In today’s digitally connected world, organizations are moving towards tools that help them organize and protect data. One of the most daunting tasks for an organization is data management and security. Fortunately, technology has paved the way toward more effective and efficient tools, including data identification tools, otherwise called Personally Identifiable Information (PII). In this post, we’ll give an overview of what PII scanning tools are, why do organizations need PII, and a list of the best ones:
What Are PII Scanning Tools?
To understand the gist behind PII scanning tools, you’ll first need to know the definition behind PII. PII stands for Personally Identifiable Information that contains all types of an individual’s data from personal information like date of birth, passport, driver’s license, mailing address, e-mail address, contact number, and insurance numbers to banking records, transactions history, credit card number, registered ID, account details, IP addresses, etc. Depending on the industry and company’s scale, some organizations like hospitals store more sensitive data of their customers than others.
PII scanning tools are software that identifies and tracks the data that goes into the system. Organizations need to know where their PII is located and stored. Not only does this help them in data discovery, but also to keep up with data protection laws and regulations. Suppose an organization is not using PII scanning tools for data protection. In this case, the chances of data breach and loss increase and puts the organization at the hands of penalties, liabilities to fines, and maybe even a lawsuit. PII scanning tools enable companies to keep data breaches at bay and maximize data security.
What Are the Benefits of Using PII?
PII scanning tools let organizations dive into a world of automation, where everything is located, stored, and protected with a single click. But why do organizations’ need PII in the first place, in other words, what do they do with this data?
Technological advancements have a two-fold benefit – 1) It allows organizations to advance quickly and keep up with the time, and 2) It has changed the way customers interact with organizations. PII empowers organizations to discover, analyze, and use customers’ data to their advantage. It has made it easier for companies to identify data, extract it, and attain more in-depth analysis. Where they needed to manually discover and store data previously, PII automates this process and makes it more precise.
The Best PII Scanning Tools
Now that you have an understanding of what PII scanning tools are, it’s time to dive into the top-rated
PII scanning tools in the market. We’ll discuss the features and pros and cons of each.
1. ManageEngine Endpoint DLP Plus (FREE TRIAL)

ManageEngine Endpoint DLP Plus is a sophisticated data loss prevention software specifically designed for protecting Personally Identifiable Information (PII) across endpoint devices. It addresses the critical need for organizations to secure sensitive data, preventing unauthorized access and potential data breaches, with a strong emphasis on PII scanning capabilities.
Key Features:
- Advanced PII Detection: The software employs deep content inspection to identify and categorize various forms of PII, such as social security numbers, credit card details, and personal health information, across endpoint systems. This capability ensures that sensitive data is accurately detected, regardless of where it resides.
- Contextual and Content-Aware Policies: Endpoint DLP Plus utilizes contextual analysis to understand the circumstances under which PII is accessed or transmitted. This allows for more precise control and minimizes false positives, enhancing both security and user productivity.
- Real-Time Monitoring and Alerts: Real-time scanning and alerting mechanisms ensure immediate detection of unauthorized PII access or transmission. This prompt response capability is vital for mitigating potential data leaks and addressing compliance requirements swiftly.
- Comprehensive Reporting and Auditing: The solution provides detailed reports and audit trails that document all activities involving PII. This feature is invaluable for compliance audits and internal reviews, ensuring that organizations can verify and demonstrate their adherence to PII protection standards.
- Automated Remediation Actions: In cases of policy violations, Endpoint DLP Plus can automatically enforce remedial actions, such as quarantining sensitive files or blocking data transmissions. This reduces the risk of human error and ensures consistent enforcement of security policies.
Why do we recommend it?
ManageEngine Endpoint DLP Plus is a package of data loss prevention tools that focus on the protection of sensitive data. This service will scan all endpoints in a search for PII and compile a data inventory. This database holds the file name and path of each location of PII. The service is then able to protect those files.
I appreciate Endpoint DLP Plus for its streamlined interface, which simplifies the management of PII protection policies and the review of incidents. The software’s design facilitates a quick setup and efficient ongoing management, even for users with limited technical expertise.
Despite its comprehensive scanning capabilities, Endpoint DLP Plus is engineered to have minimal impact on system performance. This ensures that endpoint devices maintain optimal functionality without compromising on security.
