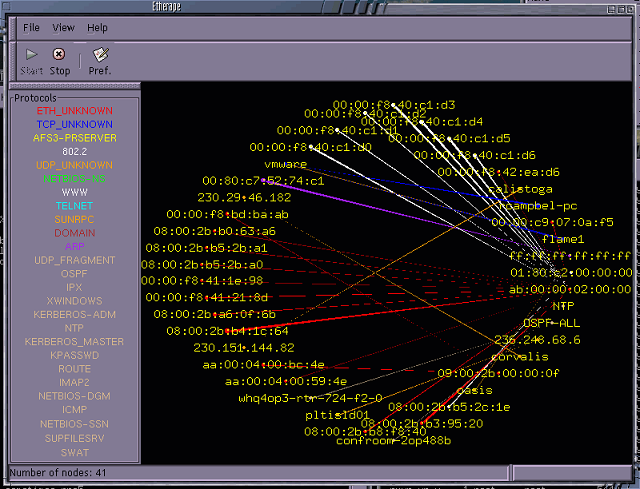
EtherApe was written for Unix and Unix-like systems, so it can be installed on Linux and MacOS. This packet sniffer is a free utility based around a graphic representation of the links in a network.
The console of the tool shows all of the hosts in a network, identifying each by its IP address. These hosts are plotted in a circle and the connections from one to another are linked by straight lines. Each line is colored, with a different color representing each protocol generating traffic on the network. The source for this information is in the headers of the packets that the program captures.
Each line expands and contracts in width according to the current traffic volume that it generates. A constantly changing visual representation of the traffic on your network is based on live data. The packet sniffer can work with both IPv4 and IPv6 addressing systems and it tracks both TCP and UDP packets. You can filter the data for the display to concentrate on a limited list of traffic sources. You can also switch the perspective of the data to show either end to end connections, network-only traffic, or port number activity for TCP traffic. The packet sniffer can cover wireless traffic and virtual environments as well.
EtherApe can write packets to a file. The displayed traffic can be sourced from files instead of live traffic events. Clicking on a node gives detailed information on the activities at that host’s network card.
This packet sniffer has been around since the year 2000 and its longevity has earned it a good reputation among the system administrator community. It is particularly popular with administrators who have been in the business a long time and have come to rely on the tool. Newer practitioners of the trade would probably be drawn to tools with more sophisticated interfaces, such as SolarWinds, ManageEngine, or Paessler products.
6. SmartSniff
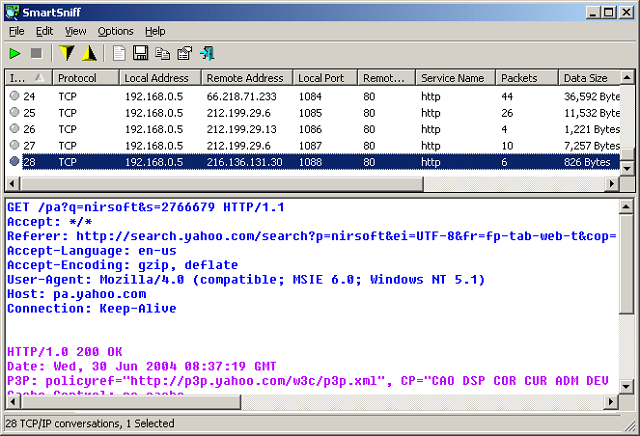
SmartSniff can be installed on any version of Windows and Windows Server. It is a free packet sniffer that captures data packets on networks. Although the utility can access packets on wireless networks, those WLANs need to be unencrypted in order for SmartSniff to access the packet data. The chances of ever coming across an unprotected wireless system are just about nil, so don’t rely on SmartSniff to analyze wireless networks.
The main focus of this tool is traffic passed over TCP connections. The reporting module of the utility will categorize traffic by network application, such as HTTP, POP3, FTP, and SMTP. Packet capture is started and stopped on demand. The console for the tool has two panes. The upper panel shows each connection and the two devices engaged in each exchange. If you select one of these connection records, the lower panel shows the packet stream that passed in both directions in the connection.
You can filter data either at the point of collection, or in the conversation viewer. The filter options include including or excluding TCP, UDP, and ICMP messages. You may specify an IP address or port range for the session.
Collected data can be saved to file and you can also load file contents into the console for viewing. SmartSniff isn’t one of the most sophisticated packet sniffing tools on this list, but it has a following.
