Most of us have heard that good network security is like an onion. With its many layers, it protects the core at its center. Today we’ll be looking at the top five Intrusion Prevention Systems (IPS), and exactly how they provide a unique layer of security to your own network.
Here is our list of the top intrusion prevention systems:
- ThreatLocker Detect – EDITOR’S CHOICE Uses advanced technology to accurately detect events and anomalies in your network. It sends alerts, presents the data in easy-to-understand dashboards, and can even take automated actions based on policies. Start a 30-day free trial.
- ManageEngine Log360 (FREE TRIAL) Leverages AI, machine learning, and automation to detect and present threats before they compromise your network. Start a 30 day free trial.
- OSSEC Leverages automated active response and machine learning to detect evolving threats.
- Snort Utilizes a vast array of rule sets that give you flexibility when scanning and protecting your network.
- Zeek (Bro) A high-level network analyzer that provides you with the raw data you need to make the best security-related changes.
- SolarWinds Security Event Manager Provides the perfect balance between network security, ease of use, and functionality.
- Siracata Similar to Zeek, this tool runs via command line only and can quickly scale and record network traffic across enterprise environments.
The Best Intrusion Prevention Systems (IPS)
1. ThreatLocker Detect (FREE TRIAL)
At the top of our list is ThreatLocker Detect, as it offers comprehensive protection against unauthorized access to your network resources. It continuously scans your endpoints, and also collects data from other ThreatLocker modules and Windows system logs. Putting it all together, it identifies events and sends alerts for quick remediation.
Why do we recommend it?
During our testing process, one of the first things that stood out to us was ThreatLocker’s extensive coverage and insights. It gathers and analyzes data to provide relevant context to every threat or anomaly, making it easy for your employees to fix issues quickly. Also, you can use policies to configure automated actions, like blocking activities in an infected device, disconnecting it from the network, and more, to prevent the further spread of the infection.
More importantly, all this information is presented in easy-to-understand formats on dashboards, enabling people of all backgrounds to understand the threats and take action if required. At the same time, it also offers the flexibility to make custom rules and policies, so your administrators are in complete control.
Who is it recommended for?
ThreatLocker Detect works well for organizations of all sizes, especially those that handle large volumes of data. Its flexibility and scalability make it a good choice for SMBs, enterprises, MSPs, and organizations that have to comply with multiple regulations.
Start a 30-day free trial.
EDITOR'S CHOICE
ThreatLocker Detect is the editor’s choice for the best IPS because of its comprehensive features and coverage. It takes a methodical approach to detecting and mitigating cyberthreats, making it a highly effective platform for handling known and unknown threats. Along with sending alerts, it also provides contextual information and recommendations based on frameworks like CISA and MITRE to help administrators fix the issue before it creates a big impact on your organization. Its well-developed dashboards and incident response support are other reasons for this tool to be at the top of our list.
