Microsoft’s Windows Server Update Service (WSUS) can be clunky and lack many of the features sysadmins need to manage their networks effectively. Most of the tools we review below offer features that go well beyond basic patch management.
Here is our list of the best WSUS Alternatives for Patch Management:
- NinjaOne Patch Management EDITOR’S CHOICE This tool is part of a cloud-based remote monitoring and management platform and it will keep operating systems and applications up to date.
- ManageEngine Patch Connect Plus (FREE TRIAL) An SCCM-based patch manager that is able to channel updates for non-Microsoft software through to WSUS.
- N-able N-sight (FREE TRIAL) Cloud-based remote monitoring and management software that includes patch management for Windows systems and Microsoft software.
- Atera (FREE TRIAL) This SaaS platform of tools for MSPs includes a patch manager for Windows and macOS that can also install and update software packages.
- Kaseya VSA Patching deployment with integrated remote management. Good for environments that need both patching and remote management.
- WSUS Offline Tool Free patching tool built with offline in mind. Great for keeping legacy systems updated without connecting it to the internet.
- Ivanti PatchLink WSUS alternative patch manager that adds detailed search and filtering options to your deployments.
- PDQ Deploy Patch management solution for both WSUS and third-party apps.
- BatchPatch A simple tool for patch manager with key functionality but lacks some of the more detailed reporting and enterprise features.
The best WSUS Alternatives
Let’s take a look at eight of the best WSUS alternative tools.
1. NinjaOne Patch Management (FREE TRIAL)
NinjaOne Patch Management is a service that can perform patching for endpoints no matter where they are located. This service is part of a cloud-based system that is aimed at the IT operations departments of multi-site businesses and managed service providers. Its cloud location means it is not bound to one specific network and you can enroll any device into your account, including individual computers used by home-based employees.
Why do we recommend it?
NinjaOne Patch Management earns our recommendation as a versatile cloud-based solution designed for IT operations in multi-site businesses and managed service providers. Our testing reveals its ability to perform endpoint patching irrespective of location, making it ideal for businesses with diverse setups, including remote employees. The high degree of automation in patch management, covering both operating systems and over 100 third-party applications, streamlines the update process. The system’s unattended operation during off-hours ensures efficiency without requiring manual intervention. The user-friendly console and comprehensive activity reporting contribute to a seamless experience, allowing technicians to review patch application statuses the following day.
The patching system offers a high degree of automation, which means that you don’t have to look up whether patches have become available for the operating systems that your endpoint fleet runs. The system will also monitor the versions of more than 100 third-party applications and keep them patched.
As it is an automated system, the patch manager will run unattended during unsociable hours. The designers of this package made sure to include an easy-to-use console and activity reporting, so technicians can see the next morning whether each patch was applied successfully. The information given in the completion status report for each patch lets the support team decide whether to run the patch again, investigate further, or hold off the patch.
The patch status reports get stored and the NinjaOne package includes cloud storage space for these and other system logs. The entire NinjaOne platform offers a suite of remote monitoring and management tools, which includes a backup manager, automated IT asset inventories, and a service desk ticketing system.
Who is it recommended for?
NinjaOne Patch Management is highly recommended for IT operations in multi-site businesses and managed service providers. Our hands-on experience highlights its cloud-based flexibility, enabling endpoint patching for devices across various locations, including those used by home-based employees. The system’s automation, covering both operating systems and third-party applications, caters to businesses seeking a streamlined patch management process. The unattended operation during off-hours and detailed completion status reports make it user-friendly and efficient for technicians.
You can get to know the NinjaOne platform with its patch management service by accessing a demo of the system and learning more about pricing. Investigate further with a 14-day free trial.
EDITOR'S CHOICE
NinjaOne Patch Management, a part of the NinjaOne RMM, is a comprehensive platform for patching all kinds of devices across multiple sites. It handles the entire patching process, from identifying missing patches to testing and deployment, thereby reducing the burden for IT administrators while plugging in the vulnerabilities that come from unpatched applications. Its ease of use, a high degree of automation, and an intuitive interface that provides complete control and visibility are some key reasons for NinjaOne to be the editor’s choice for the best WSUS alternative.