7. Microsoft Message Analyzer
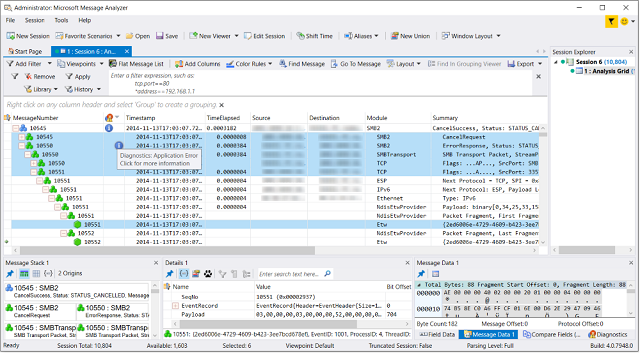
Microsoft Message Analyzer offers an alternative packet sniffing strategy. This research method might please your CIO because it does not involve reading the passing data generated by users, which may require privacy enforcement. This application only examines communication messages generated by protocols to manage connections. Limiting packet sniffing to these types of messages preserves data privacy.
The dashboard displays messages in a hierarchy, so you can see related messages together. Those message overviews appear in the main panel of the data viewer. Smaller detail panes below the main panel give you detailed information on any selected message.
You can store captured messages to a file and the viewer can display live network messages or stored records loaded in from a file. The viewer allows you to group and filter messages. You can trace messages through their journey to an endpoint on your network.
Although the Microsoft Message Analyzer won’t give you access to actual data packets, the protocol details that you can capture will give you a good indication of network load.
The free utility can be installed on Windows 7, Windows 8, Windows 8.1, Windows 7, 8, 8.1, and 10 and Windows Server 2008 R2, Windows Server 2012, Windows Server 2012 R2, and Windows Server 2016.
8. Free Network Analyzer/HHD Network Monitor

The Free Network Analyzer and the paid Network Monitor from HHD Software are both available for Windows and Windows Server. This paid packet sniffer is available in three editions: Standard, Professional, and Ultimate. With the free version your session will cut off after 15 minutes and you can only start up the system five times a day.
All versions of the Network Analyzer/Network Monitor allow you to capture packets and view them in the console. You can’t save records to a file with the Standard or free versions. You are only able to view the raw packets in the Ultimate version.
The packet sniffer will pick up data from wired and wireless networks. Ultimate edition can read packets written to the MODBUS industrial network standard. You can set select criteria to only record packets with specific characteristics. You can also choose to filter packet data once it is in the viewer. The viewer shows live traffic and can buffer up to 1GB of data.
Although you can only store packets to a file with the Ultimate version, all versions can read in packet data from a file.If you don’t have the Ultimate edition, however, those files would need to be assembled by another application.
The viewer of the Free Network Analyzer and the HHD network monitor shows packet summaries in a top pane and details for selected packets in the bottom. The viewer can interpret data into visualizations such as graphs.
9. Network Miner
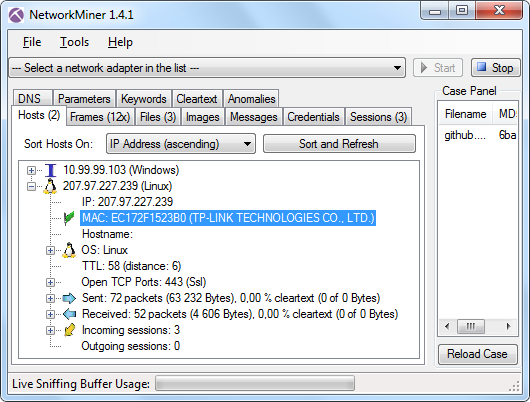
You can use a free version of Network Miner or you can pay for the Professional edition, which costs $900. This packet sniffer works on Windows, Linux, Mac OS, and FreeBSD. The free version has a number of limitations, including the inability to write captured packets to a file. With Network Miner you can examine packets from a live stream taken from your network. The data viewer can also read in packets stored to a file.
Network information contained in packet headers is richer for TCP than for other transport layer protocols. As with most network analyzers, Network Miner gives much more detailed information for TCP connections than messages transferred with other protocols. The packet sniffer will pick up UDP packets, though it won’t be able to string those together into a stream of related packets. The Network Miner packet sniffer can identify FTP, TFTP, SMB, SMB2, HTTP, SMTP, POP3 and IMAP streams and can extract the security certificate details from session establishment exchanges for secure connections, such as HTTPS and SMTPS.
The packet sniffer for both free and paid versions has some features that may make you uncomfortable as a network administrator. It can extract files and during transfer and it can also identify users. The user credentials search will display user names and passwords of those users connected to the network. These facilities would help hackers and data thieves by compromising the confidentiality of personal information sent across your network. For these reasons, your CIO might not let you use Network Miner.
