When most people think of a directory the first thing that comes to mind is a telephone book. Opening up a phone book and searching through the pages can tell you lots of information about the businesses and people in your local area. A directory service isn’t so different from this in that it acts as a centralized catalog of important information within an enterprise.
>>>Jump to the directory service monitoring tools<<<
A directory allows privileged users throughout an enterprise to look up sensitive information. This includes everything from the names of staff to pay grades. Access is controlled via login credentials to ensure that confidential information stays protected. In this article, we look at what directory services are and why organizations use them.
Contents
- 1 What is a Directory Service? (What is Directory Networking?)
- 2 A Brief History of Directory Services
- 3 LDAP: The Protocol Behind Active Directory and OpenLDAP
- 4 Modern Directory Service Products
- 5 Why do I need a Directory Service?
- 6 Reasons Why You Don’t Need a Directory Service
- 7 Deploying Directory Services (A Look at Active Directory)
- 8 Directory Service Monitoring
- 9 The Future of Directory Services
- 10 Directory Networking: A Necessary Evil
What is a Directory Service? (What is Directory Networking?)
A directory service is a central point of control that enables users to locate and manage resources throughout their network. This information may be accessed from a centralized location but the data itself is generally stored in a distributed format (in the form of a database). This database should change with your network infrastructure and be independent of any physical location.
There are a number of basic components that make up a full-fledged directory service; one of these is that data can be separated into numerous different physical locations. Different physical locations ensure that there is no single point of failure vulnerable during a network disaster.
The directory service also needs to offer users a way to search through its database. This way you can quickly find information on all facets of your network storage. There are many different forms of directory services, these include:
- LDAP – Lightweight Directory Access Protocol (LDAP) is a protocol that allows a user to store and search for records on individuals and groups.
- Key File – This is a text file that contains a hashed password that is linked to groups to which the user belongs. In order to use the Key File, you need to have HTTP authentication.
- Digest File – This is used to store information on entities and users based on their username and password (encrypted).
A Brief History of Directory Services
One of the key milestones in the history of directory services is that of the production of Microsoft Active Directory in 1999. Active Directory was designed as a solution to allow the user to manage a diverse range of IT infrastructure and applications. This service took root because most organizations were using IT environments almost entirely comprised of Windows products. Therefore it made sense to deploy a solution designed specifically for this purpose.
All this started to change once Windows started to be challenged as Mac and Linux products began to grow more popular. Companies were implementing new devices into their environments that weren’t produced by Microsoft and shaking up traditional enterprise networks. However, this was just the tip of the iceberg. What started out simply as new hardware providers entering the scene evolved into a wave of new disruptive technology.
As companies like Google and Amazon started to deploy cloud-driven services like G Suite and Amazon Web Services (AWS) the needs of enterprises across the world became much more complex. As a result, organizations started to move away from Active Directory.
While there have been patchwork solutions in the form of Identities and Access Market Solutions (IAMs) such as single sign-on web apps and password managers, these haven’t quite bridged the gap. While Active Directory works well with Windows products it hasn’t been able to keep up with the multi-vendor, cloud-based demands that are commonplace within larger organizations today.
LDAP: The Protocol Behind Active Directory and OpenLDAP
Lightweight Directory Access Protocol (LDAP) is a protocol that dictates how information is organized and stored when placed inside an LDAP directory. This useful protocol was originally created by Tim Howes and a number of other academics at the University of Michigan in the early 1990s.
Initially, when LDAP emerged it was a little-known replacement for X.500 directories; today it is behind services such as Microsoft Active Directory and OpenLDAP. Almost every directory service you encounter makes use of LDAP. You’ll also see these services support the use of X.500, DNS, NIS, HTTP, DSML, SCIM and NDS.
Modern Directory Service Products
Microsoft Active Directory
Microsoft Active Directory is one of the market’s leading directory networking products. Many organizations have chosen Microsoft Active Directory on account of its compatibility with organizations looking to keep infrastructure on premises. This directory service is best avoided by those who plan to adopt multi-environment solutions such as cloud services which span multiple geographical areas.
How does Active Directory Work?