Download: Get a 14-day FREE trial
Official Site: https://www.ninjaone.com/patch-management/
OS: Cloud based
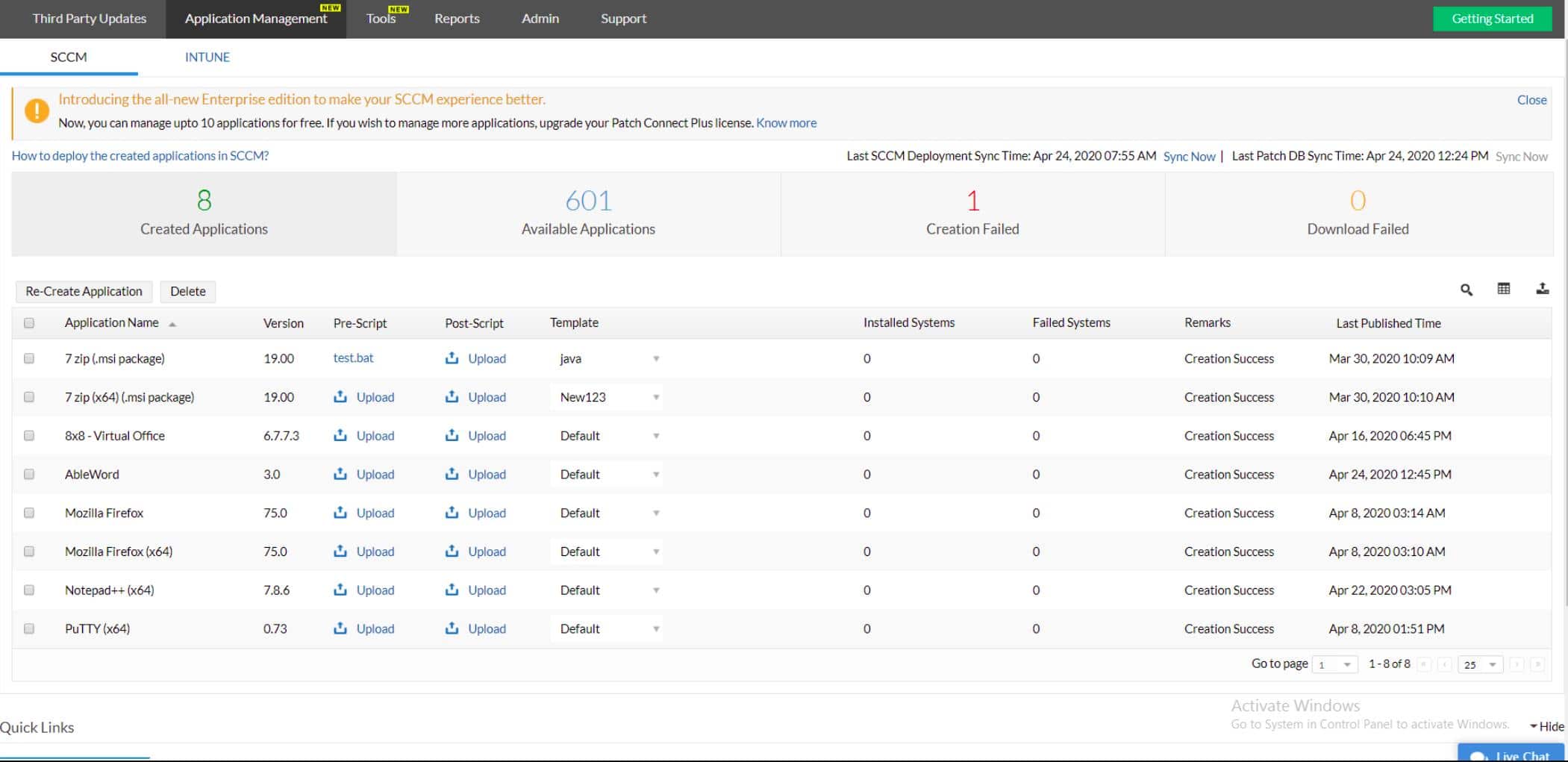
2. ManageEngine Patch Connect Plus (FREE TRIAL)
ManageEngine Patch Connect Plus offers a solution for those who don’t want to use several different tools to manage software on Windows Server. Although WSUS has its faults, it is the official tool for updating Windows Server systems, so it is best practice to use it. That leaves out all of your third-party software.
