They are without a doubt an excellent product that has a significant emphasis on being easy to use. Small businesses, branch offices, data centers, and remote enterprise systems can all benefit from the cloud-managed security and SD-WAN solutions offered by the Cisco Meraki firewall. It is not overly complicated and can be understood and handled with little effort.
Meraki’s firewall alternatives to its firewall are designed to incorporate all of your other advanced security services. Because they are next-generation firewalls, you can rest assured that they will take care of everything that needs to be taken care of, from geo-based firewalling to remote access connectivity and everything in between, to ensure that the bandwidth of your company is not wasted on content that is not productive.
Here is our list of the best Cisco Meraki Firewall alternatives:
- FortiGate NGFW It offers both high performance and security features of the next generation, which together offer complete network coverage and protection from end to end.
- SonicWall The SonicWall firewall, in contrast to those offered by other vendors, already comes equipped with several ports.
- Point NGFW Checkpoint Provides customers with the option to purchase pre-configured packages, as well as the software blades necessary to custom, create a solution
- The Sophos UTM It protects the network from the most recent dangers posed by malware, viruses, and bugs while simultaneously boosting the performance of your important applications and traffic to cloud apps.
- WatchGuard Network Security This is an excellent tool that will provide you with total visibility, enable you to make quick and effective decisions on the security of your network from anywhere and at any time, and safeguard people, data, and devices across your whole network from a single platform.
- Forcepoint NGFW The Unified Forcepoint Next-Generation Firewall software is a software/virtual appliance that was built to secure cloud and virtual infrastructure.
- Juniper Firewall With this, all advanced requirements are met, including next-generation firewalls that react to new threats and cloud-based services.
The Best Cisco Meraki Firewall Alternatives
1. FortiGate NGFW
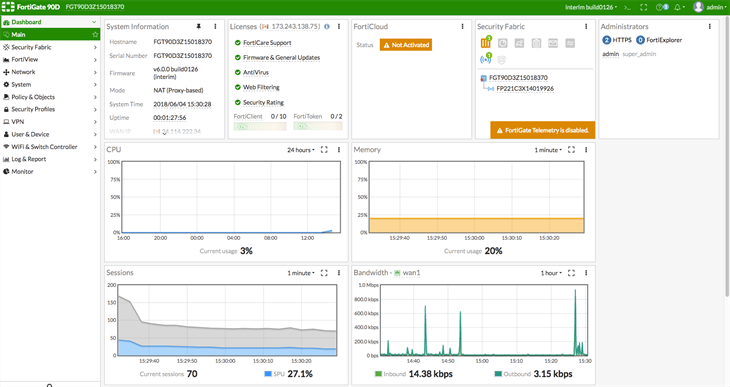
Fortinet should be on your list of potential Meraki Firewall Alternatives to consider if you are interested in superior protection at an affordable cost. These next-generation firewalls from FortiGate offer high performance, many layers of security, and deep visibility to provide comprehensive end-to-end protection for a whole company network. With that, scalable performance and low latency are provided by the purpose-built security processors (SPUs) utilized by it.
Key features:
- Protection from persistent and advanced threats
- Protection against and detection of intrusions
- Filtering of email, websites, and content
- Data loss prevention (DLP)
- Virtual private network (often abbreviated as VPN)
The Fortinet Security Fabric is made possible by the software that powers the FortiGate Next-Generation Firewall (NGFW). It is a dynamic architecture that can identify and respond automatically and is integrated with various types of cybersecurity threats. In addition to this, it employs AI and machine learning to provide detection and prevention of cyber threats based on behavioral patterns.
The FortiGuard Services can be purchased as a standalone subscription or as a software bundle, either with or without the accompanying hardware. The core of the support services is the device-based support that is provided by Forti-Care. This includes firmware upgrades, technical assistance, and foundational subscriptions to FortiGuard.
Firewalls manufactured by FortiGate utilize machine learning-based threat information provided by FortiGuard Labs and contain in-depth analytics made possible by Forti-Analyzer. They are also capable of being coupled with Forti Sandbox, which allows for the automatic generation of local threat intelligence to protect against new zero-day and advanced attacks.
2. SonicWall