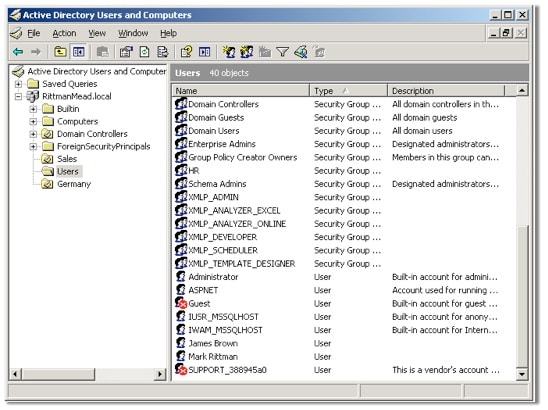
An Active Directory is used to store information about objects on a network. This includes hardware, services, and other applications. The idea is to enable an administrator (or other privileged users) to search through records and access important information. All the information stored within Active Directory is hierarchical and provides the user with a top-down perspective.
Every object has its own identification information referred to as a characterization schema. This dictates how the object is used on a network and can be used to tell apart different elements. The overall hierarchy of Active Directory is comprised of three levels; forest, tree, and domain. The forest level allows the user to see all objects. A tree is effectively a collection of domains that have one parent object.
On the other hand, a domain is a group of network elements that share the same Active Directory Database. The distinction between a tree and domain is that a tree is comprised of multiple domains. An administrator uses these views to perform updates on key equipment and allow or restrict user access to specific applications. With Active Directory the user can manage their network from a centralized location.
OpenLDAP
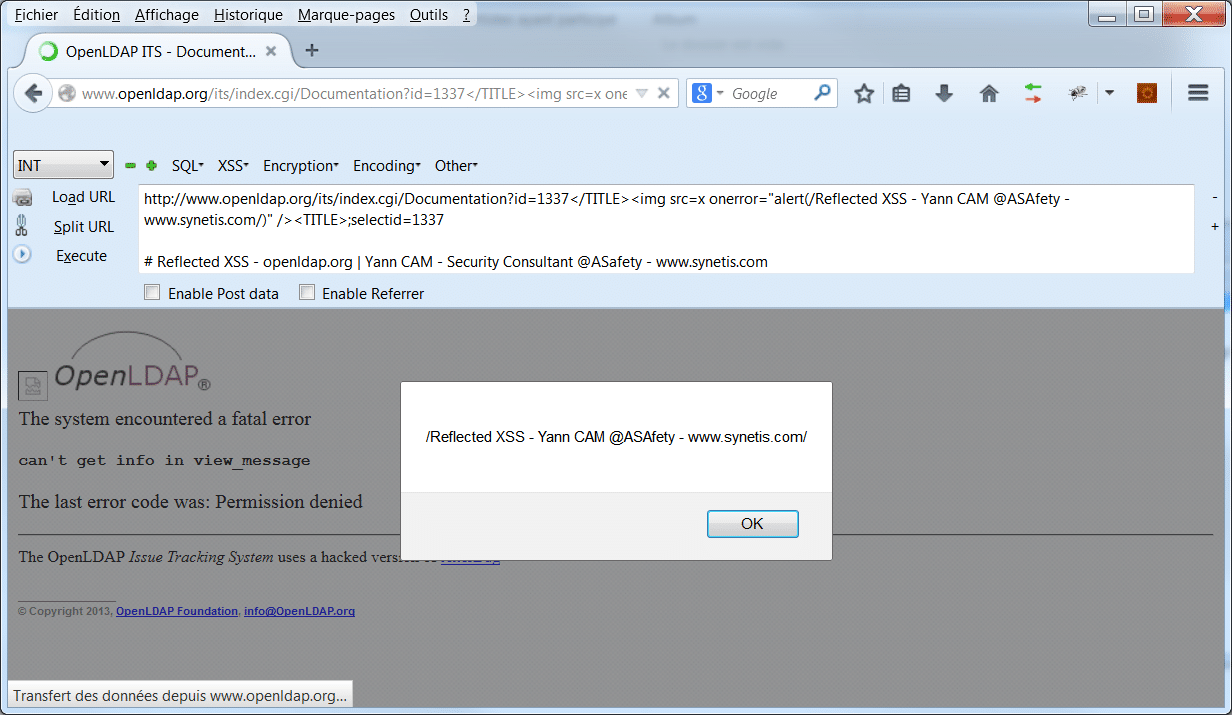
Another option is OpenLDAP. OpenLDAP is an open-source solution that can be tricky to implement but is excellent for organizations that need to monitor Linux or other high maintenance applications. You can also automate some of your management activity. The only issue with OpenLDAP is that if you need protocols such as SAML and RADIUS then this choice is far from ideal.
