
Networking has brought many wonderful opportunities to modern enterprises but it has also opened the door to a world of security threats. Setting up an enterprise network produces a ton of different vulnerabilities that need to be managed. Network vulnerability scanners are key tools for finding security issues before outside attackers do.
Everyone from SMEs to multinational corporations are using network vulnerability scanners to discover threats within their commercial networks. Given the sophisticated nature of modern cyber attacks, network vulnerability scanners have become an essential tool for staying online and fighting off cyber crime.
We cover a lot of detail on each of the tools that made this post below, but in case you are short of time, here is our list of the best network vulnerability scanners:
- ManageEngine Vulnerability Manager Plus EDITOR’S CHOICE is a comprehensive vulnerability discovery and remediation tool designed for medium to large-sized organizations. Start a 30-day free trial.
- Site24x7 Network Vulnerability Scanner (FREE TRIAL) A cloud-native tool that checks firmware across 75+ vendors for known CVEs and maps severity using NIST data. Start a 30-day free trial.
- CrowdStrike Falcon Spotlight This cloud-based service continuously checks on a system’s endpoints for outdated software and loose settings.
- Paessler PRTG Network Monitor Implements network monitoring to spot unusual performance that could indicate malicious activity. Runs on Windows Server.
- SolarWinds Network Configuration Manager This on-premises system keeps networks devices hardened against attack by standardizing their settings and blocking unauthorized changes. Runs on Windows Server.
- Intruder A Web-based scanner that is good for use by IT Operations technicians with support for external cloud services.
- OpenVAS A highly-respected free system vulnerability scanner that was forked from Nessus. Runs on Linux or on Windows over a hypervisor.
- ImmuniWeb An AI-based SaaS vulnerability system with a range of plans that includes a free Community Edition.
- Nessus Professional The paid version of the widely-used Nessus system that grades discovered weaknesses by a severity rating. Operates through a Web site.
- Qualys A platform of security tools that includes vulnerability scanning, patch management, and file integrity monitoring. Delivered from the cloud.
- Rapid7 Insight VM This is a cloud-based service that offers delivery options that include AWS and Axure integration and an API that lets you integrate the scanner into other monitoring systems.
What does a Network Vulnerability Scanner do?
A network vulnerability scanner is designed to scan your network, hardware, and software in search of vulnerabilities. The scanner evaluates the network for vulnerabilities and flags issues for the administrator to address. Once an issue has been flagged, a notification is sent to the user with further detail so that the user can start troubleshooting to eliminate the issue. Regular vulnerability scanning minimizes points of entry for potential attackers and keeps your service safe from disruption.
Why is Vulnerability Scanning Important?
Whenever an organization connects to the internet they are putting themselves at risk of being compromised. Vulnerability scanning tools allow you to use one centralized tool to manage these vulnerabilities and protect a network from external threats. In effect, vulnerability scanning tools automate the management of a network’s security so that the network administrator has less manual tasks to do.
Once vulnerabilities are discovered, a vulnerability scanner can send an alert to the administrator to start troubleshooting. This is a more efficient method of managing security issues than having an administrator comb through every individual system looking for faults.
Vulnerabilities come in many different shapes and sizes. There are so many different vulnerabilities that it is impossible for a network administrator to keep track of them manually (particularly in a large network). Using a network monitoring tool automates the discovery of vulnerabilities that you might have missed or overlooked. In this article we’re going to look at the best network vulnerability scanners for enterprises.
The best network vulnerability scanners
1. ManageEngine Vulnerability Manager Plus (FREE TRIAL)
ManageEngine Vulnerability Manager Plus is a platform that combines asset management, vulnerability discovery, and vulnerability remediation into a single solution. It scans the network to identify different assets, probes them for vulnerabilities, and searches for network vulnerabilities using similar scanning methods.
Key features:
- Takes a holistic approach to network security and vulnerability remediation
- Prioritizes vulnerabilities for remediation
- Provides steps to address vulnerabilities
Each vulnerability is then classified based on severity, enabling teams to prioritize patching accordingly. In addition, the platform provides remediation steps for each vulnerability to help reduce exposure time. VMP is a valuable tool for both small internal teams and outsourced network security to stay ahead of threats and prioritize the most impactful vulnerabilities for the business.