Download: Start a 30-day FREE Trial
Official Site: https://www.threatlocker.com/try-threatlocker
OS: Windows, macOS, Linux, Cloud/SaaS and Hybrid
2. ManageEngine Log360 (FREE TRIAL)
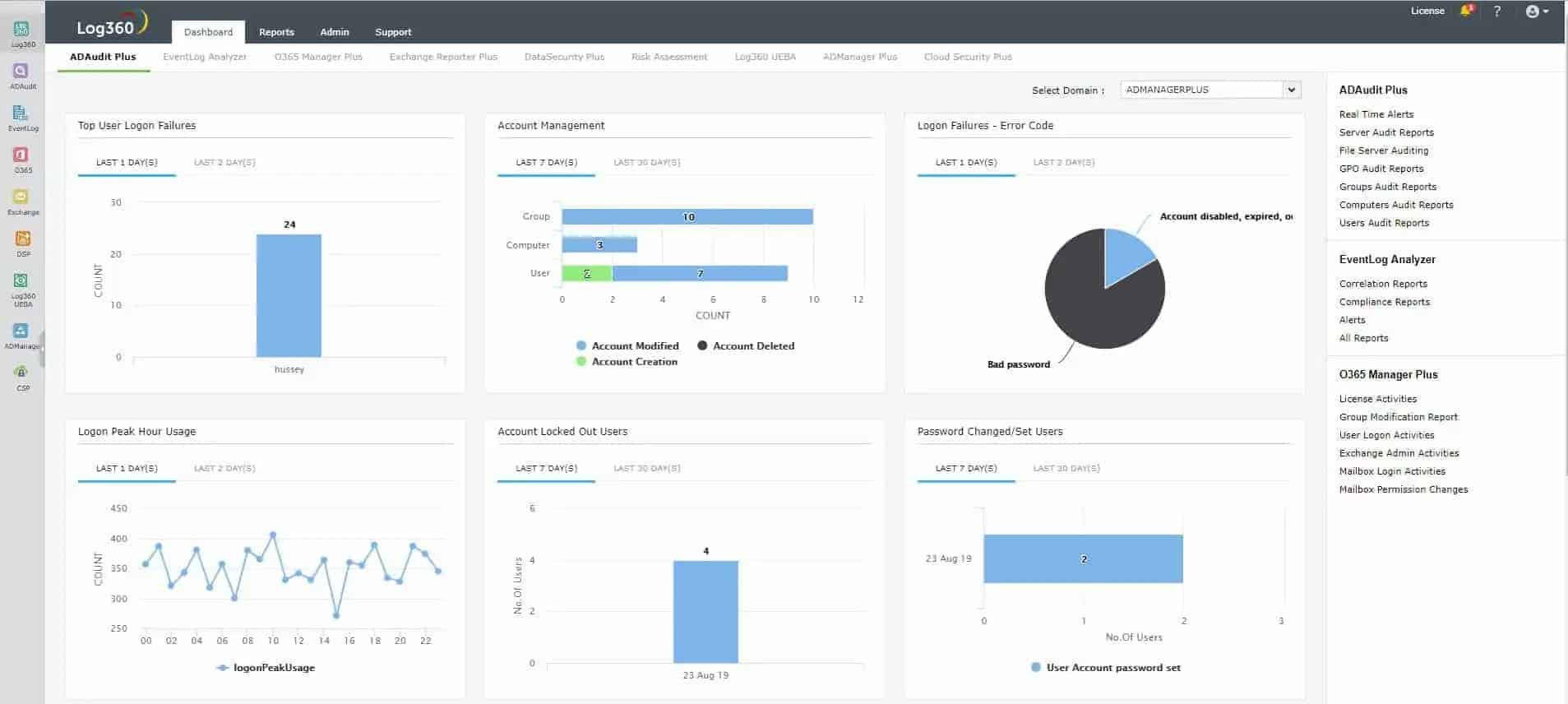
ManageEngine Log360 is a robust security information and event management (SIEM) solution that provides comprehensive protection for enterprise networks against sophisticated attacks. With its integrated DLP and CASB capabilities, Log360 can detect, prioritize, investigate, and respond to security threats.
Key Features:
- Automated threat identification and response
- Granular filtering and controls
- Wide range of SIEM integrations
Why do we recommend it?
ManageEngine Log360 is highly recommended as a robust Security Information and Event Management (SIEM) solution that provides comprehensive protection against sophisticated attacks for enterprise networks. Its integration of Data Loss Prevention (DLP) and Cloud Access Security Broker (CASB) capabilities ensures the detection, prioritization, investigation, and response to security threats. The platform stands out with automated threat identification and response, granular filtering and controls, and a wide range of SIEM integrations. Leveraging advanced threat intelligence, machine learning-based anomaly detection, and rule-based attack detection techniques, Log360 excels in identifying malicious activities and minimizing critical response time during an attack.
The platform utilizes advanced threat intelligence, machine learning-based anomaly detection, and rule-based attack detection techniques to identify malicious activities and minimize the critical response time during an attack.
The platform aggregates data from IDS and IPS devices, firewalls, and Active Directory infrastructure to alert security teams of possible intrusion attempts in real time. This is done through Log360’s threat intelligence module that can analyze the source, destination, and severity of the intrusion. Once an intrusion is detected, security teams can investigate further and automate their response with workflows to minimize response time.
Log360 also uses threat intelligence to detect compromised systems within the network. When a system is compromised, it can be controlled by an external command-and-control server. Log360 can detect these attempts by analyzing data from reputed threat feeds and alerting security teams when a system attempts to communicate with a malicious source. The platform also provides details such as the reputation score, age, and geolocation of the domain to aid in analysis.
Who is it recommended for?
ManageEngine Log360 is recommended for enterprises seeking a powerful SIEM solution with integrated DLP and CASB capabilities. It is ideal for security teams looking to detect, prioritize, and respond to security threats efficiently. The platform’s ability to aggregate data from various security devices and infrastructure, along with its threat intelligence module, makes it suitable for real-time alerting and analysis. Log360 is particularly valuable for organizations focusing on automated response workflows to minimize response time. It is a comprehensive choice for Windows, Linux, and Unix systems, providing monitoring and prevention against privilege escalation.