10. Capsa
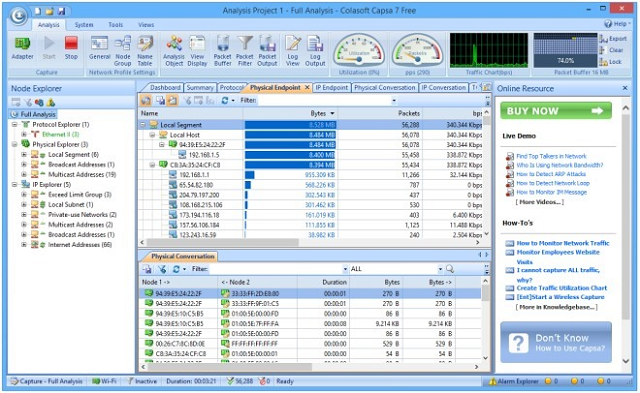
Capsa comes in three versions: Free, Standard, and Enterprise. With the paid versions, your purchase gives you the right to use the software forever, but you only get one year’s maintenance. After the first year, you will have to sign up for an annual maintenance plan in order to continue receiving updates and patches. You can get a 15-day free trial for either of the paid versions of Capsa.
You can monitor up to 10 IP addresses with the free version of Capsa. With the Standard Edition, that limit goes up to 50. There is no limit on the number of addresses you can monitor with the Enterprise Edition. The Free and Standard versions of Capsa only monitor Ethernet networks. The Enterprise Edition covers wireless networks and can list data by port number. Both the Standard and Enterprise versions can filter data capture by application or process.
Security functions are reserved for the Enterprise Edition. These give you an opportunity to analyze both past and ongoing DoS attacks. The Enterprise version can also highlight suspicious connections and scan for worm activity.
You can write data out to files with all versions of the system, but you can only log data saves with the Enterprise and Standard versions. Printing and exporting data are not possible with the free version.
The Capsa Network Analyzer runs on Windows.
11. Netsniff-NG

Netsniff-NG is a free network monitoring utility written for Linux. A packet sniffer forms the core of this tool, but extra functionality has been added on over the years.
The extra facilities bundled into the Netsniff-NG package include two traceroute-like facilities that track the origins of connections to the network from external sources. This ties in with geo-location information to give the physical location of the host that connects to the network. A packet filter utility lets you reduce the captured traffic to see only certain categories of network traffic. A utility called ifpps creates overview reports on network traffic statistics.
Once installed, traffic generators help test new equipment before connecting to the network. Another useful tool is a basic tunneling program that lets you divert test traffic around your firewall. Such an action helps assess the effects that network defense software has on network performance.
Netsniff-NG has been around since 2009 and it doesn’t have the sophisticated GUI interface that newer packet sniffers on this list provide. Another problem with the package is that it doesn’t write to a file. However, with command line manipulation, you could easily pipe output to a file yourself. The output isn’t formatted and results can be difficult to interpret. However, regular long-term users of Netsniff-NG become accustomed to the patterns of regular traffic and can quickly spot anomalies.
12. Kismet

Kismet is a free packet sniffer for wifi networks that can be extended by plug-ins to monitor standards other than 802.11, such as Bluetooth. This is a free tool that includes some interesting stealth features. It is available for Linux, Unix, and MacOS. If you have Kali Linux, then you don’t need to install Kismet because it is part of the Kali bundle.
The packet sniffer of Kismet can pick up signals generated to 802.11a, 802.11b, 802.11g, and 802.11n standards. Its operating methods are a little worrying because they make it a perfect live hacker tool. Kismet doesn’t query APs, so it cannot be detected by other network monitoring systems. If there is a computer on your network running Kismet and gathering information on all connected hosts, you will just see it as a regular endpoint rather than a traffic monitor.
Kismet’s packet sniffer is called a “drone.” It passively gathers wifi signals and logs them. Those signals contain enough information to allow the Kismet data interpreter, called the “server,” to assemble statistics on each transmitting host and the traffic that it generates. That data is then displayed by the “client.” You can substitute other packet analyzing interfaces for the Kismet client if you wish.
Although other intrusion detection systems can’t spot Kismet, this tool can spot other wifi sniffers actively probing the network. Kismet reads the headers of packets to get its information. You can get file dumps of all traffic, including packet payloads.