Why do we recommend it?
Our recommendation for ManageEngine Patch Connect Plus is rooted in its efficient consolidation of software management tools for Windows Server, eliminating the need for multiple applications. Through our hands-on testing, we’ve observed its seamless integration as a plugin to SCCM, addressing the gap left by WSUS for third-party software updates. The plugin not only logs all software in the Windows Server environment but also regularly checks suppliers for updates, streamlining the patching process. The use of Deployment Templates empowers system administrators to control update executions, offering flexibility in deployment timing and strategies. With additional tools like a patch tester and update assessment services, ManageEngine Patch Connect Plus enhances SCCM’s capabilities, providing a comprehensive solution for software management.
Patch Connect Plus operates as a plugin to SCCM that enables updates to be sent through the WSUS system, thus enabling all patches and updates to be run through a unified system. The service checks the Windows Server environment and logs all software. It is then able to regularly check on the suppliers of those packages for any updates, listing them for installation.
The execution of updates is dictated by the setup of Patch Connect Plus, which is driven by Deployment Templates. According to whichever template you select, updates will be run through SCCM or set aside. They will be rolled out immediately, on the next occurrence of an authorized time window, or when the system administrator commands it.
The plugin adds-on a whole section of tools to SCCM. These include a patch tester and other update assessment services. It is possible to pause an update for further analysis without having to hold up everything that is set to run. Once runs have completed, Patch Connect Plus reports on completion statuses and offers the option to re-launch failed patches.
ManageEngine Patch Connect Plus is on-premises software for installation on Windows Server. The system is offered in three editions: Standard, Professional, and Enterprise. Standard is free to use but it just loads a list of third-party software updates into SCCM.
Who is it recommended for?
ManageEngine Patch Connect Plus is ideal for organizations seeking an integrated solution for Windows Server software management. Our testing indicates that it’s particularly beneficial for users relying on SCCM and looking to extend WSUS functionality to third-party patches. System administrators who prioritize a centralized approach to updates will appreciate the software’s versatility in scheduling and deployment. The three editions—Standard, Professional, and Enterprise—cater to varying needs, with the Enterprise edition offering advanced tools like an Applications Management system. From small businesses to enterprises, ManageEngine Patch Connect Plus is a valuable addition to SCCM, providing an efficient and scalable solution for comprehensive software management.
The Professional edition integrates into SCCM, offering the option to implement third-party patch rollouts with WSUS. This version includes system scans that create and update a software inventory. The Enterprise edition has more tools, such as an Applications Management system. You can try the Professional and Enterprise editions on a 30-day free trial. The trial version will only monitor up to 10 apps.
3. N-able N-sight (FREE TRIAL)
N-able N-sight is a remote monitoring and management tool that enables IT departments to conduct systems management functions centrally for several remote sites. The software service includes a comprehensive patch management function for Windows systems.
Why do we recommend it?
N-able N-sight’s Patch Manager stands out by not only identifying devices and logging operating systems but also conducting a thorough inventory of installed services and software on each server and endpoint. The tool’s ability to update not just operating systems but also critical software such as Adobe tools, Java, and web browsers showcases its versatility. The inclusion of LOGICcard, an intelligence feed drawing from a vast endpoint network, adds an extra layer of security, providing insights into both threats and potential unintended consequences of patches. Through our evaluation, N-able N-sight proves to be an efficient and all-encompassing solution for IT departments managing multiple remote sites.