With its robust PII scanning and protection capabilities, Endpoint DLP Plus significantly enhances an organization’s security posture. It helps meet strict regulatory requirements for data protection, such as those outlined in GDPR, HIPAA, and other privacy laws, by providing thorough coverage against potential PII breaches.
Who is it recommended for?
This service is suitable for all sizes of businesses. Small enterprises will be interested in the Free edition, which provides all of the services of the paid version but it is limited to monitoring only 25 endpoints. The package doesn’t just discover PII but it protects the files that contain it. Methods track data movements and log, block, or allow those transactions.
Endpoint DLP Plus is particularly effective for organizations with a critical need to protect PII. Its sophisticated detection technologies, combined with powerful policy enforcement and auditing tools, offer a high level of security against data loss and unauthorized data exposure. For enterprises that handle sensitive information routinely, Endpoint DLP Plus represents a reliable, comprehensive solution for PII protection. Start a 30-day free trial.
EDITOR'S CHOICE
ManageEngine Endpoint DLP Plus is our top pick for a PII scanning tool because it is able to discover and classify sensitive data, utilizing the PII definitions of a range of data privacy standards. This system uses templates and the administrator needs to select one from the library before performing a system scan. It is also possible to create a custom template. The service is able to operate several standards simultaneously. After discovering and classifying sensitive data, the service creates a sensitive data inventory. That provides administrators and the data protection process a list of files that need to be protected. The package uses containerization to protect those files and control access.
Download: Access a 30-day FREE Trial
Official Site: https://www.manageengine.com/endpoint-dlp/download.html
OS: Windows Server
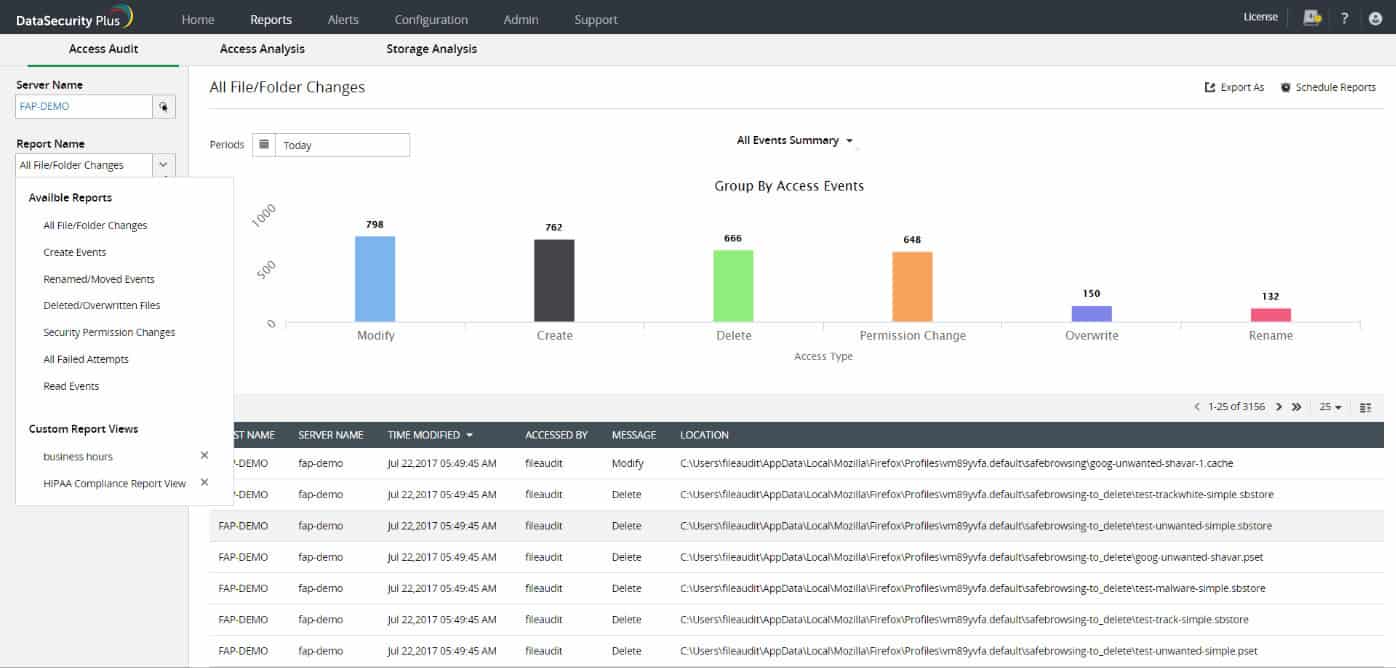
2. ManageEngine DataSecurity Plus (FREE TRIAL)
ManageEngine DataSecurity Plus is also an excellent and well-known PII scanning tool. Although this tool does not have a cloud version, it operates best on Windows devices. For instance, if you are searching for a software that finds and analyzes sensitive personal data, such as electronically protected health information (ePHI) or personally identifiable information (PII), stored in Windows-managed file servers, failover cluster environments, or Microsoft SQL servers, ManageEngine DataSecurity Plus is just what you need.
