An ounce of prevention is worth a pound of cure. It’s a cliché, but the old adage holds true in the world of network security. With so much of our valuable business and personal information residing within computer networks and productivity so interconnected with uptime, it is more important than ever to ensure that our network security is as robust as possible. In this article, we’ll provide an overview of an important component of network security; Intrusion Prevention Systems (IPS). We’ll start by defining what an IPS is, compare it to other network security technologies like IDS, review functionality, and close with software products that can help you get started with your next IPS/IDS deployment to block malicious activity.
Here is a quick list of the best IPS & IDS tools:
- ThreatLocker Detect EDITOR’S CHOICE A powerful platform that monitors endpoints for any unusual events or Indicators of Compromise (IoC), and sends alerts accordingly. Start a 30-day free trial.
- ManageEngine Firewall Analyzer (FREE TRIAL) Multi-vendor firewall log analysis and policy management with compliance reporting, bandwidth insights, and real-time monitoring. Download a 30-day free trial.
- ManageEngine Log360 (FREE TRIAL) Offers powerful threat prevention stopping internal and external threats using syslog aggregation, artificial intelligence, and behavior monitoring. Download a 30-day free trial.
- SolarWinds SEM Combines enterprise log management and threat detection to detect and prevent threats before they cause downtime.
- SNORT Highly customizable open-source IPS best for security experts
- Security Onion Intrusion detection/prevention designed specifically for Linux environments.
- Zeek A powerful and flexible security framework designed for cybersecurity professionals.
- WinPatrol Provides IDS through a simple GUI, ideal for smaller network environments.
- Osquery Leverage SQL to capture data on each device to detect malicious intent.
What is an IPS?
An IPS is an IT security system that monitors for malicious activity on a network (e.g. a DoS or DDoS attack) and proactively attempts to mitigate the damage created by the activity or prevent it altogether.
Oftentimes, IPS solutions are dedicated hardware appliances that run IPS software. A popular example of these hardware IPS devices is Cisco’s Firepower NGIPS (Next Generation Intrusion Prevention System) product line. These robust cybersecurity devices are often found in enterprise networks. In home networks these dedicated IPS devices would generally be overkill and IPS is handled by a router or software running on a computer. In both use cases the purpose of the IPS is the same: identify and mitigate security risks on the network.
How is an IPS different from a firewall?
Given what we have covered to this point, you may be wondering “why do I need an IPS if I have a firewall?” If a firewall is properly configured, what benefit can an IPS provide? These are good questions, and the answer becomes clear once you understand that firewalls and IPS operate in different ways and solve different problems.
A traditional firewall implements rules that prevent network traffic based on protocol, source/destination address, and/or source/destination port. Firewalls can help you implement access control lists and prevent the use of insecure protocols. For example, if you need to block all traffic on TCP port 23 (Telnet’s default port), a firewall rule is the way to go.
However, oftentimes attacks occur in ways that do not violate firewall rules.
For example, consider a brute force SSH attack on a server. If the server generally accepts connections via SSH, there will not be a firewall rule blocking the port. This is where IPS could come in. IPS works by analyzing the headers and payloads of packets and if suspicious behavior is detected, it can drop the packets. In short, by analyzing the entirety of network packets, IPS can detect potential malicious behavior that does not inherently violate firewall rules.
Host Based IPS and Network Based IPS
IPS can be deployed either at the host level or the network level. Host-based IPS monitors and protects the specific host (e.g. a single PC) it is installed on. Network-based IPS on the other hand focuses on protecting an entire network. Generally, a network-based IPS gives you better overall visibility and protection by mitigating issues before they make it onto network endpoints that contain critical data. On the other hand, a host based IPS make sense when you consider the benefits of defense in-depth, monitoring changes to local files, and detecting attacks that begin from within those endpoints (for example a program launched from a flash drive).
IPS vs IDS
The terms IPS and IDS (Intrusion Detection System) can sometimes be confused with one another. This makes sense given that many products support both and IPS is essentially a extension of IDS. In fact, IPSes are sometimes referred to as “reactive IDS” or “proactive IDS”. The fundamental difference between an IPS and an IDS is that an IPS proactively attempts to mitigate threats while an IDS simply detects them.