Pros:
- Great dashboard visualizations, ideal for NOCs and MSPs
- Can integrate multiple threat data steams into the platform
- Offers robust searching of logs for live and historical event analysis
- Provides monitoring cross-platform for Windows, Linux, and Unix systems
- Can monitor configuration changes, preventing privilege escalation
Cons:
- ManageEngine offers a suite of advanced services and features can time to explore and test out
You can test out ManageEngine Log360 through a 30-day free trial.
3. OSSEC

OSSEC is an open-source, community-driven IDS leverages log-based monitoring to analyze security data on a network in real-time. One of the best features of OSSEC is its File Integrity Monitoring system which not only monitors system and registry changes managed on a machine but keeps a forensic copy of the data as it changes over time. This automatically gives you a deep insight into how an attack unfolded, as well as a possible legal chain of evidence to use in court.
Why do we recommend it?
OSSEC secures its place as a top recommendation due to its open-source nature and community-driven Intrusion Detection System (IDS). Utilizing log-based monitoring in real-time, OSSEC excels in providing deep insights into security data on a network. A standout feature is its File Integrity Monitoring system, which not only monitors changes but also maintains a forensic copy, allowing for comprehensive understanding and legal evidence in case of an attack. OSSEC’s automated active response approach empowers users to configure actions like enabling firewall policies, running scripts, and implementing self-healing processes.
Like other tools in this list, OSSEC leverages an automated active response approach to detect threats and breaches. You can configure OSSEC to perform a number of different actions such as enabling firewall policies, running custom scripts, and self-healing processes. The security system also collects machine data such as installed hardware, software, network services, and utilization. This is particularly useful to help identify the source of a network infection and track it down to a single machine or user.
OSSEC is highly customizable and really relies on proactive sysadmins to script different solutions depending on what the monitoring logs discover. With that being said, there are also some incredibly powerful built-in scans that can be easily started. Rootcheck for example taps into a constantly updated database of rootkits and rootkit file modifications, to compare against what it finds on the network.
It will also scan workstations to see if their NIC is in promiscuous mode, and check to see if there are any suspicious services running in the background. This acts almost as a high-level antivirus scan would. In addition to malicious file detection, OSSEC can also find file permission issues and alert you to them. Files or folders owned by root, for example, don’t follow best security practices. It can be hard to manually audit all of your network’s file structures, but with OSSEC it’s not a problem.
Who is it recommended for?
OSSEC is recommended for organizations and sysadmins seeking a highly customizable and proactive IDS solution. Its ability to monitor system and registry changes, coupled with a File Integrity Monitoring system, makes it ideal for those who prioritize understanding the unfolding of attacks. Security teams looking for an open-source solution that allows for tailored scripting and proactive responses will find OSSEC valuable. The system’s scans, including rootkit detection, NIC mode checks, and identification of suspicious services, make it akin to a high-level antivirus scan. OSSEC is particularly beneficial for users aiming to address file permission issues and ensure adherence to best security practices across their network.
OSSEC is completely free to use and falls under the GNU Public License. It’s compatible with Windows, MacOS, and Linux systems.
4. Snort

Don’t let its playful name or mascot fool you. Snort is a powerful Intrusion Protection System that you won’t want to turn your nose up at. Snort is a flexible IPS that can run in almost any Windows, Linux, or MacOS system. Snort might not be for everyone, as it does not come with a Graphical User Interface to run reporting and commands from; strictly command line only. You can configure the software in a number of different ways to suit your security needs.
Why do we recommend it?
Despite its unassuming name and playful mascot, Snort stands out as a robust Intrusion Protection System (IPS) that commands serious attention. Operating seamlessly on Windows, Linux, or MacOS, Snort is a versatile IPS with a notable focus on packet sniffing capabilities. While lacking a Graphical User Interface, its flexibility allows configuration to meet diverse security needs. Snort’s prowess lies in its ability to detect various attack methods, including SMB probes, OS fingerprinting, and port scans, making it a potent choice for network security.
Its most popular function is that of a packet sniffer, where Snort, well “snorts” all of the traffic across your network. There are a number of attack methods Snort can detect such as SMB probes, OS fingerprinting, port scans, and plenty more.
At the center of the operation, Snort uses something called Snort Rules to define and detect threats. These rules are constantly updated and community-focused. If you’re looking to detect or identify a very specific type of network traffic you can even create your own Snort rule file. Rather than having one big rule file, you can get rule files in categories ranging from java exploit detection, to know vulnerabilities in image extensions such as .jpg and .png.