The Patch Manager of N-able N-sight seeks out all devices and logs their operating systems. It also takes an inventory of all of the services and software installed on each server and endpoint. The patch manager will update Windows implementations with any patches that arise. The responsibilities of the system don’t end with patches for operating systems; it also updates essential software.
The software and services that the Patch Manager can update include services such as Adobe tools Java, and web browsers. Although the system monitoring service in SolarWinds is able to monitor devices running Linux, the Patch Manager isn’t able to update the software on them.
One of the features of the N-able N-sight is an intelligence feed that not only informs on threats, it also warns against unintentional damage that some patches and updates cause. This service is called LOGICcard and it is an information system that gathers the experiences of more than 5,000,000 endpoints around the world.
The Patch Manager can be limited to a specific time window in any day or week that allows patches to be rolled out. Patches queued can be suspended or removed before they applied, which enables systems administrators to act on the information gleaned from the LOGICcard feed.
The Patch Manager produces status reports on all patch installation attempts and leaves a record in the dashboard of success or failure of each run so a manager can review events after the fact. Patches that weren’t applied can be rerun or applied manually.
Who is it recommended for?
Our hands-on exploration underscores its suitability for organizations relying on Windows systems, with a seamless and comprehensive patch management function. System administrators and IT professionals seeking a cloud-based solution will find N-able N-sight appealing, especially given its subscription-based model without setup costs. The Patch Manager’s flexibility, allowing for specific time windows for patch rollouts and the ability to suspend or remove queued patches based on LOGICcard insights, makes it a valuable asset for proactive systems administration. With status reports and a dashboard record of patch installation attempts, N-able N-sight ensures transparency and accountability in the patch management process.
The N-able N-sight system is a cloud-based system and includes all supporting services. There is no setup cost involved in taking up this service, which is charged for by subscription. The N-able N-sight is available for a 30-day free trial.
4. Atera (FREE TRIAL)
Atera is a SaaS platform that offers the software that a managed service provider (MSP) needs in order to support the systems of their clients. Accounts with this service are multi-tenanted to keep the data of different MSP clients separate and the software includes a remote monitoring and management (RMM) package. Within the RMM tools of Atera is a patch manager for Windows and macOS.
Why do we recommend it?
Atera stands out as an essential SaaS platform for Managed Service Providers (MSPs). Through our thorough testing, we found its Remote Monitoring and Management (RMM) tools, particularly the patch manager for Windows and macOS, to be robust and efficient. Automation is a key highlight, allowing the patch manager to operate seamlessly during designated maintenance windows without manual intervention. This ensures timely updates and eliminates the need for technicians during unconventional hours. Atera’s versatility extends beyond patch management, offering automated tasks, software package updates, and customizable script execution, making it an indispensable tool for MSPs looking to streamline system support.
The Atera patch manager can be set up to run periodically at a suitable maintenance window. This is most likely to be out of office hours. However, there is no need to go to the expense of paying a technician to work unsociable hours in order to watch the patch rollout because the system will launch automatically on a time trigger and report completion statuses for manual verification the next morning.
The patch manager can also be used to install or update software packages and there are a number of automated tasks that the interface offers, such as the clearing out of temporary files. You can set up the patch manager to run a customized script. Therefore, this system can be used to launch just about any process on a schedule.
Other features in the Atera platform include a ticketing system and a remote access package for manual technician access to supported endpoints. The full platform offers professional services automation (PSA) functions that help MSP managers run the business.
Who is it recommended for?
Atera is highly recommended for Managed Service Providers seeking a comprehensive SaaS platform. Our hands-on experience highlights its multi-tenanted accounts, ensuring data separation for different MSP clients. The platform’s patch manager operates during off-hours, automating tasks and providing reports for manual verification. With additional features like a ticketing system, remote access package, and Professional Services Automation (PSA) functions, Atera caters to the practical needs of MSP managers, offering a holistic solution for system support and business management.