How does OpenLDAP work?
As the name suggests, OpenLDAP features the use of LDAP, which is a lightweight protocol used to gain access to a X.500 driven directory service. LDAP is based extensively on entries. Each entry has a Distinguished Name (DN) which is used to clearly differentiate entries from each other. Every entry is provided with a type and multiple values. Some common types are cn (common name), mail (email address) and jpegPhoto (JPEG image in binary).
The simplest way to summarise LDAP is to say that it uses a client-server model. A single or multiple LDAP servers contribute data to the directory information tree. LDAP has its own method of authentication which allows users to prove their identity before having access to sensitive information.
JumpCloud Directory-as-a-Service
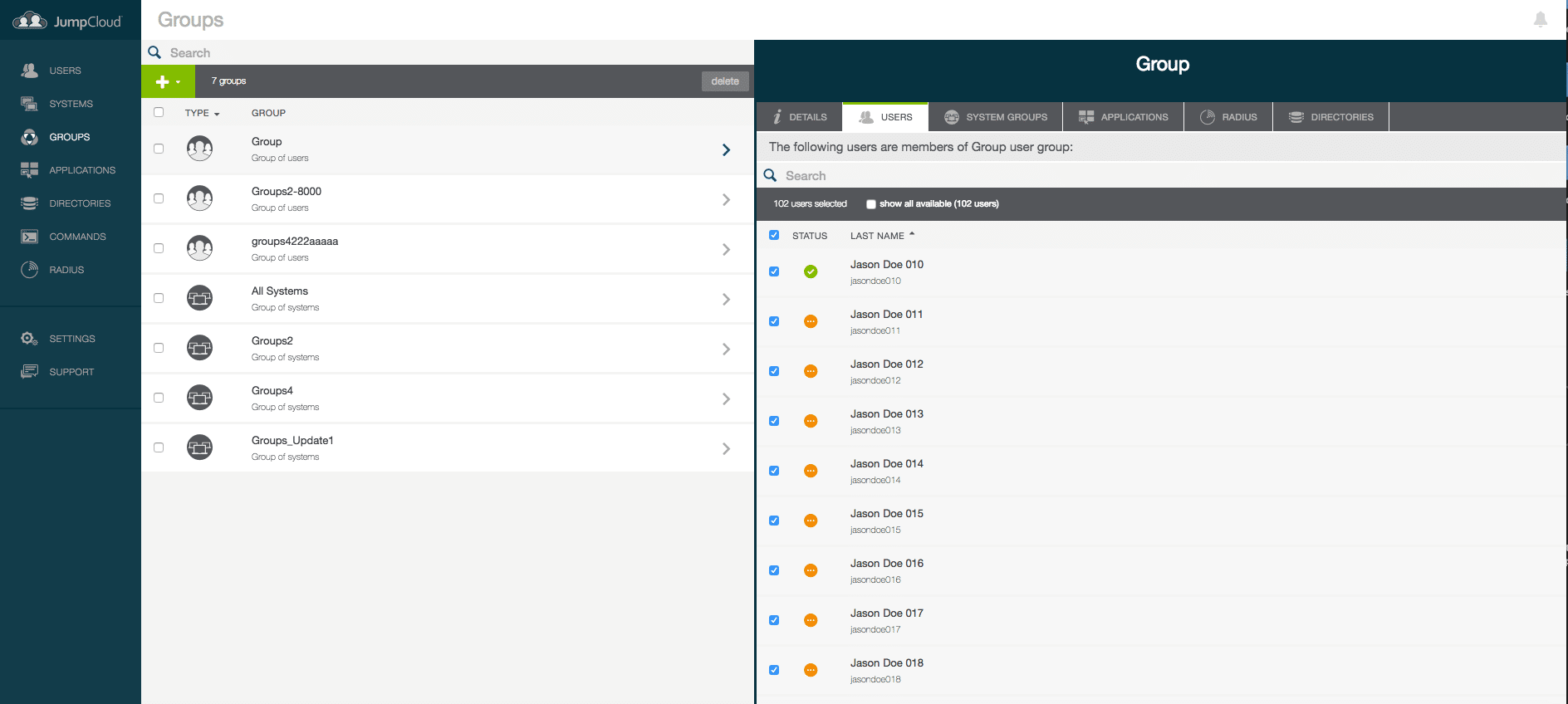
JumpCloud Directory-as-a-Service (DaaS) is a type of directory networking best utilized by companies that are looking to incorporate cloud technology. The cloud directory allows you to manage onsite and remote systems without any issues. As a result, this is perhaps the most modern type of directory service available. This solution works whether you are operating a mixed machine environment (with Windows, Linux and Mac devices); the SaaS approach can minimize the inconvenience of cross-operation.