Pros:
- Ideal for the ongoing scanning and patching of devices
- Comprehensive reporting can help show improvements after correction
- Compatible with Windows, Linux, and Mac
- Threat intelligence is constantly updated to include the latest threats and vulnerabilities
- Offers a free version for small businesses
Cons:
- May require some time to explore all features of ManageEngine Vulnerability Manager Plus fully
You can download a 30-day free trial of the ManageEngine Vulnerability Manager Plus.
EDITOR'S CHOICE
ManageEngine Vulnerability Manager Plus is our editor’s top pick for the best network vulnerability scanner because of its end-to-end vulnerability management. It scans your remote and local surface areas to identify potential vulnerabilities in operating systems, configurations, third-party software, web servers, and more. Along with alerts, it provides contextual information that makes it easy to prioritize and fix vulnerabilities before they impact operations. Additionally, it mitigates the exploitation of security loopholes to prevent further problems from the same vulnerabilities. With such a comprehensive approach, it can be a great value addition to any organization.
Download: Start a 30-day FREE Trial
Official Site: https://www.manageengine.com/vulnerability-management/
OS: Windows, Linux, Mac
2. Site24x7 Network Vulnerability Scanner (FREE TRIAL)
Site24x7’s Network Configuration Manager offers a built-in ‘firmware’ vulnerability scanner. It is designed to detect firmware-level threats in network devices. This tool also checks device firmware against the NIST CVE database and highlights vulnerabilities by severity. This is perfect for helping IT teams prioritize critical fixes.
Key features:
- Scans firmware on routers, switches, and firewalls using real-time CVE data
- Flags vulnerabilities with severity ratings and links to vendor advisories
- Supports 75+ vendors including Cisco, Fortinet, Juniper, and Palo Alto
Pros:
- Quick setup with minimal configuration needed
- Accurate detection with regularly updated threat intelligence
- Clean dashboard makes it easy to review and prioritize issues
- Helps teams stay compliant by identifying unpatched firmware
Cons:
- Learning curve for advanced configuration and reporting features
- Site24x7 offers a 30-day free trial with access to its full vulnerability scanning tools, no credit card required.
3. CrowdStrike Falcon Spotlight
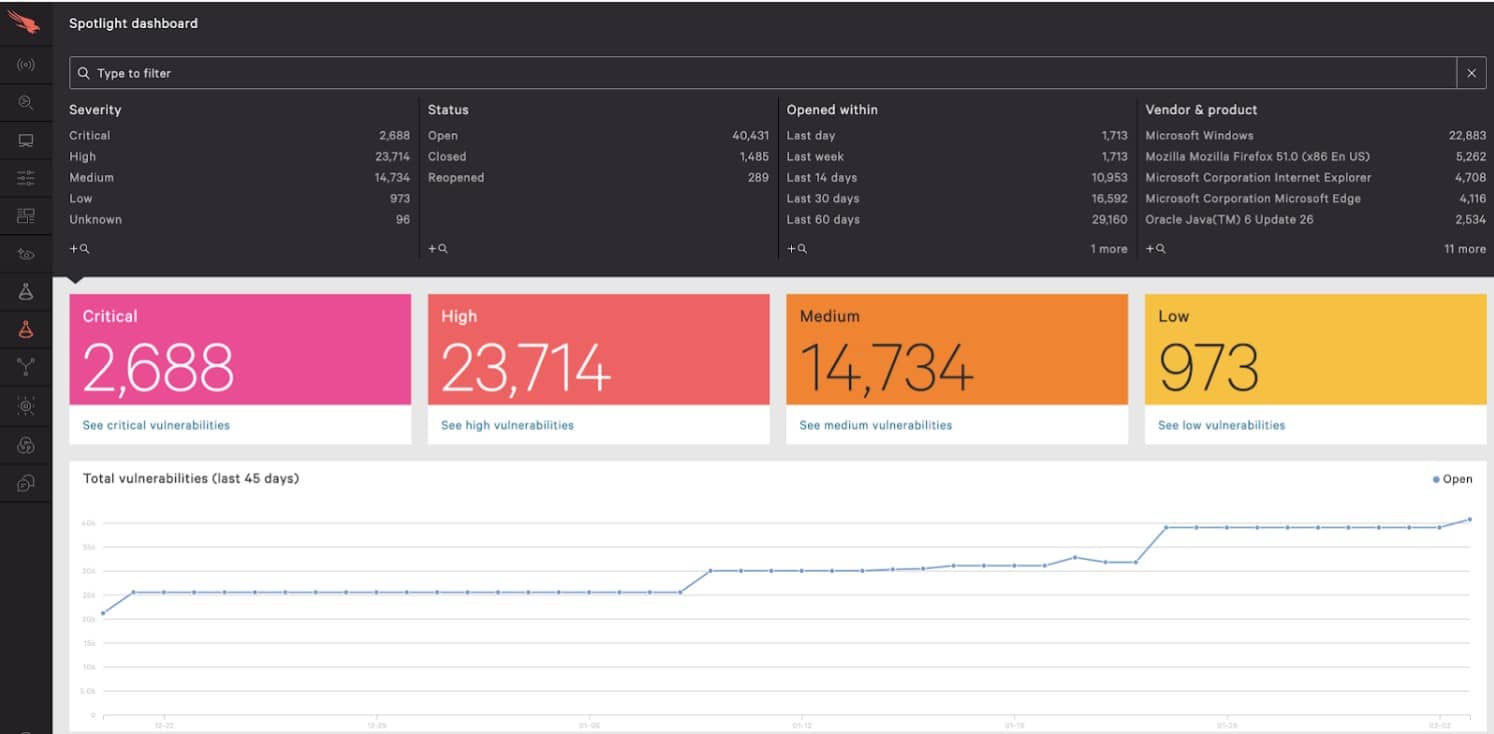
CrowdStrike Falcon Spotlight is delivered from a cloud platform that includes a range of cybersecurity tools. This system implements “scanless” vulnerability management. What that term means is that the Spotlight system is designed more like a system monitor for endpoints, networks, and software, rather than an external system that works through a crawl-like checking routine.
The CrowdStrike Falcon strategy is very focused on data from endpoints, so it is a bit of a squeeze to get this tool into a list of network vulnerability scanners. However, think of this tool as a vulnerability scanner than gets into your network rather than an external attack surface scanner.
