
Cloud Security Posture Management (CSPM) tools are a robust set of utilities for securing your cloud data and identifying and resolving problems in various cloud infrastructures due to incorrect configuration. As more and more individuals migrate to the cloud, the need for effective security technologies has grown. This is where CSPM tools are put to use. Compliant risk detection, risk visualization, and risk assessment capabilities are all provided by these software applications. In this article we will take a look at the best Cloud Security Posture Management (CSPM) tools on the market.
In addition, they provide alert systems that keep cloud customers up to date on attacks and other security concerns they may be exposed to. With these tools, administrators can execute instance scanning for misconfigurations, maintain consistency across all cloud environments, monitor storage buckets, and conduct risk assessments.
There are now Cloud Security Posture Management (CSPM) tools available on the market for identifying compliance issues in the cloud architecture. CSPM products, their features, relevance, and considerations for purchasing IT security technologies for the enterprise will be discussed here. The top CSPM tools on the market have also been selected for your company’s benefit.
Here is our list of the best Cloud Security Posture Management (CSPM) tools:
- Aikido Cloud platform that delivers security scanning for DevOps teams with services that begin with software composition analysis and runs through to the CSPM service, which tests the platforms that will host the new applications.
- CrowdStrike Falcon Cloud Security CNAPP includes a CSPM module and Cloud Workload Protection together with container security and a Cloud Infrastructure Entitlement Management (CIEM) unit for access controls.
- Datadog Cloud Security Cloud-based system provides options for cloud security posture management and cloud workload protection.
- Cyscale This package provides a full cloud-native Application Protection Platform that delivers a CSPM and a CWPP together with container and Kubernetes security, IAM auditing, and compliance management.
- Check Point Cloud Security Posture Management Part of a platform of cloud security tools that automate protection for all types of cloud assets and enforces security best practices.
- Lacework CNAPP service that includes a CSPM, a CWPP, container and Kubernetes security, and a CIEM.
- Fugue Now part of the Synk Developer Cloud Security platform, this service provides ongoing protection and verification for live applications.
- F5 Distributed Cloud App Infrastructure Protection Extensive cloud asset protection platform provides CSPM through vulnerability scanning for cloud management consoles, hosts, containers, Kubernetes, and applications.
- Trend Micro Hybrid Cloud Security This package integrates with other Trend Micros security products in the Cloud One family to provide a suite of protection measures for DevOps systems.
- BMC Helix Cloud Security This platform provides CSPM configuration tests and automated remediation for discovered weaknesses with compliance built in.
What is Cloud Security Posture Management (CSPM)?
CSPM tools enable enterprises to identify and remediate security compliance issues via automated monitoring and assessments. They keep an eye out for both incorrectly implemented rules and incorrectly configured cloud apps, containers, infrastructure, and services. Anomalies and misconfigurations may be automatically fixed by CSPM tools, which are triggered by administrator-defined rules.
Security Posture Monitoring is the only tool that provides continuous monitoring and visibility of security posture across heterogeneous computing environments while providing automated detection and remediation of issues. CSPM tools are the only ones that can provide this level of automation across a wide range of platforms.
Why do we need Cloud Security Posture Management (CSPM)?
With the help of CSPM, one may protect the cloud environment and limit the risk of data breaches in a cloud environment.
Every day, the cloud makes connections to a variety of different networks. Cyberattacks are more likely as a result of this. As a result, cloud-based systems should be protected and secured by CSPM tools. Multi-cloud visibility is made possible by security technologies, which shield data from unintentional vulnerability or setup errors. It is also possible to scan and analyze the surroundings in real-time and find concealed risks. In addition, it reduces false positives, i.e., artificial intelligence’s alert fatigue.
Things to remember before choosing Cloud Security Posture Management (CSPM) tools
A CSPM tool must be chosen based on several factors.
- Company’s Demand Evaluate your needs in light of the company’s priorities and identify the most pressing issues. Don’t rush into investing in new technology without thoroughly considering the security risks of your firm and the cloud environment. Go over a variety of options before deciding on the best one for your organization.
- Extraordinary Features Advanced features such as monitoring capabilities and automatic setups must be taken into account when selecting a solution for your firm.
- Price Information Keep in mind your spending limit at all times. Online, you’ll find a wide range of tools with a wide range of functions for a low price. An investment in an affordable tool with similar features is preferable to an investment in an expensive tool with the same features. Don’t rush into deciding before you’ve looked at the plans and price of all the options.
- Free Trial Session Many tools offer free trial features that include all of the resources needed to begin the task. It’s best to look for these tools and see if the members of the team think they’re adequate before starting the procedure. It can also help you evaluate the tool and switch if necessary.
The Best Cloud Security Posture Management (CSPM) tools
The following are some of the most common Cloud Security Posture Management (CSPM) tools, which may be used by both small and large enterprises.
1. Aikido

Aikido provides a CSPM as part of a DevSecOps package that ensures new applications don’t have security weaknesses. The CSPM verifies that the supporting cloud services that the new application will run on are correctly configured.
Key Features:
- Real-Time Cloud Monitoring: Constantly scans your cloud environments to detect misconfigurations and compliance risks.
- Automated Compliance Checks: Evaluates infrastructure against SOC2, ISO27001, CIS, and other frameworks to streamline audits.
- IaC Configuration Scanning: Inspects Terraform, CloudFormation, and Kubernetes templates to catch security issues before deployment.