To help conceptualize the difference, let’s consider what an IPS and IDS would do if malicious activity is detected. To detect the threat, both technologies scan packets looking for suspicious activity (more on how this works in the next section). Once the threat is detected, an IDS will write to a log file and/or send a notification, whereas an IPS would also drop the packets. The tradeoff here is that an IPS offers the benefits of preventing an attack while IDS lowers the likelihood of false positives affecting performance.
Signature based detection vs anomaly based detection
At a high level, IPS detects threats using one of two methodologies: signature-based detection or anomaly-based detection. Signature-based detection compares network traffic to a database of known threats, and takes action when the traffic matches the patterns (or “signature”) of a predefined threat.
On the other hand, anomaly-based detection first creates a baseline of network activity and then compares traffic to that baseline. If network traffic deviates significantly from the baseline, it can be interpreted as a threat. Given the heuristics involved in anomaly-based detection it can be a good way to help reduce the threat of zero-day attacks on a network that signature-based methods would not yet have a signature to compare to. Given their complexity, anomaly-based detection systems can be more difficult and expensive to develop.
The Importance of SIEM Software
Security information and event management software products, or SIEMs help aggregate and analyze data related to network security. This includes data from endpoints running IDS or IPS software. SIEMs help make IPS and IDS more scalable and can better enable organizations to achieve compliance, improve reporting, and identify correlations that can indicate a broader threat. In short, SIEMs enable organizations to scale their IDS and IPS data into a more complete security solution.
Now that we have established an understanding of IPS, IDS, & SIEM;
Our methodology for selecting intrusion protection systems
We reviewed the market for intrustion protection systems and analyzed tools based on the following criteria:
- Assess your current infrastructure and future needs like threat detection, compliance, and incident response
- Consider detection techniques, real-time monitoring and alerts, threat-hunting capabilities, live network monitoring, and integration
- Deployment options like on-premises vs. cloud-based
- Know pricing structure and cost of ownership, and also review hidden fees if any
- Explore the free trial and look for the money-back guarantee
- Look for training, community support and peer feedback
1. ThreatLocker Detect (FREE TRIAL)
ThreatLocker Detect is an endpoint detection and response tool that proactively monitors every endpoint to identify abnormal events and patterns. It is a policy-based tool that allows you to set up custom policies to identify specific threats, and also take remedial actions automatically.
Key Features:
- Automated Response: It can be configured to take automated responses when an event is detected.
- Custom Policies: Enables you to set custom policies, based on which it detects and responds to anomalies.
- Dashboards: Presents all findings on an intuitive dashboard, allowing everyone to better understand the data.
- Recommendations: Provides appropriate recommendations based on MITRE and CISA frameworks.
Why do we recommend it?
We recommend ThreatLocker Detect, as it analyzes data from endpoints, other ThreatLocker modules, and Windows system logs to identify both known and unknown threats. You can configure it to take actions automatically, like blocking activities, shutting down a device, and more. Such actions can prevent the further spread of an infection, limiting its impact on your network.
Also, ThreatLocker can recommend actions based on frameworks like MITRE and CISA. More importantly, it can help you comply with regulations.
Another highlight of this tool is its dashboards. All the gathered and analyzed data is presented in an easy-to-understand format on the dashboard, making it easy for people from different backgrounds to understand the security posture as well as the issue. Such an approach improves stakeholder communication and trust.
Who is it recommended for?
ThreatLocker Detect works well for organizations of all sizes. It is also a good choice for MSPs who have to manage the security of clients’ devices and networks. It can be particularly useful for organizations that have stringent compliance requirements.
Pros:
- ThreatLocker Community: Experts can share their policies with others.
- Automated Actions: Ensure that incident response aligns with the organization’s security/
- Microsoft 365 Support: Detects anomalies in M365 environments.
- Cyber Hero Team: Provides policy recommendations based on frameworks.
Cons:
- Limited Integrations: Fewer integrations with existing applications.
Overall, ThreatLocker Detect can help across the entire process, from identifying to remediating threats and their impact on your organization. Start a 30-day free trial.
EDITOR'S CHOICE
ThreatLocker Detect is an end-to-end intrusion prevention, detection, and remediation platform that can protect your environments from cyberthreats. Its comprehensive features and wide-ranging support make ThreatLocker the top choice. Starting from using a structured process for identifying known and unknown threats to providing recommendations based on frameworks, this platform can help you stay on top of events and anomalies. Its automated actions act as the first line of defense, while its dashboards provide the insights you need for informed decision-making.