Why do we recommend it?
ManageEngine DataSecurity Plus goes beyond data scanning, offering features like access rights management improvement, parallel and incremental scanning for efficiency, and additional functionalities including top-notch inventory management, multi-factor authentication, data encryption, and role-based access. Focused on Windows-managed file servers, failover cluster environments, and Microsoft SQL servers, this tool excels in finding and analyzing sensitive personal data like ePHI or PII. It creates a comprehensive sensitive data inventory, cataloging information such as passport numbers, national IDs, credit card data, and financial data. The tool’s accurate detection capabilities leverage rules, regulations, regular expressions, and keyword sets to pinpoint exact matches, ensuring thorough compliance enforcement.
Once this tool has scanned for such business-critical data, it creates a sensitive data inventory by locating and cataloging passport numbers, national IDs, credit card data, and financial data. Additionally, you can detect sensitive data accurately with the help of ManageEngine DataSecurity Plus’ rules and regulations. Search for regular expressions or specific keyword sets, and you will find the exact matches. You can also analyze, rearrange, and improve your access rights management by using ManageEngine DataSecurity Plus, which will further assist you in enforcing compliance with ease.
Your system carries a lot of loads, which can have a significant impact on performance and can reduce efficiency if raised above a threshold level. ManageEngine DataSecurity Plus has come up with a way to increase efficiency by minimizing the load. Instead of wasting critical business hours on scan times, the tool’s software uses parallel and incremental scanning capabilities to manage the entire data scanning process with ease.
Who is it recommended for?
ManageEngine DataSecurity Plus is recommended for businesses and organizations operating in Windows environments that prioritize efficient and accurate PII scanning. Ideal for those seeking comprehensive data protection and compliance enforcement, this tool is suitable for managing sensitive data in various forms, including passport numbers and credit card information. Its parallel and incremental scanning capabilities make it efficient for large-scale operations, and additional features like multi-factor authentication and role-based access enhance overall data security. Trusted by major companies like Toyota, Sony Music, and Xerox, ManageEngine DataSecurity Plus is a robust choice for managing and protecting sensitive data effectively.
Additional features of ManageEngine DataSecurity Plus include top-notch inventory management, multi-factor authentication, data encryption, and role-based access. These features and advantages were more than enough to convince large-scale businesses such as Toyota, Sony Music, and Xerox to use ManageEngine DataSecurity Plus for managing and protecting their data. Start with a 30-day free trial.
3. Egnyte

There might be several candidates as to which PII scanning tool is the best, but there is no debate whatsoever that Egnyte is among the most successful and trusted tools for PII scanning.
Why do we recommend it?
Egnyte stands out as one of the most successful and trusted PII scanning tools, providing a robust platform based on unified cloud content. Operating as a Software as a Service (SaaS), Egnyte offers a secure environment for compliance, data security, threat detection, and collaboration. Its strength lies in the combination of human and machine-generated metadata, enabling users to search storage platforms, device applications, and repositories seamlessly. As an AI-supported software, Egnyte is certified by ISO/IEC and SOC 2, as well as CCPA compliant, ensuring the highest standards of security and compliance for sensitive data.
The basic idea behind Egnyte’s infrastructure is to provide its clients and users with the only platform based on unified cloud content. If you are a multi-cloud business owner who is looking for a highly secure environment for compliance, data security, threat detection, and collaboration, Egnyte is your perfect solution.
