
Ransomware is by far the scariest cyber threat we face today. As time goes on, ransomware attacks get smarter, and the amount of money that needs to be paid keeps going up. Cloud backups are an important part of a security plan, but is it even possible to keep ransomware away from backups?
In response to the growing number of threats, organizations use policies, software, and strategies for data security that are meant to reduce the risk. Even though the main goal is to stop and avoid ransomware attacks, it’s just as important to have a plan for how to recover from one if it does happen. With a cyberattack happening every 36 seconds, it’s no longer a question of if you’ll be attacked, but when.
Today, businesses have a lot of tools at their disposal to improve their cybersecurity. One of the most important security tools is a backup of your data that is stored offsite or in the cloud and follows the 3-2-1 rule.
What is an Attack with Ransomware?
Ransomware is a type of malware that gets on your computer and locks down your files, folders, software, and other systems. Once it’s attached to your systems, it encrypts all of your data so you can’t access or use it.
The person or group in charge of the ransomware then sends you a message saying they’ve taken over your files and want a ransom to unlock them. Until you pay the ransom, you won’t be able to get to your files.
Most companies will usually pay the ransom because even a short period of downtime could be disastrous for their business. As shown by the hack of the Colonial Pipeline in the second quarter of 2021, ransoms can range from a few hundred dollars to thousands or even millions of dollars. Since 2019, ransom amounts have gone up by 171%, according to the latest data.
What Makes Ransomware so Bad?
Small businesses often think that ransomware won’t affect them, but the truth is much sneakier. In 2019, nearly a third of cybercrime victims were small and medium-sized businesses, and this number is likely to keep going up.
Sometimes, bad people like to target small businesses because they know their security isn’t as good as it should be. So don’t assume you’re not a target. Ransomware is a major threat to businesses of all sizes and types. No one is safe.
But ransomware attacks pose other risks besides keeping you from accessing your important business data. Most of the time, it takes weeks for ransomware to completely take over a company’s systems. During that time, the bad guys have full access to your sensitive files, folders, and financial information, which they could easily steal and either sell on the dark web or use as more leverage to try to get you to pay twice.
Plus, there’s no guarantee that these criminals will stick to what they say. Even if you pay them, they may leak your information anyway.
Imagine that the leaked data includes personally identifiable information (PII), financial data, payment data, or intellectual property that belongs to one of your clients. In that case, you could be fined by the government and sued, and your company might not be able to recover.
How ransomware works
Emails are the way that ransomware gets into your system. In an attachment is the code for encrypting the system. Another way is through malicious websites that pop up a message saying that the visitor’s computer is infected and they need to download a tool to get rid of it.
Ransomware can be hidden in PDFs, ZIP files, RAR files, IMG files, and ISO files. Of course, EXE files can also be infected with ransomware.
At first, ransomware only locked up the computer it was downloaded to. So, if one of your users opens an email attachment or downloads a file from a website, only the files on that user’s device will be encrypted. So, user devices are the most likely to be attacked, but ransomware packages can travel across a network if they are smart enough. Syncing makes it possible for viruses to be put on shared drives at a later time.
Those infections that spread through networks can do a lot of damage. If they get onto your central servers, where you keep your databases, you could be in big trouble. These ransomware attacks would go to your backup system and could infect it. Ransomware is a type of attack that makes it important to protect your backups.
Keep Ransomware Away from Your Backups
Stop ransomware from destroying your backups by stopping viruses before they reach your backup server. A backup copy that has been hacked is useless. Even if the ransomware can’t or doesn’t work on the backup drive, it will just infect the protected device again when you restore the backup.
Four Things You Need to Do to Avoid Getting Ransomware
- Don’t let people download viruses and other bad files.
- Don’t let infections spread through the network.
- By syncing, you can stop ransomware from putting files on shared drives.
- Don’t let ransomware get on the backup server.
The wrong approach is to try to get rid of ransomware from a backup server. The only way to keep ransomware from getting to backups is to stop it from getting there in the first place.
Secure Backup Strategies
There is no backup strategy that will completely keep ransomware away from backups. You should follow a few rules when doing backups to make sure that your system can be put back together easily.
The 3-2-1 Rule
The 3-2-1 system is the traditional rule for backup. You should do this a lot. This system needs you to make three copies of every file on your computer:
- The first record
- On-site copy on a different medium
- A copy that is not on the site
Many system administrators strongly suggest that the first backup be saved to a removable storage medium, like DAT tape.