Download: Start a 30-day FREE Trial
Official Site: https://www.threatlocker.com/try-threatlocker
OS: Windows, macOS, Linux, Cloud/SaaS and Hybrid
2. ManageEngine Firewall Analyzer (FREE TRIAL)
ManageEngine Firewall Analyzer is a vendor-agnostic tool for analyzing firewall logs and managing policies. It supports more than 50 firewall brands — including Check Point, Cisco, Juniper, Fortinet, and Palo Alto. It collects and analyzes firewall, VPN, IDS/IPS, and proxy logs without requiring any agents. The platform can also deliver real-time insights into traffic, user activity, and policy compliance.
Key Features:
- Vendor-Agnostic Coverage: Works seamlessly with 50+ firewall vendors. This is perfect for centralized monitoring in mixed environments.
- Agentless Log Analytics: Collects and analyzes logs from firewalls, VPNs, IDS/IPS, and proxies. Ideal for fast root-cause investigation.
- Policy/Rule Management: Detects anomalies and suggests cleanup/reorder actions. This helps improve performance and security.
- Compliance Reporting: Generates out-of-the-box reports for PCI-DSS, ISO 27001, GDPR, HIPAA, SOC 2, and more. Includes automated audit scheduling.
- Real-Time Monitoring & Alerts: Tracks VPN usage, proxy activity, and bandwidth spikes from a single pane of glass.
- Forensics & Investigations: Reconstructs incidents with raw log reviews and aggregated database views.
Why do we recommend it?
ManageEngine Firewall Analyzer excels at bringing together various components, such as multi-vendor firewall monitoring, rule optimization, and compliance automation, into one platform. This combination reduces the need for having multiple point solutions. It also shortens the time you need to spend between detection, analysis, and remediation. The solution also does not need agents. This agentless architecture simplifies deployment, even in distributed or resource-constrained environments.
The built-in compliance reporting templates are extremely useful for regulated industries such as finance or healthcare. They automate much of the audit preparation process, which can save time and money.. We also recommend this solution for its policy analysis tools, which are perfect for quickly identifying unused or conflicting rules.
If your organization is operating multiple sites or managing firewalls for multiple clients, we recommend the Enterprise Edition’s multi-tenant architecture. It also comes with high availability features that support MSSP workflows and ensure consistent visibility across all deployments.
Who is it recommended for?
We recommend Firewall Analyzer for enterprises and MSSPs. Any organization that is focused on compliance and manages large firewall fleets would find this solution quite useful. It’s also ideal if your team needs real-time monitoring and proactive rule management without locking in with a special vendor.
Pros:
- Multi-Vendor Compatibility: Broad support with agentless deployment across diverse environments.
- Policy & Compliance: Strong policy optimization and compliance automation built in.
- Real-Time Visibility: Dashboards and instant alerts enable faster response.
- Scalability: Flexible enough to handle SMB setups through large, distributed enterprises.
Cons:
- Performance at Scale: Can experience slower performance with very high log volumes unless properly sized.
ManageEngine Firewall Analyzer is not really an IDS or IPS—meaning it doesn’t inspect network traffic for threats or actively block them. Instead, it is a centralized, vendor-agnostic platform for policy optimization, security forensics, and compliance automation. It acts as a central management and forensic layer over IDS/IPS tools. So it integrates with existing IDS/IPS systems, collecting their logs and correlating alerts with firewall data. Download 30-day free trial.