Pricing starts at $129 per technician. The Atera platform can be accessed on a 30-day free trial.
5. Kaseya VSA

Kaseya VSA is a full-fledged remote monitoring and network management tool that gives you a wide variety of features and control. One of those features is a powerful patch management component that adds additional utilities to the WSUS system.
Why do we recommend it?
Kaseya VSA stands out as a robust remote monitoring and network management tool, encompassing a wide array of features. Notably, its powerful patch management component enhances WSUS capabilities, allowing seamless automation and troubleshooting of Windows and software patches. The user-friendly dashboard offers an intuitive interface for creating custom patching schedules, blackout times, and blacklisting specific updates prone to causing issues. Critical conditions for agents are intelligently highlighted, aiding in prioritizing deployments based on security patch importance. Whether devices are online or offline, Kaseya VSA ensures efficient patch management through .CAB file deployments, making it a comprehensive solution for diverse IT environments.
Through the patch management console, you can automate and troubleshoot your Windows and software patches from a single dashboard. The interface provides an easy to read screen and highlights exactly which agents are in critical condition. Not all patches are created equally, Kaseya VSA knows this and brings important security patches to your attention so you can properly prioritize your deployments.
In a few clicks, you can easily create different patching schedules for your devices and even block out specific times when patches won’t run. The dashboard also allows you to blacklist specific updates that may cause issues with your applications. Microsoft is known for pushing out a bad update from time to time, so having that ability to blacklist certain patches can save you a lot of trouble down the road.
Patch management through Kaseya VSA works both while devices are on and off the network. When a device isn’t connected to the network, it can push out critical updates through .CAB files. One of the few downsides of using this tool is the lack of reporting and patch testing. If reporting and compliance are a major part of your business you might want to look towards a more holistic solution.
Who is it recommended for?
Kaseya VSA is recommended for those seeking a versatile remote monitoring and network management tool with robust patch management capabilities. Our testing underscores its adaptability for different patching schedules, user-friendly interface, and the ability to manage updates online or offline. While it excels in many areas, businesses heavily reliant on comprehensive reporting and compliance features may need to explore more specialized solutions. For organizations prioritizing holistic solutions and efficient patch management, Kaseya VSA offers a powerful and user-friendly platform.
You can try a 14-day free demo of Kaseya VSA to see if it’s right for your patch management needs.
6. WSUS Offline Update
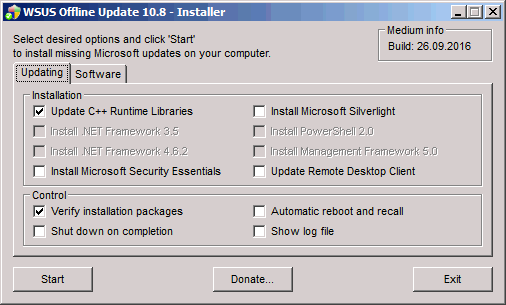
If your network supports older versions of Windows and other legacy products, WSUS Offline Update tool is a great application to manage patches for them. WSUS Offline Update helps you fill the gaps in your patching without having to connect to the internet or download every single missing patch from Microsoft.
Why do we recommend it?
WSUS Offline Update earns our recommendation as an invaluable tool for managing patches, especially for networks supporting older versions of Windows and legacy products. Ideal for maintaining archaic systems, this tool efficiently fills patching gaps without requiring an internet connection. Particularly beneficial for end-of-life servers, WSUS Offline Update allows the retrieval of critical security patches, bug fixes, and feature updates without exposing servers to the internet. Its flexibility extends beyond operating system patches, offering the ability to patch older versions of Microsoft Office with customizable inclusions or exclusions of various components. While its primary focus is on legacy products, WSUS Offline Update also provides patching capabilities for modern servers and operating systems, making it a versatile and free addition for sysadmins supporting diverse environments.
