One of several overlooked commands that can produce a world of hurt for networks is the IP Directed-broadcast command. This command was introduced in Cisco’s routers at IOS version 10. Cisco soon realized that this command was being maliciously exploited in denial of service attacks, and action had to be taken- particularly against smurf attacks.
How a Smurf Attack Works
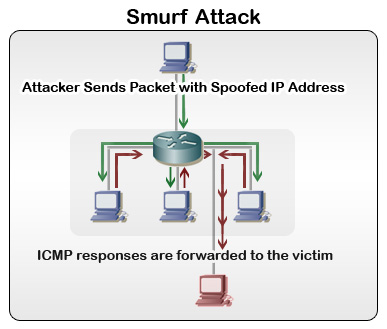
Smurf attacks are a type of denial of service attack, in which the Internet Control Message Protocol (ICMP) and broadcasts are being exploited. Normal ICMP requests (commonly referred to as pings) are used to verify network connectivity. But since they require a response from the target machine, they can maliciously be used to consume network resources if many are sent at once.
Broadcasts come into the equation, however, since they give capability to send requests to every computer on a network. Obviously if a broadcast were to be sent multiple times, the traffic would slow down the network. Imagine 100 computers sending back an ICMP request at the same time- network performance would take a huge dip.
It should be noted that smurf attacks work via an attacker spoofing the IP address of the broadcast. The IP address is actually the IP address of the victim the attacker chooses. When every computer on the network responds to the ICMP request, all of these requests go to the computer the attacker borrowed the IP address from. In this instance, the network only acts as an amplifier to the attack, not necessarily the victim.
Unfortunately, smurf attacks leave little room for victims to recover from an attack. Instead, the attack must be staved off at the network level via filtering. We can do this specifically through the no ip directed-broadcast command in Cisco routers.
No IP Directed-Broadcast
An IP Directed-Broadcast is simply an IP packet, of which has a destination address of a particular IP subnet. The broadcast in this instance is sent from a different network, as one could probably guess from the command name. (The broadcast is being directed via IP, not a unicast address.)
Keep in mind that if you are running a Cisco IOS version 12.0 or above, you do not need to follow these steps. No IP Directed-Broadcast was enabled by default after IOS 12.0. It is strongly recommended that No IP Directed-Broadcast be enabled if your IOS version is below 12.0. If you aren’t sure which version you have, simply type in the following commands from user exec mode:
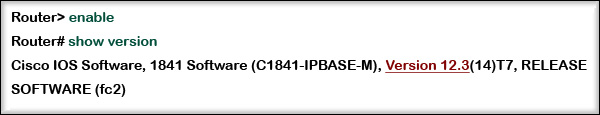
As you can tell in the above example, the version number is higher than 12.0. In this instance, we would not need to take further action. If the number happens to be below 12.0, then you will need to apply the No IP Directed-Broadcast command. First, you should find out the naming convention for your router’s interfaces, as show below.

Now that we know our interface naming convention, FastEthernet 0/0, we can modify it. You may wish to write this down, since this will be what you will always refer to your interfaces to from now on. You may now proceed to apply the command to the interface, as seen below.
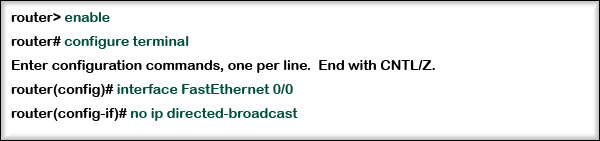
Note that we only applied this to a single interface (FastEthernet 0/0).It should be applied to all interfaces for maximum protection.
Closing Comments
Very few IP applications will make use of the IP directed broadcast, so it is almost always perfectly fine to leave it off. You can, however, configure access lists to permit or deny IP Directed-Broadcasts. This is usually only feasible with smaller networks, since access lists can be quite tedious to maintain on all but the smallest networks.
Photo Attribution: moniquewingard Flickr via Compfight cc
![SIEM Alerts Guide [Everything You Need To Know]](https://www.itprc.com/wp-content/uploads/2023/05/SIEM-Alerts-Guide-211x150.jpeg)


clear explanation
Amazing!
Solves my problem in 2 minutes……….
Good Explanation…
Hi there!
I read some of your posts on the blog and I must say congratulations!
Your post really direct people to the right information that they are looking for!
Great job! Keep it like this!
What is the protocol and what is the purpose of the
following address?
238 255 255 255
A. IPX a SAP broadcast
B. IP a multicast group
C. IP a reserved address
D. IP a directed broadcast
E. IPX a flooded broadcast
Very helpful explanation for Cisco 2 student lab.
Thank you!
could not understand the process of pinging,the ip directed broadcast.
Otherwise very good .
Well explained !!