Cybercrime was projected to cost businesses over $6 trillion a year by 2021.
If your incident response tools are lacking, we’ve got you covered. Here are nine of the best incident response tools you can use to mitigate attacks and recover quickly if your network is breached.
Here are our top choices for best incident response tools:
- ManageEngine Log360 (FREE TRIAL) This SIEM tool includes a threat intelligence feed plus UEBA to spot attacks and alerts operators to suspicious activity. Available for Windows Server. Start 30-day free trial.
- Datadog Security Monitoring A cloud-based solution designed to work out of the box.
- CrowdStrike Falcon XDR A cloud-based endpoint detection and response package.
- UnderDefense MAXI MDR This cybersecurity consultancy provides a managed detection and response service to supervise you security system.
- SolarWinds Security Event Manager Provides an easy to use balance of proactive and reactive tools for any size organization and budget.
- Sumo Logic Uses machine learning and AI to track and prevent security events.
- Splunk Robust response tool that uses Elasticsearch.
- Rapid7 InsightIDR Can create honeypots to act as an early warning system.
- LogRhythm Uses playbooks to create predictable outcomes when handling threats.
- AlienVault USM Uses behavioral monitoring for internal and external threats.
- OSSEC Free open-source incident response tool.
Best incident response tools
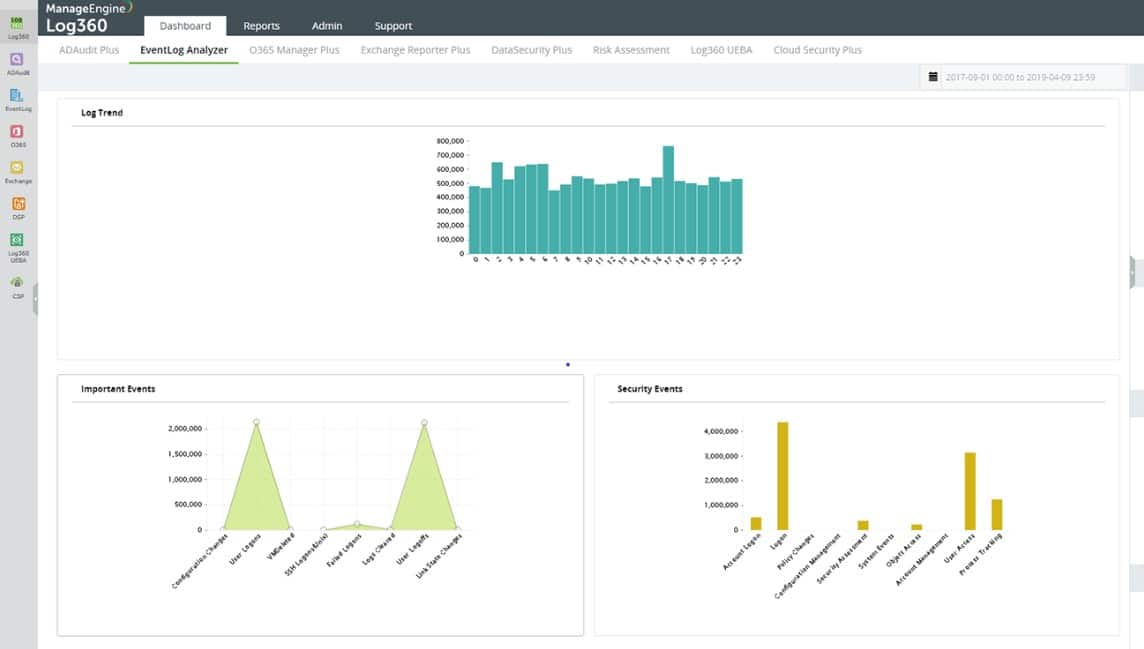
1. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is a SIEM system that gathers log messages from operating systems and software packages to provide a basis for research. The service also employs user and entity behavior analytics to establish a baseline of normal activity and then spot anomalous behavior. The UEBA records standard events to create a profile per user account and per device. This technique is very good at spotting insider threats and account takeover as well as intruders.
Key features:
- Scans on-site systems and cloud platforms
- Consolidates and stores logs
- Uses UEBA
The log management part of Log360 collects Windows Events and Syslog messages and it interacts with more than 700 software packages to extract activity data. The tool can also get log data from AWS, Azure, and Salesforce cloud platforms. Those logs are centralized, converted into a common format, searched, and then filed. Those stored logs are useful for compliance auditing for PCI DSS, GDPR, FISMA, HIPAA, SOX, and GLBA.