- Container Image Analysis: Reviews container images for vulnerabilities, improving container security posture.
- Secrets Detection: Flags exposed credentials and API keys in code to prevent unauthorized access.
The CSPM integrates CloudSploit and AWS Inspector and produces a severity score for each discovered problem. Related issues are grouped into one notification by de-duplication. The system logs all issues with their severity scores and compares retesting results to show how that risk has improved.
Pros:
- Broad Cloud Environment Support: Works across AWS, Azure, and GCP, offering unified cloud security management.
- Developer-Centric Interface: Clean, intuitive UI makes it easy for developers to act on security findings.
- All-in-One Security Platform: Combines posture management, dependency scanning, and static analysis in one place.
- Smart Prioritization: Uses reachability and context to highlight the most critical vulnerabilities first.
Cons:
- Dependency on Open-Source Tools: Uses open-source scanners, which may not always match proprietary tool depth.
You can access a free trial of the Aikido system.
2. CrowdStrike Falcon Security
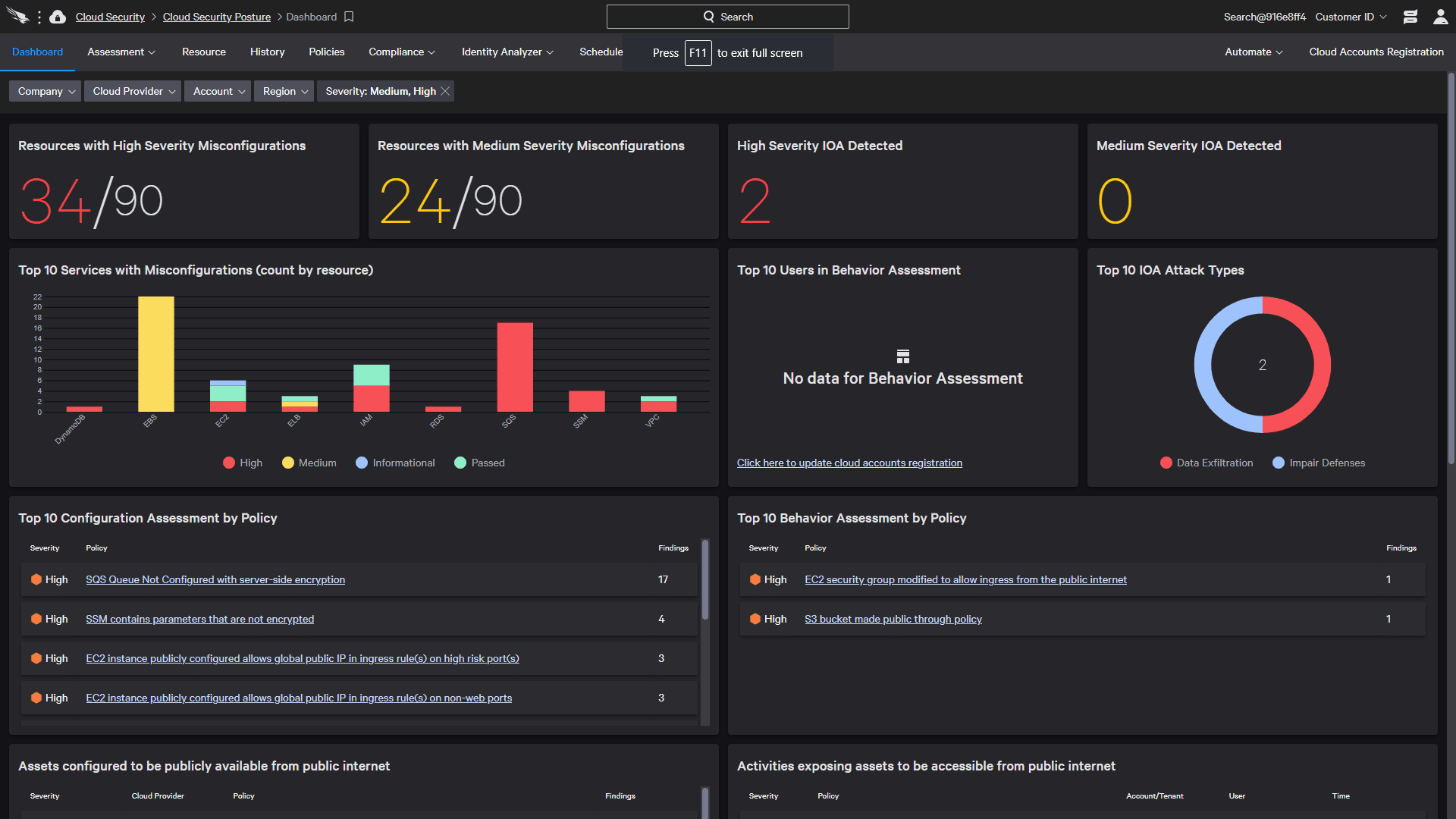
CrowdStrike Cloud Security is a package of security tools that includes a CSPM. This platform is able to manage hybrid systems, extending protection to on-premises systems as well. The CSPM will assess multiple cloud platforms simultaneously and consolidate scanning across service accounts.
Key Features:
- Constant and intelligent monitoring of cloud resources to uncover errors and dangers before they become an issue.
- Secure cloud application deployment with greater speed and efficiency.