Who is it recommended for?
Snort is recommended for users seeking a powerful, free, and open-source IPS solution with a command-line interface. While not tailored for those reliant on graphical reporting tools, it is an excellent choice for individuals and organizations comfortable with command-line configurations. Security enthusiasts and professionals who prioritize community-driven updates and the ability to create custom rules for specific network traffic types will find Snort particularly appealing. Additionally, its paid yearly subscription offers expedited access to Snort rules, the capability to report false positives, and the opportunity to become an authorized reseller, making it suitable for a broad range of security needs.
Snort is free and open-source, but also offers a paid yearly subscription that gives you access to Snort rules faster, the ability to report false positives, and even the ability to become an authorized reseller. Pricing for the premium version starts at $29.99 (£24.47) a year.
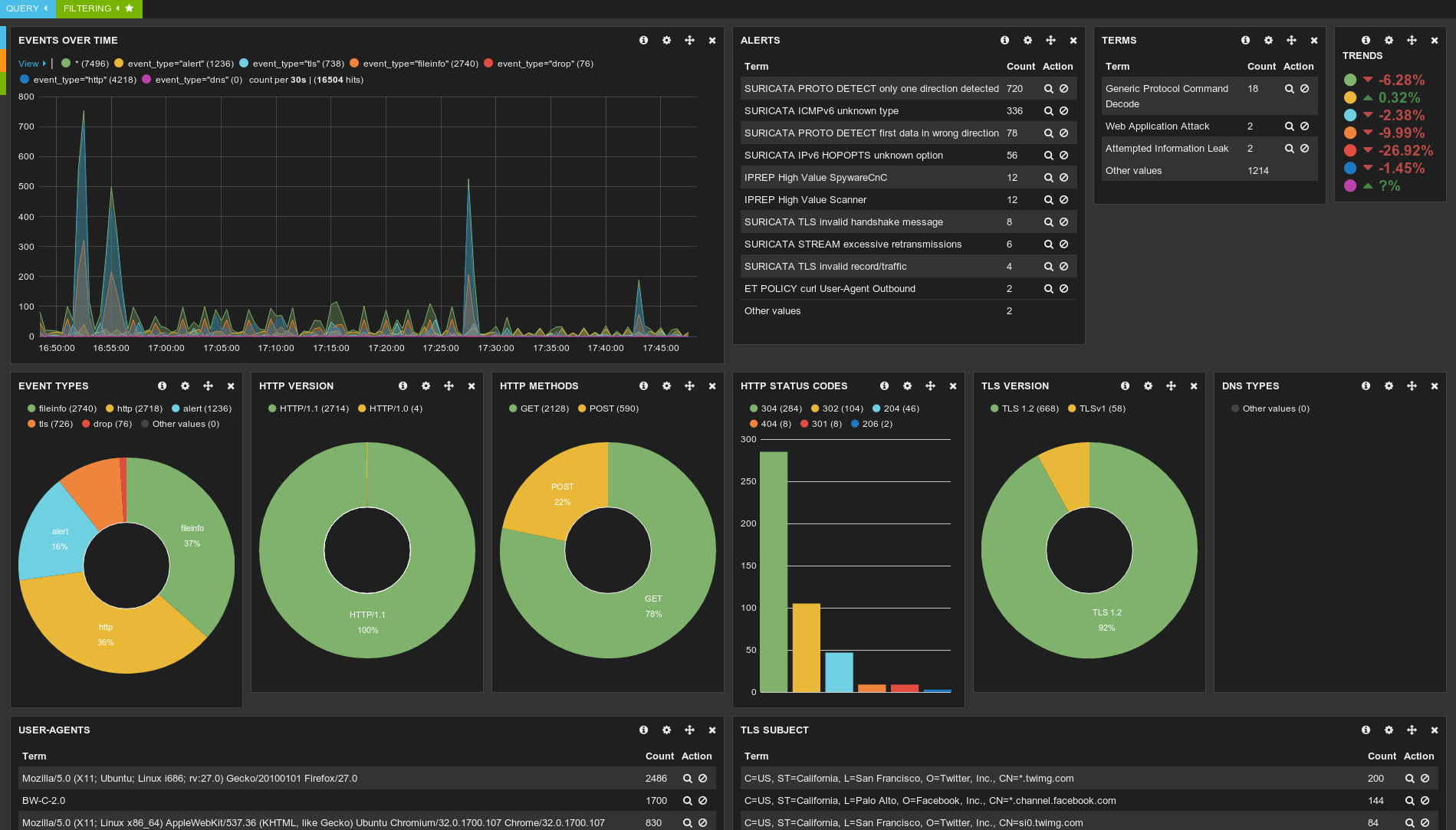
5. Zeek (formerly Bro)

Zeek, formerly known as ‘Bro’ was first started in the 1990s by a man named Vern Paxson, who wanted to know what was happening on the university’s network and in his laboratory. This modest pet project soon branched off into a much larger endeavor that positioned Zeek as a security tool used among researchers and administrators across the globe.