Operating as a SaaS or Software as a Service, Egnyte offers several services such as searching for storage platforms, device applications, and repositories. Azure and SharePoint are a couple of cloud collaborative platforms that you can look up with Egnyte. This PII scanning tool is powered by both human and machine-generated metadata and is programmed in such a way that it allows its users to share data with both internal and external groups. Another plus point of Egnyte, which also happens to be an AI-supported software, is that it is certified by ISO/IEC and SOC 2 and is also CCPA compliant.
Who is it recommended for?
Egnyte is recommended for multi-cloud businesses seeking a highly secure and compliant solution for PII scanning. It caters to organizations requiring a unified cloud content platform for effective collaboration, threat detection, and data security. With its diverse range of services, Egnyte suits businesses utilizing cloud collaborative platforms like Azure and SharePoint. The tool’s certification and compliance with ISO/IEC, SOC 2, and CCPA make it an ideal choice for businesses prioritizing the protection of sensitive data against both internal and external threats. The seamless functionality, whether used online or offline, adds to its appeal for over 17 thousand businesses and firms utilizing its services.
With the help of Egnyte, you can locate all the sensitive data, control any risks, and protect this valuable data from all sorts of threats, whether they are internal, such as accidental data deletion, or external, such as data infiltration. Moreover, its functionality is so perfect and seamless that the software works smoothly when used both online and offline. Due to these features and benefits, almost 17 thousand businesses and firms utilize the services of Egnyte, which is why you should consider this tool too.
If you wish to know more about Egnyte, you can look them up here.
4. Nightfall
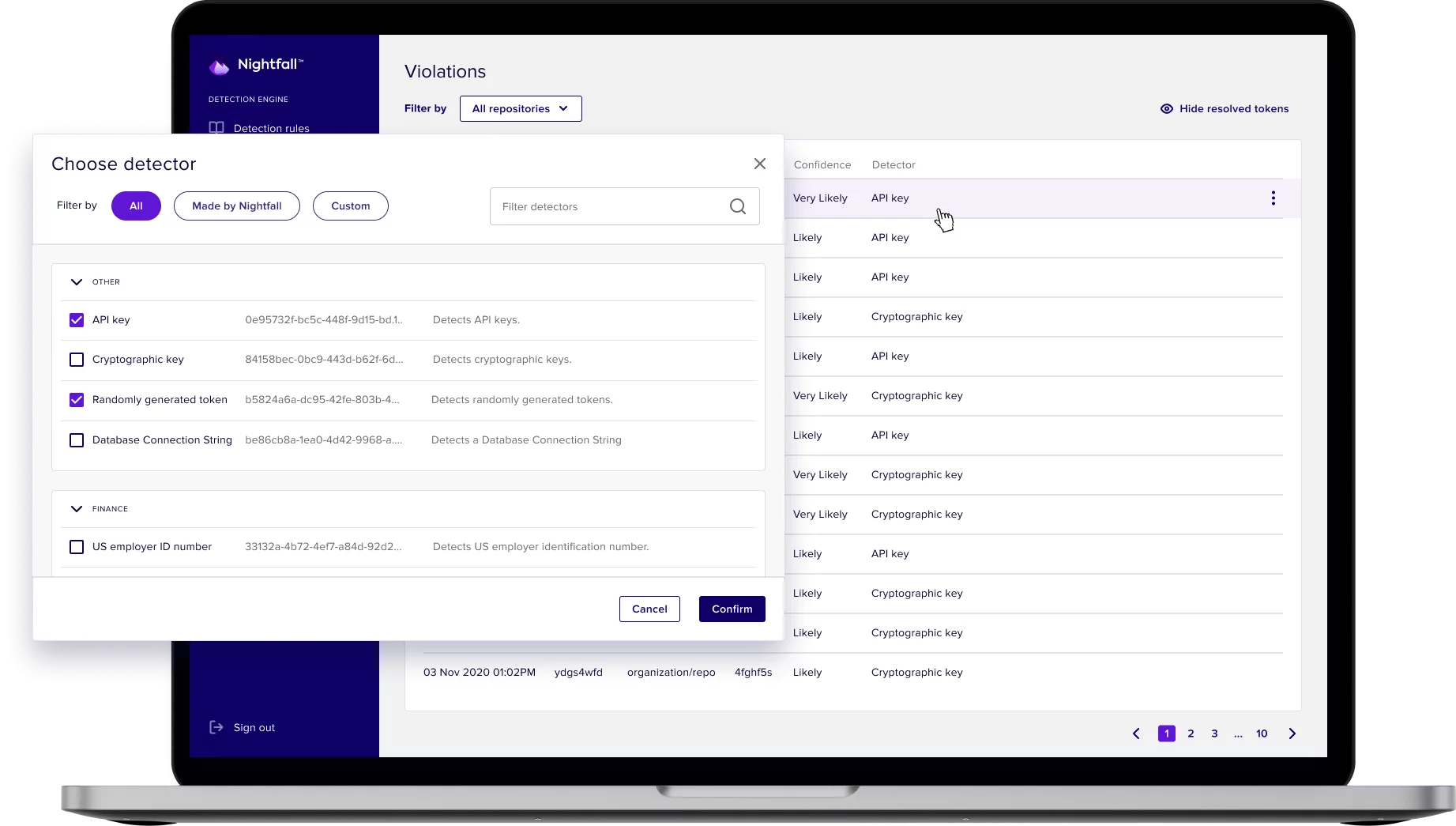
Nightfall is another web-based Saas tool that utilizes machine learning for PII scanning. The configuration of the software aids in determining how to handle all the sensitive data. Being a cloud-based security platform, Nightfall also works best with apps like Google Drive, GitHub, Slack, and Atlassian to solve critical data problems and prevent data loss. With the help of Application programming interfaces or APIs, you or your team can delete unwanted data, prevent data loss, quarantine data, and trigger alerts.
Why do we recommend it?