The system raises an alert if it spots suspicious activity. That alert is displayed in the dashboard of Log360 and can also be forwarded as a notification through service desk systems, such as ManageEngine ServiceDesk Plus, Jira, and Kayoko.
Other security features in the Log360 package include file integrity monitoring and the benefit of a threat intelligence feed to speed up threat hunting.
The Log360 system installs on Windows Server. There is a Free edition and a fully-functioning 30-day free trial of the paid Professional edition. If you decide not to buy at the end of the trial period, the package will keep working but as the Free edition.
2. Datadog Security Monitoring

Datadog is a powerful cloud-based incident response tool that also leverages large amounts of log data to handle network threats. Datadog is categorized as a SIEM tool but has plenty of features that make it excellent for reactive incident response.
Key features:
- 75+ premade rulesets.
- Cloud-based platform.
- 600+ vendor integrations.
The platform really shines when it comes to ease of use. Everything is designed to be launched and ready to go from the start. This gives the Datadog a unique out-of-the-box feel without stripping away any technical features or controls.
Datadog uses 75+ premade detection rules based on best practices that are mapped using the MITRE ATT&CK framework to get you started quickly. Creating your own rulesets is easy with the built-in rule editor. You can define your search query, set your rule, and define the event all without having to learn a query language.
Datadog can automatically filter log data into meaningful security events and assign priority to each potential issue. This allows you to quickly scan the logs and assign team members to investigate incidents on the network. These insights are called Signals and can be shared in just a few seconds via email, or third party application such as Slack.
You can download and test Datadog on your network free through a 14-day trial.
3. CrowdStrike Falcon XDR
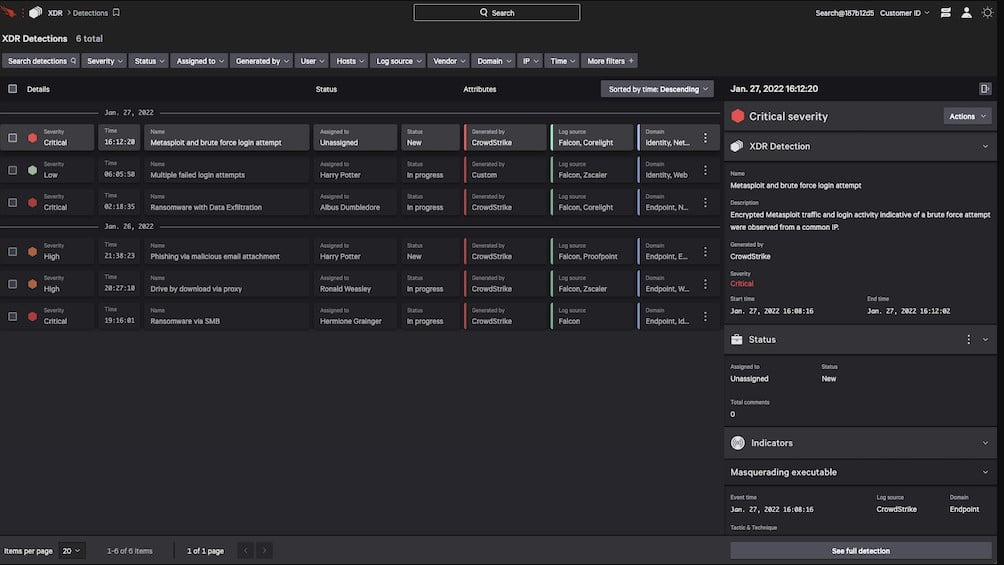
CrowdStrike Falcon XDR is a cloud-based service that receives activity data from endpoint agents and third-party software. This system is part of a family of cybersecurity products, called Falcon, that CrowdStrike provides from a cloud platform. The foundational product of the Falcon suite is the only component of the group that isn’t cloud-based. This is CrowdStrike Falcon Prevent, a next-generation anti-virus.