It is very simple to manage and create new policies using the SonicWall Dashboard beginning with version 7.0. The SonicWall firewall, in contrast to those offered by other vendors, already comes equipped with several ports. With the newly improved GUI, we can now set up Site to Site as well as SSL VPN in a shorter amount of time. When SonicWall is deployed, it immediately begins protecting the network with several different security profiles that have already been preconfigured.
Key features:
- Filtering of material on the web and identification of applications
- Malware protection, IP reputation analysis, and SSL verification
- Decryption and inspection of LS/SSL/SSH traffic
- Reassembly-Free Deep Packet Inspection (RFDPI), which provides a comprehensive real-time security analysis of all traffic.
- Support for TLS 1.3, which allows for inspection of encrypted traffic
- Fully Integrated and Protected SD-WAN
Since the beginning of the firewall industry, SonicWall has been a leader in the field. The SonicWall Firewall is capable of supporting installations in a variety of environments, including cloud, virtual, and physical ones. The company’s hardware is driven by a piece of software known as SonicOS, which enables all of the various networking and security functions.
Investing in a complete and integrated solution that combines encrypted traffic inspection, reputation services, malware analysis, and cloud app security is necessary if you want to secure your organization and put a stop to threats. This program can give you all of these things at a cost that is manageable within your budget, making it an ideal Meraki Firewall Alternatives.
SonicWall is regarded as one of the leading cybersecurity businesses in the industry by a wide variety of third-party organizations, and the feature-packed and high-performance firewalls that it offers lend credence to this position. The throughput and connectivity choices provided by Gen 7 firewalls are excellent, making them suitable for deployment in environments ranging from small businesses to enterprises.
3. Point NGFW Checkpoint

The Check Point NGFW is a next-generation firewall that facilitates the secure use of internet applications by blocking dangerous applications while allowing safe apps to function normally behind the firewall. In context to that, deep packet inspection, which is used by Check Point NGFW to identify and control applications, is one of its many functions. Other features include user and application control, as well as integrated intrusion prevention (IPS)
Key features:
- Connectivity via Virtual Private Network (VPN) allows the safe transmission of data between several vendors.
- It enables on-demand cloud level expansion as well as hyper-scale threat avoidance.
- It can cut your security operations by as much as 80 percent, which results in a gain in efficiency.
- It offers unified security management control across several network layers and Internet of Things platforms.
- Incorporate the most cutting-edge methods of protection and prevention against threats, as well as consolidated management.
The SmartConsole offered by Check Point makes it simple to manage and modify the various policies and settings about network security. Users can control all of the firewall gateways and access logs as well as install databases from a single location when utilizing the SmartConsole. The effectiveness of network security operations is improved while the costs of IT are cut down thanks to unified management control across the network.
Moreover, in this, the sandBlast Zero-Day protection is one of the ways that NGFW provides the highest level of threat prevention available. The SandBlast protection agent performs a continuous scan of the moving network traffic in search of vulnerabilities and exploits. After that, potentially harmful files are mimicked within a digital sandbox to observe their behavior and report any abnormalities.
The license system used by Check Point is built to be both scalable and adaptable. To achieve this goal, Check Point provides customers with the option to purchase pre-configured packages, as well as the software blades necessary to custom create a solution. If you wish to utilize a firewall, intrusion prevention system (IPS), and an IPSec VPN, you will need a software license for each of those blades.
4. Sophos UTM

Sophos UTM, originally known as Astaro Security Gateway, is an integrated security solution that combines all of the necessary software into a single device. High-performance streaming, the Intrusion Prevention System (IPS), deep packet inspection, application control, web protection, sandboxing, and deep learning provide you the ability to prevent the most recent data breaches and ransomware attacks.
Key features:
- The protection provided by a Next-Generation Firewall (NGFW)
- Protection, encryption, and anti-spam measures for email
- Virtual Private Networks for on-site and remote access
- Regulation of user access to mobile networks
All the access to manual updates, a knowledge base, a community forum, and return and replace services are all included in the regular support package offered by Sophos. Also, premium support provides you with technical assistance from Sophos Support professionals around the clock, along with enhanced replacements and automated updates.
You can use this automatically or even according to the policies of your company to accelerate your cloud traffic, SaaS, video, and other trusted applications, putting them on the fast track to maximize their performance.
The architecture of the Sophos Firewall shields your network from the most recent malware, virus, and bug threats while simultaneously boosting the performance of your important applications and traffic to cloud apps. It does this by performing an intelligent TLS examination that is both fast and effective. Additionally, it makes use of the most recent standards while allowing for extensive exceptions to simplify your work through the use of pointing and clicking tools.
5. WatchGuard Network Security