- Unified visibility and control across many cloud environments.
- Security problems are handled in a step-by-step manner.
- For developers, guardrails are a way to keep them from making expensive errors.
- Targeted threat detection is designed to minimize alarm fatigue.
- The integration with SIEM solutions is seamless.
Why do we recommend it?
CrowdStrike Falcon Security’s CSPM capabilities are part of a comprehensive security package that excels in managing hybrid systems, providing security not only for cloud environments but also extending protection to on-premises systems. The platform stands out with constant and intelligent monitoring of cloud resources, enabling the identification and mitigation of errors and threats proactively. The unified visibility and control across multiple cloud environments, seamless integration with SIEM solutions, and targeted threat detection contribute to its recommendation. Moreover, the platform offers guardrails for developers, facilitating secure cloud application deployment with speed and efficiency.
The facts and insights you get about your overall security posture are complemented by suggestions on how to prevent future security concerns.
Who is it recommended for?
CrowdStrike Falcon Security is recommended for organizations seeking an integrated security solution that covers both cloud and on-premises systems. Its ability to assess multiple cloud platforms simultaneously makes it suitable for businesses operating in hybrid environments. The platform’s developer-friendly features, such as guardrails to prevent costly errors, make it a valuable choice for organizations with a focus on agile and secure cloud application deployment. CrowdStrike Falcon Security is an ideal fit for enterprises looking for constant, intelligent monitoring and targeted threat detection, minimizing the risk of security incidents across diverse cloud environments.
3. Datadog Cloud Security
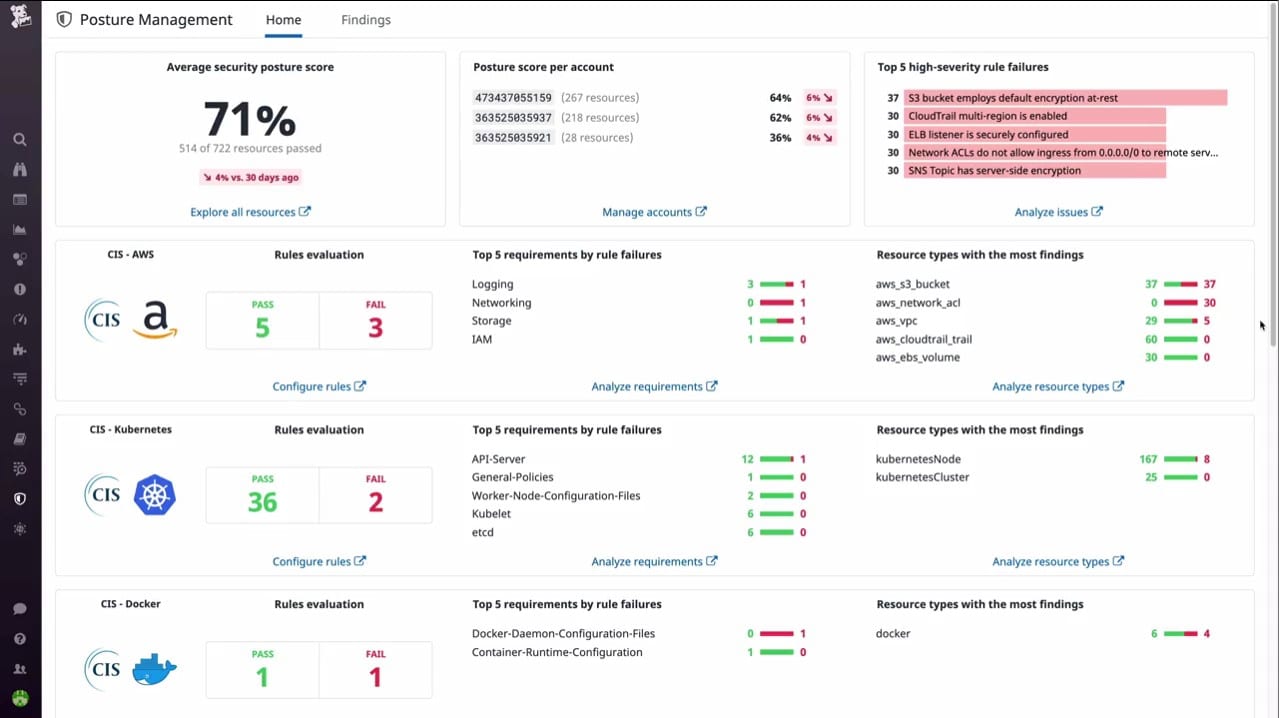
Datadog Cloud Security Management is a cloud platform that is divided into two modules: the Cloud Security Posture Management service and the Cloud Workload Security system. The CSPM checks on system configurations and corrects settings that create security weaknesses.
Key Features:
- Scans IaaS and PaaS
- Secures compute engines and storage accounts
- Checks the settings of applications
- Tracks API call rates for service account limits
- Misconfiguration alerts
- Security scores and compliance management
- Risk assessments and vulnerability prioritization
Why do we recommend it?
Datadog Cloud Security Management offers a robust cloud security platform with two key modules: Cloud Security Posture Management (CSPM) and Cloud Workload Security (CWS). The CSPM service is particularly noteworthy for its ability to scan IaaS and PaaS, secure compute engines and storage accounts, and identify and rectify misconfigurations that may pose security risks. The platform provides a comprehensive set of features, including API call rate tracking, misconfiguration alerts, security scores, compliance management, and risk assessments. Its integration with other Datadog modules, such as Cloud SIEM and Application Security Management, enhances its capabilities and provides a holistic approach to cloud security.