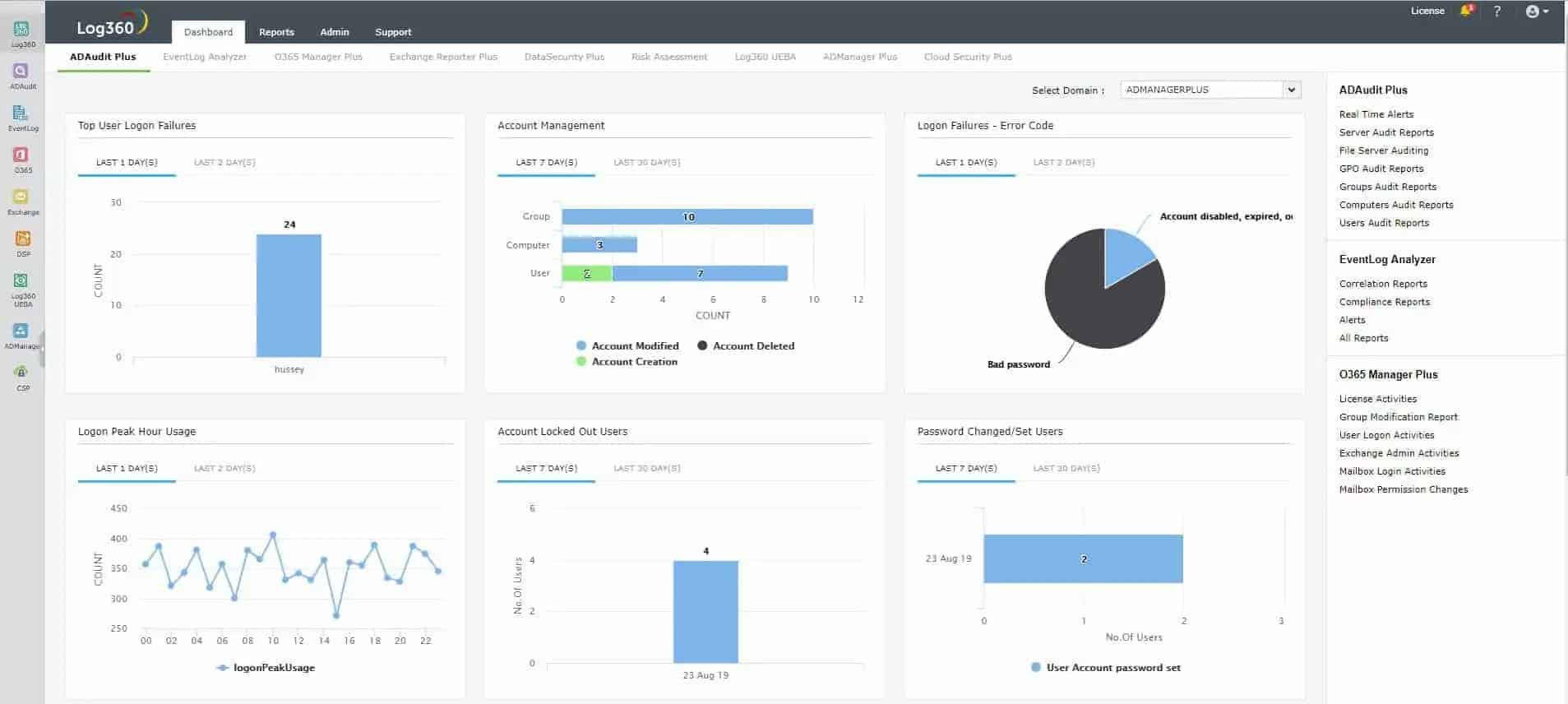
3. ManageEngine Log360 (FREE TRIAL)
ManageEngine Log360 is a unified SIEM solution with integrated DLP and CASB capabilities that detect, prioritize, investigate, and respond to security threats. It combines threat intelligence, machine learning-based anomaly detection, and rule-based attack detection techniques to detect sophisticated attacks.
Key Features:
- Incident management: Organizations of any size can easily manage occurring incidents with the help of real-time alerts.
- Custom Templates: Includes built-in custom templates which can be used fulfill your internal security policies.
- Ticketing Tools: Can also be integrated to receive real-time alerts from ticketing tools like service desk, jira, and more.
- Multi-Environment Compatibility: Helps to prevent intrusion and threats in all environments, whether it is virtual, physical, or cloud.
Why do we recommend it?
ManageEngine Log360 is a comprehensive Security Information and Event Management (SIEM) solution that excels in detecting, prioritizing, investigating, and responding to security threats. What sets it apart is its integrated Data Loss Prevention (DLP) and Cloud Access Security Broker (CASB) capabilities. This platform combines various threat detection techniques, including threat intelligence, machine learning-based anomaly detection, and rule-based attack detection, to effectively identify and counteract sophisticated attacks.
With Log360, you can monitor all security events compiled from your Windows and Linux/Unix machines; IIS and Apache web servers; SQL and Oracle databases; and perimeter security devices such as routers, switches, firewalls, intrusion detection systems, and intrusion prevention systems in real-time through interactive dashboards, out-of-the-box reports, and graphs.