Key features:
- Searches log data
- Interacts with third-party tools
- Automated response
CrowdStrike Prevent installs on Windows, macOS, and Linux and, while scanning for suspicious activity and protecting the device, uploads activity data to the Falcon platform. CrowdStrike produces an endpoint detection and response (EDR) system, called Insight. This processes log data sent up by Falcon Prevent instances, consolidates them into a single data pool, and then scours them for indicators of compromise. CrowdStrike Falcon XDR is an alternative to Falcon Insight. It does the same thing as Insight but it adds in data extracted from third-party security tools and operating systems.
The Falcon XDR system uses a methodology called security orchestration, automation, and response (SOAR). This term denotes the ability to interact with third-party security tools, such as firewalls and access rights managers – two types of systems that CrowdStrike doesn’t produce. SOAR gets extra data into the threat hunting system of the XDR and it is also used to send instructions for actions to shut down suspicious activity.
As CrowdStrike Falcon XDR is based in the cloud, it isn’t limited to supervising endpoints on one network and it creates the opportunity to centralize the supervision of activities on multiple sites.
CrowdStrike doesn’t publish its price list and the company also doesn’t offer a free trial for Falcon XDR. However, CrowdStrike does offer a 15-day free trial of Falcon Prevent.
4. UnderDefense MAXI MDR

UnderDefense is a cybersecurity consultancy and it offers a managed security service that gives you an outsourced security operations center. The company doesn’t produce its own security software. Instead, the consultants will advise you on your current systems and advise on new acquisitions. The team can link together third-party software to get it to operate as a unit.
Key Features:
- Remote security management
- Incident response for security breaches
- Options for on-call advice
The UnderDefense team manages your existing security software or will advise on which tools to get. The company offers an on-demand service for companies that already have a cybersecurity team. In this option, your people can call UnderDefense experts to give their opinions about suspicious activity on your system and what actions they should take.
This system solves any problems that you might have encountered finding your own security staff. This is common in many parts of the world where there just aren’t any experienced cybersecurity experts available. You might also find that the cost of these hard-to-find experts is too high. The UnderDefense staff work remotely, so you don’t need to find them office space or provide them with desks and workstations.
If you already have security support technicians, you might want to supplement their expertise with a support contract from UnderDefense. This gives your team an on-call expert to consult.
UnderDefense MAXI MDR is a managed detection and response service that works with your own security software. The starting point of your contract with the UnderDefense team is an audit of your current systems. This assesses whether you have sufficient security services in place. If you have none, the team will guide you through the purchasing process. Once your security software is in place and correctly configured, the team provides ongoing management of the system. This removes the need for you to go out and hire your own team. Not every business can afford to keep a full cybersecurity team on the payroll and in many locations, it just isn’t possible to find them. The UnderDefense team works in its own office and connects to your security software across the internet. They look through the alerts generated by your security software and take appropriate action. They can even set up your cybersecurity system to implement automated responses on the detection of a threat.
UnderDefense offers a free account, which includes access to three UnderDefense systems. These are a Dark Web scanner, a compliance guide, and a risk assessment template library. Once you have signed up, you can chat with a cybersecurity consultant to organize a support contract. Start with the free demo.
5. SolarWinds Security Event Manager

SolarWinds Security Event Manager (SEM) has an impressive set of features that work to prevent attacks, and respond instantly if a breach is detected. Once installed on-premises in a Windows environment, SEM works to pull logs and network information across all of your endpoints, sites, and services.
Key features:
- Real-time automated incident response.
- Live and historical security event searching.
- Easy to use interface.
This data is both analyzed in real-time as well as stored for auditing or forensic investigation. This brings all security events from any part of your network into one location to be reviewed. The SEM interface is intuitive and allows you to sort events by server, location, or type. You can customize your hub simply by choosing metrics you wish to track, or building out your own query.
This flexibility ensures you and your team always have an at-a-glance look at the most important insights to your environment. From a single search bar you can filter live and past records by event, application, group, or user. While most tools are clunky to switch between historic and live data, SEM gives you the option to toggle the time range right from the search results.
But the real power lies in Security Event Managers automated correlation templates. SolarWinds provides hundreds of prebuilt rulesets that are designed to start protecting your network out-of-the-box. These rules follow general best practices and can be configured to either create an alert or execute an automated action when detected. Templates can be completely customized, giving you a solid foundation to build your own rulesets if you desire.