The Datadog platform includes many IT monitoring and management tools, and the cloud security systems can be combined with many of those companion modules. For example, the platform offers Cloud SIEM, Application Security Management, and Application Vulnerability Management, which can work together with the CSPM and the CWS services.
Who is it recommended for?
Datadog Cloud Security Management is recommended for a versatile cloud security solution that covers both security posture management and workload security. The CSPM module is suitable for businesses relying on IaaS and PaaS, with a focus on securing compute engines and storage accounts. The platform’s integration capabilities make it well-suited for organizations already leveraging other Datadog modules, creating a unified and cohesive approach to IT monitoring, management, and security. It is an ideal choice for enterprises looking for a comprehensive cloud security solution with the ability to manage security configurations, workloads, and compliance effectively.
The Datadog system is delivered from a cloud platform and you can try any and all of its modules with a 14-day free trial.
4. Cyscale
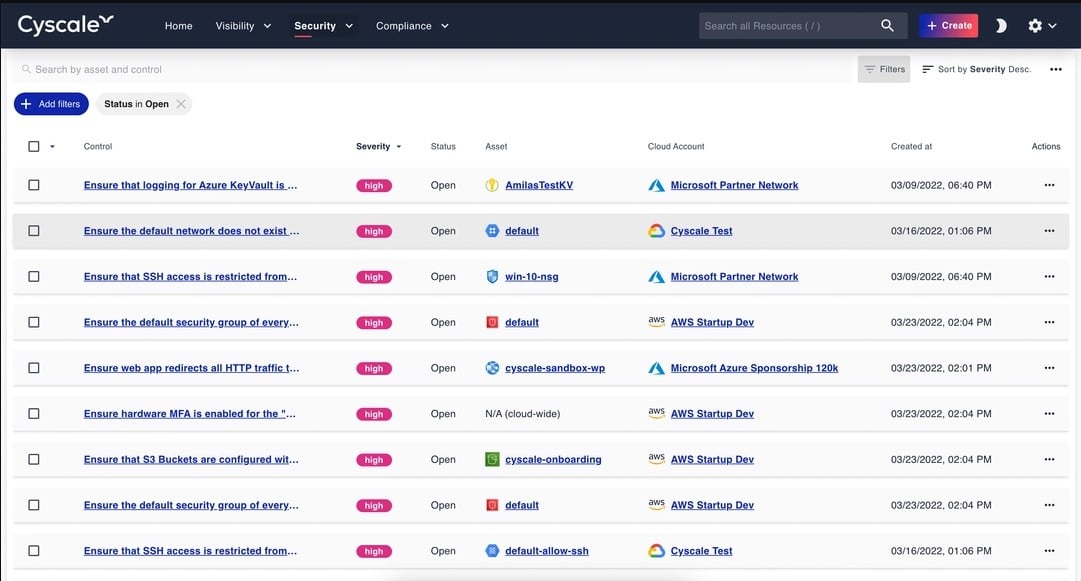
Delivered as a cloud platform, the Cyscale SaaS package provides cloud asset discovery, security scanning, sensitive data protection, compliance management, and cloud value assessments. This system is very easy to set up because it provides its own foundation date through a cloud scan, which results in the production of an application dependency map, called the Security Knowledge Graph.
Key Features:
- Identifies all cloud subscriptions and assesses their utilization
- Scans virtualizations, serverless systems, databases, compute accounts, and all types of storage
- Crosses AWS, Azure, Google Cloud, and Alibaba cloud
- Provides assessments of security weaknesses
- Discovered data stores and recommends protection measures
- Provides templates for applying stronger configurations
- Compliance enforcement and reporting
- Adaptable to CI/CD pipeline continuous testing
Why do we recommend it?
Cyscale SaaS stands out as a top recommendation due to its comprehensive suite of cloud security posture management (CSPM) tools delivered through a user-friendly cloud platform. The tool excels in cloud asset discovery, security scanning, sensitive data protection, and compliance management. Its unique feature, the Security Knowledge Graph, provides an application dependency map, enhancing visibility and understanding of security landscapes. The ease of setup is a notable advantage, as the platform initiates with a cloud scan, streamlining the foundation process.
The Cyscale platform helps you cut costs, perform security checks on cloud assets, create a full security policy, and impose controls on access to PII for standards compliance.
Who is it recommended for?
Cyscale SaaS is well-suited for businesses seeking a robust and user-friendly CSPM solution. Its cloud asset discovery capabilities make it an ideal choice for organizations aiming to gain complete visibility into their cloud subscriptions and assess utilization efficiently. Security-conscious enterprises benefit from the platform’s scanning capabilities across various cloud environments, including AWS, Azure, Google Cloud, and Alibaba Cloud. Furthermore, its adaptability to continuous testing in CI/CD pipelines caters to organizations emphasizing a DevSecOps approach, ensuring security throughout the development lifecycle. Overall, Cyscale SaaS is recommended for businesses prioritizing effective cloud security management without compromising on simplicity and versatility.