Nightfall is a web-based SaaS tool employing advanced machine learning for PII scanning, making it a robust choice for organizations prioritizing data security. As a cloud-based security platform, Nightfall seamlessly integrates with popular apps such as Google Drive, GitHub, Slack, and Atlassian, addressing critical data concerns and preventing loss. Its configuration options empower users to determine how sensitive data is handled, offering capabilities like data deletion, prevention of data loss, quarantine, and alert triggering through APIs. Nightfall provides a range of templates to establish sensitive data controls, ensuring compliance with data security initiatives like CCPA, HIPAA, GDPR, and PCI DSS. Leveraging deep learning concepts, it excels in detecting structured and sensitive data such as credit card numbers, credentials, secrets, and emails.
By using the numerous templates provided by Nightfall, you can set up sensitive data controls to satisfy data security initiatives and become CCPA, HIPAA, GDPR, and PCI DSS compliant. Nightfall provides you with a variety of deep learning concepts which can be applied to leverage standard detectors of structured and sensitive data such as credit card numbers, credentials, secrets, and emails. Moreover, Nightfall is also an AI-supported cloud-native software system with the help of which high-level data protection and data loss prevention are possible. Not only that, but it also monitors all the data flowing into and out of the servers and classifies it continuously so that none of the important information gets missed out.
Who is it recommended for?
Nightfall is recommended for businesses and organizations seeking an advanced PII scanning solution with a focus on data security. Ideal for those using cloud collaboration platforms like Google Drive and Slack, Nightfall’s API-driven capabilities enable efficient data management, including deletion, prevention, and alerting. The variety of deep learning concepts and continuous classification of data flowing in and out of servers make it suitable for organizations requiring high-level data protection and loss prevention. Nightfall’s special Startup Solution caters to new businesses entering the market, while its automation of workflows for data discovery and alerts ensures time efficiency. Trusted by major companies like Tesla, Google, and Facebook Meta, Nightfall is a reliable security system for safeguarding sensitive and valuable data.
There are numerous benefits of using Nightfall as your security system. For starters, Nightfall has a special Nightfall Startup Solution, which is an excellent initiative, especially for business owners and companies that are new to the market. In addition, the Nightfall system detects data loss using raw data and automates workflows for data discovery, alerts, and deletions, which save you a significant amount of time. No wonder business tycoons such as Tesla, Google, and Facebook Meta rely on the Nightfall security system to protect their sensitive and valuable data.