Unlike anti-malware software or a firewall, Zeek sits silently on a network and observes everything it can see. Zeek captures this traffic and builds high-fidelity logs and customizable outputs to be reviewed by data scientists, analysts, or forensic teams. Zeek is truly a high-level analysis tool, so you don’t find any fancy graphical interface or visualizations for the data you capture.
Why do we recommend it?
Zeek has evolved from a modest university project in the 1990s to a globally recognized security tool employed by researchers and administrators. Unlike traditional anti-malware or firewall solutions, Zeek discreetly observes network activities, capturing and generating high-fidelity logs for thorough analysis by data scientists, analysts, or forensic teams. While lacking a graphical interface, Zeek’s strength lies in its comprehensive logging, making it a valuable tool for manual identification of suspicious or malicious events. Its open-source nature fosters a collaborative community that contributes to feature development and documentation updates.
Like most open-source projects, Zeek is entirely open source and relies heavily on its community of users to add new features, and update documentation. If you’re looking for a done-for-you security solution, Zeek is not it.
If you’re running security or administering a network, Zeek can be a great tool that works in conjunction with a network firewall and other security measures to help you dial in and manually find suspicious or malicious events.
Zeek’s comprehensive logging means everything is captured, recorded, and stored. While some extremely savvy malware can erase its movements inside a network from log files and event viewers, it cannot escape the all-seeing eye of Zeek, which captures the raw network data.
With no front end to analyze this captured data with, you’ll need something to view it and better understand what you have. A popular tool you can use in tandem with Zeek is Kibana. Kibana is an open-source front-end tool that provides search and data visualization.
Who is it recommended for?
Zeek is recommended for security professionals and network administrators seeking a powerful open-source tool to enhance manual threat detection and network analysis. While it lacks a ready-made security solution, Zeek serves as a valuable component when used alongside network firewalls and other security measures. The tool’s detailed logging captures raw network data, providing a comprehensive view that even savvy malware struggles to evade. Network administrators, particularly those comfortable with Linux environments, can leverage Zeek’s capabilities for in-depth analysis. For enhanced data visualization, combining Zeek with tools like Kibana proves effective, offering a meticulous approach to network security.
While most network administrators won’t need the level of detail Zeek provides, it’s still a great free and open-source tool you can use to comb through the intricacies of your network. The preferred operating system to install Zeek is Linux, but you can install Zeek on Windows using the Quick Start Guide.
6. SolarWinds Security Event Manager

Starting at the top of our list is the Security Event Manager by SolarWinds, which is one of the most comprehensive and detailed security tools on the market. In a clean and easy-to-navigate interface you’ll have access to both historic logs and real-time security events that are happening on your network.
Why do we recommend it?
SolarWinds Security Event Manager (SEM) earns our top recommendation for intrusion prevention due to its exceptional comprehensiveness and detailed security features. SEM stands out with its clean, user-friendly interface, offering easy navigation through both historical logs and real-time security events on your network. What sets SEM apart is its proactive approach to threat mitigation, utilizing real-time event correlation and machine learning to identify potential threats swiftly. The tool’s Active Response feature allows for a high level of customization in dealing with specific attacks, from disabling user accounts to quarantining infected machines. SEM’s elegant reporting capabilities, including compliance reports for standards like HIPAA and PCI-DSS, further contribute to its status as the best intrusion prevention product.
While logging hundreds of security events and logs might seem messy, Security Event Manager (SEM) does an excellent job not only prioritizing alerts but proactively taking corrective action to stop a threat from getting further into your network. SolarWinds SEM utilizes real-time event correlation to identify potential threats by even minuscule trace evidence intruders leave behind.
Instead of pouring over hours of logs, SEM can use its machine learning to see the precursor events to an attack and stop it in its tracks incredibly quickly, and arguably faster than any human manually could.