Endpoint agents need to be running on each device on the network and this generates a software inventory, which is the main medium of the Spotlight system. This listing is constantly updated and the Spotlight platform is able to check on the current availability of patches for each package. The tool does not include a patch manager.
The Falcon Spotlight system uses an AI process that refers to the CrowdStrike threat intelligence database. The system spots known vulnerabilities and then ranks them for attention in the service’s dashboard If you subscribe to other services on the Falcon platform, such as its Falcon Insight endpoint detection and response service, all services share the same data feed from endpoint agents. You can access a 15-day free trial.
4. Paessler PRTG Network Monitor

Next on this list we have Paessler’s PRTG Network Monitor, a network monitoring platform that also offers a complete vulnerability monitoring experience. PRTG Network Monitor is capable of monitoring everything from entire networks to endpoints, ports, and servers.
To keep track of your network’s status, PRTG uses a combination of SNMP, NetFlow, and packet sniffing to make sure your network is secure. Network monitoring activities are managed through one central dashboard. Through it you can check up on the status of your entire network. You have over 200 sensors at your disposal to monitor for new vulnerabilities.
In the off chance that you miss something important, PRTG Network Monitor has you covered with alerts. Whenever a sensor takes a reading that exceeds a certain threshold you are sent a notification to take action. Notifications can be sent to you via email, text message, or push notifications to ensure that you keep up with events as they unfold.
There are many different pricing options available for PRTG Network Monitor so we recommend that you check out the pricing section on their site to see which package is right for you. There is even a free version for smaller businesses that can monitor 100 sensors free of charge.
5. SolarWinds Network Configuration Manager

SolarWinds Network Configuration Manager is a configuration management solution that provides straightforward vulnerability scanning. With SolarWinds Network Configuration Manager you can look for security vulnerabilities across multi-vendor networks and scan your current network configurations for vulnerabilities. If you’re using Cisco devices then this tool is an excellent choice because it is integrated with the National Vulnerability Database in the US.
Vulnerability management takes place through one view. The user interface allows you to change configurations and identify when changes are taking place within your network. The visibility provided by this user interface makes it easy to take action once a new vulnerability crops up.
Network Insight is the main feature that helps you to manage vulnerabilities for Cisco ASA and Cisco Nexus. You can manage firmware upgrades, and search for and filter configuration changes. There is also the option to combine SolarWinds Network Configuration Manager with SolarWinds Network Performance Monitor to add wider network monitoring to the mix as well.