Configuring an automated response is as easy as picking one from a list. Responses can range from blocking an IP address, disabling a user account, detaching a USB device, or just simply creating an email alert. SEM also features file integrity monitoring across your entire network. This can be configured to detect and stop events like ransomware or alert your security team when unauthorized changes are being made internally to registry keys or files.
Lastly, built-in reporting provides quick insights into security events, compliance status, and overall improvement over time. These reports can be attached to tickets, automatically emailed, or saved to a secondary location.
You can test the SolarWinds Security Event Manager completely free through a 30-day trial.
6. Sumo Logic

Sumo Logic offers cloud-native incident response tools in the form of a SIEM platform. It combines operations, business, and security intelligence information into one system to bring you a big picture view of your digital assets.
Key features:
- 150+ applications and integrations.
- Leverages machine learning.
- Continuous compliance monitoring.
By using artificial intelligence Sumo Logic reads between the lines of thousands of log files to identify indicators of compromise. These are subtle signs that an attack is in progress on your network. These signs aren’t always clear if you don’t have the proper incident response tools in place.
Additional features such as anomaly detection and root-cause analysis can measure your network’s baseline behavior and learn what normal traffic should look like. A machine learning process uses a patented pattern analysis algorithm to detect threats both externally and internally.
Through a single customizable dashboard, you can monitor and respond to threats across both on-premises and cloud environments. Information is broken down into signals and insights. Signals are security events that may point to bigger-picture problems and need further investigation.
Insights represent intelligently clustered and prioritized signals that are ready to be analyzed by the security team. These insights give deep context into the who, what, and where of an incident, and drastically cut down on investigation time. Both insights and signals are all automatically generated using artificial intelligence and forms of shared data.