To know more about this tool, head up to their website.
5. One Trust

According to a data analysis report published in 2019, One Trust is the leading organization in terms of global data privacy management software market shares, with almost 35 percent of the total shares belonging to One Trust. Ever since its rise, One Trust has continuously and consistently gained the trust of older clients and attracted new customers and is showing no sign of slowing down, let alone stopping.
Why do we recommend it?
One Trust stands out as a global leader in the data privacy management software market, commanding nearly 35 percent of the total market shares. Its consistent growth and widespread adoption showcase its reliability and effectiveness. One Trust’s platform, driven by One Trust Athena and a robotic automation engine, offers an AI-supported system that excels in identifying, analyzing, and classifying sensitive and private data with exceptional efficiency. The tool addresses the high-risk scenarios faced by companies dealing with PHI or PII, providing robust protection against third-party data infiltration. One Trust’s central agile workflow efficiently mitigates third-party risks, emphasizing its commitment to governance, risk management, security, privacy, ethics, ESG programs, and data governance. The platform’s broad-spectrum applicability ensures compliance with various regulations, including CCPA, LEPD, PDPA, GDPR, and ISO27001.
Ranked as the most widely used privacy platform, One Trust provides its customers and clients with several advantages. For instance, the One Trust platform has a strong backbone powered by its One Trust Athena. When coupled with its robotic automation engine, you get an AI-supported system that identifies, analyzes, and classifies sensitive and private data, just like Egnyte, but at a higher efficiency rate. Not many companies solely own their PHI or PII.
These companies are at a high risk of third-party data infiltration. As a result, they are in dire need of a PII scanning tool. One Trust has a central agile workflow that it uses to negate any third-party risks and concerns. Moreover, One Trust claims to focus on providing its clients with GRC, security, privacy, ethics, ESG programs, and data governance, and they have the credentials to back this claim. One Trust has broad-spectrum applicability, as it fulfills several compliance requirements such as CCPA, LEPD, PDPA, GDPR, and ISO27001. For all these reasons, One Trust attracts large businesses and is even on the payroll of various fortune 500 firms.
Who is it recommended for?
One Trust is recommended for businesses of all sizes, particularly those with extensive data privacy management needs. Ideal for companies dealing with PHI or PII and facing high risks of third-party data infiltration, One Trust provides comprehensive protection through its advanced AI-supported scanning capabilities. Its central agile workflow makes it suitable for organizations seeking to efficiently manage third-party risks. One Trust’s compliance with multiple regulations, including CCPA, LEPD, PDPA, GDPR, and ISO27001, makes it an excellent choice for businesses prioritizing adherence to global data privacy standards. Its clientele, including various Fortune 500 firms, attests to its effectiveness and reliability.
You can dig deep into them if you hit up their website.
6. Endpoint Protector

A good PII scanning tool should have a complete data loss protection (DLP) solution. Endpoint Protector not only fulfills this requirement but also has a competent and efficient threat detection system. Due to its top-notch features and excellent functionality, it is recognized as an up-to-the-mark choice and solution in the latest Enterprise DLP Magic Quadrant by Gartner. The working of Endpoint Protector is quite smooth and free-flowing.
Why do we recommend it?
Endpoint Protector is a highly recommended PII scanning tool, acknowledged for its comprehensive Data Loss Protection (DLP) solution and robust threat detection system. Recognized in Gartner’s Enterprise DLP Magic Quadrant, it stands out for its top-notch features and functionality. The software operates seamlessly, conducting thorough sweeps of endpoints to assess the entire data collection and categorizing sensitive data. The central server facilitates auditing of access rights management, enhancing data access permissions. Endpoint Protector’s encryption feature ensures data security, particularly for information stored on USB devices. Its ability to detect account takeovers, intruder activities, and internal threats, along with advanced features like forensics and web filtering, makes it a standout choice.
Once you have specified your security policies and installed all the right stations, the software sweeps all the endpoints to assess the entire data collection. Next, the software categorizes all this data to see which parts are sensitive and valuable. The customer can also use the central server for auditing their access rights management to get better data access permissions. Once this step is completed, the software can encrypt these data locations. If you have your data stored in a USB storage device, you can also encrypt, manage, and secure it with a password in an easy and simple step.