Full, differential, and incremental backups
The second copy that is kept on-site and the third copy that is kept away from the office need different plans.
There are three ways to get a copy of something.
- Complete backup Copy everything.
- Differential backup Copy everything that’s changed since the last full backup.
- Incremental backup Copy everything that has changed since the last backup of any kind.
Full backups take longer than differential and incremental backups to fixed drives, either on-site or off-site. They are hard to perform on tape, though. For full backups, tape is better.
You don’t have to use both your onsite and offsite backups the same way. You should also get a safe place, like a fireproof safe, to store your onsite tapes.
Changes and Rollbacks
The best backup plan for your business will depend a lot on how big it is and how busy it is. System managers have traditionally been told to do a full backup once a week and an incremental or differential backup every day. This might be too infrequent for a fast-paced business like a stock trading platform where every second of data processing is important.
Running backups through versioning is a good way to protect them from ransomware. Instead of doing an incremental backup that deletes older copies of certain files that were backed up, the system keeps the original state and saves the new version separately. Since these versions are usually stored on the same drive, an infection in the most recent version will wipe out all of them.
You can implement versioning in a way that lets you go back to a clean copy. This is about the best chance you have of recovering from a backup that has been infected by a ransomware executable file.
Since the 3-2-1 rule gives you two copies of every file, you can use versioning on one store and incremental backups on another. There are sophisticated software tools for managing versions, but you can also do it simply. That is, make sure your backup to tape on site is full every day.
Plan your tape backup for when the batch processes that run overnight are done. This makes sure that you have the most up-to-date information before people come to work.
The most common time for ransomware attacks to happen is during business hours because users usually start them. In these situations, you can shut down the system and then bring it back from a backup tape. All of the transactions from that day will be erased for the time being. But this is better than doing nothing and will get rid of the ransomware program.
Once the system is back up and most of the users’ data is back, you have time to look through the offsite incremental backup, compare file versions, and see where you can provide a more recent version of certain files. This plan would work for a site with a lot of traffic and backups that are done at different times of the day.
Multiple Back-Ups
Protect your backups from ransomware by making it hard for the program to spread from one type of data to another. Run different backup systems for different kinds of data and even assign other people to take care of backups. DBAs make it clear who does what when it comes to backing up. The DBA should make sure that the database is backed up separately from all other data stores.
The database could be backed up to a different cloud storage account, which would keep it completely separate from backups of the file server, which would be the job of the system administrator. You can back up each desktop separately with its own cloud account. This plan will keep ransomware from destroying your backups by limiting the spread to just one backup location.
Keep in mind that ransomware is most likely to get into a user’s computer. If you can keep it there, all of your other devices and backup stores will be safe.
The Best Tools to Protect Your Backup Data from Ransomware Attacks
1. ThreatLocker (FREE TRIAL)
ThreatLocker is an advanced cybersecurity tool that can protect your backups from ransomware attacks. This tool allows only pre-approved applications to get installed on any device in your network, and this means that malicious files like ransomware will be blocked right away. Also, it comes with a feature called Ringfence, which requires permissions for an application to access resources and interact with other applications.
Moreover, it monitors inbound traffic and activities in your network and reports anomalies to the concerned employees, so action can be taken immediately. Due to these features, ThreatLocker can prevent ransomware attacks on your assets.
Start a 30-day free trial.
2. ManageEngine Endpoint Central (FREE TRIAL)
ManageEngine Endpoint Central provides many tools for monitoring and managing a fleet of endpoints, which includes scanning for ransomware activity. The package prepares for defense by periodically backing up files so that they can quickly be restored. The ManageEngine system uses a native service in Windows to automatically take shadow copies of files. That means the tool is tailored to protect computers running Windows and not those that operate macOS or Linux.
ManageEngine offers Endpoint Central as a SaaS platform or you can opt to download the software and run it on Windows Server. The system is available for a 30-day free trial in both formats.
3. ManageEngine RecoveryManager Plus (FREE TRIAL)
ManageEngine RecoveryManager Plus offers extensive data protection from Ransomware attacks. This tool allows you to back up data from Active Directory, Azure, Microsoft 365, Google Workspace, and Exchange environments. In the event of an attack, it quickly restores data from the backups to minimize disruptions.