Pricing for Sumo Logic is determined by how much data you process and relies on a credit system to keep costs predictable. You test out Sumo Logic yourself through a free 30-day trial.
7. Splunk
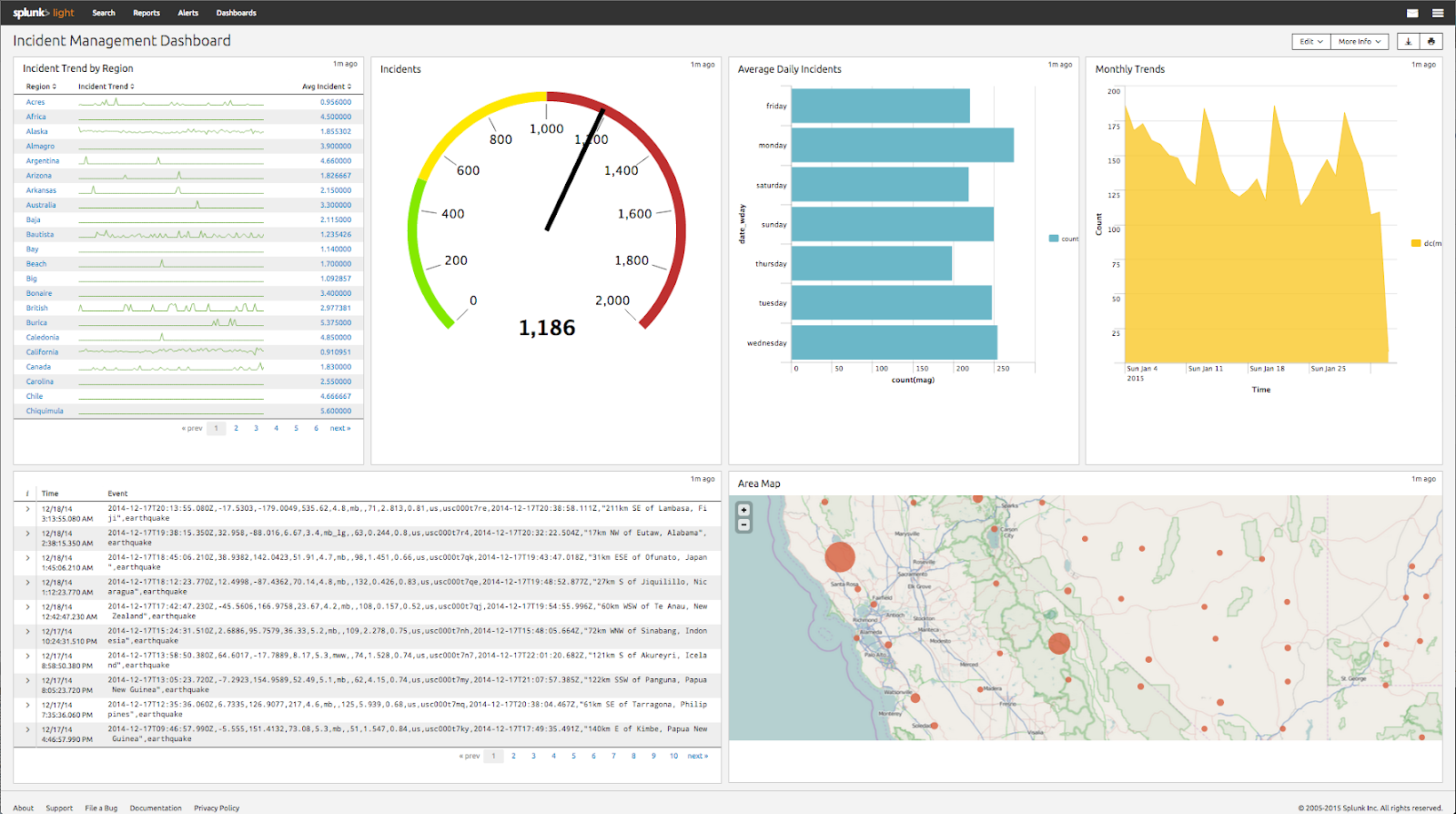
Splunk is a comprehensive incident response tool that is built to serve large enterprise networks. At the heart of Splunk’s incident response is AI-powered security monitoring and prevention. This system constantly monitors for suspicious behavior, attacks, and compliance violations.
Key features:
- Query-based real-time and historical analysis.
- AI-powered threat detection.
- Windows, Linux, and macOS compatible.
Splunk heavily relies on artificial intelligence and machine learning to power its security services, which actively scan through log data and monitor your network in real-time. Events are analyzed, clustered, and then assigned a threat score to let you know exactly how impactful a situation may be. This same intelligence is applied to internal user action to help identify insider threats. Repeated suspicious activity from a single user could trigger an alert for manual review, or a machine showing signs of compromise can automatically be isolated from the network
Reacting to threats can be done through Splunk’s Asset Investigator and log search. Here you can review automatically flagged incidents and either launch an investigation or change how Splunk’s automation handles those types of events.
Searching Splunks logs is intuitive but will require you to understand their Search Processing Language (SPL) If you’re a data scientist or are familiar with other query languages, SPL isn’t difficult to learn. This may introduce a learning curve to those who have never worked with large amounts of data before.
Splunk is built to scale so pricing will vary depending on your size and data needs. A trial version of Splunk is available on the company homepage.
8. Rapid7 InsightIDR
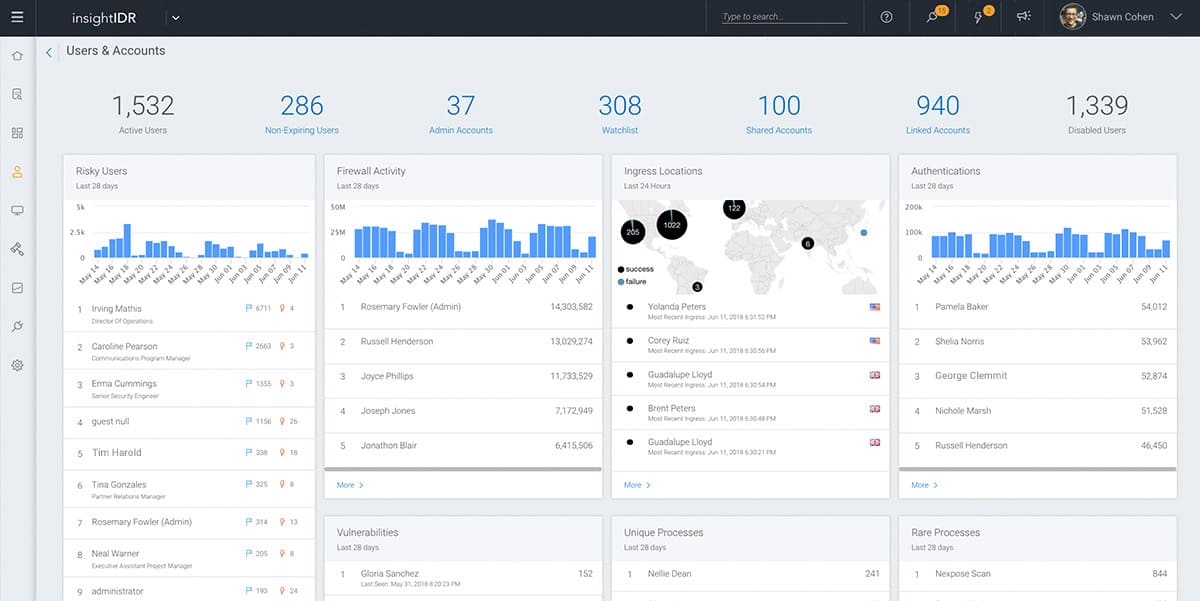
Rapid7 InsightIDR is a cloud-based SIEM built to provide complete visibility across your network no matter how large it is. InsightIDR provides features that are more geared towards larger enterprises but could be implemented in medium-sized environments as well.