5. Check Point CloudGuard Posture Management
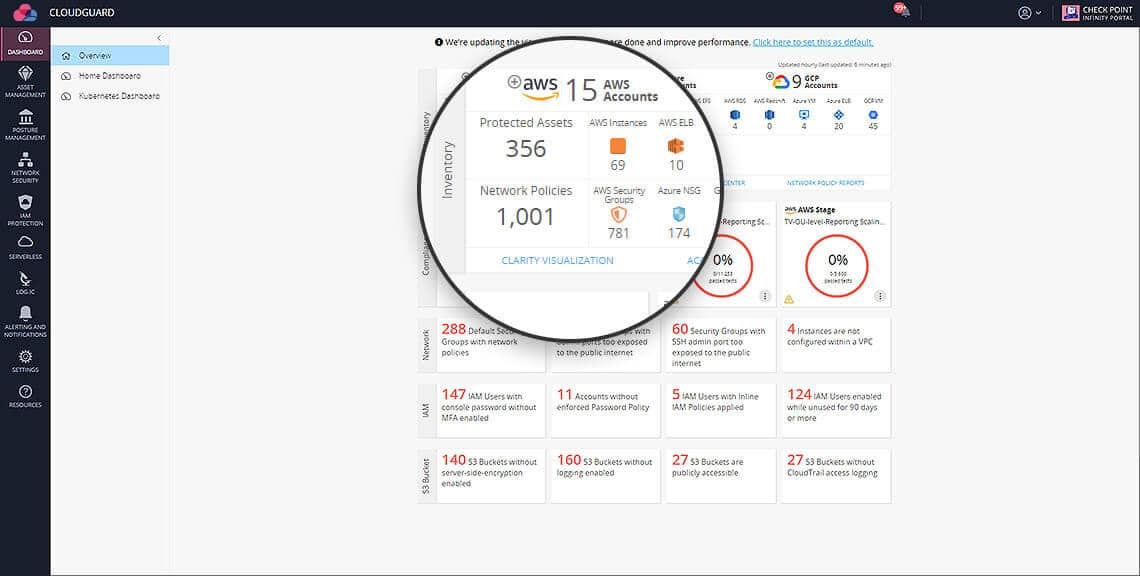
API-based agentless SaaS platform Check Point CloudGuard Posture Management optimizes administration across multi-cloud assets as part of the CloudGuard Cloud-Native Security Platform. Misconfiguration detection, security posture assessment, and visualization are some of the services provided, as are the implementation of security best practices and compliance frameworks.
Key Features:
- Enables users to apply gold standard criteria across projects, accounts, virtual networks, and geographies. Users may view their security posture and target, prioritize, and automatically fix problems.
- CloudGuard Posture Management ensures that users automatically adhere to regulatory requirements and security best practices. Users are constantly informed of their security and compliance status through comprehensive reporting.
- Privileged identity protection, based on Identity Access Management (IAM) roles and users, allows users to prevent unauthorized access to critical activities. CloudGuard Posture Management conducts frequent audits of IAM users and roles to look for anomalies.
Why do we recommend it?
Check Point CloudGuard Posture Management stands out as an API-based agentless SaaS platform that optimizes cloud administration across multi-cloud assets. As part of the CloudGuard Cloud-Native Security Platform, it offers robust misconfiguration detection, security posture assessment, and visualization services. The platform goes beyond by enabling users to apply gold standard criteria across projects, accounts, virtual networks, and geographies. It empowers users to view their security posture, prioritize issues, and automatically implement fixes. The continuous adherence to regulatory requirements, security best practices, and proactive privileged identity protection further enhance its capabilities.
Who is it recommended for?
Check Point CloudGuard Posture Management is recommended for organizations seeking a comprehensive and automated cloud security solution. It caters to users managing multi-cloud assets, allowing them to streamline administration and enforce security best practices seamlessly. The platform’s ability to ensure compliance with regulatory requirements, coupled with its proactive privileged identity protection, makes it well suited for businesses with stringent security and compliance needs. Whether targeting projects, accounts, virtual networks, or spanning various geographies, CloudGuard Posture Management provides a centralized solution for assessing, visualizing, and securing cloud environments.