Nearly one million of WatchGuard’s integrated, multi-function threat management appliances have been sold to customers all over the world as Meraki firewall alternatives. These customers run organizations ranging from small and medium-sized firms to huge multinational enterprises. Even though it acknowledges the unfulfilled demand for a security solution that can keep up with the constantly shifting nature of the threat landscape, it does not explicitly target major corporations or massive data centers. On the other hand, when it comes to performance, it is right up there with the best in the business.
Key features:
- A feature of spam blocker that is uncomplicated and dependable, successfully blocking questionable emails.
- Firewall designed for enterprise use.
- They offer SSL inspection as well as advanced security against malware that masquerades as encrypted communication.
- Methods for visualizing and analyzing traffic.
- Networking, Wireless, and Voice over Internet Protocol.
- You can update signatures, block threats, and destroy malware all without lifting a finger if you deploy or automate from the cloud.
Tabletop, rackmount, and software virtual appliances are all available for the WatchGuard Firebox, giving you the ability to deploy the solution either as a hardware appliance in a physical setting or as software in a virtual or cloud architecture.
It provides threat visibility capabilities that are suitable for every company, regardless of how sophisticated it is, how large it is, or how much money it has. In addition, consumers have the option to pay a membership to either the Standard, plus it supports 24/7; Gold, each of which provides a higher priority to your support issue. WatchGuard offers subscriptions for the various security software modules that are compatible with Firebox appliances, and these subscriptions can be purchased singly or as a bundle.
6. Forcepoint NGFW

Gartner recognizes Forcepoint as one of just a few unique alternatives in the category of Future. With this one, people and data that are accessed everywhere in a business, including its offices, branches, and the cloud, can be connected to and protected by Forcepoint NGFW. Forcepoint NGFW is a next-generation firewall that enables security teams to swiftly deploy, monitor, and update thousands of firewalls, VPNs, and IPSs through a single console. This can be done internally or through a managed service provider. High-availability clustering and software-defined wide-area networking are included.
Key features:
- The Forcepoint 2100 and 1100 series are both physical appliances that offer protection at the edge of the network.
- Physical appliances of the Forcepoint 300, 120, and 60 series are aimed at remote sites and branch offices.
- The physical appliances in the Forcepoint 50 series are aimed toward home offices and small to medium-sized businesses.
When installed on a laptop, desktop, or server, Forcepoint NGFW’s Endpoint Context Agent enables the firewall to control access to the network based on the state of the endpoint (using NAC-like attributes such as whether AV is active) and to whitelist or blacklist specific endpoint applications and versions. Forcepoint NGFW supports the optional use of its Endpoint Context Agent.
Administrators can deploy, monitor, and update up to 2000 Forcepoint NGFW appliances from a single centralized management console by utilizing the Forcepoint NGFW Security Management Center (SMC). For the protection of both your network and the data it contains, it combines authentic SD-WAN, intrusion prevention, and seamless interaction with cloud-based SASE security. Forcepoint NGFW supports installations across physical, virtual, and cloud environments.
It features an integrated intrusion prevention system (IPS) with anti-evasion protections, policy-driven centralized management, whitelisting and blacklisting of client applications and versions, anti-malware sandboxing, and a great deal more besides.
7. Juniper Firewall

It is common knowledge that Juniper Networks is the provider of high-performance Next-Generation Firewalls (NGFW) that offer granular control and visibility from client to cloud. It has been determined that Juniper is a contender in the Gartner Magic Quadrant for Network Firewalls for the year 2020.
Key features:
- It offers security against the most recent threats.
- It has a welcoming and intuitive user interface.
- Traffic load balancing helps to maximize the effectiveness of both of the internet links being used.
- It gives total email and enterprise data security.
- Complete sway over how the website and applications are used
You have the option with Juniper’s network firewall to install it in the form of a physical appliance (SRX series), a virtual appliance (vSRX), or a containerized firewall (cSRX). The Juniper license model is a subscription-based one. To make use of a licensed feature, you will need to first acquire, then install, then activate, and finally manage the license that is associated with that feature. Through the Juniper Agile Licensing Portal, you will have the ability to administer and manage the permits.
You have full control over everything thanks to their availability in both virtual and physical form factors, as well as role-based access controls and deep-packet inspection capabilities. You could even supply important security services that protect against bots, commands, advanced persistent threats, zero-day threats, and control servers. To do so, you would have to labor.
The Junos Space Security Director serves as the primary management for all Juniper Next-Generation Firewalls (NGFW). A centralized web-based interface is used to administer security policies for all physical, logical, and virtual firewalls that are managed by the system.
Our Choice
With these Meraki Firewall alternatives, you get a full collection of next-generation firewall technologies that work to protect your network in real-time from scripting, denial-of-service attacks, and other network threats like trojans, worms, malware, and many other things.
The FortiGate NGFW is a better option for Meraki Firewall alternatives than any of the above-mentioned alternatives to Cisco Meraki firewalls. Stateful examination of incoming and outgoing network traffic is one of the many functionalities offered by this Next-Generation Firewall. Only a limited amount of control and visibility can be achieved using traditional firewalls.