What we love about this tool is its flexibility. It supports both full and incremental backups, and even allows you to schedule backups at regular intervals to reduce human interference. Also, you can choose to store the backup data on the cloud or in local storage, depending on your organization’s security policies and compliance requirements. All these features protect your backups from ransomware attacks, while providing complete control over your backup and restoration processes. Download a 30-day free trial.
4. CrowdStrike
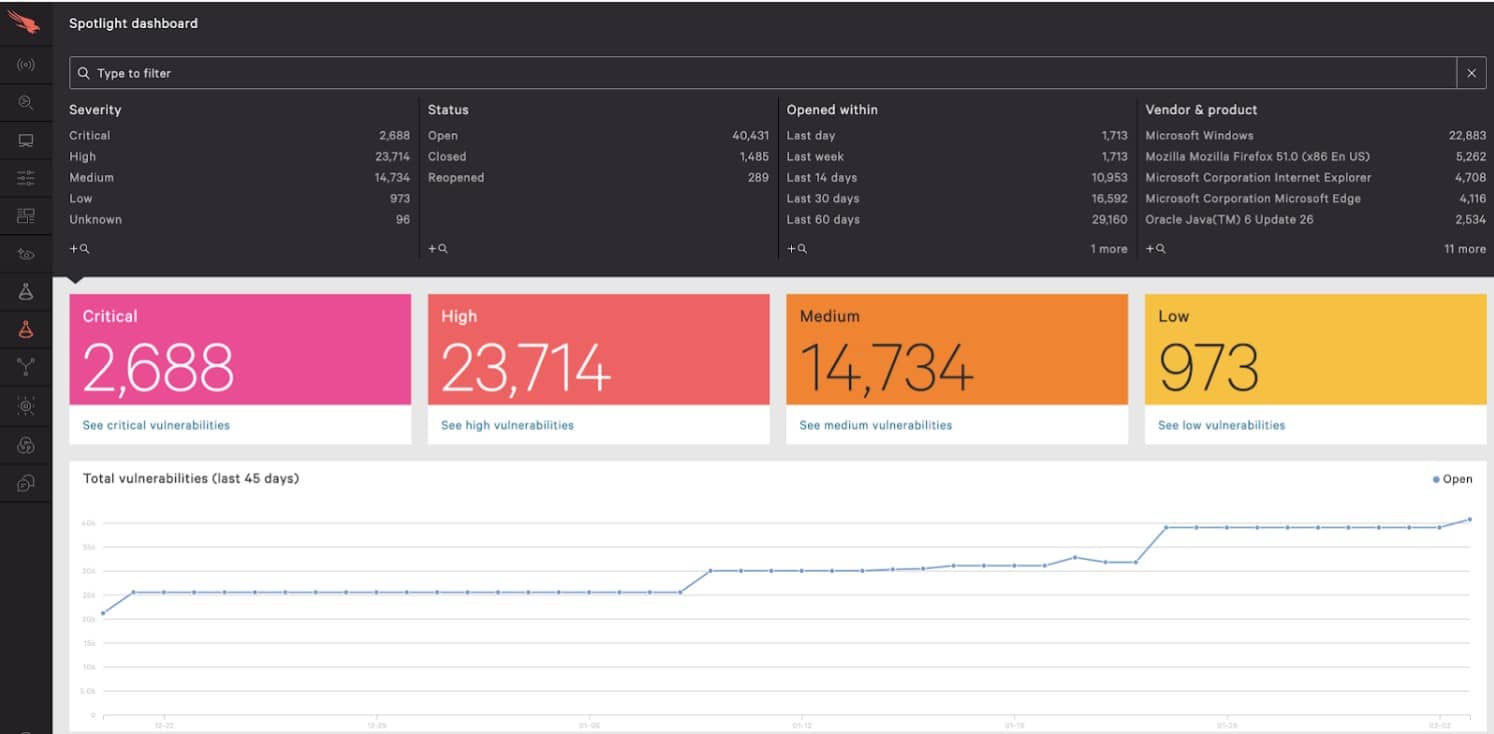
CrowdStrike Falcon is a set of products for security. Falcon Prevent is an endpoint detection and response system that is part of this line. It installs on every device on your network and protects each one from getting ransomware.
The Falcon system has a cloud console that keeps track of what each endpoint is doing. Even though Falcon Prevent should find and stop ransomware as soon as it hits a device, technicians are notified of the attack by a program called Falcon Insight.