6. Lacework
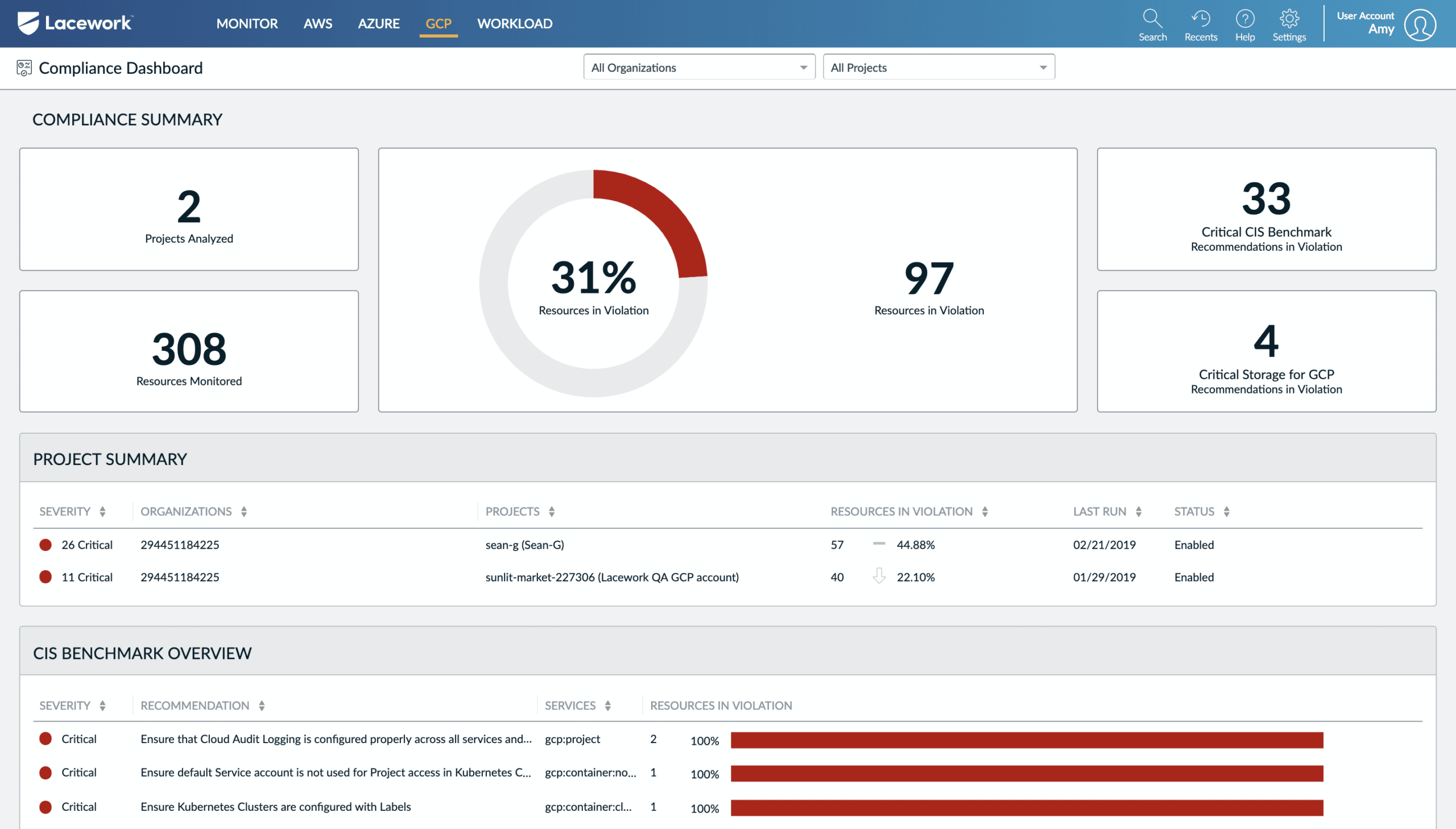
Data-driven cloud security platform Lacework automates cloud security at scale, enabling customers to innovate quickly and safely. Lacework gathers, analyses, and correlates data across an organization’s Kubernetes, AWS, Azure, and GCP systems with pinpoint precision, and then distills it down to a few important security events. Its automatic detection of intrusions, security visibility, one-click investigation, and easy cloud compliance sets Lacework apart from its rivals.
Key Features:
- Lacework alerts enterprises to any changes to rules, roles, or accounts, and notifies them of any new action. It does this by detecting new activity, documenting changes, and alerting users.
- Lacework discovers IAM issues, checks for logging best practices monitors essential account actions such as illegal API requests and maintains safe network setups to ensure that users aren’t missing anything.
- Lacework users may maintain their compliance and security up to date with a daily re-audit. Unusual actions are accounted for in lacework analysis, regardless of whether they are legal or illegal.
Why do we recommend it?
Lacework stands out as a data-driven cloud security platform that excels in automating cloud security at scale. With a focus on Kubernetes, AWS, Azure, and GCP systems, Lacework empowers organizations to innovate quickly and securely. The platform’s ability to gather, analyze, and correlate data with pinpoint precision enables automatic detection of intrusions, providing unparalleled security visibility. Lacework further differentiates itself with one-click investigation capabilities and seamless cloud compliance management, making it a top choice for those seeking efficient and effective cloud security solutions.
Who is it recommended for?
Lacework is recommended for enterprises that prioritize automation, innovation, and scalability in their cloud security efforts. Its broad compatibility with major cloud platforms like AWS, Azure, and GCP, coupled with specialized focus on Kubernetes, makes it suitable for organizations with diverse cloud environments. Lacework is particularly valuable for those who prioritize quick and safe innovation, as it not only detects intrusions automatically but also provides one-click investigation features. The platform’s continuous monitoring of changes, IAM issues, and compliance ensures that security remains up to date and aligned with industry best practices.
7. Fugue

Security and compliance platform Fugue safeguards the whole development lifecycle with a uniform policy engine backed by the Open Policy Agent (OPA). Security and cloud engineering teams have greater confidence in cloud security because of Fugue, enabling them to operate more effectively and efficiently. Security checks on CloudFormation, AWS, Kubernetes manifests, and docker files can be performed using Fugue and actionable remedial feedback may be sent using developer-friendly interfaces.
Key Features:
- Open-source policy engine Fugue enables organizations to implement compliance and security policies across the software development lifecycle.
- Fugue’s resource data engine delivers extensive visualization and reporting capabilities by continually capturing snapshots of client cloud settings to record detailed cloud resource configurations, connections, characteristics, and drift.
- Fugue’s Regula policy engine lets clients safeguard their CloudFormation and Terraform IAC at every stage of development and deployment.