How does JumpCloud Directory-as-a-Service Work?
Jumpcloud DaaS provides users with a cloud service where they can manage users securely. The advantage of this solution is that you don’t need to maintain any servers on your site, everything is done independently of infrastructure. Obviously taking such an approach is a risk, which is why JumpCloud has provided a number of security provisions. You can encrypt your data and manage passwords with on or offline authentication.
In the event that someone attempts a brute force hack into your device, JumpCloud will flag it and raise an alert. Perhaps the most useful thing about this new style of directory services is that you can conduct RESTful commands. RESTful commands give you a greater say over your infrastructure management.
Why do I need a Directory Service?
As an organization, your staff is one of your most important assets. While directory services can be used for physical infrastructure and other things, they are mainly used to record information about staff. Recording staff information on a directory service means that an administrator can access it easily and solve problems when they arise.
It is also recommended for businesses that deal with external clients on a face-to-face basis. For example, in a doctor’s surgery when a visitor walks in the receptionist would use a directory to view information pertaining to the customer at hand. In a large enterprise with hundreds of staff, a directory service acts as a means of finding information about certain employees while keeping information confidential.
Reasons Why You Don’t Need a Directory Service
Your Organization is too Small
The main reason why an organization wouldn’t need a directory service is that it may be too small. A business with limited staff and infrastructure doesn’t need a centralized solution in order to be managed. Within small organizations, most administrators can manage connections manually without the need for a specialized product. This approach becomes problematic when an organization needs to upscale and the administrator cannot realistically track all connections manually.
Cloud Services are Your Bread and Butter
A directory service may not be a good idea if you don’t have much if any on-premises infrastructure. Organizations operating mainly within cloud services are generally unable to manage directories. In order to use a directory service, the organization has to take on infrastructure such as servers alongside additional software to safeguard against security threats. This simply isn’t worth the investment for organizations that are estranged from traditional infrastructure.
Your Infrastructure is Too Modern
Many organizations are working in environments with multiple operating systems and complex SaaS solutions like Salesforce which have helped to throw traditional network structures out the window. Products like Microsoft Active Directory have been struggling to keep up with the rate at which modern networking has changed. The consequence is that organizations have stepped away from directory services as they can’t manage modern infrastructure effectively.
Cost
A directory service is as much of a liability as it is an asset. Once a directory service has been deployed it needs to be managed constantly in order to be effective. There is also the significant cost of the hardware and software that needs to be in place to sustain such a solution. It is no surprise that many organizations are hesitant to incorporate Directory services because of this.
Deploying Directory Services (A Look at Active Directory)
As outlined above, Microsoft Active Directory is one of the most used services of large organizations. While Active Directory will configure topology in a standard manner, many organizations would be better off creating custom designs. This can be a little more complex but has the advantage of simplifying an enterprise network management. One of the main ways this is achieved is by selecting your domain structure.
It is incredibly common to see larger organizations use one domain per office site but there are many ways to structure domains. You can also set your domain structure based on user domains, resource domains or your topology. With user domains, you could provide selected individuals in an organization with single user domains. This would allow them to manage accounts while keeping all data protected.
An alternative option is to create resource domains. Under this model, you can group devices under one umbrella domain. The advantage of doing this is that you can segregate the management of your key services. So you can group the management of devices like desktop computers and Hyper-V servers.
Finally, you can organize your domains by the geography of your physical infrastructure. Every office should be organized within one Active Directory location. A good rule of thumb is to provide each location within a unique subnet. The reason is that one subnet can’t operate across multiple sites.