Wifi networks are a lot more complicated than wired systems because the many frequencies available for transmission can only be monitored if the receiver uses the same frequency. So, Kismet constantly hops from channel to channel to capture data from as many frequencies as possible. It is possible to specify the channels that the receiver tunes into and the sequence of those visits, but Kismet installs with a default channel order that is probably best to leave in place.
The interface of Kismet is user-friendly, including live histograms of passing data. However, if you already have a tool that you prefer to use, you may be able to import stored traffic data gathered by Kismet. This is because the utility can store data files in tcpdump and Airsnort formats, which many network analysis tools can read. Kismet is a very thorough wireless network analysis tool.
13. KisMAC 2
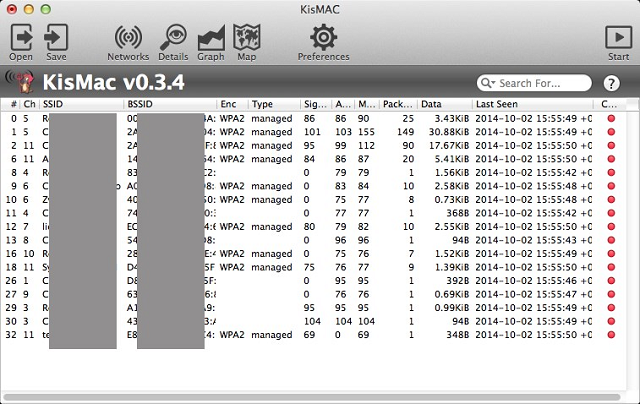
KisMAC was a useful network monitoring tool written for Mac OS. It shut down but has since been revived by others as KisMAC 2. This wifi packet sniffer is a free utility.
KisMAC and KisMAC 2 closely emulate the capabilities of Kismet — hence the names. KisMAC 2 has some nice data visualization tools not available in Kismet. For example, it is able to draw a wifi signal map that shows the footprints of surrounding wifi APs. KisMAC 2 can detect signals from WAPs and wireless NICs following the 802.11b, 802.11n, and 802.11g standards. It is particularly effective for monitoring Apple’s AirPort and AirPort Extreme traffic.
The compatibility with Kismet extends to the fact that you can use a Kismet “drone” to collect data and feed it into KisMAC 2. It can read in files created in the PCAP format and write output in PCAP or tcpdump formats, so it can be used to supply data to many other packet analyzing tools.
Although KisMAC 2 is advertised as a security tool, many of its features look a lot like hacker utilities. These include brute force WEP and WPA key cracking, packet injection, and deauthorization attacks. The original KisMAC project was developed in Germany and was abandoned when changes in German law made its capabilities illegal. KisMAC 2 is now managed from Russia.
As with Kismet, this tool can be used for ethical hacking. Its ability to reveal hidden/cloaked SSIDs is a really useful feature that aides intrusion detection.
14. Ettercap
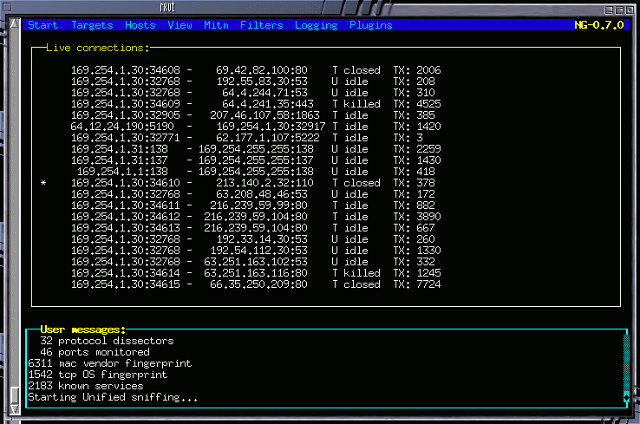
Ettercap is a hacker tool used to carry out “man in the middle” attacks on networks. However, it is able to detect other players performing hacker scams on a network, and so it is a useful poacher-turned-gamekeeper ethical hacking tool. This is a free utility and it is available for Linux, Unix, Mac OS, and Windows.
Most network cards have a “promiscuous mode” which enables them to discover other devices and communicate directly with them. Once a target has been identified, Ettercap practices ARP poisoning to get its host computer regarded as a network access point or router. This makes Ettercap particularly effective at capturing traffic traveling into the network from an external source or destined for a connection to an external source. Ettercap can work on the MAC address level to masquerade as a genuine host on the network.
Ettercap can gather passwords for a range of network applications and can even induce SSL procedures to disclose security certificates, which enables the host to pose as a bona fide correspondent and reap passwords on secure connections.