Why do we recommend it?
Anchored by the Open Policy Agent (OPA), Fugue provides a uniform policy engine that instills confidence in security and cloud engineering teams. By enabling organizations to implement compliance and security policies across the software development lifecycle, Fugue enhances operational efficiency and effectiveness. Its support for security checks on CloudFormation, AWS, Kubernetes manifests, and Docker files, along with actionable remedial feedback through developer-friendly interfaces, makes it a comprehensive solution for cloud security.
Who is it recommended for?
Fugue is recommended for organizations seeking a comprehensive security and compliance platform that covers the entire software development lifecycle. It is particularly valuable for security and cloud engineering teams looking for a solution that instills confidence in cloud security operations. Fugue’s support for open-source policy engines, extensive visualization and reporting capabilities, and the ability to safeguard Infrastructure as Code (IAC) in CloudFormation and Terraform make it suitable for organizations that prioritize compliance, security, and efficient cloud resource management.
8. F5 Distributed Cloud App Infrastructure Protection
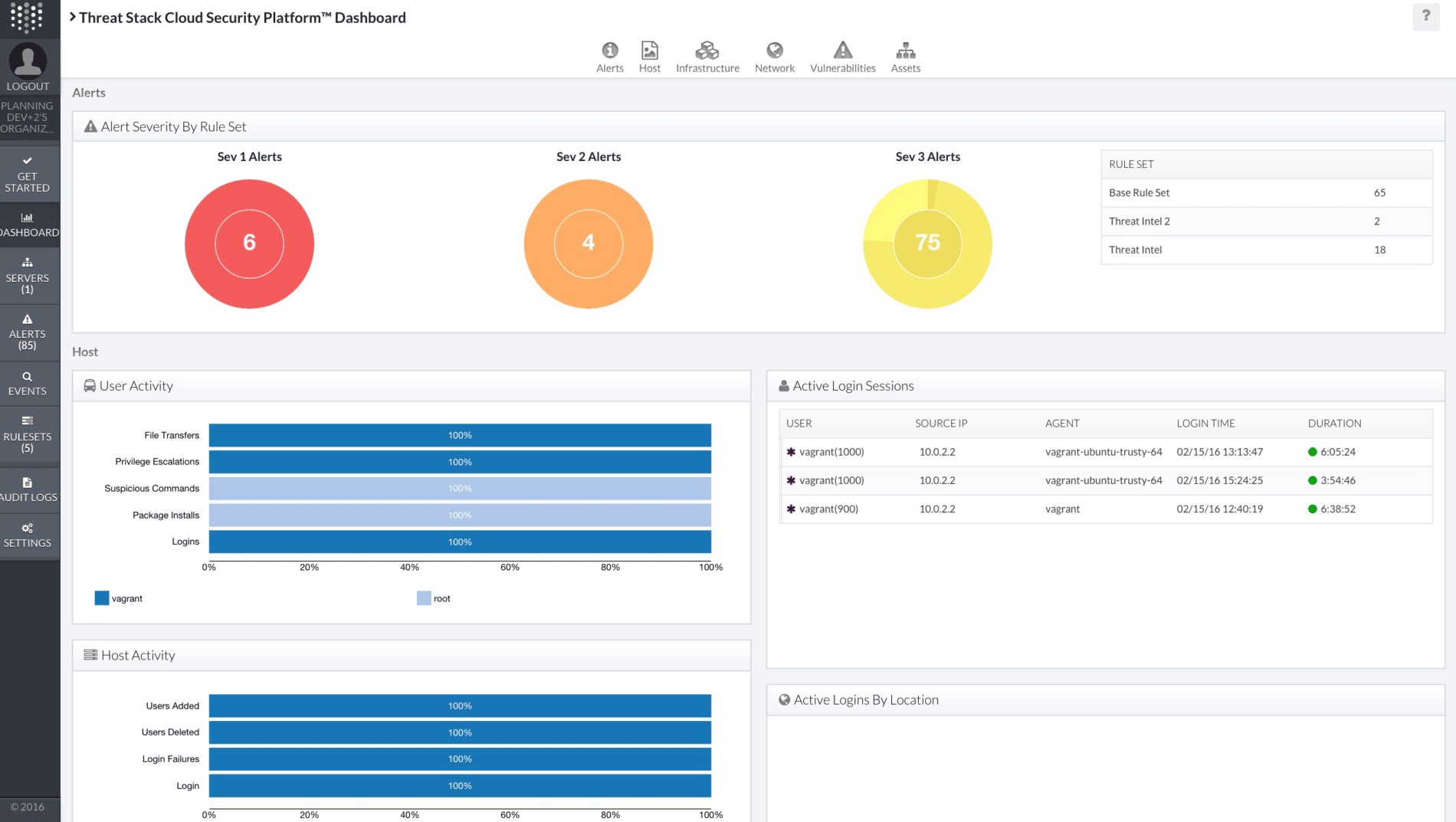
At the beginning of 2023, the Threat Stack Cloud Security Platform was bought by F5 and integrated into the F5 Distributed Cloud system. It is now called F5 Distributed Cloud App Infrastructure Protection (AIP). Although the service has been added to the F5 Distributed Cloud brand, it focuses on monitoring services hosted on premises and on the AWS platform.
Key Features:
- Implements CSPM through vulnerability scanning, identifying misconfigurations in services and applications.