Endpoint Protector also helps you detect any account takeover, intruder activity, or internal threat. The system has an option that profiles all user activities once enabled. Once it starts to monitor all the actions and commands, the system creates a baseline of repetitive everyday activities and makes a standard pattern. If any activity deviates from this standard pattern, you or your team will get a security alert. Other than that, Endpoint Protector has an excellent history of satisfying customers with great offline support, forensics, encrypted algorithms, blended threat protection, HTTPS malware detection, exploiting blockers, and web filtering. No wonder AON, Allianz, Samsung, and Western Union trust Endpoint Protector for their PII scanning.
Who is it recommended for?
Endpoint Protector is recommended for businesses seeking a robust PII scanning tool with a complete Data Loss Protection (DLP) solution. It’s ideal for organizations requiring thorough data assessment on endpoints, efficient categorization of sensitive data, and the ability to audit access rights management for enhanced data access permissions. The encryption feature, especially for data stored on USB devices, adds an extra layer of security. Endpoint Protector’s advanced threat detection capabilities make it suitable for businesses focused on detecting account takeovers, intruder activities, and internal threats. Its history of satisfying customers, including prominent names like AON, Allianz, Samsung, and Western Union, underscores its reliability and effectiveness.
Here is a link to their website if you are looking for more details.
7. Netwrix Auditor
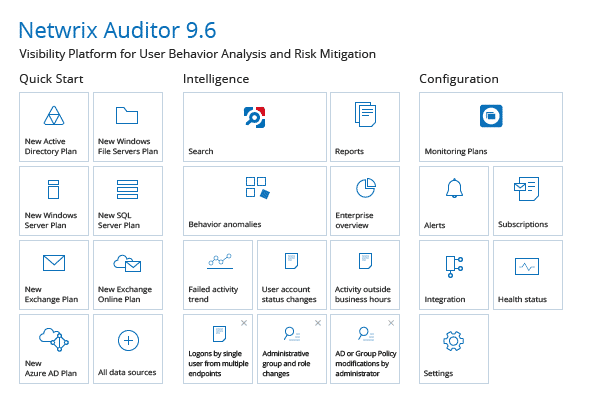
The PII scanning market is flooded with tools that manage and protect data on SharePoint, Office 365, and file servers. In such a tough, competitive environment, Netwrix Auditor has managed to make its way to the top because of its outstanding features and numerous benefits.
Why do we recommend it?
Netwrix Auditor stands out in the competitive PII scanning market for its exceptional features and numerous benefits. It proves to be a significant boost to businesses by efficiently detecting security threats, enhancing team efficiency, and ensuring compliance. The software excels in analyzing sensitive data, identifying infrastructure gaps, and minimizing IT risks by exposing loose permissions. Automated security checks and responses, along with threat pattern alerts, provide accurate and efficient threat investigations, allowing businesses to be proactive against security breaches. Netwrix Auditor’s time-saving capabilities in organizing configuration reports and preparing for audits make it a valuable asset, especially for GDPR and HIPAA compliant firms.
Netwrix Auditor is a massive boost to your business since it detects security threats, increases your team’s efficiency, and proves compliance.
Every firm has sensitive private data, security gaps, and loose permissions which can be exposed. A huge chunk of your critical assets is shared with external third-party members, while many accounts with sensitive data have no passwords or restrictions. Netwrix Auditor analyzes all the data, identifies any infrastructure gaps such as a large number of proactive users, and minimizes the IT risk by exposing loose permissions. Moreover, Netwrix Auditor is programmed to perform automated security checks and responses for more accurate and efficient investigations as well as sending alerts on threat patterns. This way, you will be notified of a security breach before it occurs.
Nowadays, business owners do not have the time to get and organize configuration reports and prepare for audits, and that is where Netwrix Auditor is your savior. With the help of this software, you can not only save up a significant amount of time combing through audit logs but are also saved from the hassle of struggling with log files, spreadsheets, and scripts, which is a key element of GDPR and HIPAA compliant firms.
You can also avail the services of Netwrix Auditor Free Community Edition if you wish to focus on access control regulation. Netwrix, by nature, is an auditing software, with most of its features tilted towards instantaneously dealing with audit requests. In addition, its simple and easy-to-use interface makes it an ideal choice for users who are not that tech-savvy.