Log360 collects logs from various sources, including end-user devices, servers, network devices, firewalls, and antivirus and intrusion prevention systems, and analyzes logs easily on dashboards displaying information in the form of graphs and intuitive reports, which help with discovering attacks, spotting suspicious user behaviors, and stopping potential threats.
Who is it recommended for?
ManageEngine Log360 is highly recommended for organizations seeking a unified solution to enhance their security posture. It’s particularly beneficial for those looking to streamline threat monitoring and incident response with the integration of SIEM, DLP, and CASB features. With support for various integrations and the ability to monitor a wide range of security events from different sources, it is a valuable tool for IT staff responsible for safeguarding networks, servers, and critical systems. Additionally, its real-time Active Directory monitoring is an asset for organizations aiming to detect and mitigate insider threats effectively.
Pros:
- Free Trial: Offers a hassle-free 30-day free trial period to explore its all advanced features.
- Mitigate External and Internal Threats: Intuitive dashboards and reports tab in the tool which allows you to monitor internal and external threats.
- Custom Log Parser: Helps you to analyze audit logs in readable format.
- Compliance Reporting: Users can use pre-defined templates to create reports compliant with GDPR, PCI, DSS, SOX, and much more.
Cons:
- System Dependent: Might need a high-end computer to run this tool properly with few technical specifications required.
IT staff can also use the platform for post-attack analysis to assess the impact of security incidents and identify the attack pattern to stop ongoing attacks through log forensics. Additionally, Log360 can monitor and audit critical Active Directory changes in real time, allowing you to track suspicious user behavior, monitor critical changes in groups and OUs, and proactively detect insider threats. Start a 30-day free trial.
4. SolarWinds Security Event Manager
SolarWinds Security Event Manager (SEM) is an enterprise log management solution with a focus on network security. SEM is a virtual appliance running a pre-hardened Linux operating system and can be deployed on VMware vSphere or Microsoft HyperV hypervisors.
Key Features:
- Compliance Reporting: Built-in report templates for PCI DSS, HIPAA, SOX, and more which will provide real-time log analysis and log correlation.
- Cyber Threat Intelligence: Helps to analyze log data and cyber threat feeds so that admins can quickly respond to network threats and user issues.
- Automated Incident Response: Preconfigured and customizable actions by which you can easily respond to the triggered threats and stop them.
- File Integrity Monitoring: Detects and alerts for any file, folder or registry changes to prevent data loss and theft.
Why do we recommend it?
SolarWinds Security Event Manager (SEM) stands out as a comprehensive and user-friendly solution for intrusion detection and prevention. It offers enterprise-level log management, and prioritizes network security. SEM’s virtual appliance and flexible deployment options make it highly adaptable to various network environments. Notably, its integration of a Snort log analyzer and threat intelligence feeds enhances its threat detection capabilities.
Who is it recommended for?
SEM by SolarWinds is an ideal choice for enterprises and organizations looking for a robust intrusion detection and prevention system. It suits those who value the convenience of virtual appliance deployment and want to bolster their network security. Whether in large-scale corporate networks or smaller setups, SEM provides the necessary features and scalability for effective threat management and event monitoring.
Pros:
- Valuable Log Data: Intuitive UI and easily deploys virtual appliances which will give you valuable data from logs in less time.
- Easy Compliance and Reporting: Quickly prepares audits for reports for HIPAA, PCI, SOX, DSS, etc.
- Quick Response to Cyber Threats: Security event manager that helps you to automate the response with correlation rules, allowing you to change privileges, block devices, and much more.
- Risk Reduction: Keeps an eye on network activity 24/7 and provides useful insight hence admin can work on the issues and reduce risk impact with faster response.
Cons:
- Technical Knowledge Required: Many users reported that it is quite expensive and requires a proper understanding of technical knowledge for hardware implementations.
In addition to a variety of reporting and monitoring features, SEM includes features like a Snort log analyzer (more on Snort below) and threat intelligence feeds that help compliment and scale your network security efforts. To try, download a 30-day free trial.
5. SNORT

SNORT is an extremely popular open-source IPS with a large community of users. In addition to running as a network-based IDS/IPS in Network Intrusion Detection System Mode (you can specify if you want to alert or block detected threats, thereby dictating if SNORT works as an IDS or IPS), SNORT can run in Sniffer Mode to work as a packet sniffer and Packet Logger Mode to log network traffic.