If you’re someone who needs to keep archaic systems up and running, this tool will prove useful in getting out critical security patches, bug fixes, and even feature updates to your legacy end of life servers. If your server is strictly only accessible from the LAN WSUS Offline Tool gives you the option to limit your older servers exposure to the internet while still getting critical patches to it.
In addition to operating system patches, you can even patch older versions of Microsoft Office and choose exactly what you want to be included. You’ll have the option to include or exclude runtime libraries, service packs, Microsoft Security Essentials updates, language packs, and Windows Defender definitions.
Who is it recommended for?
WSUS Offline Update is highly recommended for sysadmins tasked with supporting networks that include older versions of Windows and legacy products. Our testing highlights its efficiency in filling patching gaps without an internet connection, making it particularly useful for servers strictly accessible from the LAN. The tool’s flexibility extends to modern servers and operating systems, providing a powerful and free patching solution for sysadmins working in diverse environments. Whether dealing with end-of-life servers or modern systems, WSUS Offline Update stands out as a versatile and essential tool for effective patch management.
While WSUS Offline Tool is certainly focused on legacy products, it has the ability to provide patching for modern servers and operating systems as well. WSUS Offline Tool is completely free and is a powerful add-on for any sysadmin who has to support older environments.
7. Ivanti PatchLink

PatchLink is a WSUS patching tool designed for larger networks and provides a vast array of features and options to help you manage your patching on an enterprise level. PatchLink puts security and uptime and the forefront by pre-testing all patches that come through the software.
Why do we recommend it?
Ivanti PatchLink stands out as a robust WSUS patching tool tailored for larger networks, offering a comprehensive set of features for enterprise-level patch management. Notably, PatchLink prioritizes security and uptime by pre-testing all patches before deployment, ensuring a proactive approach to system stability. Its intuitive search functions and filtering capabilities on the patching dashboard are particularly impressive, allowing users to efficiently search for installed and available patches based on various criteria. This feature becomes especially valuable in larger environments with numerous endpoints. PatchLink’s integration with Microsoft’s System Center Configuration Manager (SCCM) further enhances its capabilities, providing reporting, OS deployment, software distribution, and third-party application patching.
One of my personal favorite features of PatchLink is it’s intuitive search functions and filtering. From the patching dashboard, you can search both installed and available patches based on vendor, security level, type of product, and KB number. This feature really shines in larger environments with more endpoints.
PatchLink can tap directly into Microsoft’s System Center Configuration Manager (SCCM) to provide reporting, OS deployment, software distribution, and patching for third-party applications.
Who is it recommended for?
Ivanti PatchLink is highly recommended for organizations with larger networks seeking an enterprise-level WSUS patching solution. Our testing highlights its emphasis on security and uptime, making it suitable for environments where these factors are critical. The intuitive search and filtering functions cater to the needs of larger environments with numerous endpoints, providing efficient patch management. Additionally, its seamless integration with Microsoft’s SCCM enhances its versatility, offering a comprehensive solution for reporting, OS deployment, software distribution, and third-party application patching. PatchLink is a strong choice for organizations prioritizing proactive and efficient patch management at an enterprise scale.
You can test out PatchLink for yourself by requesting a free trial on Ivanti’s website.
8. PDQ Deploy

PDQ Deploy is a lightweight but powerful program that can handle all aspects of both WSUS and third-party application patch management. There is a lot of versatility under the hood outside of just patch management as well. You can execute and run custom scripts, send commands, and fully install and uninstall programs from the dashboard.
Why do we recommend it?
Beyond patching, PDQ Deploy offers versatility, allowing users to execute custom scripts, send commands, and fully install or uninstall programs directly from the dashboard. Its patch management section stands out with scheduling features that can be configured for diverse environments, offering flexibility even in non-traditional setups. Notably, PDQ Deploy addresses the challenge of keeping laptops up to date by waiting for offline agents to come online and automatically queuing missing patches for deployment. With over 250 applications labeled as “ready to deploy,” PDQ Deploy ensures a streamlined process with the latest tested versions available, making it an efficient and time-saving solution.