- Integrates with the F5 Distributed Cloud Web App and API Protection (WAAP) package to provide full security for all cloud assets.
- Provides threat remediation guidance across the AIP and WAAP spheres.
- Scanning covering AWS services, Docker, Kubernetes, Windows servers, and Linux hosts.
- Provides file integrity monitoring.
Why do we recommend it?
The F5 Distributed Cloud App Infrastructure Protection (AIP) is a comprehensive security solution integrated into the F5 Distributed Cloud system. Focused on monitoring services both on-premises and on the AWS platform, AIP implements Cloud Security Posture Management (CSPM) through thorough vulnerability scanning. It excels in identifying misconfigurations in services and applications, ensuring a robust security posture. The integration with the F5 Distributed Cloud Web App and API Protection (WAAP) package further enhances its capabilities, providing complete security coverage for all cloud assets. Additionally, AIP offers threat remediation guidance across its sphere, making it a valuable tool for organizations aiming to secure their cloud infrastructure.
Who is it recommended for?
F5 Distributed Cloud App Infrastructure Protection (AIP) is recommended for organizations with a focus on securing their cloud assets, particularly those hosted on-premises and on the AWS platform. It is well-suited for enterprises seeking a comprehensive security solution that includes Cloud Security Posture Management (CSPM) capabilities. The integration with F5 Distributed Cloud Web App and API Protection (WAAP) makes it an ideal choice for organizations looking for an all-encompassing security suite for their cloud infrastructure. AIP’s scanning capabilities covering a range of services, including AWS, Docker, Kubernetes, Windows servers, and Linux hosts, make it suitable for diverse cloud environments.
9. Trend Micro Hybrid Cloud Security Solution

Security for cloud architects is the focus of the Trend Micro Hybrid Cloud Security Solution. With this solution, customers can easily protect their cloud infrastructure with a single, integrated platform. Because of the cloud’s security, clients may take advantage of its advantages and efficiency. It’s not only cloud platforms that Trend Micro Hybrid supports, but also DevOps processes and toolchains.
Key Features:
- While covering the network layer, Trend Micro Hybrid Cloud automates the detection and protection of cloud environments and provides easy and scalable cloud security throughout migration and growth.
- Security for your cloud services is made easier with Trend Micro Cloud One’s application-aware protection that keeps up with the latest development methodologies and technologies.
Why do we recommend it?
The Trend Micro Hybrid Cloud Security Solution provides a single integrated platform, making it effortless for customers to secure their cloud infrastructure effectively. This solution is not limited to safeguarding cloud platforms alone; it extends its protection to encompass DevOps processes and toolchains, reflecting its commitment to holistic cloud security. The platform’s automated detection and protection capabilities, specifically tailored for cloud environments, make it a valuable asset during migration and growth phases. Moreover, Trend Micro Cloud One’s application-aware protection ensures that security keeps pace with the latest development methodologies and technologies, further enhancing its appeal as a robust cloud security solution.
Who is it recommended for?
The Trend Micro Hybrid Cloud Security Solution is recommended for cloud architects and organizations prioritizing robust security for their cloud infrastructure. It is an ideal choice for those seeking a comprehensive, integrated platform that seamlessly protects against a range of security threats in cloud environments. The solution’s support for DevOps processes and toolchains makes it suitable for modern, dynamic cloud-centric workflows. Additionally, Trend Micro Cloud One’s application-aware protection makes it well-suited for organizations embracing the latest development methodologies and technologies in their cloud services.
10. BMC Helix Cloud Security

Using BMC Helix Cloud Security, services like Infrastructure as a Service (IaaS) and Platform as Service (PaaS) can be set up securely and consistently, with an audit trail, without the need for any scripting. Improved control and reduced risk are achieved by integrating compliance and security testing into the service delivery and cloud operations of BMC Helix Cloud Security.
Key Features:
- BMC Helix Cloud Security simplifies the administration of cloud security posture for customers that utilize Center for Internet Security (CIS) rules for cloud assets.
- The software’s self-driving remediation, automated remediation through an intuitive user interface, and customized remediation assistance all simplify the repair process for end-users.
- CIS, GDPR, and PCI are just a few of the regulations that BMC Helix Cloud Security adheres to. BMC Helix also supports the creation of custom policies.
Why do we recommend it?
BMC Helix Cloud Security is a highly-recommended solution for organizations looking to establish secure and consistent services such as Infrastructure as a Service (IaaS) and Platform as a Service (PaaS). What sets BMC Helix apart is its ability to achieve this without the need for extensive scripting, providing an efficient and streamlined approach to service setup. By seamlessly integrating compliance and security testing into service delivery and cloud operations, BMC Helix Cloud Security enhances control, reduces risk, and ensures an audit trail. The platform’s adherence to key regulations like Center for Internet Security (CIS), GDPR, and PCI, coupled with support for custom policies, underscores its versatility and reliability.
Who is it recommended for?
BMC Helix Cloud Security is recommended for organizations seeking simplified administration of cloud security posture, especially those utilizing Center for Internet Security (CIS) rules for cloud assets. The platform’s self-driving remediation, automated remediation through an intuitive user interface, and customized remediation assistance make it particularly suitable for end-users looking for an efficient and user-friendly solution. With support for various regulations, including CIS, GDPR, and PCI, BMC Helix Cloud Security caters to diverse compliance needs.