Who is it recommended for?
Netwrix Auditor is recommended for businesses seeking a comprehensive PII scanning tool that efficiently detects security threats, enhances team efficiency, and ensures compliance. It is particularly beneficial for organizations dealing with sensitive data, shared assets with external parties, and loose permissions, as Netwrix Auditor effectively addresses these challenges. The software’s automated security checks and threat alerts make it suitable for proactive threat management. Additionally, Netwrix Auditor Free Community Edition is an excellent choice for those focusing on access control regulation. Its user-friendly interface makes it an ideal option for users with varying levels of technical expertise.
You can also lookup their website to get more information.
8. Digital Guardian DLP
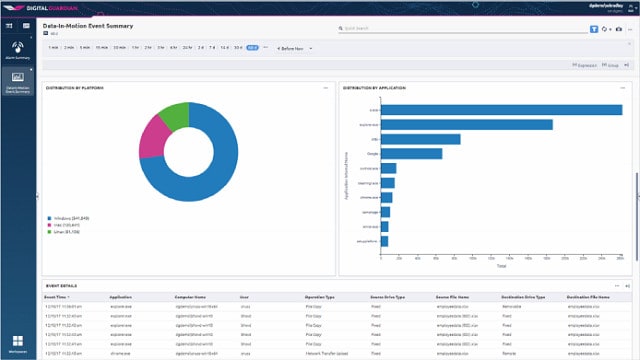
Digital Guardian is another Software as a Service platform that helps in data loss prevention, but what makes this service stand out is that it also offers timely threat detection.
Why do we recommend it?
Digital Guardian Endpoint DLP is a standout Software as a Service (SaaS) platform for data loss prevention, offering not only robust prevention measures but also timely threat detection. Its versatility makes it compatible with Windows, Linux, and macOS devices, providing a cloud-based solution known for its effectiveness. The platform excels in assessing and organizing access rights management, facilitating users in enforcing compliance effortlessly. A notable feature is the eDiscovery sweep, continuously scanning data for personally identifiable information (PII) and recording user activities for baseline profiling. In the event of an intrusion or account takeover threat, Digital Guardian promptly alerts the team for timely intervention. The software’s ability to classify data based on functions, control data movement, and provide additional threat detection methods contributes to enhanced security and privacy.
The Digital Guardian is a cloud-based system that is well-known for its versatility and works best on any device, whether it runs on Windows, Linux, or macOS. Digital Guardian helps assess and organize access rights management structure and, like every other data loss prevention system, benefits its users in enforcing compliance with ease. As a result, users can easily regulate and monitor access to sensitive data through different security policies.
An innovative feature of Digital Guardian is its eDiscovery sweep. When enabled, the software continuously goes through the data and searches it for identifying the PII. Additionally, any system under the protection of Digital Guardian records all the user activities and profiles them to create a standard baseline. If any hacker or intruder breaks the usual cycle, the software sends an intrusion or account-takeover threat to your team so that they can take appropriate steps timely.
Who is it recommended for?
Digital Guardian Endpoint DLP is recommended for businesses seeking a comprehensive and versatile SaaS solution for data loss prevention. It is ideal for organizations using a variety of devices, including those running on Windows, Linux, or macOS. The platform’s effectiveness in access rights management and compliance enforcement makes it suitable for businesses dealing with sensitive data. The eDiscovery sweep and proactive threat detection features make it particularly beneficial for those prioritizing timely response to potential security threats. Digital Guardian is a valuable choice for enterprises aiming to enhance overall security, privacy, and intellectual property protection.
Digital Guardian has several benefits. With the help of this software, you can classify your data according to specific functions along with efficiently controlling data movement. The industry’s sole Saas solution for enterprise data loss prevention also provides additional threat detection methods along with secured intellectual properties for enhanced security and privacy.
If you are interested in using their services, visit their website for further details.
Final Take
Accelerating technological advancements has its benefits, but it increases the risks of data breaches and loss as well. To maintain customers’ trust and loyalty, organizations need to equip themselves with tools that can prevent a disastrous scenario where your customers’ data lands in the hands of a data hacker. Use a suitable PII tool to protect personal and sensitive data at all times.