Directory Service Monitoring
Directory services are an effective way to manage your network but they also need to be monitored. There are a variety of ways you can monitor the performance of your directory service, depending on the product provided and set up. One of the most common ways to do this is to use a network and application monitoring service. For example, a tool like Site24x7 can be used to help run troubleshooting on an Active Directory service.
A tool like Site24x7 Directory Service Monitor can help you to flag domain controller issues, replication failure, and user account lockouts. You don’t necessarily have to pay extra money to monitor your directory service either. Paessler PRTG has its own free Active Directory monitor which can flag replication errors and monitor your services for any problematic activity.
Of all the complications that come with deploying a directory service, it can be tempting to overlook the monitoring phase. However, this is a mistake as a directory service is just like any other active service on your network; it needs to be maintained. While you can do this manually to some extent even the most skilled administrator can’t keep up with every little change.
Site24x7 Directory Service Monitor (FREE TRIAL)
Site24x7 is one of the most complete cloud-based observability and monitoring platform developed by Zoho Corporation. It has introduced many important updates in 2025. When it comes to directory service monitoring, Site24x7 is a solid option thanks to its built-in Active Directory monitor. Once the Windows agent is installed on a domain controller, the platform begins tracking detailed performance and security metrics. With it, admins can monitor domain controller health, LDAP session activity, and replication status from a central cloud dashboard.
The platform shows directory read and write operations, and alerts on replication issues or policy changes, among other features. LDAP statistics like active sessions, threads, and bind operations are also available. For on-prem environments, the setup is quick and easy. The Windows agent handles data collection and sends it to Site24x7 without you needing to change anything at the firewall level. Azure AD isn’t monitored directly, but logs can be streamed for analysis.
Site24x7 is available as a cloud service with a 30-day free trial.
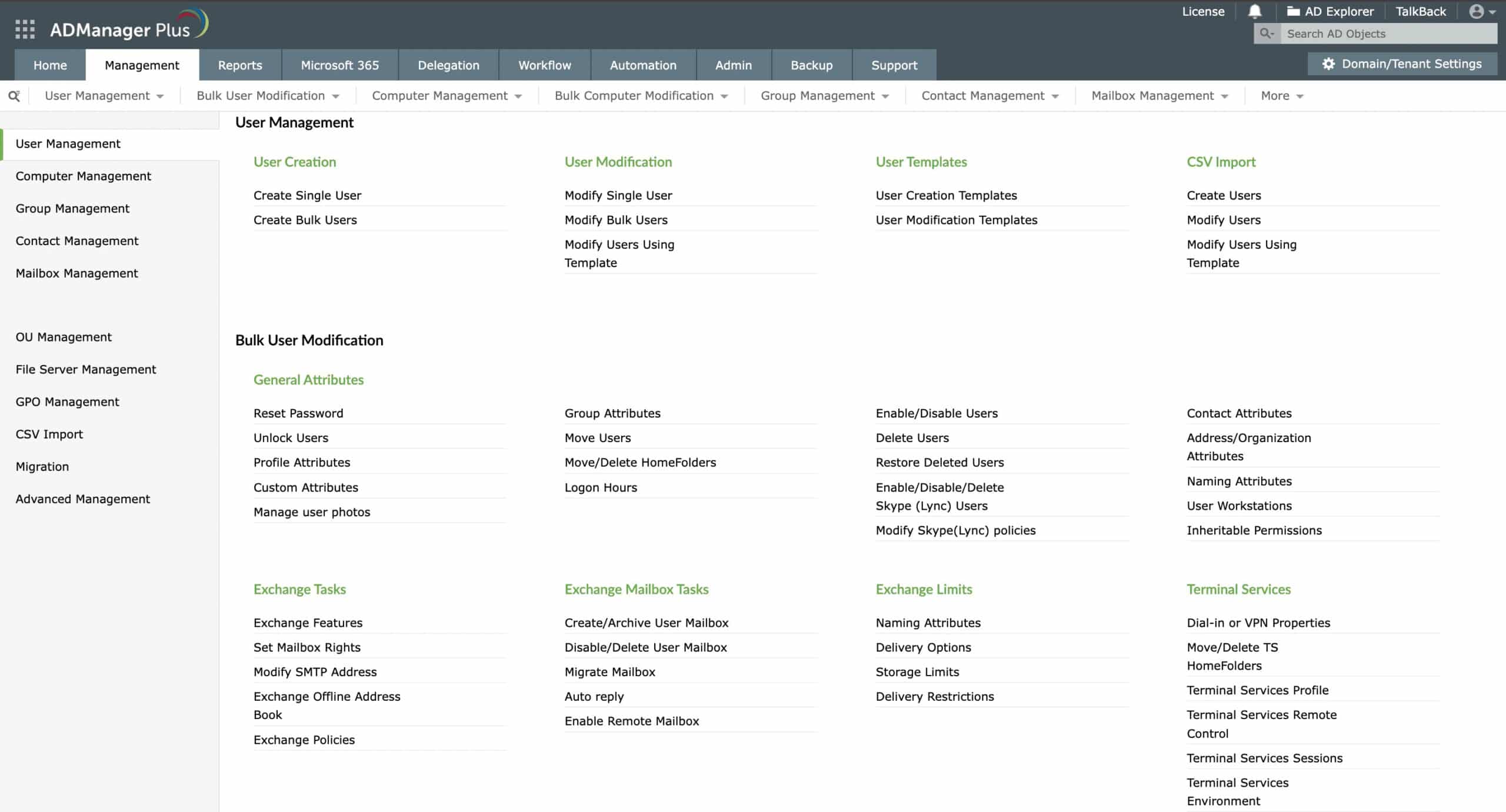