Key features:
- Managed service option.
- Threat identification.
- Ability to build honeypots.
With a combination of behavioral analytics, automated actions, and log management, InsightIDR reports are able to reduce response time by one-third of the most unmanaged environments. The platform uses AI to start monitoring your networking traffic right away. It does this so it can protect your environment as well as begin to form a baseline of what your day-to-day traffic looks like.
The main dashboard displays your entire network at a glance and can be tailored to your liking. Stats such as events processed, physical locations, events processed, and outstanding alerts are all visible from a single pane. InsightIDR also stores and processes what it labels as “notable behaviors.” These events alone don’t raise any alarms but could be useful to look over if a threat or incident occurs. It’s this level of historical information that will help bring context to an attack and ultimately resolve the breach faster.
InisghtIDR also uses data pulled from external global databases to help identify known attackers. Behavioral analytics can identify unmasked threats sometimes by their actions alone. Another unique feature of InsightIDR is the ability to set honeypots. These exist within your network as traps for attackers and help sound the alarm before they’ve reached your critical assets.
Lastly, if you like the idea of having incident response capabilities, but don’t want to hire in-house for it, Rapid7 offers this as a managed detection and response service. Rapid7’s security team will manage and implement solutions on your behalf using InsightIDR.
Pricing for InsightIDR is currently $2156 (£1635.81) per month, billed annually.
9. LogRhythm
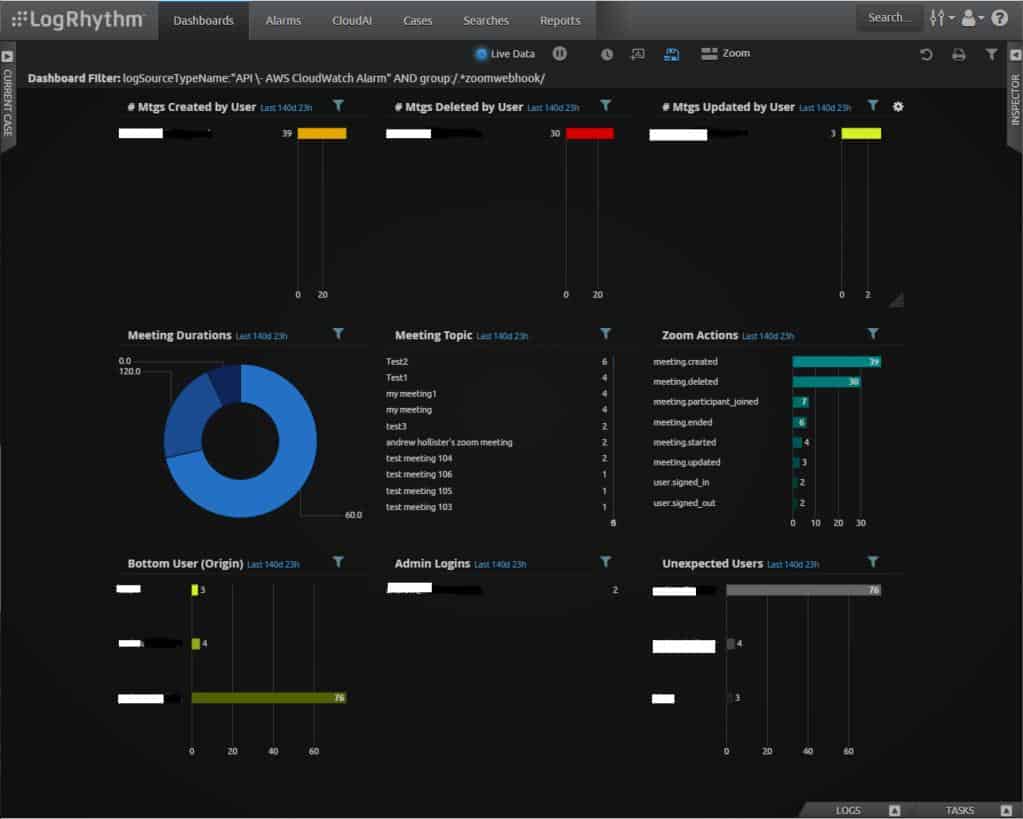
LogRhythm combines search analytics with machine learning to provide swift incident response and actionable security insights for your network. The platform uses an Elasticsearch back-end, which can create a steep learning curve for those who have never used the open-source search tool.