Key Features:
- Open-Source IPS: Uses a series of rules that allow users to detect malicious activity across the network.
- Live-Traffic Analysis: Helps admins to monitor network packets in real time with log scanning.
- Cisco System Supported: You can trust this tool as it is Cisco supported, hence providing robust security.
Why do we recommend it?
SNORT offers both Intrusion Detection System (IDS) and IPS capabilities, allowing users to choose whether they want to receive alerts or actively block detected threats. With its signature-based approach, SNORT provides effective threat detection and prevention, and it comes with a base set of policies that can be customized to suit specific security needs. The extensive user community contributes to a wealth of knowledge and rulesets, making it a valuable choice for those seeking an open-source IPS solution.
The IDS/IPS functionalities of SNORT are mostly signature based. SNORT comes with a set of base policies, but you can also write your own. While this may seem intimidating at first, the large community makes things a lot easier and helps contribute to a robust set of knowledge and rulesets available for SNORT.
As a bonus, if you are looking to get started working with a free IPS software that will have value even in enterprise applications, consider getting familiar with SNORT. Enterprise devices like Cisco’s 4000 Series Integrated Services Routers use SNORT for IPS and IDS.
Operating systems supported:
- Windows
- Fedora
- Centos
- FreeBSD
*Source code available
Who is it recommended for?
SNORT is recommended for a broad range of users, from individuals looking to enhance their personal network security to enterprise-level applications. Its versatility and community-driven development make it suitable for various scenarios. It’s particularly noteworthy for enterprises using devices like Cisco’s 4000 Series Integrated Services Routers, where SNORT is employed for IPS and IDS functionalities. The supported operating systems, including Windows, Fedora, CentOS, and FreeBSD, provide flexibility for different IT environments and preferences.
Pros:
- Free and Open-Source: Freely available so anyone can access it for intrusion detection and prevention.
- Wider Community Support: Documents, resource pages, tutorials, and broad community support for help.
- Three Modes: Packet logger, sniffer mode, and intrusion detection.
Cons:
- Cisco Bugs: Being open-source and easily accessible, users have noticed unexpected Cisco bugs that require frequent updating of this tool.
6. Security Onion
Security Onion is a Linux distribution that serves as a robust security solution, including IDS/IPS. Security Onion uses OSSEC for host-based IDS/IPS and SNORT & Suricata for network based IDS/IPS.
Key Features:
- Network Visibility: Covers your whole network and offers comprehensive visibility by collecting data from Zeek, Suricata, and various other tools.
- Host Visibility: Features an elastic agent for event collection and provides end-to-end host visibility for the organization.
- Timely Alerts: Users can receive alerts to manage events, packets, and content using security onion.
- Full Packet Capture: Can also use Security Onion to import the packet-captured files and do static analysis with window event logs.
Why do we recommend it?
Security Onion stands out as a comprehensive Linux distribution that offers a robust security solution with a focus on Intrusion Detection System (IDS) and Intrusion Prevention System (IPS). It leverages OSSEC for host-based IDS/IPS and incorporates SNORT and Suricata for network-based IDS/IPS. Additionally, Security Onion provides a range of security tools, including Elasticsearch, Logstash, Kibana, Bro, Sguil, Squert, and NetworkMiner. This integrated approach makes it a compelling choice for those seeking a one-stop solution for network security, especially when coupled with its user-friendly setup wizard.
According to the Security Onion website, in addition to the aforementioned tools, this Linux distro ships with Elasticsearch, Logstash, Kibana, Bro, Sguil, Squert, NetworkMiner, and a number of other security tools. While it may seem like an intimidating solution to get started with, it includes an easy-to-use setup wizard that helps streamline configuration.
Who is it recommended for?
Security Onion is recommended for security-conscious users and organizations looking for a comprehensive security solution that combines host-based and network-based IDS/IPS. Its diverse set of tools and user-friendly setup wizard cater to both experienced security professionals and those new to the field. Security Onion is particularly valuable for individuals or teams responsible for network security and monitoring, as it streamlines the configuration process and offers a wide array of tools to enhance security postures.
Pros:
- Advanced Features: Several advanced features catering to complex organizational needs.
- Highly Scalable: Scalable from a single network to a thousand nodes according to needs.
- Signature-Based Detection: Offers signature-based detection via robust protocols like Zeek, Suricata, and more to provide comprehensive network visibility.