Overall SolarWinds Network Configuration Manager is highly recommended to companies who want to mix vulnerability scanning with configuration management. SolarWinds Network Configuration Manager starts from a price of £2,275 ($2,932), and you can download a 30-day free trial.
7. OpenVAS

Next up on this list we have OpenVAS. OpenVAS is an open source vulnerability assessment tool that was originally based on the Nessus network scanning tool. This vulnerability scanner is used by companies of all sizes and is regularly updated with Network Vulnerability Tests to keep it up-to-date (there are over 50,000 in total!).
Once you open up OpenVAS you can scan your network for security vulnerabilities. Once your network has been scanned, you will be shown a list of all the security issues that have been found by the scan. For instance, OpenVAS can identify anonymous FTP access, ProFTPD security issues, null sessions, and weak authentication.
For a free vulnerability scanner, OpenVAS offers a competitive experience that will suit the needs of most smaller organizations. OpenVAS is available as a virtual appliance on Windows virtual machines or source code on Linux distributions. If you’d like to download OpenVAS, you can do so for free.
6. Intruder

Intruder is another high-performance, cloud-based network vulnerability scanner. With this tool, you can scan for open ports and compromised services to look for anything that a potential attacker could exploit. What makes Intruder special is its support for external cloud services. You can connect to AWS, Google Cloud, or Microsoft Azure and synchronize external DNS hostnames with your network.
As one of the top network vulnerability scanners, Intruder also offers notifications and reports. Whenever Intruder has finished a scan you are sent an email or slack notification that tells you its findings. Notifications have a threat level ranking system that marks alerts as Low, Medium, High, or Critical. This is useful because you can tell immediately if a substantial problem has emerged.
Intruder can detect over 10,000 different security vulnerabilities and can prevent high profile threats like WannaCry from taking you offline. The wide-ranging diagnostic potential of Intruder makes it an ideal choice for medium- to large-sized organizations.
There are a number of different pricing options available for Intruder starting from $101 per month for the Essentials version, which supports two user accounts and runs monthly assessments. The Pro version starts from $163 per month which runs scheduled and on-demand scans with support for an unlimited number of user accounts. The Vanguard version adds hybrid penetration to the mix and you can get a tailored price when you contact their sales team. You can download the free trial of Intruder.
8. ImmuniWeb

ImmuniWeb is one of the most advanced web-based vulnerability scanners on the market. ImmuniWeb uses Artificial Intelligence (AI) to scan for gaps in network security with zero false-positives SLA. This tool’s use of AI makes it one of the most accurate and sophisticated vulnerability scanners on this list. ImmuniWeb has a proven track record of identifying security risks like injection, broken authentication, broken access control, and misconfiguration.
It is also worth noting that ImmuniWeb AI offers notifications to ensure you don’t fall behind on security threats. You can receive instant vulnerability alerts via email, SMS, and phone. These alerts ensure that no security concern is overlooked and keep your network monitoring responsive to evolving new threats.
If you’re looking to reduce false positives and automate the bulk of your vulnerability assessment activities, ImmuniWeb is the tool for you. ImmuniWeb AI is available in a number of different packages. For complete protection, the ImmuniWeb Continuous package offers 24/7 web application monitoring for £930 ($1,199) per month. Alternatively, there is ImmuniWeb Discovery which provides you with an Application Security Scorecard free of charge. You can request a demo of the ImmuniWeb AI platform.
9. Nessus Professional

Nessus Professional is perhaps the most popular vulnerability scanner available today. With .32 defects per 1 million scans this tool has one of the lowest false positive rates in the vulnerability assessment space. Nessus Professional is a tool that has been designed to combat the most cutting-edge cyber security threats that cyber criminals can muster.
From the moment you load the web-based Nessus Professional GUIthere are over 450 configuration templates available out-of-the-box. For instance, scan templates range from a Host Discovery to Mobile Device Scan and a Policy Compliance Auditing template. These templates enable you to hit the ground running from the moment you deploy Nessus Professional.
For monitoring, there is a Live Results Scan view which shows you the results of live scans. Live scans display color-coded vulnerabilities which are ranked as Info, Low, Medium, High, or Critical. Scans are automatically conducted whenever a plugin is updated to keep your network maintained.