ManageEngine ADManager Plus (FREE TRIAL)
ManageEngine ADManager Plus is an advanced Active Directory monitoring and management tool that eases the work of administrators without compromising on security and control. With this tool, you can manage AD users, computers, and groups through a single console. Also, you can automate AD tasks, delegate roles, manage bulk users through predefined template options or CSVs, move users across OUs, and more. You can even force group updates, manage passwords, and streamline access to resources for every employee in your organization. The best part is that none of these actions require PowerShell scripts, and you can do them through an intuitive user interface.
A highlight of this tool is its extensive reports. They provide information about every transaction in your organization. There are also different types of reports that provide insights into just the information you need. Moreover, it supports automated workflows that can save time and effort.
To get a first-hand feel of ADManager Plus, download a 30-day free trial.
Paessler PRTG Network Monitor

Paessler PRTG Network Monitor is another platform that enterprises often use for active directory monitoring. This program even has its own Active Directory Monitor that is designed to recognize replication errors, logged out users and group membership. The PRTG Active Directory Replication Errors Sensor has the ability to monitor multiple domain controllers and produce an alarm if any problematic activity occurs.
This sensor provides you with a wealth of information on any active directory replication error that occurs. For instance, you can view the number of consecutive synchronization errors, if the source was deleted, the time of last synchronization attempt and if it was successful. This provides you with the basics you need to gain transparency over your active directory service and Paessler offers a 30-day free trial for download, which remains free as long as you use up to 100 sensors.
SolarWinds Server and Application Monitor
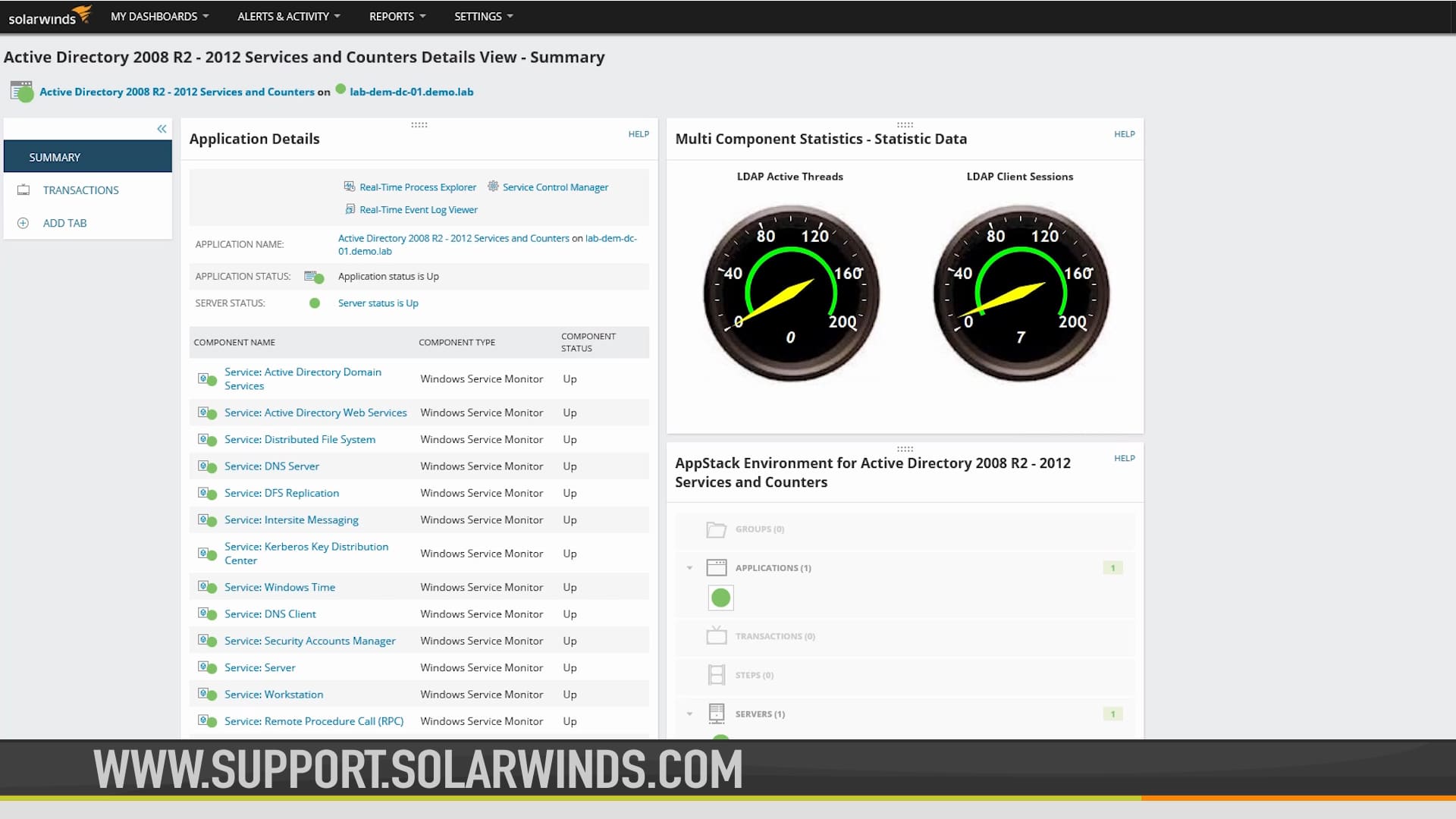
SolarWinds Server & Application Monitor is one of the most widely used tools for directory service monitoring. One of the reasons why its so widely used is its excellent support for Active Directory. Active Directory management is an area where SolarWinds Server and Application Monitor performs extremely well. For instance, you can monitor the active directory, physical and virtual environments from one location.