- Easy Setup: Setup within a few minutes to have a distributed grid.
Cons:
- Limited to Linux: Specifically limited to Linux users so users with other platforms might face difficulty using Security Onion.
Security Onion itself is a Linux distribution. Download the ISO for free here.
7. Zeek Network Security Monitor

Zeek, formerly Bro, is a sophisticated network analysis framework that includes network-based IDS and IPS functionality. First developed by Vern Paxson, the project is now lead jointly by Vern and a team consisting of members from the International Computer Science Institute in Berkeley, CA and the National Center for Supercomputing Applications in Urbana-Champaign, IL. Zeek is popular in scientific, academic, supercomputing, and open source circles. Bro sponsors include Mozilla and the National Science Foundation.
Key Features:
- Traffic analysis: Gives you a detailed picture of network packets and their activity to spot intrusion or threats.
- Signature Detection: Detects malicious activity and threats based on the specific patterns and signatures.
- In-Depth Application Analysis: Provides deep application monitoring which will help you understand network activities.
- Automation: Admins can use automated scripts which will enhance the monitoring efficiency and faster response.
Why do we recommend it?
Zeek Network Security Monitor is backed by the expertise of Vern Paxson and a dedicated team from reputable institutions. Zeek is highly regarded in scientific, academic, and open-source communities, with support from prominent sponsors such as Mozilla and the National Science Foundation. Its approach to threat detection encompasses signature-based methods, anomaly detection, and behavioral analysis, making it a robust and flexible choice for network security.
Zeek supports signature-based detection methods, but that is not its only means of mitigating and detecting threats. Zeek takes a varied approach to detecting network threats that include anomaly-based detection and behavioral analysis. Additional benefits of Zeek include application layer analysis, passive monitoring, scalability to 100G networks, and its large development community.
Who is it recommended for?
Zeek Network Security Monitor’s support for diverse detection methods and extensive application layer analysis makes it suitable for various use cases. Zeek excels in both passive monitoring and scalability, making it an excellent choice for environments with high-speed networks. Security professionals, researchers, and those working with supercomputing and large-scale networks will find Zeek to be a valuable addition to their security toolkit.
Pros:
- Application Layer Analysis: Allows users to understand complex protocols and detect sophisticated threats that may bypass simpler, lower-layer inspections.
- Passive Monitoring: Allows you to observe network traffic without interfering and continuously monitor the threats.
- Scalability to 100G Networks: Capable of handling high-volume traffic and can be extended to 100G networks as per your organization’s requirements.
- Large Development Community: Large community and knowledge base that shares regular updates, plugin info, and much more.
Cons:
- Poor GUI: Many users reported that the Bro tool is not user-friendly as users must need technical understanding of SIEM, NIDS, IIDS, and other technologies to use it properly.
Operating systems supported:
- Linux
- Mac OS X
- Free BSD
You can try Zeek directly from your browser here.
8. WinPatrol
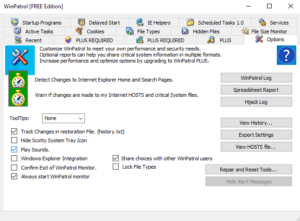
WinPatrol is significantly different from the other entries on our list as it is a Windows host-based solution. If you came to this article looking for an IDS software that can protect a Windows host against malicious traffic, this entry may be worth a look. The WinPatrol includes features that monitor changes in file type associations, creation of scheduled tasks, changes to your default search provider, changes to the registry, changes to hidden files, and more.
Key Features:
- Real-Time Intrusion Detection: Alerts you to unauthorized changes made by a person in critical system areas, allowing you to prevent malware infections and other suspicious activity.
- Scheduled Task Management: Monitor your tasks allowing you to modify, review, and stop the automated task.
- File Type Monitoring: Prevents threats as the tool will notify you when anyone tries to change the program or opens a particular file type.
- Security Alerts: Monitor and review past activity with constant security alerts to troubleshoot the problems.
Why do we recommend it?
WinPatrol is worth considering if you’re specifically seeking an IDS software to protect Windows hosts from malicious traffic. It offers a range of features that actively monitor and detect changes in critical areas of your Windows system, including file type associations, scheduled tasks, registry modifications, and hidden files. This level of host-based monitoring enhances your system’s security and helps prevent unauthorized changes.
Who is it recommended for?