The program can alter the contents of passing packets and even cause connections to drop. All in all, you probably wouldn’t want anyone else using Ettercap on your network. However, the software’s ability to detect the usage of these techniques by others makes it a good tool for intrusion detection. The in-app facility to disconnect and isolate a suspicious user means you don’t have to switch to another network management tool in order to repel intrusion.
Reading through the capabilities of Ettercap might make you anxious. However, installing and using this tool yourself will educate you in the possible actions of hackers and intruders and help you create strategies in order to defend your network. The packet sniffing, data and packet injection and connection killing facilities in Ettercap may save your network.
15. EtherDetect

EtherDetect is a lightweight packet sniffer for Windows. This is not a free utility. It costs $99.95 and you get 30 percent off if you don’t use it for a business. The packet sniffer works on wired networks and it can operate from any Windows device.
The packet sniffer captures entire packets, not just the headers, and it can reap both TCP and UDP transmissions. Traffic is displayed live in the program’s viewer. If the speed of passing data is too much for interpretation, you can filter traffic to only capture specific protocols. You can also sort and search data in the data displaying interface. The viewer will also interpret the signals and codes used in packet headers according to the conventions of the protocol under scrutiny.
The viewer can save packet captures to files and you can load saved data later for analysis when offline. Getting stored data allows the viewer to organize traffic by connection. With this view you can follow the messages that travel back and forth between two endpoints rather than trying to spot those threads among all the other network traffic as it streams past in live mode.
The viewer gives you options to either view the raw packet data in hex format or get every character interpreted into an alphanumeric display. Another feature will highlight protocol tags in colors to help you spot the header fields and their values for HTTP and data formats for HTML and XML.
Packet sniffer insights
Depending on the packet sniffer you choose, this category can give you a range of insights into your network’s performance. A packet sniffer is more usually used for on demand analysis to give you information on why congestion has occurred. The packet capture and storage functions of a classic packet sniffer creates large volumes of data, and so you won’t want to leave one turned on all the time.
NetFlow analyzers that reap summaries of packet information provided by routers are more suitable for constant monitoring scenarios. These tools can be left running in order to alert you when surges in traffic occur and when a constant rise in traffic threatens to congest your network. These insights are useful as part of intrusion detection plans and also to help you introduce traffic shaping in order to give you the best value from your network infrastructure budget. Being able to head off congestion in the short term, and plan for the expansion of services will prevent you from losing time with firefighting.
By introducing a packet sniffer to your support toolset you can head off problems and reduce demand on your Help Desk, thus freeing up staff for more constructive network administration activities.
Packet sniffer selection
As with any category of networking utility, packet sniffers range from quick, free command line data dumps to sophisticated traffic visualization tools. Your choice of tool really depends on your budget, the complexity of your network, and the types of network administration tools that you already have.
Some of the tools on this list border on illegal, in that they are advertised as security and monitoring utilities but are often used by hackers. Ettercap outright advertises itself for use by hackers. Although you may not want to be associated with such utilities, getting to know the methodologies of network intrusion will help you defend your network from attack. The “ethical hacking” tools included in this list have detection and blocking features that make them useful for thwarting hackers.
High-end packet sniffers, such as those produced by SolarWinds, ManageEngine, and Paessler, are so comprehensive they could more accurately be described as network monitoring systems rather than just plain packet sniffers.
Alternatives to packet sniffers
Packet sniffers are not universally popular. You may find that others in your organization block your plans to install one. This is because packet sniffers capture data in transit over the network and it is normal procedure to store that data in a file for analysis. However, if your company keeps sensitive information or personal data, the CIO may not allow you to copy data at will.
A packet sniffer is a type of network traffic analyzer. However, not all network traffic analyzers are packet sniffers. It is possible to get traffic information without examining passing data packets.
Router manufacturers include messaging and reporting systems in the firmware of their products. Examples of this are NetFlow by Cisco, J-Flow from Juniper Networks, NetStream by Huawei and a non-proprietary network messaging system called sFlow. These reporting standards offer an alternative method to measure network traffic flows that don’t require any packets to be copied off the network.
Packet sniffing issues
It is easy to see why many organizations regard packet sniffers with distrust. In these cases, there are alternative network monitoring methods to look out for. Packet sniffers have a role in a network administrator’s toolkit and some circumstances might arise in which you really need to look at passing packets to resolve a traffic problem on your network.
You may not feel the need to install and maintain a packet sniffer permanently on your network. However, in emergency situations, knowing where to find a free packet sniffer to examine protocol performance on your network can help get you out of a hole very quickly.