With regards to Active Directory itself, SolarWinds Server and Application Monitor can also be used to monitor the domain controller for failed login attempts, performance issues, and audit policy changes. You can also view password change attempts, reset attempts and deleted user accounts as well. SolarWinds Server & Application Monitor is available for download on a 30-day free trial.
The Future of Directory Services
At this point, it is indisputable that directory services are in a constant state of motion. In many ways, this has been triggered by the growth of cloud services. Cloud solutions have expanded the functionality of directory services so that identities can be managed through the cloud. This is appealing because it allows organizations to utilize a directory on a location independent basis.
The next step in the future is for directory services to enter into a blend of Active Directory and LDAP. Creating a hybrid SaaS/cloud service (Directory as a Service) would eliminate many of the concerns raised by manual configuration and installation. It would also reduce the administrator’s concerns to ensure the security of these external systems.
Directory Networking: A Necessary Evil
Directory services are one of the best-kept secrets of larger organizations’ internal processes. A directory service may not catch your attention as the most important system within an organization but it is nonetheless a very useful tool. Being able to take a hierarchical look at users, applications, and devices helps to make sure that everything is running smoothly.
Smaller organizations can get by on the “old school method” of having an administrator mentally keep track of users and devices but that simply doesn’t cut it for larger companies. While directory services are not an infallible solution and need to be monitored, they do streamline the enterprise management process.
Implementing a directory service is particularly relevant for those organizations that have deployed a diverse range of systems or cloud services. The further away from a traditional legacy structure, you move, the more you should consider integrating a directory service into your network environment. In many ways, they are a necessary evil.