But stopping a single attack isn’t enough, especially once it’s already inside your network. One of my favorite features of SEM is the level of customization you can apply to how a threat is dealt with. SEM uses a feature called Active Response, which will automatically deal with specific attacks in the way you configure it.
You can choose to automatically disable user accounts, block IP addresses, kill processes, stop or reboot services, and even quarantine infected machines from your network.
SEM also provides detailed and elegant reporting that can not only give you a 30,000 foot view of your network security but also produce compliance reports for standards such as HIPAA and PDC-DSS. In a few clicks, you can schedule reports to be on customized intervals, making quarterly reports something you almost don’t have to even think about.
SEM really provides the best intrusion prevention product, not just because of its proven ability to protect a network, but because of its ease of use. Like most techs, I’ve spent a fair amount of time in the command line. So it’s really refreshing to see a product that allows for such an easy to use interface, or that doesn’t sacrifice the level of control for the sake of having a GUI.
Who is it recommended for?
SolarWinds SEM is recommended for organizations and IT professionals seeking a comprehensive intrusion prevention system that excels in both real-time and historical security event analysis. Its ease of use makes it suitable for users with varying levels of technical expertise, providing a powerful interface without sacrificing control. SEM’s deployment flexibility, compatible with VMware Vsphere ESX, ESXi, or Microsoft Hyper V, caters to diverse network environments. The tool is particularly valuable for those prioritizing proactive threat prevention and customization options in responding to security incidents.
SolarWinds Event Security Manager is simple to install and is deployed as a virtual application that is compatible with both VMware Vsphere ESX, ESXi, or Microsoft Hyper V.
You can try out SolarWinds Security Event Manager in your network through a completely free and fully functional 30-day trial.
7. Suricata
Siracata is a flexible open-source IPS that can run on Linux, Windows, and MacOS. Much like Zeek, Siracata gathers network data through deep packet inspection and pattern matching, making it an excellent tool for analysis and threat detection.
Why do we recommend it?
Suricata stands out as a flexible and open-source Intrusion Prevention System (IPS) compatible with Linux, Windows, and MacOS. Employing deep packet inspection and pattern matching, Suricata excels in network data analysis and threat detection. The ability to configure Suricata in various modes, including network detection and intrusion prevention, provides users with operational flexibility. Notably, its prevention mode actively drops specified threat-related packets, while the detection mode passively scans and records raw data for subsequent analysis. Designed for efficiency, Suricata’s lean and fast backend is particularly well-suited for large enterprise environments, offering multi-threaded signature detection for scalable port scanning capabilities. Additionally, Suricata’s application-awareness ensures intelligent detection of protocols over non-standard ports, surpassing limitations observed in some comparable tools.
You can configure Siracata in a number of different ways, two of the most popular being network detection, and intrusion prevention mode. When Siracata is operating under prevention mode, it will drop packets that you specify as a threat, whereas in detection mode it is passively scanning raw data and recording it for analysis.
The backend of Siracta was built to run lean and fast, making it ideal for large enterprise environments. Features like multi-threaded signature detection allow you to scale your port scanning capabilities very quickly across a network without having to tweak any settings or configurations.
Who is it recommended for?
Suricata is recommended for security professionals and network administrators seeking a versatile and efficient IPS solution. Its compatibility with Linux, Windows, and MacOS makes it adaptable to diverse operating environments. The ability to operate in prevention or detection modes caters to different security needs, providing both active threat mitigation and passive data recording for analysis. Suricata’s scalability, particularly evident in its multi-threaded signature detection, suits the demands of large enterprise networks, enabling swift and effective port scanning. For users who prioritize application awareness and intelligent protocol detection, Suricata emerges as a valuable choice, surpassing limitations observed in some other intrusion prevention systems.
A final key feature is that Siracata is application-aware. Simply put, this means Siracata is smart enough to detect protocols over non-standard ports and label their services. This is an area where tools such as Snort had fallen short in the past. You can download the software for free via this link here.
Conclusion
While intrusion prevention systems can’t protect you on their own, they are a vital key component when it comes to securing and auditing your network. If you’re looking for an IDS that provides an excellent balance between ease of use and effectiveness then SolarWinds Security Event Manager is a clear winner.
Need to dive deeper and perform a live audit on your network with forensic level granularity? Zeek will have you covered. No matter which system you choose, having an IDS on your network will add another layer to your security to keep you one step ahead of the bad guys.
Do you currently run an intrusion prevention system? What are your biggest challenges with it? Let us know in the comments below.