Inside the patch management section, you’ll have access to scheduling features that can be configured in a number of different ways to suit even the most non-traditional environments.
If you struggle with keeping laptops up to date because they go missing for months at a time, you’ll be happy to know that PDQ Deploy will wait for that agent to come online and queue its missing patches for deployment. This itself is a huge time saver, and you won’t have to worry about an old vulnerable laptop coming online and jeopardizing your network’s security.
If you have a large number of applications to patch in addition to Windows updates, PDQ Deploy has over 250 applications that they label as “ready to deploy.” This means their servers have the latest tested versions and are ready to go.
Who is it recommended for?
PDQ Deploy is highly recommended for users seeking a versatile and efficient solution for both WSUS and third-party application patch management. Our testing highlights its lightweight yet powerful capabilities, including the execution of custom scripts and program installations/uninstallations directly from the dashboard. Its scheduling features cater to diverse environments, making it suitable for both traditional and non-traditional setups. The ability to wait for offline laptops to come online and automatically queue missing patches adds a layer of security for organizations dealing with sporadically connected devices.
Lastly, you can configure PDQ Deploy to send you or your team email notifications when a patch deployment or script execution is successful. PDQ Deploy is completely free with limited access to some features. Full access pricing starts at $500.00 (£394.16) a year per admin.
9. BatchPatch

BatchPatch is a very simple and easy to use bulk patching program that extends the usefulness of WSUS. Much like most of the WSUS alternatives in this list BatchPatch provides more visibility and control over the entire patching process through features like patch scheduling, offline mode, remote script execution, and custom reboot options.
Why do we recommend it?
BatchPatch earns our recommendation as a straightforward and user-friendly bulk patching program that enhances the functionality of WSUS. In line with other alternatives, BatchPatch provides increased visibility and control over the patching process, offering features like patch scheduling, offline mode, remote script execution, and customizable reboot options. A notable feature is the live ping functionality, allowing users to monitor when a PC comes back online after reboots or updates, particularly useful for remote environments with devices that haven’t been patched for an extended period. While BatchPatch lacks detailed and visual reporting features, it compensates with simplicity and ease of use.
When a PC reboots or is undergoing updates BatchPatch has a live ping feature that you can set up to see exactly when a PC comes back online, which is specifically useful for machines that haven’t been patched in a long time in a remote environment.
If you’re a stickler for detailed and visual reporting BatchPatch might not be for you. The software does have a reporting feature but appears to be limited to HTML and text exports. Their site also has a number of tutorials which I personally found helpful. These are blog-style format tutorials that go over some of the most common uses and functions you’d want to implement with the program.
Who is it recommended for?
BatchPatch is recommended for users seeking a simple and user-friendly bulk patching solution that extends the capabilities of WSUS. Our testing highlights its straightforward features, including patch scheduling, offline mode, and remote script execution. The live ping feature makes it particularly useful for monitoring the status of devices in remote environments, especially those that have been offline for an extended period. While not suitable for users requiring detailed and visual reporting, BatchPatch compensates with ease of use. The availability of tutorials on their site is an added benefit, providing helpful insights for users looking to maximize the program’s functionality.
You can download a fully functional evaluation version for free. In order to have more than four target machines, you’ll need to purchase BatchPatch. Pricing starts at $399.00 (£314.17) per user.
Which WSUS Alternative Is For You?
It’s pretty clear that WSUS native functionality isn’t enough for most sysadmins these days. To get the most for your money you’ll want to choose a tool that suits your needs, and is appropriate for the number of agents you’re looking to patch and manage.
Feel free to test out any of the trials to see what’s right for your network. How do you feel about WSUS tools? Do you think alternative tools are needed to patch networks effectively? Let us know in the comments below.