Key features:
- Response playbook.
- Automated Smart Responses.
- Open source Elasticsearch back-end.
The engine searches your logs for patterns, threat indicators, correlations, and behavioral changes to recognize and stop threats before damage can be done. Automated actions can be configured by using rulesets, and real-time alerts can notify the security staff of stubborn advanced persistent threats.
While other signature-based tools miss clever malware attacks, LogRhythm reads between the lines and can identify attacks based on their behavioral patterns, not just by their payload signature. When LogRhythm does detect an anomaly or threat, it’s assigned a calculated risk score, giving you a simple way to prioritize your team’s workload.
Specific incidents can even be assigned playbooks. These playbooks are step-by-step troubleshooting and resolution guides that are designed to give any technician the information needed to remediate an attack. These playbooks not only help guide a technician through solving the issue, but also store the information gathered as digital evidence.
Incident response tools like hash lookups and host queries give you everything you need to identify and stop a threat all from one screen. Lastly, LogRhythm provides Smart Responses for each identified threat. These act as automated suggested courses of action to stop the threat.
Pricing for LogRhythm is not publicly available. To test the tool out for yourself you can request a demo from the official site.
10. AlienVault USM

AlienVault USM provides threat detection, incident response, and compliance management to form a complete umbrella of security for medium to large sized companies. Sensors and endpoints deployed throughout your network work to gather both log data and contextual information. The AlienVault USM is now part of AT&T Cybersecurity which also offers a host of additional security services and tools businesses may want to explore as well.
Key features:
- Available for Linux and Windows.
- Behavioral monitoring.
- Intrusion detection.
The platform uses a web portal to interact and monitor both the on-premises and cloud-based installations of AlienVault. The dashboard is clean and displays insights as a combination of charts, graphs, and counters, giving you a holistic look at your network health.
Outside of just incident response tools, AlienVault provides services such as vulnerability assessments, compliance audits, and penetration testing.
USM pricing comes in three tiers and starts at $1075.00 (£815.66) per month, billed annually. Pricing may be customized depending on size, usage, and support options when you reach out to their sales team.
11. OSSEC

OSSEC is one of the most popular open-source host-based intrusion detection systems on the market. Their platform is powered by a robust correlation and analysis engine that uses integrated logs from across your network to develop a faster incident response, and an overall stronger security posture.
Key features:
- Open-source.
- Runs on Linux, Windows, and macOS.
- Both on-premises and cloud-based hosting.
OSSEC can be seen as a hybrid tool, as it shares some characteristics found in SIEM tools, while also providing Host Based Intrusion Detection Services (HIDS). OSSEC can be configured to cover issues ranging from rootkit and malware detection, file manipulation, compliance auditing, and advanced persistent threats.
The incident response portion of OSSEC offers both automated threat management as well as self-healing actions that can be applied if a threat is detected. These actions can be launched both manually or automatically. OSSEC has dozens of third-party integrations, which makes it a great addition to existing network security tools.
OSSEC is completely open-source and free to use. As with all open-source platforms you will be responsible for applying updates, maintenance, and finding support.
Conclusion
No matter what size network you’re in charge of, SolarWinds Event Security Manager can provide a fast and efficient incident response in virtually any environment. SEM also offers proactive pre-made security solutions that will cut down on the number of incidents created.
Do you have a favorite incident response tool? Be sure to let us know in the comments below.