5. SpinOne

It keeps files in the cloud from being changed. The system keeps track of who opens files and checks for ransomware. Another part of this package backs up and restores data. When an unauthorized change is made to a file, the system cuts off all API access right away. This blocks the source of the ransomware since programs don’t run in the data storage itself. This makes it much easier to stop the spread of ransomware.
The SpinOne system keeps infected files separate while it looks into where the attack came from. This keeps the damaged file from being copied to the backup store and wipes out the original content. Once the source of the attack has been found, the damaged files are thrown away and the backup copies are put in their place.
Once a ransomware attack has been stopped and fixed, the SpinOne system makes a report that explains what happened and how the threat was dealt with. The staff that manages the security software is part of the SpinOne service. On this staff are cybersecurity analysts. The service level agreement for Spin.ai says that the company will be back up and running in two hours (SLA).
6. ManageEngine DataSecurity Plus
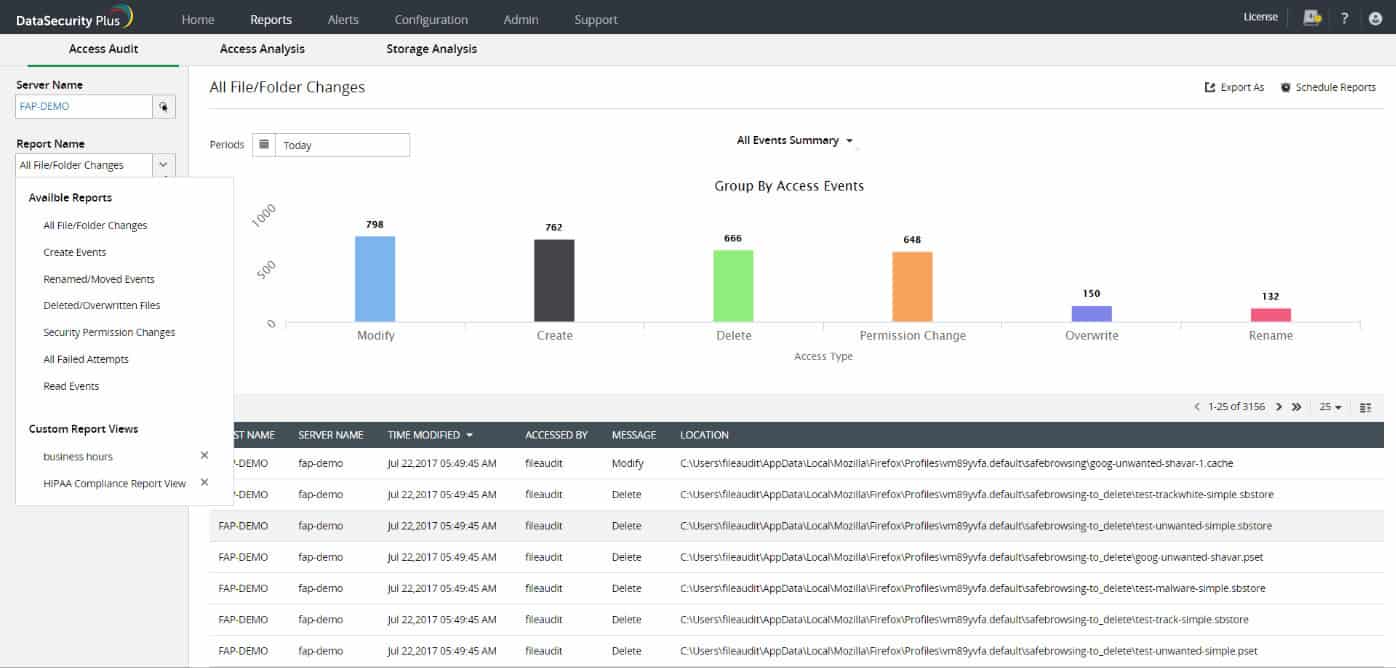
ManageEngine DataSecurity Plus is designed to prevent tampering with files, and as a result, it can detect any unwanted modifications that are made by ransomware. It is possible to adjust the settings of the file monitor so that it focuses on mass changes. This service safeguards computers running Windows, which is the operating system that is targeted by ransomware attacks the most frequently.
Even though a modification must take place before DataSecurity Plus can recognize it, the system is equipped with automated responses and technician notifications. One of the automated solutions is locking down the device that has been compromised, which will stop the ransomware from spreading to other computers on the network.