Based on the quality of its all-round monitoring experience, Nessus Professional is a tool that should be considered by organizations of all sizes who are looking to stay secure. Nessus Pro can be purchased as a one-year or multi-year license. For a one-year license Nessus costs £2,238.60 ($2,884). For two years the price is £4,364.76 ($5,623), and £6,378.48 ($8,219) for three years. There is also a seven-day free trial.
10. Qualys

Qualys is one of Nessus’s closest competitors, and offers a top-tier vulnerability management experience. With Qualys you can monitor everything from services and databases to storage units. All of these elements are scanned with the results displayed to you on a custom dashboard which details any vulnerabilities that have been found.
With Qualys, threat responses are prioritized automatically. For instance, if a number of different vulnerabilities are discovered within your network then Qualys displays current vulnerabilities according to their severity on the dashboard. A Top 10 vulnerabilities tab lets you know those security issues that you should address first based on how much of a threat they are to your network.
However, if you prefer to take a more active approach to vulnerability management there is a searchable IT asset inventory for you to comb through. Whether these assets are on-premises or in the cloud you can monitor them effectively with Qualys. The types of searches you can run include how many nodes are manufactured by a particular vendor and which devices are running outdated operating systems.
File integrity monitoring is a particularly effective vulnerability detection feature. With file integrity monitoring Qualys monitors OS’s in real-time to monitor for changes as they occur. To view a quote for Qualys you’ll have to contact the sales team directly. There is also a 30-day free trial.
11. InsightVM

Finally, we have Rapid7’s InsightVM, one of the most future-minded vulnerability scanning products on the market. InsightVM has a flawless user interface with live dashboards that can be customized for every user. Like Qualys, InsightVM offers risk prioritization and highlights those vulnerabilities which could have the biggest impact on your network. Vulnerabilities are assigned a Real Risk Score from 1-1000 based upon the level of risk they have to your service.
InsightVM also has a RESTful API which allows you to shape your monitoring experience as you see fit. You can use the RESTful API to automate those day-to-day tasks like scans which take up unnecessary time and distract you from other important tasks you could be doing. The supporting documentation provided with InsightVM helps you to get the most out of the RESTful API.
Another area where InsightVM excels is in the realm of hybrid deployments. InsightVM can monitor on-premises, cloud, and virtual services to give you complete visibility over both your tangible and intangible assets. There is also direct integration with Amazon AWS, Microsoft Azure, and VMware so that you can identify threats no matter where they are located.
Insight VM comes recommended to organizations looking for a highly-customizable vulnerability assessment tool. The RESTful API will give you complete control over how you manage your system’s vulnerabilities. To find out the price of InsightVM you’ll have to contact Rapid7 directly. There is a free trial of InsightVM.
Best Network Vulnerability Scanners: SolarWinds Network Configuration Manager and ImmuniWeb
As the list above has shown, there are plenty of options when it comes to network vulnerability scanners. So many in fact that it can be difficult to choose. Based on the strengths of each individual tool we recommend SolarWinds Network Configuration Manager for managing device configurations and Nessus Professional for meticulously tracking potential vulnerabilities on your network.
While products like ImmuniWeb also offer an exceptional experience, Nessus Professional offers more comprehensive coverage for a competitive price point. Given that all of these products are a substantial investment it is advisable to make use of at least one free trial before making a purchase. After all, what is right for one business may not be right for you.
What if I Can’t Afford a Network Vulnerability Scanner
Network vulnerability scanners carry a hefty price tag and there are many organizations that are unable (or unwilling) to pay a premium to keep their network protected. If you’re part of an enterprise that is in this bracket there is another option available to you: deploy multiple vulnerability scanners.
Taking a hybrid approach and mixing a proprietary tool with an open-source vulnerability scanner can help to keep costs low while keeping you protected. You can use the proprietary vulnerability scanner to monitor key points in your network while the open-source platform monitors the wider network.
By combining two tools together you can make sure that costs are kept low while keeping your network secure from external threats. This approach is generally used in environments where budgetary constraints restrict supporting one of the premium tools on a network-wide basis.
The only issue with using multiple tools is that you have to manage two platforms instead of just one. So if you want to try and save money on your vulnerability assessment strategy you’ll need to weigh whether the reduction in price is worth the hassle of juggling two systems.