WinPatrol is primarily recommended for Windows users and organizations looking to bolster the security of their Windows hosts. It’s particularly useful for those who want to proactively monitor and safeguard their systems against various threats, including potentially malicious changes and activities. While there is a free version available with essential features, users seeking more advanced protection and monitoring capabilities may consider upgrading to the premium version, WinPatrol Plus.
Pros:
- Behavioral Detection: Detects malware and makes sure of zero-day attacks by understanding activity behavior and signatures.
- Best at Malware Blocking: Experts find this tool useful for malware blocking.
- Protects Your Documents: Also protects from ransomware and protects your documents.
Cons:
- False Flagging: Many users noticed unwanted flagging of the application as malicious so this created a lot of confusion in the user’s mind.
WinPatrol offers a free version with a limited feature set relative to their plus offering. You can download the free version of WinPatrol here.
Operating systems supported:
- Windows
9. Osquery
Osquery is a Facebook Open Source project that enables a very unique approach to intrusion detection. Osquery uses basic SQL commands to capture data on a device.
Key Features:
- SQL-Based Query Interface: You can write SQL queries to run processes, read system information, load kernel modules, and more.
- Real-Time Event Monitoring: Provides timely insights for real-time file system changes, process executions, network connections, and other system activities.
- Centralized Logging and Reporting: Correlates data and event logs by sending query results.
- Scheduled Queries: Schedule specific queries to have regular compliance checks and continuous monitoring.
Why do we recommend it?
Osquery employs basic SQL commands to gather device data. This approach has significant potential for enhancing security. By running simple SQL queries, you can uncover anomalies like processes running without an original binary on disk, as demonstrated in the example provided. Osquery’s flexibility and customization make it a powerful tool for tailored intrusion detection.
While this may seem like a relatively trivial functionality at first, simply viewing the sample “Security” code that can be run from the osquery console help reveal the potential here:
osquery> SELECT name, path, pid FROM processes WHERE on_disk = 0; name = Drop_Agent path = /Users/jim/bin/dropage pid = 561
The above sample from Osquery’s home page demonstrates how you could use the tool to find a process that is running without an original binary on disk. This functionality can be extended and customized to meet your specific requirements for intrusion detection monitoring making Osquery a novel approach that could have significant security benefits.
To install osquery on Windows using Chocolatey, use the command “choco install osquery”.

Who is it recommended for?
Osquery is recommended for organizations and security professionals seeking a novel approach to intrusion detection and monitoring. Its compatibility with various operating systems, including Windows, macOS, and different Linux distributions, makes it a versatile choice. This tool can be particularly valuable for those looking to enhance their security measures by identifying unusual activities and potential threats with the help of SQL-based queries.
Pros:
- Fast and Tested: Experts test for memory leaks and thread safety on a regular basis.
- Can be Run Anywhere: Due to its cross-compatibility feature, you can run it on multiple operating systems, including macOS, Linux, and Windows.
- Open-Source: This tool is open-source so you can use its advanced features for free of cost.
- Good Community Support: Any user can get started with this tool due to its excellent community support.
Cons:
- Lack of Accountability: Few users don’t understand how their data is collected and used as it is open-source.
Operating systems supported:
- Windows
- macOS
- Centos
- FreeBSD
- Many other Linux operating systems
Summary
IPS and IDS are an important part of network security.
However, don’t expect these strategies to offer complete security solutions. Hackers have other methods to intrude into your network without having to break encryption or steal passwords. Social manipulation of employees is another growing entry point for data thieves and those intent on causing disruption. It is important to educate staff in controlling the information that they give out about themselves. You also need to introduce interactive identity authentication methods to prevent staff from being duped by an email or phone call from a hacker masquerading as an executive.
Other measures needed to protect your company’s assets include document access controls that prevent confidential information held in digital format from being printed, emailed out, or altered. Don’t overlook the shielding of wifi signals to prevent the wireless signal from being accessible from outside your premises and be careful to enforce encryption on all external communications. Implement device management policies if you integrate mobile devices into your network — both company-provided and employee-owned.
As attackers become more creative, we need to adopt more robust security tools and practices and IPS and IDS can play an important role in that, particularly in enterprises. There are a variety of solutions available, and what is best for you will vary significantly depending on the specific requirements of your use case. Do you have experience with any of the tools described above or is there a particular solution you think we left out? Let us know in the comment section below.